Reading view
TCLBANKER Banking Trojan Targets Financial Platforms via WhatsApp and Outlook Worms

Worried about the nationwide Canvas data breach? Take these 6 steps now
Windows rivals to MacBook Neo are arriving - but can you handle their shortcomings?
Flying soon? American Airlines has new portable battery rules - what to know before you go
Fake Call History Apps Stole Payments From Users After 7.3 Million Play Store Downloads

'Dirty Frag' Linux flaw one-ups CopyFail with no patches and public root exploit

Meta U-turns on encryption push for Instagram as DMs go plaintext

How to Protect Yourself After the Canvas Education Data Breach + Fake Amazon Recall Texts

If you have ever checked your child’s grades online, submitted a college paper through a school portal, downloaded homework assignments, or received messages from a teacher through a classroom app, there is a good chance you have used Canvas, a nationwide learning management system that was just in a massive data breach.
This is exactly the moment McAfee+ Advanced was built for. With our built-in Scam Detector to flag risky links, QR codes, and deepfakes; Identity Monitoring that alerts you when your data appears where it shouldn’t; and Personal Data Cleanup that removes your information from the dark web and data brokers, McAfee+ Advanced is an all-in-one solution for protection after a data breach.
Now let’s get into what you need to know about this breach:
Who Is Behind the Canvas Breach?
The ransomware group ShinyHunters is claiming responsibility for the attack. The group alleges it stole roughly 275 million records tied to nearly 9,000 schools and educational institutions worldwide.
How Did the Canvas Cyberattack Happen?
Instructure, the company behind Canvas, confirmed a cyber incident affecting its cloud-hosted environment. The attackers later posted claims about the breach on their leak site, where ransomware groups pressure organizations into paying by threatening to release stolen data publicly.
What Information Was Stolen in the Canvas Breach?
The stolen data reportedly includes:
- Student names
- Teacher and staff names
- Email addresses
- Student IDs
- Course and enrollment information
- School-related records
ShinyHunters claims the breach exposed roughly 275 million records and more than 231 million unique email addresses.
How Could the Canvas Data Breach Impact Families and Students?
Even if financial information was not exposed, this kind of data can still be extremely valuable to scammers. Criminals can use real school names, real classes, teacher names, and student information to create highly convincing phishing emails, fake school alerts, scholarship scams, tuition scams, or password reset messages.
A scam message referencing your child’s actual school or assignment is much harder to spot as fake.
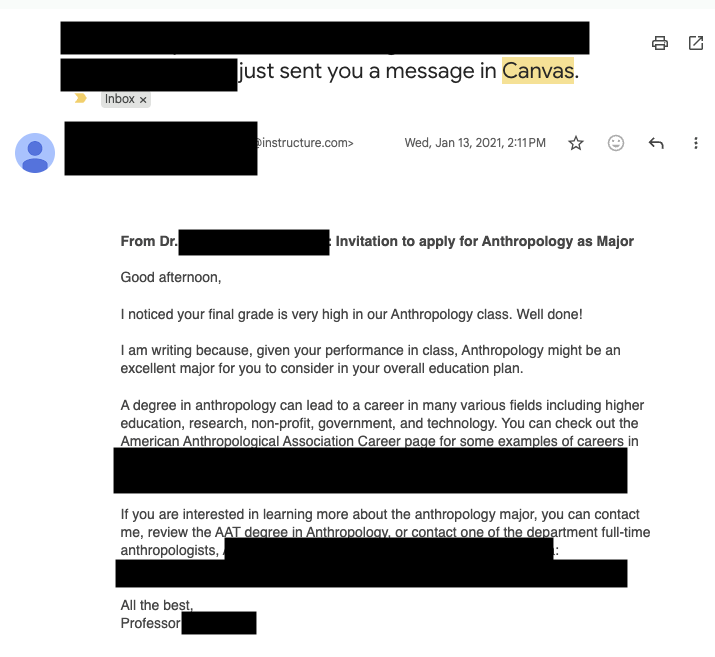
This is a real message from Canvas from a community college professor after yours truly took an anthropology class for fun during the pandemic. It’s full of links to apply for programs and reach out to professors. It has exact details about courses I’ve taken.
While this correspondence is real, it’s exactly the type of messaging that scammers could fake and replicate, replacing real links with fake “paid” opportunities to pursue degrees.
Now think of the millions of messages and specific scenarios scammers have access to, to create dubious and convincing scams. That’s why protecting yourself after a breach is key.
What To Do Right Now
Here are some actions you can take immediately ot protect yourself after this breach:
- Change you or your child’s Canvas password immediately, and update any other accounts where they reuse that password
- Turn on multi-factor authentication (2FA) on parent and student accounts wherever the school permits it — Instructure’s own post-incident guidance specifically called out enforcing MFA as a recommended precaution
- Ask your school what identity protection is being offered if sensitive data was involved
- Consider placing a credit freeze on your or your child’s file to block new accounts from being opened in their name
- Avoid clicking links in any messages that reference the breach, go directly to the official site instead
And that, my friends, is issue number one in this week’s This Week in Scams. Let’s get into what else is on our radar in cybersecurity and scam news.
Fake Amazon Recall Texts Are Targeting Shoppers
Your phone buzzes. It’s a text from an unknown number, but the message looks official.
“Dear Amazon Customer, we are writing to inform you that an item from your March 2026 order has been identified for recall.” There’s an order number. A link at the top of the message. A note about quality standards and a refund waiting for you.
It looks real. It has the Amazon logo, the branded formatting, even a reference to the “Amazon Customer Safety Team.” The only thing it doesn’t have? Any connection to Amazon at all.
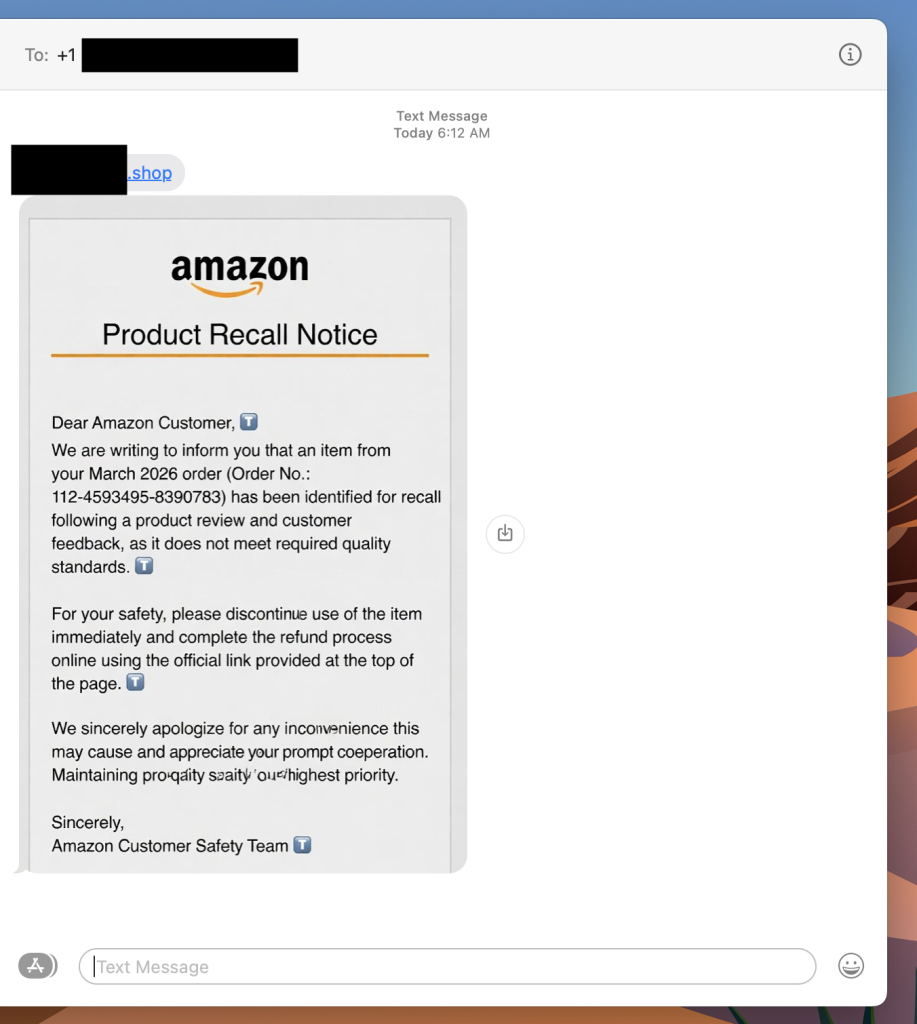
This is a fake Amazon recall scam, and it is making the rounds right now. The goal is to get you to click that link, which takes you to a site designed to harvest your login credentials, payment information, or both.
If you get a text like this, do not click the link. Go directly to amazon.com in your browser, log in, and check your orders and messages from there. Amazon does not initiate recall or refund processes through unsolicited texts with outside links.
What Is a Fake Amazon Recall Scam And How Does It Work?
A fake Amazon recall scam is a text message or email in which criminals impersonate Amazon to convince you that one of your recent orders has been flagged for a product recall. The message directs you to an external link leading to a phishing site designed to steal your Amazon credentials, credit card details, or personal information.
Red Flags To Watch For
- The text comes from an unknown number, not a short code or verified sender
- The link goes to a domain that is not amazon.com
- The message asks you to complete a refund through an external link
- Small typos or awkward phrasing appear in what looks like official communication
- The greeting says “Dear Amazon Customer” rather than your actual name
What To Do If You Get One
- Do not click the link
- Go to amazon.com directly and check your orders and account notifications
- Report the text to Amazon at stop-spoofing@amazon.com
- Block the number
Where McAfee Steps In (So You Don’t Have to Guess)
Scams today are layered. A fake email leads to stolen credentials. A breach leads to targeted phishing. And those follow-ups are getting harder to spot.
With McAfee+ Advanced, multiple layers work together so you’re not left figuring it out after the damage is done:
- Identity Monitoring alerts you if your personal info shows up where it should not, so you can act fast
- Personal Data Cleanup helps remove your information from sites selling it.
- Scam Detector flags suspicious texts, emails, links, QR codes, and even deepfake videos before you engage
- Safe Browsing helps block risky sites, even if you do accidentally click
- Device Security helps detect malicious apps or downloads
- Secure VPN keeps your data private, especially on public Wi-Fi
McAfee Safety Tips This Week
Our advice based on this week’s scams and stories:
- If your child’s school uses Canvas, update their password now and enable multi-factor authentication if available
- Consider a credit freeze for your child’s identity, especially if sensitive identifiers were part of the breach
- Never click links in unsolicited texts about refunds, recalls, or account issues — go directly to the official site instead
- Treat any message that references your recent orders or personal account details with extra skepticism, even if it looks legitimate
- Use Scam Detector to check suspicious links before engaging, and stay alert in the weeks and months after a breach, not just the first few days
And we’ll be back next week with more scams and cybersecurity news making headlines.
The post How to Protect Yourself After the Canvas Education Data Breach + Fake Amazon Recall Texts appeared first on McAfee Blog.
Quasar Linux RAT Steals Developer Credentials for Software Supply Chain Compromise

Hackers ate my homework: Educational SaaS Canvas down after cyberattack

Meta fights Ofcom over how many billions count as billions

One Missed Threat Per Week: What 25M Alerts Reveal About Low-Severity Risk

New Linux PamDOORa Backdoor Uses PAM Modules to Steal SSH Credentials

Meet Rassvet, Russia’s Answer to Starlink

Linux Kernel Dirty Frag LPE Exploit Enables Root Access Across Major Distributions

The Canvas Hack Is a New Kind of Ransomware Debacle

Canvas Breach Disrupts Schools & Colleges Nationwide
An ongoing data extortion attack targeting the widely-used education technology platform Canvas disrupted classes and coursework at school districts and universities across the United States today, after a cybercrime group defaced the service’s login page with a ransom demand that threatened to leak data from 275 million students and faculty across nearly 9,000 educational institutions.

A screenshot shared by a reader showing the extortion message that was shown on the Canvas login page today.
Canvas parent firm Instructure responded to today’s defacement attacks by disabling the platform, which is used by thousands of schools, universities and businesses to manage coursework and assignments, and to communicate with students.
Instructure acknowledged a data breach earlier this week, after the cybercrime group ShinyHunters claimed responsibility and said they would leak data on tens of millions of students and faculty unless paid a ransom. The stated deadline for payment was initially set at May 6, but it was later pushed back to May 12.
In a statement on May 6, Instructure said the investigation so far shows the stolen information includes “certain identifying information of users at affected institutions, such as names, email addresses, and student ID numbers, as well as as messages among users.” The company said it found no evidence the breached data included more sensitive information, such as passwords, dates of birth, government identifiers or financial information.
The May 6 update stated that Canvas was fully operational, and that Instructure was not seeing any ongoing unauthorized activity on their platform. “At this stage, we believe the incident has been contained,” Instructure wrote.
However, by mid-day on Thursday, May 7, students and faculty at dozens of schools and universities were flooding social media sites with comments saying that a ransom demand from ShinyHunters had replaced the usual Canvas login page. Instructure responded by pulling Canvas offline and replacing the portal with the message, “Canvas is currently undergoing scheduled maintenance. Check back soon.”
“We anticipate being up soon, and will provide updates as soon as possible,” reads the current message on Instructure’s status page.
While the data stolen by ShinyHunters may or may not contain particularly sensitive information (ShinyHunters claims it includes several billion private messages among students and teachers, as well as names, phone numbers and email addresses), this attack could hardly have come at a worse time for Instructure: Many of the affected schools and universities are in the middle of final exams, and a prolonged outage could be highly damaging for the company.
The extortion message that greeted countless Canvas users today advised the affected schools to negotiate their own ransom payments to prevent the publication of their data — regardless of whether Instructure decides to pay.
“ShinyHunters has breached Instructure (again),” the extortion message read. “Instead of contacting us to resolve it they ignored us and did some ‘security patches.'”
A source close to the investigation who was not authorized to speak to the press told KrebsOnSecurity that a number of universities have already approached the cybercrime group about paying. The same source also pointed out that the ShinyHunters data leak blog no longer lists Instructure among its current extortion victims, and that the samples of data stolen from Canvas customers were removed as well. Data extortion groups like ShinyHunters will typically only remove victims from their leak sites after receiving an extortion payment or after a victim agrees to negotiate.
Dipan Mann, founder and CEO of the security firm Cloudskope, slammed Instructure for referring to today’s outage as a “scheduled maintenance” event on its status page. Mann said Shiny Hunters first demonstrated they’d breached Instructure on May 1, prompting Instructure’s Chief Information Security Officer Steve Proud to declare the following day that the incident had been contained. But Mann said today’s attack is at least the third time in the past eight months that Instructure has been breached by ShinyHunters.
In a blog post today, Mann noted that in September 2025, ShinyHunters released thousands of internal University of Pennsylvania files — donor records, internal memos, and other confidential materials — through what the Daily Pennsylvanian and other outlets later determined was, in part, a Canvas/Instructure-mediated access path.
“Penn was the named victim,” Mann wrote. “Instructure was the mechanism. The incident was treated as a Penn-specific story by most of the national press and quietly handled by Instructure as a customer-specific matter. That framing was wrong then. It is dramatically more wrong in light of the May 2026 events, which now look like the planned escalation of an attack pattern that ShinyHunters had been working against Instructure’s environment for at least eight months prior. The September 2025 Penn breach was the proof of concept. The May 1, 2026 incident was the production run. The May 7, 2026 recompromise was ShinyHunters demonstrating publicly that the May 2 ‘containment’ did not happen.”
In February, a ShinyHunters spokesperson told The Daily Pennsylvanian that Penn failed to pay a $1 million ransom demand. On March 5, ShinyHunters published 461 megabytes worth of data stolen from Penn, including thousands of files such as donor records and internal memos.
ShinyHunters is a prolific and fluid cybercriminal group that specializes in data theft and extortion. They typically gain access to companies through voice phishing and social engineering attacks that often involve impersonating IT personnel or other trusted members of a targeted organization.
Last month, ShinyHunters relieved the home security giant ADT of personal information on 5.5 million customers. The extortion group told BleepingComputer they breached the company by compromising an employee’s Okta single sign-on account in a voice phishing attack that enabled access to ADT’s Salesforce instance. BleepingComputer says ShinyHunters recently has taken credit for a number of extortion attacks against high-profile organizations, including Medtronic, Rockstar Games, McGraw Hill, 7-Eleven and the cruise line operator Carnival.
The attack on Canvas customers is just one of several major cybercrime campaigns being launched by ShinyHunters at the moment, said Charles Carmakal, chief technology officer at the Google-owned Mandiant Consulting. Carmakal declined to comment specifically on the Canvas breach, but said “there are multiple concurrent and discrete ShinyHunters intrusion and extortion campaigns happening right now.”
Cloudskope’s Mann said what happens next depends largely on whether Instructure’s customers — the universities, K-12 districts, and education ministries paying for Canvas — choose to apply pressure or absorb the breach quietly.
“The history of education-vendor incidents suggests the path of least resistance is the second one,” he concluded.
Update, May 8, 11:05 a.m. ET: Instructure has published an incident update page that includes more information about the breach. Instructure said its Canvas portal is functioning normally again, and that the hackers exploited an issue related to Free-for-Teacher accounts.
“This is the same issue that led to the unauthorized access the prior week,” Instructure wrote. “As a result, we have made the difficult decision to temporarily shut down Free-for-Teacher accounts. These accounts have been a core part of our platform, and we’re committed to resolving the issues with these accounts.”
Instructure said affected organizations were notified on May 6.
“If your organization is affected, Instructure will contact your organization’s primary contacts directly,” the update states. “Please don’t rely on third-party lists or social media posts naming potentially affected organizations as those lists aren’t verified. Instructure will confirm validated information through direct outreach to all affected organizations.”