Two men have been arrested for allegedly stealing data from and extorting dozens of companies that used the cloud data storage company Snowflake, but a third suspect — a prolific hacker known as Kiberphant0m — remains at large and continues to publicly extort victims. However, this person’s identity may not remain a secret for long: A careful review of Kiberphant0m’s daily chats across multiple cybercrime personas suggests they are a U.S. Army soldier who is or was recently stationed in South Korea.
Kiberphant0m’s identities on cybercrime forums and on Telegram and Discord chat channels have been selling data stolen from customers of the cloud data storage company Snowflake. At the end of 2023, malicious hackers discovered that many companies had uploaded huge volumes of sensitive customer data to Snowflake accounts that were protected with nothing more than a username and password (no multi-factor authentication required).
After scouring darknet markets for stolen Snowflake account credentials, the hackers began raiding the data storage repositories for some of the world’s largest corporations. Among those was AT&T, which disclosed in July that cybercriminals had stolen personal information, phone and text message records for roughly 110 million people. Wired.com reported in July that AT&T paid a hacker $370,000 to delete stolen phone records.
On October 30, Canadian authorities arrested Alexander Moucka, a.k.a. Connor Riley Moucka of Kitchener, Ontario, on a provisional arrest warrant from the United States, which has since indicted him on 20 criminal counts connected to the Snowflake breaches. Another suspect in the Snowflake hacks, John Erin Binns, is an American who is currently incarcerated in Turkey.

A surveillance photo of Connor Riley Moucka, a.k.a. “Judische” and “Waifu,” dated Oct 21, 2024, 9 days before Moucka’s arrest. This image was included in an affidavit filed by an investigator with the Royal Canadian Mounted Police (RCMP).
Investigators say Moucka, who went by the handles Judische and Waifu, had tasked Kiberphant0m with selling data stolen from Snowflake customers who refused to pay a ransom to have their information deleted. Immediately after news broke of Moucka’s arrest, Kiberphant0m was clearly furious, and posted on the hacker community BreachForums what they claimed were the AT&T call logs for President-elect Donald J. Trump and for Vice President Kamala Harris.
“In the event you do not reach out to us @ATNT all presidential government call logs will be leaked,” Kiberphant0m threatened, signing their post with multiple “#FREEWAIFU” tags. “You don’t think we don’t have plans in the event of an arrest? Think again.”
On the same day, Kiberphant0m posted what they claimed was the “data schema” from the U.S. National Security Agency.
“This was obtained from the ATNT Snowflake hack which is why ATNT paid an extortion,” Kiberphant0m wrote in a thread on BreachForums. “Why would ATNT pay Waifu for the data when they wouldn’t even pay an extortion for over 20M+ SSNs?”
Also on Nov. 5, Kiberphant0m offered call logs stolen from Verizon’s push-to-talk (PTT) customers — mainly U.S. government agencies and emergency first responders. On Nov. 9, Kiberphant0m posted a sales thread on BreachForums offering a “SIM-swapping” service targeting Verizon PTT customers. In a SIM-swap, fraudsters use credentials that are phished or stolen from mobile phone company employees to divert a target’s phone calls and text messages to a device they control.
Kiberphant0m joined BreachForums in January 2024, but their public utterances on Discord and Telegram channels date back to at least early 2022. On their first post to BreachForums, Kiberphant0m said they could be reached at the Telegram handle @cyb3rph4nt0m.
A review of @cyb3rph4nt0m shows this user has posted more than 4,200 messages since January 2024. Many of these messages were attempts to recruit people who could be hired to deploy a piece of malware that enslaved host machines in an Internet of Things (IoT) botnet.
On BreachForums, Kiberphant0m has sold the source code to “Shi-Bot,” a custom Linux DDoS botnet based on the Mirai malware. Kiberphant0m had few sales threads on BreachForums prior to the Snowflake attacks becoming public in May, and many of those involved databases stolen from companies in South Korea.
On June 5, 2024, a Telegram user by the name “Buttholio” joined the fraud-focused Telegram channel “Comgirl” and claimed to be Kiberphant0m. Buttholio made the claim after being taunted as a nobody by another denizen of Comgirl, referring to their @cyb3rph4nt0m account on Telegram and the Kiberphant0m user on cybercrime forums.
“Type ‘kiberphant0m’ on google with the quotes,” Buttholio told another user. “I’ll wait. Go ahead. Over 50 articles. 15+ telecoms breached. I got the IMSI number to every single person that’s ever registered in Verizon, Tmobile, ATNT and Verifone.”
On Sept. 17, 2023, Buttholio posted in a Discord chat room dedicated to players of the video game Escape from Tarkov. “Come to Korea, servers there is pretty much no extract camper or cheater,” Buttholio advised.
In another message that same day in the gaming Discord, Buttholio told others they bought the game in the United States, but that they were playing it in Asia.
“USA is where the game was purchased from, server location is actual in game servers u play on. I am a u.s. soldier so i bought it in the states but got on rotation so i have to use asian servers,” they shared.
The account @Kiberphant0m was assigned the Telegram ID number 6953392511. A review of this ID at the cyber intelligence platform Flashpoint shows that on January 4, 2024 Kibertphant0m posted to the Telegram channel “Dstat,” which is populated by cybercriminals involved in launching distributed denial-of-service (DDoS) attacks and selling DDoS-for-hire services [Full disclosure: Flashpoint is currently an advertiser on this website].
Immediately after Kiberphant0m logged on to the Dstat channel, another user wrote “hi buttholio,” to which Kiberphant0m replied with an affirmative greeting “wsg,” or “what’s good.” On Nov. 1, Dstat’s website dstat[.]cc was seized as part of “Operation PowerOFF,” an international law enforcement action against DDoS services.
Flashpoint’s data shows that @kiberphant0m told a fellow member of Dstat on April 10, 2024 that their alternate Telegram username was “@reverseshell,” and did the same two weeks later in the Telegram chat The Jacuzzi. The Telegram ID for this account is 5408575119.
Way back on Nov. 15, 2022, @reverseshell told a fellow member of a Telegram channel called Cecilio Chat that they were a soldier in the U.S. Army. This user also shared the following image of someone pictured waist-down in military fatigues, with a camouflaged backpack at their feet:

Kiberphant0m’s apparent alias ReverseShell posted this image on a Telegram channel Cecilio Chat, on Nov. 15, 2022. Image: Flashpoint.
In September 2022, Reverseshell was embroiled in an argument with another member who had threatened to launch a DDoS attack against Reverseshell’s Internet address. After the promised attack materialized, Reverseshell responded, “Yall just hit military base contracted wifi.”
In a chat from October 2022, Reverseshell was bragging about the speed of the servers they were using, and in reply to another member’s question said that they were accessing the Internet via South Korea Telecom.
Telegram chat logs archived by Flashpoint show that on Aug. 23, 2022, Reverseshell bragged they’d been using automated tools to find valid logins for Internet servers that they resold to others.
“I’ve hit US gov servers with default creds,” Reverseshell wrote, referring to systems with easy-to-guess usernames and/or passwords. “Telecom control servers, machinery shops, Russian ISP servers, etc. I sold a few big companies for like $2-3k a piece. You can sell the access when you get a big SSH into corporation.”
On July 29, 2023, Reverseshell posted a screenshot of a login page for a major U.S. defense contractor, claiming they had an aerospace company’s credentials to sell.
Flashpoint finds the Telegram ID 5408575119 has used several aliases since 2022, including Reverseshell and Proman557.
A search on the username Proman557 at the cyber intelligence platform Intel 471 shows that a hacker by the name “Proman554” registered on Hackforums in September 2022, and in messages to other users Proman554 said they can be reached at the Telegram account Buttholio.
Intel 471 also finds the Proman557 moniker is one of many used by a person on the Russian-language hacking forum Exploit in 2022 who sold a variety of Linux-based botnet malware.
Proman557 was eventually banned — allegedly for scamming a fellow member out of $350 — and the Exploit moderator warned forum users that Proman557 had previously registered under several other nicknames, including an account called “Vars_Secc.”
Vars_Secc’s thousands of comments on Telegram over two years show this user divided their time between online gaming, maintaining a DDoS botnet, and promoting the sale or renting of their botnets to other users.
“I use ddos for many things not just to be a skid,” Vars_Secc pronounced. “Why do you think I haven’t sold my net?” They then proceeded to list the most useful qualities of their botnet:
-I use it to hit off servers that ban me or piss me off
-I used to ddos certain games to get my items back since the data reverts to when u joined
-I use it for server side desync RCE vulnerabilities
-I use it to sometimes ransom
-I use it when bored as a source of entertainment
Flashpoint shows that in June 2023, Vars_Secc responded to taunting from a fellow member in the Telegram channel SecHub who had threatened to reveal their personal details to the federal government for a reward.
“Man I’ve been doing this shit for 4 years,” Vars_Secc replied nonchalantly. “I highly doubt the government is going to pay millions of dollars for data on some random dude operating a pointless ddos botnet and finding a few vulnerabilities here and there.”
For several months in 2023, Vars_Secc also was an active member of the Russian-language crime forum XSS, where they sold access to a U.S. government server for $2,000. However, Vars_Secc would be banned from XSS after attempting to sell access to the Russian telecommunications giant Rostelecom. [In this, Vars_Secc violated the Number One Rule for operating on a Russia-based crime forum: Never offer to hack or sell data stolen from Russian entities or citizens].
On June 20, 2023, Vars_Secc posted a sales thread on the cybercrime forum Ramp 2.0 titled, “Selling US Gov Financial Access.”
“Server within the network, possible to pivot,” Vars_Secc’s sparse sales post read. “Has 3-5 subroutes connected to it. Price $1,250. Telegram: Vars_Secc.”
Vars_Secc also used Ramp in June 2023 to sell access to a “Vietnam government Internet Network Information Center.”
“Selling access server allocated within the network,” Vars_Secc wrote. “Has some data on it. $500.”
The Vars_Secc identity claimed on Telegram in May 2023 that they made money by submitting reports about software flaws to HackerOne, a company that helps technology firms field reports about security vulnerabilities in their products and services. Specifically, Vars_Secc said they had earned financial rewards or “bug bounties” from reddit.com, the U.S. Department of Defense, and Coinbase, among 30 others.
“I make money off bug bounties, it’s quite simple,” Vars_Secc said when asked what they do for a living. “That’s why I have over 30 bug bounty reports on HackerOne.”
A month before that, Vars_Secc said they’d found a vulnerability in reddit.com.
“I poisoned Reddit’s cache,” they explained. “I’m going to exploit it further, then report it to reddit.”
KrebsOnSecurity sought comment from HackerOne, which said it would investigate the claims. This story will be updated if they respond.
The Vars_Secc telegram handle also has claimed ownership of the BreachForums member “Boxfan,” and Intel 471 shows Boxfan’s early posts on the forum had the Vars_Secc Telegram account in their signature. In their most recent post to BreachForums in January 2024, Boxfan disclosed a security vulnerability they found in Naver, the most popular search engine in South Korea (according to statista.com). Boxfan’s comments suggest they have strong negative feelings about South Korean culture.
“Have fun exploiting this vulnerability,” Boxfan wrote on BreachForums, after pasting a long string of computer code intended to demonstrate the flaw. “Fuck you South Korea and your discriminatory views. Nobody likes ur shit kpop you evil fucks. Whoever can dump this DB [database] congrats. I don’t feel like doing it so I’ll post it to the forum.”
The many identities tied to Kiberphant0m strongly suggest they are or until recently were a U.S. Army soldier stationed in South Korea. Kiberphant0m’s alter egos never mentioned their military rank, regiment, or specialization.
However, it is likely that Kiberphant0m’s facility with computers and networking was noticed by the Army. According to the U.S. Army’s website, the bulk of its forces in South Korea reside within the Eighth Army, which has a dedicated cyber operations unit focused on defending against cyber threats.
On April 1, 2023, Vars_Secc posted to a public Telegram chat channel a screenshot of the National Security Agency’s website. The image indicated the visitor had just applied for some type of job at the NSA.

A screenshot posted by Vars_Secc on Telegram on April 1, 2023, suggesting they just applied for a job at the National Security Agency.
The NSA has not yet responded to requests for comment.
Reached via Telegram, Kiberphant0m acknowledged that KrebsOnSecurity managed to unearth their old handles.
“I see you found the IP behind it no way,” Kiberphant0m replied. “I see you managed to find my old aliases LOL.”
Kiberphant0m denied being in the U.S. Army or ever being in South Korea, and said all of that was a lengthy ruse designed to create a fictitious persona. “Epic opsec troll,” they claimed.
Asked if they were at all concerned about getting busted, Kiberphant0m called that an impossibility.
“I literally can’t get caught,” Kiberphant0m said, declining an invitation to explain why. “I don’t even live in the USA Mr. Krebs.”
Below is a mind map that hopefully helps illustrate some of the connections between and among Kiberphant0m’s apparent alter egos.
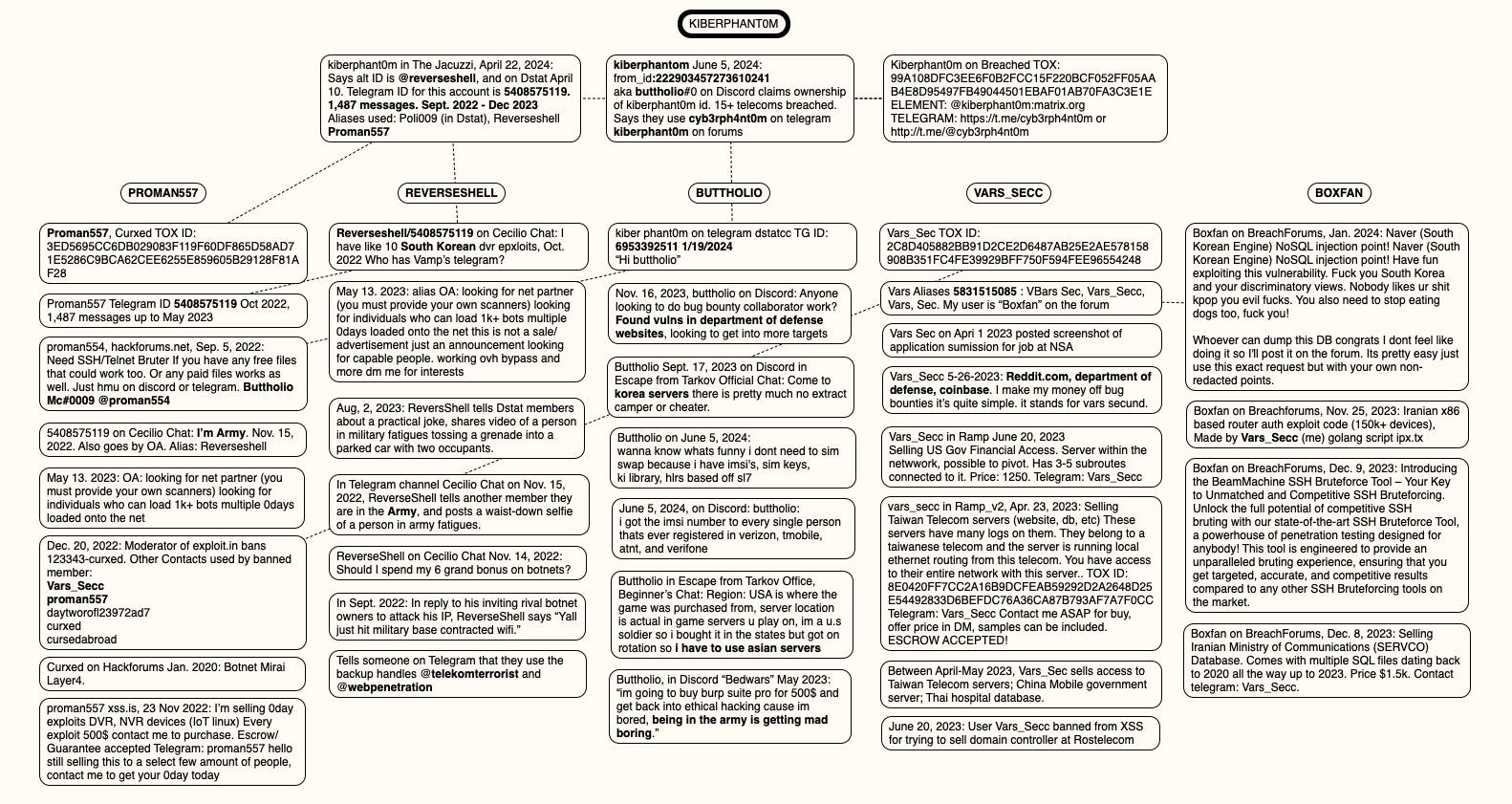
A mind map of the connections between and among the identities apparently used by Kiberphant0m. Click to enlarge.
KrebsOnSecurity would like to extend a special note of thanks to the New York City based security intelligence firm Unit 221B for their assistance in helping to piece together key elements of Kiberphant0m’s different identities.