Tax Scams Hit Nearly 1 in 4 Adults. Spot the Red Flags

John C. isn’t the person you picture getting scammed.
He’s 36. He’s tech-savvy. He’s a mechanical engineer leading a team at a national energy lab in Denver. And he told us his story for one reason: “Scammers will target anyone.”
It began with a phone call from someone claiming to be the IRS. They said John had underpaid his taxes and needed to resolve it quickly. The caller sounded polished and convincing, so convincing that John didn’t stop to question it.
“I thought maybe they sent back too much money [in my refund], and they needed it back,” he said. “I was just so busy and overwhelmed that I never really stopped to think about the situation.”
A follow-up email arrived with IRS logos, clean formatting, and a big payment button. John was trying to move fast between classes as he finished up his PhD, and he wanted to correct the situation as quickly as possible.
“I was like, let me just hurry up and do this, get it over with.”
He clicked. He paid. But later, when he checked his statement, he saw the charge didn’t look like an IRS payment at all. In fact, it was an international charge. The whole thing was a scam.
John said the scammer on the phone had appealed to his emotions and been incredibly convincing.
“It was absolutely masterful,” John said. “I would give him an Oscar for it.
And new McAfee research shows John isn’t alone, with nearly 1 in 4 (23%) US adults surveyed revealing they’ve lost money to a tax scam.
Key findings from McAfee’s 2026 Tax Season Survey
Here’s what our January 2026 survey of 3,008 U.S. adults found:
The big picture: lots of worry, not enough confidence
- 82% of Americans say they’re concerned about tax fraud this season.
- 67% say they’re seeing the same or more tax scam messages than last year.
- 40% say tax scam messages are more sophisticated than last year.
- 84% are concerned about AI making tax scams more realistic.
- Only 29% say they’re very confident they could spot a deepfake tax scam.
How often scams are reaching people
- 34% say they’ve been contacted by someone claiming to be the IRS or another tax authority (phone, text, or email).
- 38% say they’ve been asked to click a link or send payment related to a “tax issue.”
- Common asks include SSNs (15%), birth dates (11%), addresses (10%), “you owe back taxes” pressure (9%), and banking details (8%).
Who is getting hit hardest
- Nearly 1 in 4 Americans (23%) say they’ve fallen for a tax scam.
- Young adults report the highest exposure: 42% of 18–24-year-olds say they’ve fallen for at least one tax scam.
- 11% of Americans report tax-related identity theft, rising to 17% among ages 25–34.
The money is real
- Among people who say they’ve fallen for a tax scam, the average loss is $1,020.
- Separately, nearly 1 in 5 Americans say they’ve lost money to a tax scam.
Tax filing is increasingly digital (and that changes the risk)
- 55% say they file taxes online (software or IRS Free File).
- 75% say they receive refunds or pay taxes electronically (direct deposit, cards, apps, EFTPS, etc.).
- 30% say they plan to use an AI tool (like ChatGPT) to help prepare taxes, especially younger adults. This is highly dangerous, even with platform security protections. For example, if an AI tool were compromised in a data breach, user messages with personal tax information (like social security numbers, home address, and more) could be made public.
Tax Scams Now Hit Year-Round, McAfee Labs Finds
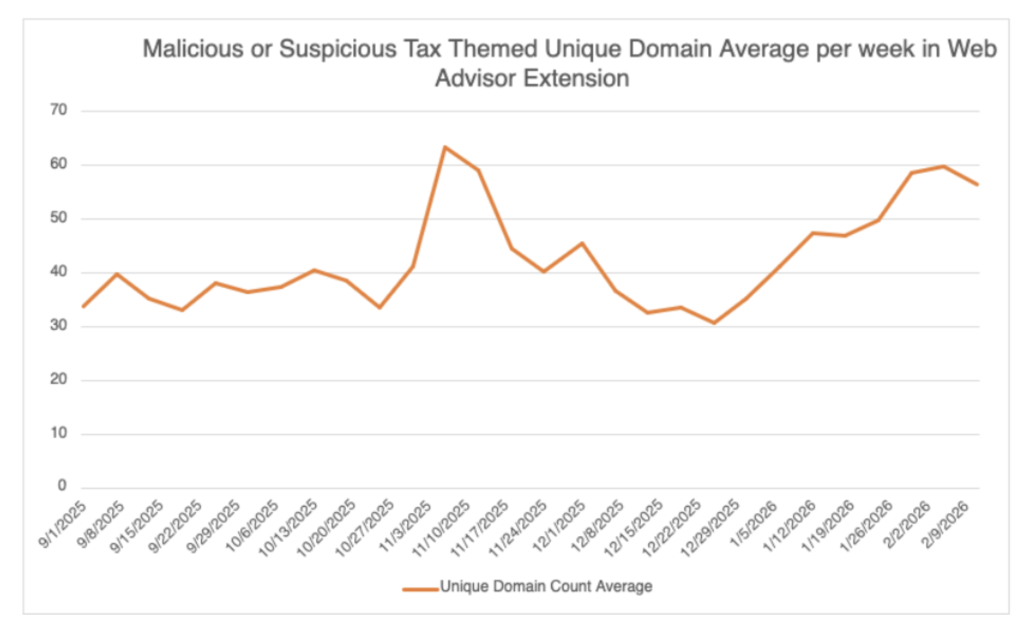
In addition to our consumer survey findings, McAfee Labs analyzed malicious URLs, apps, texts, and emails in the months leading up to filing season.
The major takeaway: tax scams don’t wait for April.
Scam activity began climbing as early as November and has again continued building steadily into 2026.
Between September 1, 2025, and February 19, 2026, McAfee Labs identified 1,468 malicious or suspicious tax-themed unique domains, an average of 43 new fake tax websites every day.
In early November 2025 alone, the average number of new tax-themed malicious domains nearly doubled in just over a week. After a brief dip in late December, activity resumed climbing into February, a pattern we expect to intensify as the April filing deadline approaches.
Fake IRS Websites Are A Major Threat
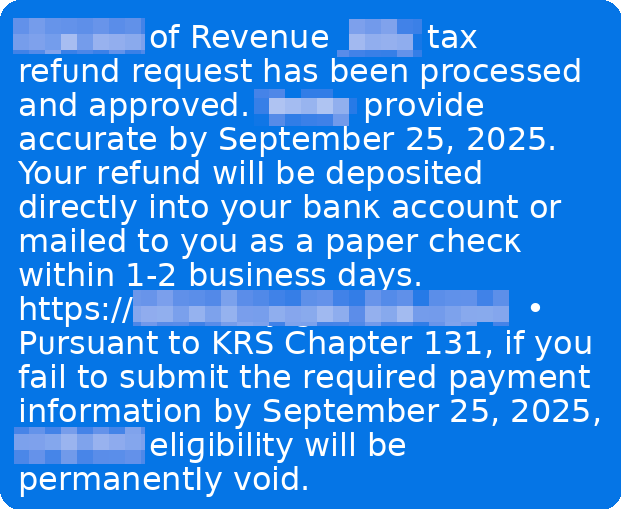
Scammers are rapidly creating lookalike IRS domains that mimic official government URLs.
They use small changes, extra letters, added words, subtle misspellings, to trick taxpayers into believing they’re on a legitimate IRS site.
Examples include domains that insert additional text around “irs.gov” or add misleading subdomains designed to pass a quick glance.
These fake portals are used to:
- Steal login credentials
- Harvest Social Security numbers and tax IDs
- Capture payment details
- Charge bogus “processing fees”
In some cases, these sites don’t just steal, they overcharge.
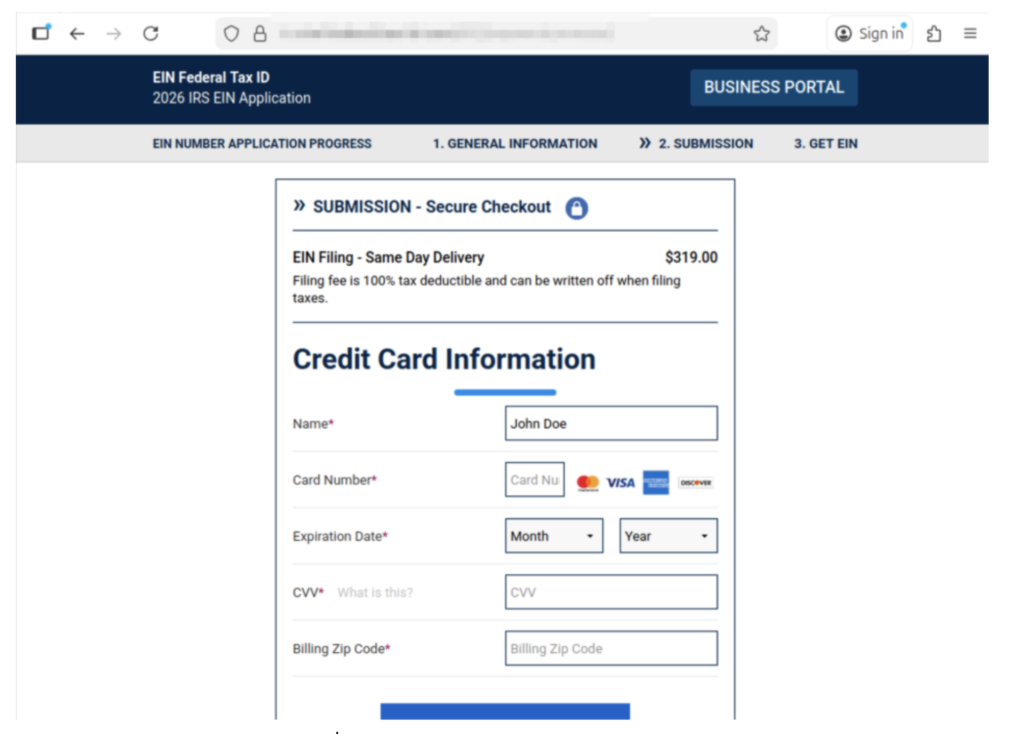
McAfee Labs observed scam services offering to file for an EIN (Employer Identification Number), something the IRS provides for free, and charging as much as $319 for it.
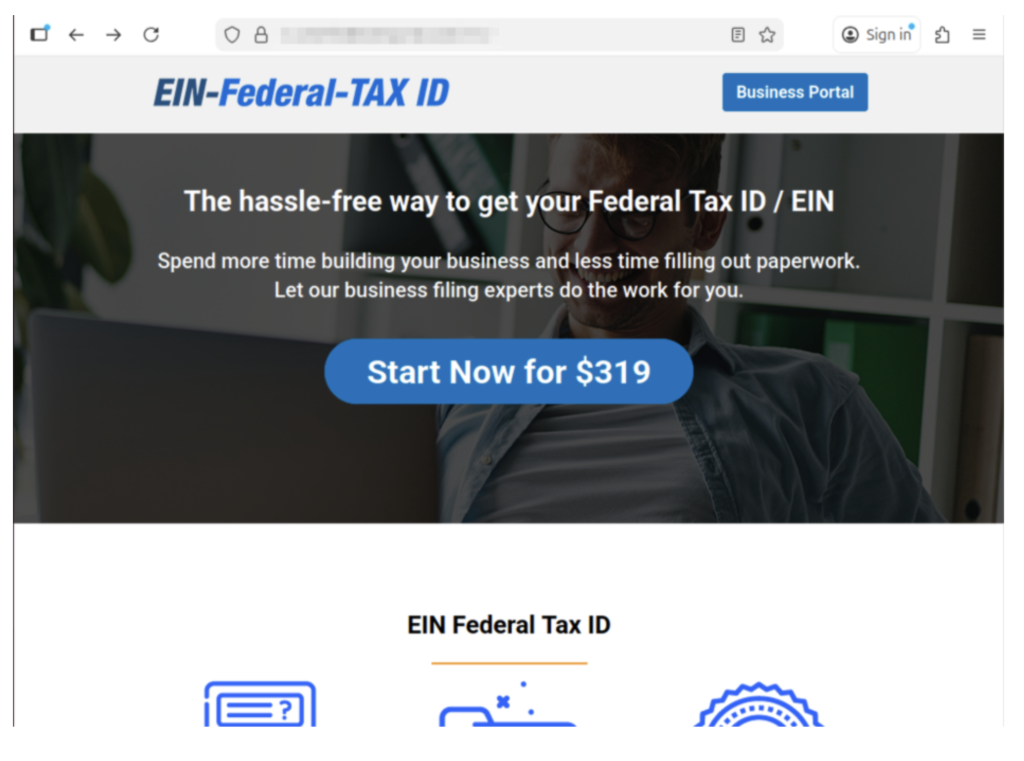
Example of a scam website we found charging for an EIN.
The official IRS website explicitly warns: you never have to pay a fee to obtain an EIN.
Other scam sites misuse legitimate policy terms, like the “Fresh Start Initiative,” to harvest personal data and enroll victims in aggressive robocall and marketing campaigns.
Tax scams don’t always steal outright. Sometimes they monetize confusion.
How a Typical Tax Scam Unfolds
Most tax scams aren’t one single message. They’re a sequence, designed to make you panic, click, and comply.
Below is the common playbook, plus the red flags that show up repeatedly.
*Note: Scammers may swap the details like AI voice, fake IRS videos, cloned websites, or impersonating tax software, but the pattern stays familiar.
| Step | What happens | Red flags you’ll see at this step | Red flags that are true every time | What to do instead |
| 1) The hook | You get a call, text, or email claiming there’s a tax issue (refund problem, underpayment, verification needed). | Message arrives out of nowhere, often during busy hours; “final notice” language; spoofed caller ID. | Unexpected contact + urgency. | Don’t engage. Pause. Go directly to IRS.gov or your tax provider’s official site (type it in). |
| 2) The authority move | They lean hard on being “the IRS” or “state tax authority,” sometimes with personal details. | They sound polished; may use AI voice cloning; may cite a “case number.” Fake or meaningless case numbers are very common. | They want you to trust the title, not verify the source. | Ask for written notice and time. Real tax issues can be verified through official channels. |
| 3) The link | They send a link to a “secure portal” or “refund page.” | Lookalike website, subtle misspellings, weird domain, shortened link, email button that says “Pay Now.” | They’re trying to pull you off official channels. | Never click the link. Navigate to the real site yourself. If unsure, delete it. |
| 4) The data grab | The site (or “agent”) asks for SSN, banking info, login credentials, or details from a prior return. | Requests that are broader than needed; “verify identity” prompts; form fields that feel too invasive. | They want sensitive info fast. | Stop. Don’t type anything. If you already did, assume it’s compromised and act quickly (see next section). |
| 5) The payment push | They demand payment to “avoid penalties,” “release your refund,” or “resolve a mistake.” | Gift cards, crypto, wire transfers, payment apps; pressure to pay today; threats. | Urgency + unusual payment method. | The IRS does not demand immediate payment via text/social, and doesn’t require gift cards or crypto. Verify independently. |
| 6) The escalation | If you hesitate, they intensify: threats, “law enforcement,” or AI video/audio that “proves” it’s real. | Deepfake IRS video, intimidating language, “you’ll be arrested,” “your license will be revoked.” | Fear is the product. | Hang up. Save evidence. Talk to a trusted person. Contact official support through verified numbers. |
| 7) The aftermath | You realize it was a scam—often after noticing a strange charge or login activity. | Charges from odd merchants; new accounts; IRS account alerts; failed tax filing due to “duplicate return.” | Shame keeps people quiet—scammers count on that. | Report it and protect your identity right away. You’re not alone, and it’s not your fault. |
Key point: A message can look “official” and still be fake. AI is making scam language smoother and scams more believable. The safest habit is simple: slow down, and verify using official sources you navigate to yourself.
What to do if you’ve been involved in a tax scam
First: take a breath. Scams are designed to trick you, especially when you’re overwhelmed, rushed, or just trying to fix a problem quickly.
John said it plainly: “Don’t be embarrassed. It does happen. It’s common… they will target anyone.”
And he’s right. The most important thing is what you do next.
1) Stop the bleeding: cut off contact
- Stop replying
- Don’t click anything else
- Don’t send more information or money
2) Capture proof (before it disappears)
Take screenshots and save:
- Phone numbers, email addresses, usernames
- The message content
- Links (don’t click them, just copy)
- Payment receipts and transaction IDs
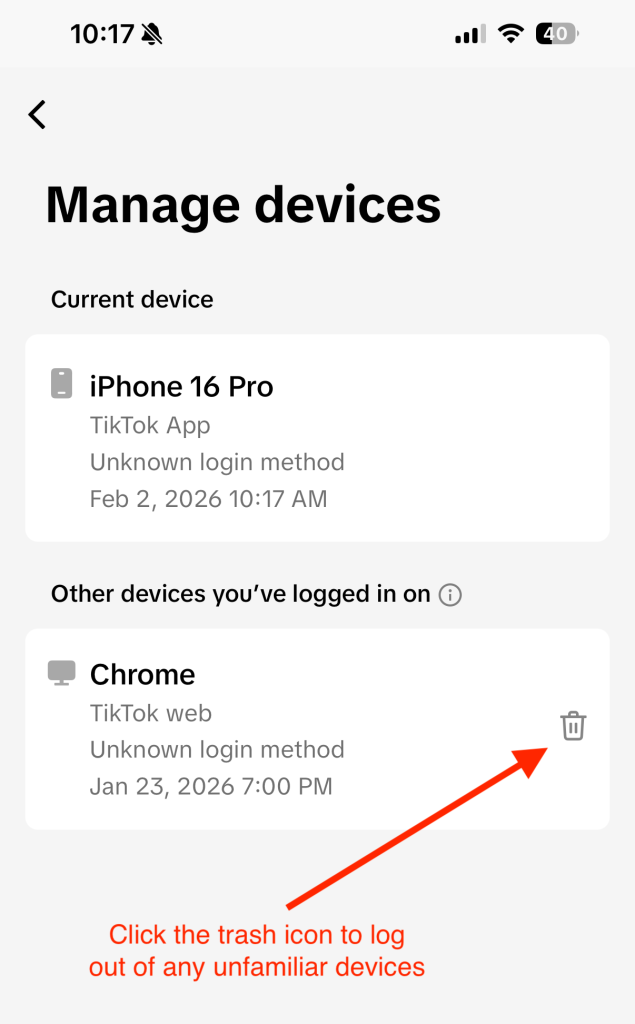
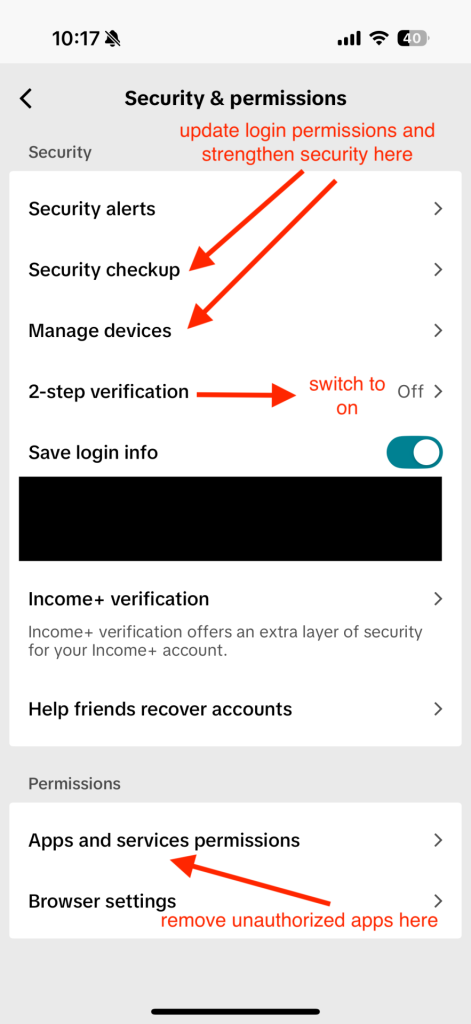
3) Lock down your accounts (especially email)
If a scammer gets into your email, they can reset passwords for everything else.
Do this today:
- Change your email password first, then banking/tax accounts
- Turn on two-factor authentication (2FA)
- If you reused passwords anywhere, change those too
Important: If you clicked a suspicious link, downloaded a file, or gave someone remote access to your computer, make sure you use a different, trusted device (like your phone or another computer) to change passwords. Why? If a scammer installed malware or has access to your computer, they may be able to see all of your brand-new passwords as you’re making them.
Tip: A password manager like McAfee’s can help you create strong, unique passwords quickly, without having to memorize them all.
4) Check for identity theft signals
Tax scams often turn into identity theft. Watch for:
- IRS notices about a return you didn’t file
- Trouble e-filing because a return was already submitted
- Alerts about a new IRS online account you didn’t create
If you suspect tax-related identity theft:
- Consider filing an IRS identity theft report (commonly done with IRS Form 14039, Identity Theft Affidavit).
- Create or log into your IRS account periodically to review account activity (John now does this every few months).
McAfee’s Identity Monitoring can help restore your sense of security and privacy online.
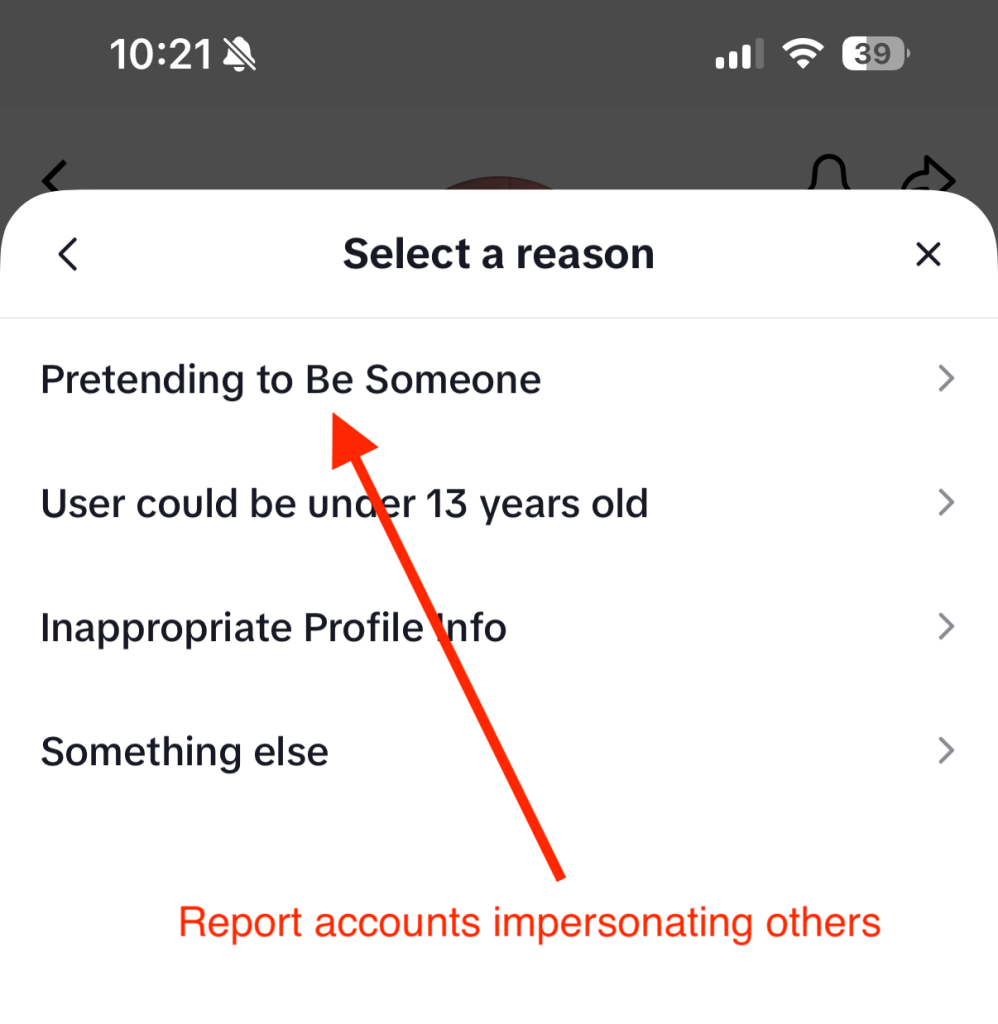
5) Report it (even if you feel weird about it)
Reporting helps you and helps stop the next person from getting hit.
Common reporting options include:
- FTC report: Report scams and identity theft at the FTC’s reporting site.
- IRS phishing email: If you received a scam email posing as the IRS, you can forward it to phishing@irs.gov.
- Your bank or card provider: If you paid, contact them immediately. Even if recovery isn’t guaranteed, speed matters.
6) Clean up your digital footprint
Scammers don’t just use what you give them. They also use what they can look up.
Removing your personal details from risky data broker sites can reduce how easily scammers can target you again. Tools like Personal Data Cleanup can help you identify where your information is exposed and guide removal.
7) Add protection for the next attempt
Tax season scams often come in waves, especially if scammers think your info is “good.”
Helpful layers include:
- Web protection to warn you about risky links and lookalike sites before you enter info – get our free WebAdvisor download here
- Scam detection that can flag suspicious messages
- Identity monitoring to alert you if key personal info shows up in risky places
- Run a free antivirus scan to check your device for malware or unwanted programs (especially if you clicked a link or downloaded anything)
The key takeaway
Tax season creates the perfect storm: time pressure, sensitive data, and a lot of official-looking communication.
Our research shows most people are worried, and for good reason. Scammers are getting more convincing, and AI is raising the bar on what “real” looks and sounds like.
“Tell your friends, tell your family,” John said. “Everyone I know at some point has heard this story, and it might just prevent someone from losing… thousands of dollars.”
If you remember just three things this season, make them these:
- Pause before you click.
- Verify through official channels you navigate to yourself.
- If something happens, act quickly, and don’t blame yourself.
The post Tax Scams Hit Nearly 1 in 4 Adults. Spot the Red Flags appeared first on McAfee Blog.