McAfee Blogs
McAfee Blogs
By:
McAfee
— November 9
th 2025 at 20:14
This is a critical time for our personal security, particularly in terms of privacy and personal information. A battle is being waged over our data by multiple parties, from criminal hackers to advertisers and data brokers. This article provides essential tips to help you protect the personal details you want to keep private and stay safe online.
The Battle for Your Personal Data
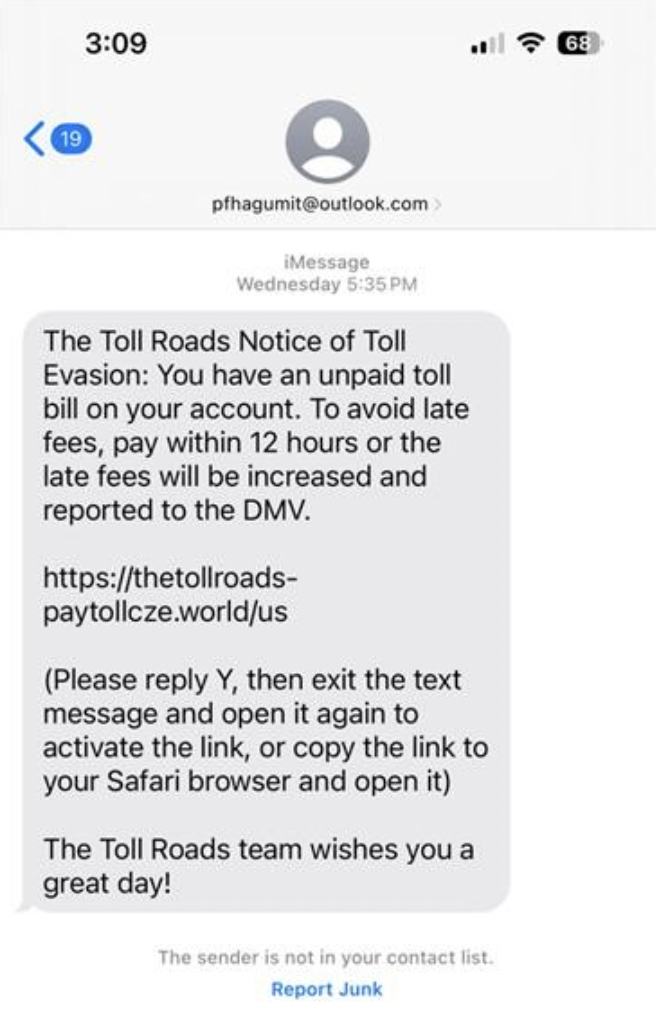
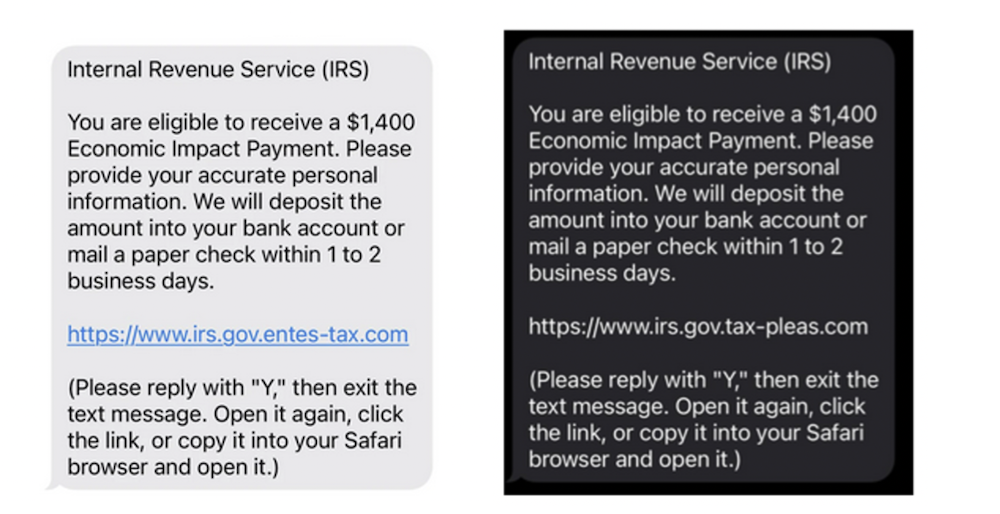
Criminal hackers and identity thieves want to use your name to open new accounts, which they can turn into cash. They may try to obtain credit cards, utility services, or mobile phones using your good credit. In other cases, these same thieves take over existing bank or credit card accounts and completely empty them out. Identity theft affects millions of Americans each year, with over 1.4 million reports filed to the FTC in recent years and an estimated 15 million victims annually.
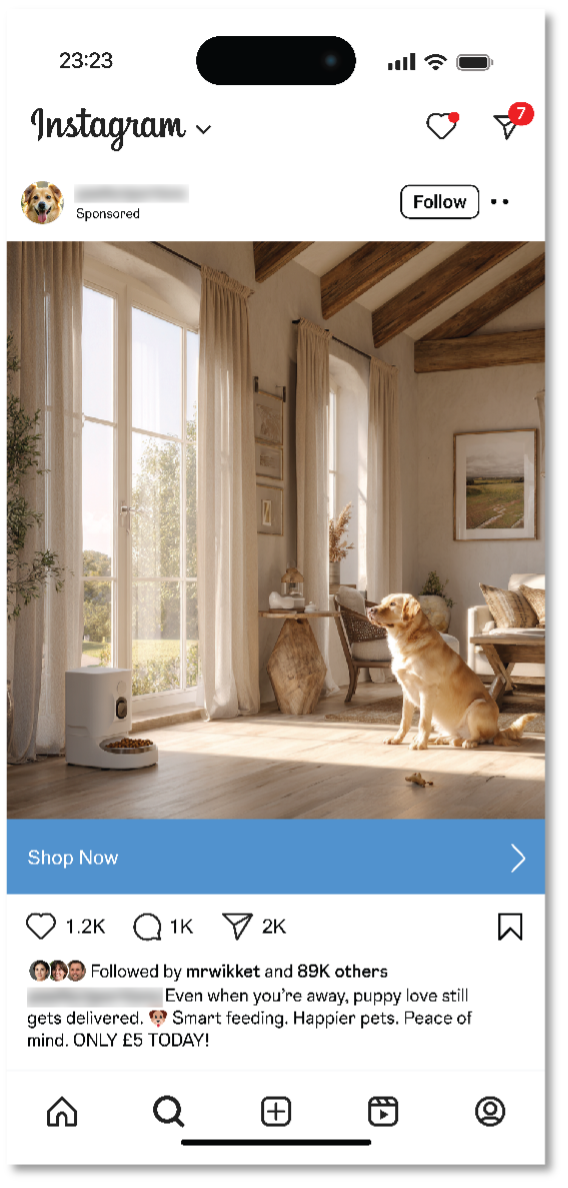
Online Tracking and Advertising
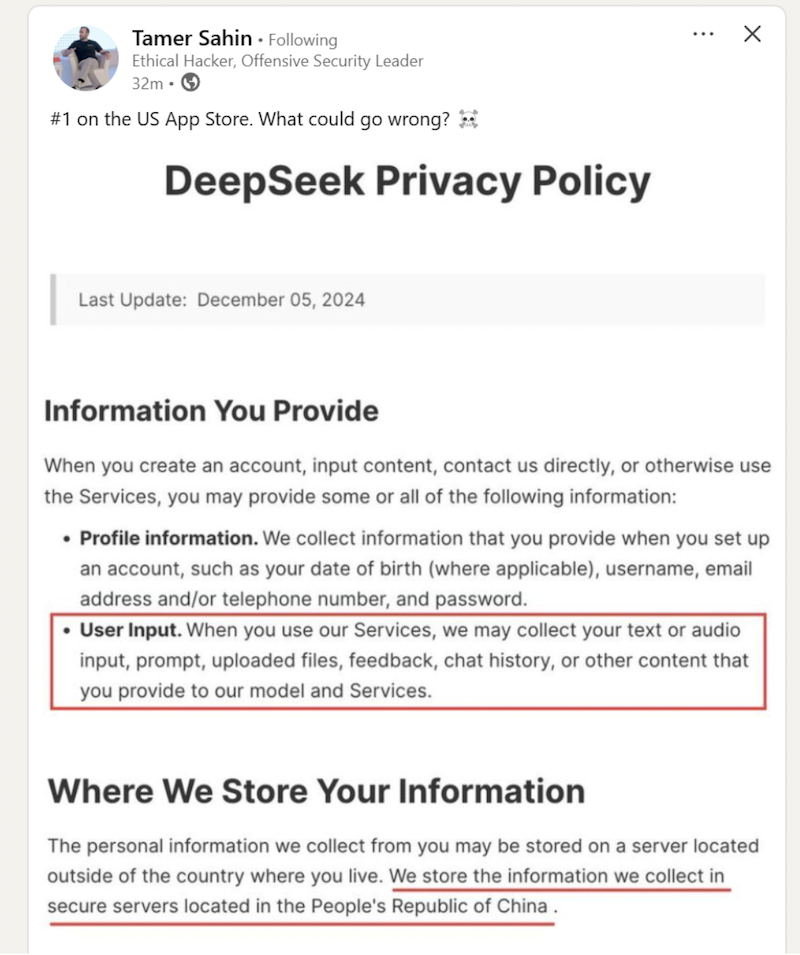
Online, advertisers and marketers use tracking cookies and sophisticated technologies to gather information about you and your web browsing habits. They can then offer you products or services based on the profile they’ve developed. Almost every major website contains cookies, and they are changing the way advertising is created and targeted.
The Federal Trade Commission (FTC) has explored options, such as “Do Not Track” mechanisms, to allow consumers to opt out of data collection; however, these efforts have faced significant challenges. Browser-based solutions have been proposed, but the advertising industry’s partnerships with major media and tech companies have made comprehensive opt-out mechanisms difficult to implement effectively.
Social Media Privacy Risks
Social media companies compete for your attention and your information because user data is valuable to advertisers and marketers. Whatever you post in your profile is broken down, cataloged, and disseminated. Your name, age, address, email, phone number, contacts, income status, job description, and other personal details are of use to anyone targeting your wallet.
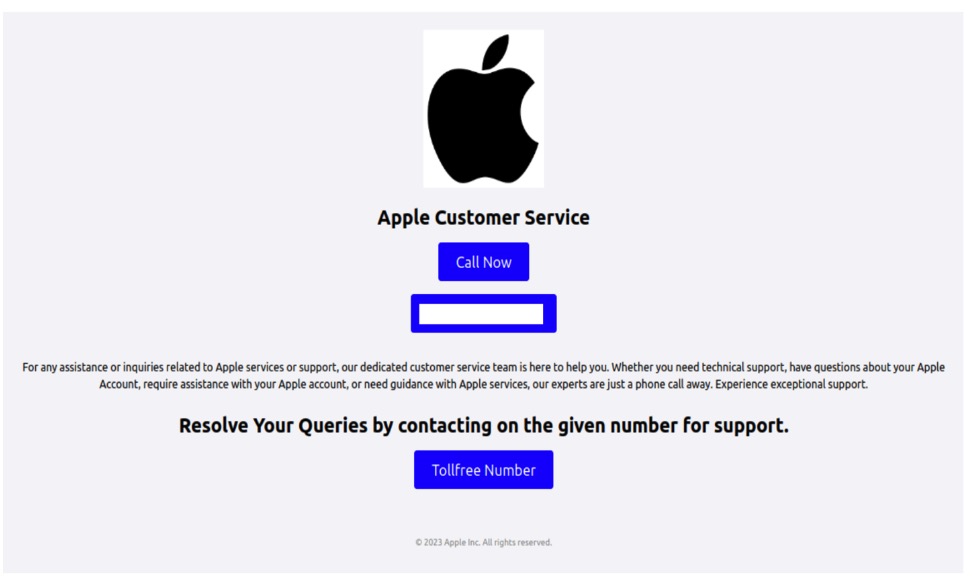
However, legitimate advertisers aren’t the only ones targeting social networks. Criminal hackers and identity thieves are accessing your data, either through the public portion of these sites or by hacking through the back door. The bad guy is using your profile information to come up with an answer to your password reset question, or to trick you into opening your wallet or entering login credentials that might allow them to take over your existing accounts.
What is Data Privacy Day?
Amid all these developments, the National Cyber Security Alliance established Data Privacy Day, an annual awareness event observed every January 28, which encourages you to take control of your personal information and understand your online privacy rights. Initially launched in 2008, this important day coincides with the anniversary of the signing of Convention 108, the first legally binding international treaty dealing with privacy and data protection.
As a U.S. consumer, Data Privacy Day matters to you more than ever because your personal information has become incredibly valuable and, unfortunately, increasingly vulnerable. Every day, you share personal details through social media, shopping websites, mobile apps, and online services, often without realizing how this information is collected, used, or shared.
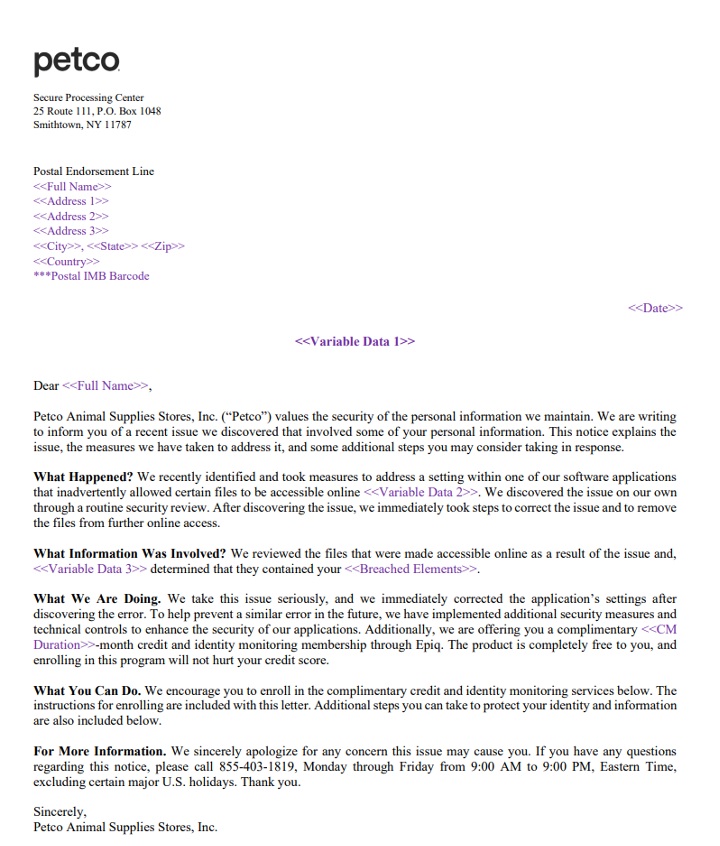
The observance of this day highlights several key risks that affect your daily digital life. Data misuse occurs when companies collect more information than necessary or use your personal details in ways you haven’t explicitly approved. Identity theft remains a significant threat, with criminals using stolen personal information to open fraudulent accounts, make unauthorized purchases, or even file fake tax returns. Additionally, data breaches continue to expose millions of Americans’ personal information each year, from social security numbers to financial details.
What makes Data Privacy Day empowering is its focus on actionable steps you can take immediately. Rather than feeling overwhelmed by privacy concerns, you can use this day as motivation to review and strengthen your digital privacy habits. The day is a reminder that privacy and data protection aren’t just technical concepts. They’re fundamental rights that help you maintain control over your digital life.
Data privacy core concepts
Before delving deeper into regulations and best practices, let’s take a look at the core concepts. The Federal Trade Commission defines data privacy as the reasonable expectation that your personal information will be handled appropriately by the organizations that collect it. It is your fundamental right to control how your personal information is collected, used, shared, and retained by the companies and services you interact with every day. At its heart, data privacy ensures that you have a say in what happens to details about your life, from your name and email address to your online shopping preferences, videos watched, social media usage, and down to your browsing habits and location data.
Your data follows a path that starts with collection, when companies gather information directly from you, such as when you fill out a form, or indirectly through cookies and tracking pixels. The use phase refers to how organizations process your information, whether to improve their services, target advertisements, or analyze user behavior. Sharing involves passing your data to third parties, from business partners to data brokers. Retention determines how long your information stays in their systems, often well beyond the end of your active relationship with the service.
Throughout this process, your information is governed by three principles of modern data privacy:
-
Consent means companies should ask for your permission before collecting and using your personal information, and this permission should be freely given, specific, and informed. You shouldn’t have to accept data collection just to use basic services.
-
Control gives you the power to access, correct, delete, or restrict the use of your personal data.
-
Transparency requires companies to clearly explain their data practices in plain language, rather than burying them in lengthy legal documents.
When Netflix asks if you want to share viewing data to improve recommendations, that’s consent in action. When Google lets you download your search history or delete location tracking, you’re exercising control. When Apple’s privacy labels show exactly what data an app collects, that’s transparency working for you.
Your data privacy rights
Under these newly instituted state privacy laws, you have several key rights that put you in control of your personal information:
-
Right to know: You can request information about what personal data companies collect about you, how it’s used, and who it is shared with.
-
Right to access: You can obtain copies of the personal information companies have collected about you.
-
Right to delete: You can request companies to delete your personal information, with certain exceptions.
-
Right to opt out: You can opt out of the sale or sharing of your personal data for targeted advertising.
-
Right to correct: You can request corrections to inaccurate personal information.
-
Right to non-discrimination: Companies cannot penalize you for exercising your privacy rights.
Data privacy and data protection
Data protection and data privacy are sometimes used interchangeably, but they serve different but complementary roles in keeping your personal information safe:
-
Data privacy is about your rights and choices in how your personal information gets collected, used, and shared. It’s less about technical security and more about giving you control over what happens with your data.
-
Data protection is about securing your information from threats such as hackers, breaches, and technical failures. It is the digital equivalent of a bank vault, using technical and organizational safeguards to keep your data safe from unauthorized access, theft, or loss.
Here are some everyday scenarios that show how these concepts work differently:
-
Your encrypted backup files represent data protection in action. Even if someone gains access to your backup drive without the proper key, encryption makes your photos, documents, and files unreadable. The technical safeguard protects your data from misuse.
-
Choosing who can see your location on social media is a privacy decision. When you decide what personal information to share and with whom, you are exercising control over your data.
-
Your password manager provides data protection by securely storing and encrypting your login credentials, making them nearly impossible for criminals to steal and use.
-
Declining to provide your phone number when signing up for a shopping account is a privacy choice. You’re limiting the amount of personal information that gets collected about you in the first place.
Data privacy laws
As a consumer, your data privacy rights translate into real, actionable benefits you can use today. However, the effectiveness of these protections often depends on enforcement and your own awareness of the tools available to you.
The U.S. privacy landscape
U.S. state privacy laws are increasingly giving you the right to know what personal information companies collect, the right to delete your data, and the right to opt out of having your information sold or shared.
America’s privacy framework is built on sector-specific federal regulations combined with increasingly robust state legislation. This approach means your rights and protections can vary significantly depending on where you live and what type of data is being collected.
At the federal level, key laws include the Health Insurance Portability and Accountability Act (HIPAA) for healthcare data, the Fair Credit Reporting Act (FCRA) for credit information, and the Children’s Online Privacy Protection Act (COPPA) for children under 13 years. While these provide important protections in specific areas, they leave significant gaps in comprehensive consumer data privacy protection.
To fill these gaps, California established crucial precedents through the California Consumer Privacy Act (CCPA) and its successor, the California Privacy Rights Act (CPRA). Other states are also now enacting comprehensive privacy laws, including Virginia’s Consumer Data Protection Act, Colorado Privacy Act, Connecticut’s Data Privacy Act, and Utah’s Consumer Privacy Act. Each provides residents with fundamental rights over their personal data while requiring businesses to implement stronger protection measures.
Extra care for highly sensitive personal data
Sensitive personal data represents the most valuable and vulnerable information about you—the details that, if compromised, could cause significant harm to your finances, safety, and peace of mind. Unlike basic contact information, sensitive data requires stronger legal protections and your extra vigilance because of its potential for misuse.
Health Information
Your health information deserves particular care because it reveals intimate details about your physical and mental well-being. HIPAA protections cover medical records, but health data collected by fitness apps, mental health platforms, or wellness websites may not receive the same legal safeguards.
Biometric data
Biometric data—your unique physical characteristics such as fingerprints, voice patterns, or facial features—can’t be changed if stolen, making this information particularly precious.
Children’s Information
Children’s data receives special attention under privacy laws because minors can’t meaningfully consent to data collection. The Children’s Online Privacy Protection Act requires explicit parental consent before companies can collect information from children under 13, while some state laws extend these protections to older teens.
GDPR for the global services
Meanwhile, global services such as Google, Facebook, or Netflix apply the Europe-established General Data Protection Regulation (GDPR) laws worldwide to maintain consistent data practices.
GDPR personal data includes obvious identifiers such as your name, email address, phone number, and Social Security number. But it also covers less obvious information, such as IP addresses, device IDs, location data, and even your online shopping habits or social media activity. Essentially, if data points can be combined to create a profile of you, they qualify as personal data under GDPR standards. This broader definition gives you stronger control over your information and has influenced many U.S. companies to offer the same rights to all users, not just those in the European Union.
Whether a company follows GDPR, California’s privacy laws, or other frameworks, the core principle remains the same: you deserve transparency and control over your personal information.
How can you celebrate Data Privacy Day?
Your privacy rights are expanding, but exercising them effectively requires staying informed and taking proactive steps. As we celebrate Data Privacy Day, we recommend you participate by taking simple, practical steps to exercise your data privacy rights.
Review your privacy settings regularly
Start with the platforms and services you use most frequently. Look for the privacy or data protection section in your account settings and review the information being collected and shared.
Submit data access requests
Many major companies now provide online forms or dedicated email addresses for privacy requests. Take advantage of these to understand what data they have about you. Popular platforms such as Google, Facebook, and Amazon have streamlined processes for data downloads.
Opt out of data sales
Look for “Do Not Sell My Personal Information” links on websites, typically found in footers or privacy policy pages. You can also use opt-out tools such as the Global Privacy Control browser setting that automatically signals your opt-out preferences.
Use data broker opt-out services
Many data brokers now offer opt-out mechanisms, though the process can be time-consuming. Consider using privacy services that handle multiple opt-out requests on your behalf.
Monitor your digital footprint
Regularly search for your name and personal information online. Set up Google Alerts for your name and key personal details to stay informed about new appearances of your information. In addition, monitor your credit reports for unauthorized changes, and use identity monitoring services that watch for your personal information appearing in data breaches or on the dark web.
Use reputable websites and tools
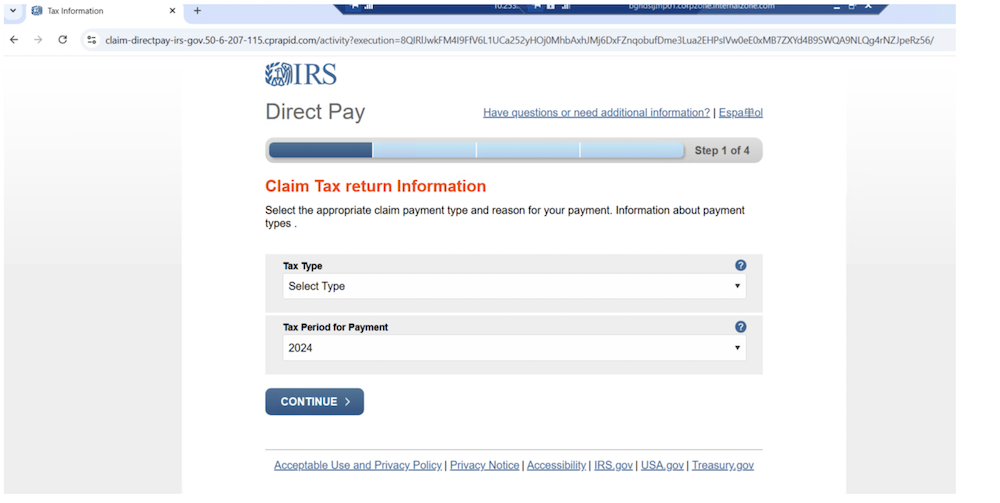
When sharing sensitive information online, verify that websites use https:// in the address bar and read privacy policies before providing personal details. Only use well-established, privacy-focused health, financial, and communication platforms with a strong track record of privacy and data protection.
Oversee your kids’ online activities
For children’s data, maintaining active oversight will help you stay ahead of potential problems in their online activities. Review the apps and websites they use, understand what information these platforms collect, and use parental controls to limit data sharing. Teach your children about privacy and the risks of sharing personal information online.
Everyday tips to maintain your privacy
Protecting your personal data doesn’t have to feel like a giant, technical project. Most privacy wins come from small, repeatable habits that you can do in minutes to shrink your digital footprint, and use the internet on your terms.
-
Limit what you share online: Review your social media privacy settings and share only what’s necessary to reduce your exposure to identity thieves and the potential for your data to be used against you.
-
Review your location permissions: For location data, regularly review and delete location history from your devices and disable location sharing for apps that don’t need it.
-
Crumble that cookie: You can turn cookies off in your browser settings. This step may prevent you from using certain websites, but it is a step toward privacy.
-
Stay private while browsing: Use a virtual private network from a reputable, reliable company to keep your online activities private, especially when using unsecured Wi-Fi in public places such as cafes, airports, and libraries.
Your personal information has value, so make sure you’re getting a fair return through services that respect your privacy.
FAQs about data privacy
What counts as personal data?
Personal data includes any information that can directly or indirectly identify you. This covers obvious details such as your name, email, and Social Security number, but also extends to IP addresses, device identifiers, location data, browsing history, and even inferences about your preferences or behavior.
How can I opt out of data sale and sharing?
On company websites, look for “Do Not Sell My Personal Information” or “Your Privacy Choices” links, usually found in the footer. You can also use the Global Privacy Control browser signal to send opt-out requests automatically. Services such as DeleteMe or manual removal requests can help you reclaim control of your information from data brokers and multiple platforms.
What should I do after a data breach?
First, change passwords for affected accounts and enable two-factor authentication. Next, monitor your credit reports and bank statements for unusual activity. If Social Security numbers or financial data were involved, place a credit freeze with all three major credit bureaus. Sign up for identity monitoring services if offered by the breached company. Be sure to document everything and report identity theft to the FTC if you notice fraudulent activity.
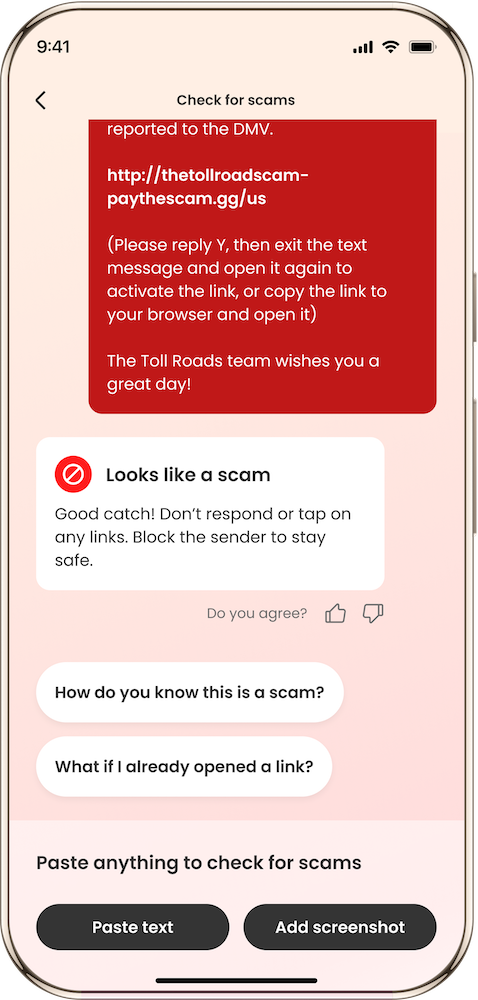
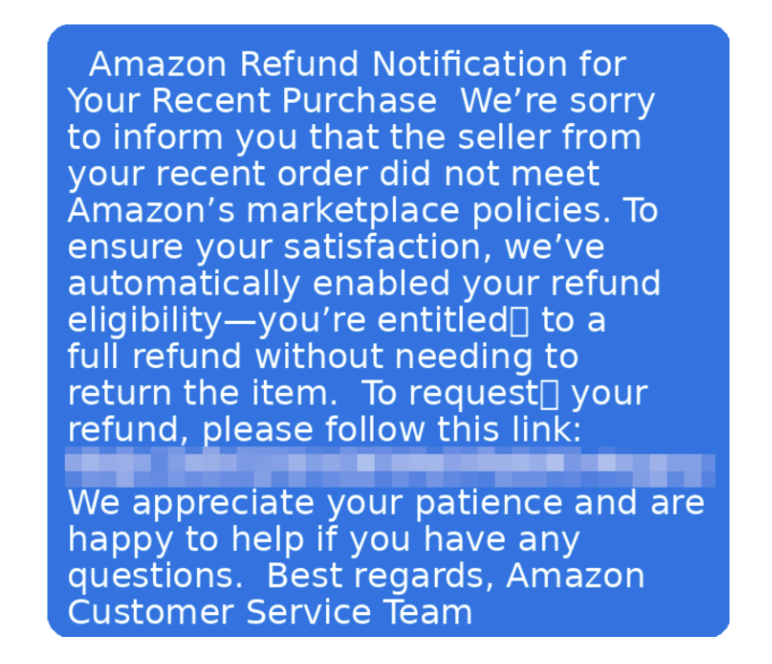
How do I spot dark consent patterns?
Watch for manipulative design tricks that push you toward sharing more data. Red flags include pre-checked boxes for marketing emails, making privacy-friendly options harder to find or understand, using confusing language that hides the intent, or making it much easier to accept all cookies than to customize your preferences. Legitimate consent should be freely given, specific, informed, and easily withdrawn.
What rights do I have over my personal data?
Depending on your location, you may have the right to know what data companies collect about you, request copies of your data, correct inaccurate information, delete your data, and opt out of its sale or use for targeted advertising. Some laws also give you the right to data portability and protect you from discrimination for exercising these rights. Check if your state has comprehensive privacy laws or if you’re covered by GDPR.
What essential resources can I read to stay informed?
To stay current with your privacy rights and the evolving legal landscape, bookmark these authoritative resources:
Final thoughts
Data Privacy Day serves as an important annual reminder, but your commitment to privacy and data protection shouldn’t end when January 28th passes. The digital threats we face continue to evolve throughout the year, making ongoing vigilance essential to protect your personal details.
Small, consistent habits can make a profound difference in your digital security. By regularly updating your passwords, enabling multi-factor authentication, reviewing privacy settings on your accounts, and staying informed about emerging threats, you create layers of protection that work together to safeguard your information.
Invest in McAfee+ identity protection, which includes proactive identity surveillance to monitor subscribers’ credit and personal information, as well as access to live fraud resolution agents who help subscribers work through the process of resolving identity theft issues.
The post Celebrate Data Privacy Day by Applying These Best Practices appeared first on McAfee Blog.









 trustmark, indicating that the site has been scanned and verified as secure by a trusted third party. This security seal indicates that the site will help protect you from
trustmark, indicating that the site has been scanned and verified as secure by a trusted third party. This security seal indicates that the site will help protect you from