
Hackers are not created equal, nor do they have the same purpose. Some hackers are paid to scrutinize security systems, find loopholes, fix weaknesses, and ultimately protect organizations and people. Others exploit those same gaps for profit, power, or disruption. What separates hackers isn’t just skill level or tactics; it’s intent.
The purpose behind an attack changes everything about how hackers shape their tactics and how the hacking process unfolds: who is targeted, which methods and tools are used, how patient the attacker is, and the kind of damage they want to cause.
The primary motivations behind these cyberattacks fall into several categories, from financial gain to recognition, and sometimes even coercion. Each driver creates different risk scenarios for your digital life, from your home banking sessions to your workplace communications. Understanding a hacker’s motivations will enable you to better protect yourself and recognize potential threats in both your personal and professional life.
In this article, we’ll look at the main types of hackers you might encounter, the core motivations and mindset that drive these cyberattacks, and finally, how you can protect yourself against these attacks.
From its beginnings as an intellectual exploration in universities, hacking was driven by curiosity, learning, and the thrill of solving complex problems. Today, it has become industrialized with organized criminal groups and state-sponsored actors entering the scene.
Modern hacking has seen the emergence of advanced persistent threats and nation-state campaigns targeting critical infrastructure and combining traditional techniques with artificial intelligence. To better understand the types of hackers, here is a window into what they do and why:
These are the good guys, typically computer security experts who specialize in penetration testing and other methodologies to ensure that a company’s information systems are secure. These IT security professionals rely on a constantly evolving arsenal of technology to battle hackers.
These are the bad guys, who are typically referred to as just plain hackers. The term is often used specifically for hackers who break into networks or computers, or create computer viruses. Unfortunately, black hat hackers continue to technologically outpace white hats, often finding the path of least resistance, whether due to human error or laziness, or with a new type of attack. Hacking purists often use the term “crackers” to refer to black hat hackers, whose motivation is generally to get paid.
This is a derogatory term for black hat hackers who use borrowed programs to attack networks and deface websites in an attempt to make names for themselves. Script kiddies, sometimes called script kitties, might be beginners, but don’t be fooled by their newbie status. With the right tools and right targets, they can wreak as much havoc as a seasoned hacker.
Some hacker activists are motivated by politics or religion, while others aim to expose wrongdoing or exact revenge. Activists typically target government agencies, public services, and organizations involved in controversial issues related to defense, elections, wars, finance, or social movements. They also attack high-profile individuals, such as executives, public figures, journalists, and activists.
State-sponsored hackers have limitless time and funding to target civilians, corporations, other governments, or even prominent citizens connected to a larger objective. Their motivations are driven by their government’s strategic goals: gathering intelligence, stealing sensitive research or intellectual property, influencing public perception, or disrupting critical infrastructure. Because they are playing a long game, state-sponsored hackers are stealthy and persistent, quietly embedding themselves in systems, mapping networks, and waiting for the right moment to act.
Corporations hire hackers to infiltrate their competitors and steal trade secrets, including product designs, source code, pricing plans, customer lists, legal documents, and merger or acquisition strategies. They may hack from the outside or gain employment in order to act as a mole, impersonating recruiters, partners, or vendors to get insiders to share access. They also take advantage of weak internal controls, such as excessive permissions, unsecured file-sharing links, or poor offboarding practices. Spy hackers may use similar tactics as hacktivists or state-sponsored espionage on a smaller scale: stealthy entry, careful privilege escalation, and long-term persistence to avoid triggering alarms. The stolen data is often not leaked publicly but delivered directly to the client and used behind the scenes.
These hackers, generally motivated by religious or political beliefs, attempt to create terror, chaos, and real-world harm by disrupting critical infrastructures such as power grids, water systems, transportation networks, hospitals, emergency services, and government operations. They combine cyber operations with propaganda campaigns and physical attacks on the systems people rely on to live safely to create turmoil far beyond the screen.
Cybercriminals aren’t just faceless entities; they’re driven by specific goals that shape their tactics and targets. Understanding their motivations empowers you to recognize potential threats and better protect yourself, your family, and colleagues.
Money remains the most common motivator. These profit-driven attacks directly impact your personal finances through methods such as ransomware, credit card fraud, and identity theft. In your home, financially motivated hackers target your banking apps, shopping accounts, and personal devices to steal payment information or hold your data hostage. In the workplace, they focus on payroll systems, customer databases, and business banking credentials.
Ideologically driven hackers, called hacktivists, pursue political or social causes through cyber means. These attacks can disrupt services that you rely on daily, from public utilities to private organizations that provide essential services or take public stances on divisive issues. Your best defense involves staying informed about potential disruptions and maintaining backup communication methods for essential services.
Many hackers begin their journey with genuine curiosity about how systems work. They might probe your home network, test website security, or experiment with app vulnerabilities, not necessarily for malicious purposes, but their activities can still expose your data or disrupt services. In professional environments, these individuals might target systems or databases simply to see if they can gain access.
Some hackers seek fame, respect within hacker communities, or professional advancement rather than immediate financial benefit. They often target high-profile individuals, popular websites, or well-known companies to maximize the visibility for their exploits. If you have a significant social media following, your accounts could become targets for these attacks. They might also focus on defacing company or government websites, or leaking non-sensitive but embarrassing information.
Nation-state and corporate espionage are some of the most sophisticated threats in cyberspace, making it a top national security concern for both government and private sector. These operations compromise daily services and infrastructure such as internet service providers, email platforms, or cloud storage services to gather intelligence such as intellectual property, customer lists, or strategic planning documents.
Some hackers use cyber capabilities to intimidate or coerce victims into specific actions. In the FBI’s Internet Crime Complaint Center report for 2024, extortion was the 2nd top cybercrime by number of complaints, demonstrating the growing prevalence of coercion-based attacks. Coercion might involve compromising personal photos, social media accounts, or private communications to demand payment or behavioral changes. Workplace coercion could target executives with embarrassing information or threaten to leak sensitive business data unless demands are met.
Many real-world attacks combine multiple motivations—a financially driven criminal might also seek recognition within hacker communities, or an ideological hacker might generate revenue through ransomware. The contrast between ethical hacker motivations and malicious ones often lies in the permission, legality, and intent. Understanding why people become hackers helps you recognize that not all hacking activity is inherently malicious, although all unauthorized access ultimately poses risks to your security and privacy.
Understanding the psychology behind cyberattacks gives you a powerful advantage in protecting yourself. When you know what drives hackers, you can better spot their tactics and stay one step ahead.
Many hackers operate with the goal of achieving high reward for perceived low risk. This risk-reward imbalance motivates attackers because they can potentially access valuable personal or financial information while remaining physically distant from their victims. This means hackers often target easy opportunities, such as when you click on suspicious links or download questionable attachments, to gain access with minimal effort. For instance, a hacker would rather send 10,000 phishing emails hoping for a few bites than attempt one complex, risky attack.
Hackers exploit well-known psychological shortcuts your brain takes. They understand that you’re more likely to trust familiar-looking emails, act quickly under pressure, or follow authority figures without question. These aren’t weaknesses, these are normal human responses that attackers deliberately manipulate. For example, urgent messages claiming your account will be closed create an artificial time pressure, making you more likely to click without thinking.
Many successful cyberattacks leverage the human tendency to follow what others are doing. Hackers create fake social media profiles, forge customer reviews, or impersonate colleagues to make their requests seem legitimate and widely accepted. In ransomware attacks targeting businesses, criminals often research company hierarchies and communication styles to make their demands appear to come from trusted sources within the organization.
Modern hacking has elements that make it feel like a game to perpetrators. Some online forums award points for successful attacks, creating competition and recognition among criminals. This helps explain why some hackers target individuals rather than large corporations, as every successful phishing attempt becomes a score, and why attacks continue to evolve.
Hackers don’t all use the same tricks, but most successful attacks rely on a familiar toolkit of methods that exploit common technical gaps and human habits. Recognizing these common techniques will help you avoid danger earlier on.
Your strongest defense against hacking combines technical safeguards, security awareness, and some consistent habits that shut down the most common paths attackers use. Here’s how to put those defenses in place and make your digital life a much harder target.
Now that you understand hackers’ motivations and psychological drivers, you can flip the script and turn it to your advantage. Instead of being the target, become the informed defender who recognizes manipulation tactics and responds thoughtfully rather than reactively. This knowledge empowers you to spot potential threats earlier, choose stronger protective measures, and navigate the digital world with greater confidence.
When someone pressures you to act immediately, that’s your cue to slow down and verify the request. Question familiar-looking messages, even if they look official. Check the sender’s address and contact the company through official channels. Trust your instincts and investigate before acting. Stay curious and keep learning from reputable cybersecurity resources that publish current research and threat intelligence. Share these tips with your family members and friends, especially those who might be less technologically savvy.
McAfee+ includes proactive identity surveillance to monitor subscribers’ credit and personal information, as well as access to live fraud resolution agents who can help subscribers work through the process of resolving identity theft issues.
The post 7 Types of Hacker Motivations appeared first on McAfee Blog.

The ability to connect wirelessly is indispensable in our lives today. Wireless internet is available in our homes, offices, cafes, restaurants, parks, hotels, airports, cars, and even airplanes. The mobility factor allows us to work anytime, anywhere, on numerous devices. “Being connected” is at an all-time high.
Wireless internet is amazing and convenient. Sadly, unsecured, unprotected wireless is everywhere. When a device connects to unprotected Wi-Fi, all the data stored on that device becomes accessible to a hacker using the proper sniffing tools.
It is, however, possible to protect your Wi-Fi from being hacked. In this article, we’ll walk you through some practical steps to stay protected when you connect, from recognizing dangerous networks to securing your home Wi-Fi. We’ll also show you what to do if you think you’ve been targeted.
Wireless network attacks happen when cybercriminals target your Wi-Fi connection to steal your personal information. It it’s equivalent to digital eavesdropping, where attackers exploit weaknesses in your wireless connection to intercept all the information you send and receive online.
Criminals can intercept your login credentials as you type them, redirect you to legitimate-looking but fake websites, or even impersonate you online using stolen information. The goal is often wireless identity theft, that is, using your compromised data for financial fraud or other malicious purposes.
The risks of unprotected Wi-Fi are particularly high because many wireless networks lack proper security measures. When you connect to an unsecured network, your data travels in a way that skilled attackers can capture and decode. This puts your banking information, social media accounts, work credentials, and personal communications at risk.
Common wireless attacks include creating fake hotspots that mimic legitimate networks, known as evil twins, intercepting data on public Wi-Fi, and using specialized software to crack network passwords.
Cybercriminals usually circumvent wireless network security in several ways, including:
Once scammers gain access to your home or an unsecured public Wi-Fi network, they can launch several types of wireless attacks that directly put your personal information and financial security at risk.
One of the most common dangers is credential theft, where attackers intercept your login information as it travels over unsecured networks. When you check your email, log into social media, or access work accounts on a compromised Wi-Fi network, cybercriminals can capture your usernames and passwords. This wireless identity theft often leads to unauthorized access to your bank accounts, credit cards, and personal profiles.
In session hijacking, attackers take over your current online activities on public Wi-Fi, then impersonate you on websites and services you’re logged into. This tactic is called the man-in-the-middle attack. They might apply for credit cards in your name, make purchases, or even commit crimes while pretending to be you. Through traffic sniffing, they can monitor all data flowing through the compromised networks, capturing everything from personal messages to financial information.
Cybercriminals will also reroute your internet traffic to malicious websites that look similar to legitimate ones. You think you’re logging into your real bank website, but you’re actually entering your credentials into a scammer’s fake site. This technique, known as DNS poisoning, makes it nearly impossible to detect the deception until it’s too late.
The attackers will push malicious software directly onto your devices, enabling them to log every keystroke you make, steal stored passwords, access your files, and even quietly activate your camera or microphone without your knowledge.
Hackers can monitor not only your device but all connected devices on your network. That means they can access your entire family’s browsing habits, private messages, stored photos and documents, and online activities, giving them detailed personal information for their identity theft schemes.
These attacks directly affect your daily activities, from online banking to e-commerce shopping to working from home. Even simple tasks, such as checking social media, can result in identity theft when conducted over compromised networks.
You don’t have to avoid public Wi-Fi entirely. By being aware of these risks and taking appropriate precautions, you can significantly reduce your exposure to wireless identity theft. The protective measures we’ll explore in the following sections will show you how to recognize dangerous networks, browse safely, and maintain your privacy even when using public connections.
If you suspect your Wi-Fi network has been compromised, don’t panic. Recognizing the warning signs early and taking decisive action can protect your identity and restore your network security.
The most common indicators of a compromised network include unexpected slowdowns in your internet speed, unfamiliar devices appearing on your network, and settings that have changed without your knowledge. You might also notice unusual data usage patterns, your router admin password no longer working, or being redirected to suspicious websites when browsing. When you detect these signs, take quick action.
To guard your network or device from hacking attempts, take action today by updating your router’s firmware and passwords, reviewing and removing unnecessary saved networks from your devices, and enabling multi-factor authentication on all your important accounts. These small, but consistent steps will deliver tangible benefits to your daily digital activities.
For better security, subscribe to an identity theft protection service such as McAfee+, which offers proactive identity surveillance, lost wallet protection, and alerts when suspicious activity is detected on your accounts. All things considered, the investment in these security measures is minimal compared to the peace of mind they provide.
The post Verify Secure Wireless Networks to Prevent Identity Theft appeared first on McAfee Blog.

It’s no longer possible to deny that your life in the physical world and your digital life are one and the same. Coming to terms with this reality will help you make better decisions in many aspects of your life.
The same identity you use at work, at home, and with friends also exists in apps, inboxes, accounts, devices, and databases, whether you actively post online or prefer to stay quiet. Every purchase, login, location ping, and message leaves a trail. And that trail shapes what people, companies, and scammers can learn about you, how they can reach you, and what they might try to take.
That’s why digital security isn’t just an IT or a “tech person” problem. It’s a daily life skill. When you understand how your digital life works, what information you’re sharing, where it’s stored, and how it can be misused, you make better decisions. This guide is designed to help you build that awareness and translate it into practical habits: protecting your data, securing your accounts, and staying in control of your privacy in a world that’s always connected.
Being digitally secure doesn’t mean hiding from the internet or using complicated tools you don’t understand. It means having intentional control over your digital life to reduce risks while still being able to live, work, and communicate online safely. A digitally secure person focuses on four interconnected areas:
Your personal data is the foundation of your digital identity. Protecting it includes limiting how much data you share, understanding where it’s stored, and reducing how easily it can be collected, sold, or stolen. At its heart, personal information falls into two critical categories that require different levels of protection:
Account security ensures that only you can access them. Strong, unique passwords, multi-factor authentication, and secure recovery options prevent criminals from hijacking your email, banking, cloud storage, social media, and other online accounts, often the gateway to everything else in your digital life.
Privacy control means setting boundaries and deciding who can see what about you, and under what circumstances. This includes managing social media visibility, app permissions, browser tracking, and third-party access to your data.
Digital security is an ongoing effort as threats evolve, platforms change their policies, and new technologies introduce new risks. Staying digitally secure requires periodic check-ins, learning to recognize scams and manipulation, and adjusting your habits as the digital landscape changes.
Your personal information faces exposure risks through multiple channels during routine digital activities, often without your explicit knowledge.
Implementing comprehensive personal data protection requires a systematic approach that addresses the common exposure points. These practical steps provide layers of security that work together to minimize your exposure to identity theft and fraud.
Start by conducting a thorough audit of your online accounts and subscriptions to identify where you have unnecessarily shared more data than needed. Remove or minimize details that aren’t essential for the service to function. Moving forward, provide only the minimum required information to new accounts and avoid linking them across different platforms unless necessary.
Be particularly cautious with loyalty programs, surveys, and promotional offers that ask for extensive personal information, as they may share it with third parties. Read privacy policies carefully, focusing on sections that describe data sharing, retention periods, and your rights regarding your personal information.
If possible, consider using separate email addresses for different accounts to limit cross-platform tracking and reduce the impact if one account is compromised. Create dedicated email addresses for shopping, social media, newsletters, and important accounts like banking and healthcare.
Privacy protection requires regular attention to your account settings across all platforms and services you use. Social media platforms frequently update their privacy policies and settings, often defaulting to less private configurations that allow them to collect and share your data. For this reason, it is a good idea to review your privacy settings at least quarterly. Limit who can see your posts, contact information, and friend lists. Disable location tracking, facial recognition, and advertising customization features that rely on your personal data. Turn off automatic photo tagging and prevent search engines from indexing your profile.
On Google accounts, visit your Activity Controls and disable Web & App Activity, Location History, and YouTube History to stop this data from being saved. You can even opt out of ad personalization entirely if desired by adjusting Google Ad Settings. If you are more tech savvy, Google Takeout allows you to export and review what data Google has collected about you.
For Apple ID accounts, you can navigate to System Preferences on Mac or Settings on iOS devices to disable location-based Apple ads, limit app tracking, and review which apps have access to your contacts, photos, and other personal data.
Meanwhile, Amazon accounts store extensive purchase history, voice recordings from Alexa devices, and browsing behavior. Review your privacy settings to limit data sharing with third parties, delete voice recordings, and manage your advertising preferences.
Regularly audit the permissions you’ve granted to installed applications. Many apps request far more permissions to your location, contacts, camera, and microphone even though they don’t need them. Cancel these unnecessary permissions, and be particularly cautious about granting access to sensitive data.
Create passwords that actually protect you; they should be long and complex enough that even sophisticated attacks can’t easily break them. Combine uppercase letters, lowercase letters, numbers, and special characters to make it harder for attackers to crack.
Aside from passwords, enable multi-factor authentication (MFA) on your most critical accounts: banking and financial services, email, cloud storage, social media, work, and healthcare. Use authenticator apps such as Google Authenticator, Microsoft Authenticator, or Authy rather than SMS-based authentication when possible, as text messages can be intercepted through SIM swapping attacks. When setting up MFA, ensure you save backup codes in a secure location and register multiple devices when possible to keep you from being locked out of your accounts if your primary authentication device is lost, stolen, or damaged.
Alternatively, many services now offer passkeys which use cryptographic keys stored on your device, providing stronger security than passwords while being more convenient to use. Consider adopting passkeys for accounts that support them, particularly for your most sensitive accounts.
Device encryption protects your personal information if your smartphone, tablet, or laptop is lost, stolen, or accessed without authorization. Modern devices typically offer built-in encryption options that are easy to enable and don’t noticeably impact performance.
You can implement automatic backup systems such as secure cloud storage services, and ensure backup data is protected. iOS users can utilize encrypted iCloud backups, while Android users should enable Google backup with encryption. Regularly test your backup systems to ensure they’re working correctly and that you can successfully restore your data when needed.
Identify major data brokers that likely have your information and look for their privacy policy or opt-out procedures, which often involves submitting a request with your personal information and waiting for confirmation that your data has been removed.
In addition, review your subscriptions and memberships to identify services you no longer use. Request account deletion rather than simply closing accounts, as many companies retain data from closed accounts. When requesting deletion, ask specifically for all personal data to be removed from their systems, including backups and archives.
Keep records of your opt-out and deletion requests, and follow up if you don’t receive confirmation within the stated timeframe. In the United States, key data broker companies include Acxiom, LexisNexis, Experian, Equifax, TransUnion, Whitepages, Spokeo, BeenVerified, and PeopleFinder. Visit each company’s website.
Connect only to trusted, secure networks to reduce the risk of your data being intercepted by attackers lurking behind unsecured or fake Wi-Fi connections. Avoid logging into sensitive accounts on public networks in coffee shops, airports, or hotels, and use encrypted connections such as HTTPS or a virtual private network to hide your IP address and block third parties from monitoring your online activities.
Rather than using a free VPN service that often collects and sells your data to generate revenue, it is better to choose a premium, reputable VPN service that doesn’t log your browsing activities and offers servers in multiple locations.
Cyber threats evolve constantly, privacy policies change, and new services collect different types of personal information, making personal data protection an ongoing process rather than a one-time task. Here are measures to help regularly maintain your personal data protection:
By implementing these systematic approaches and maintaining regular attention to your privacy settings and data sharing practices, you significantly reduce your risk of identity theft and fraud while maintaining greater control over your digital presence and personal information.
You don’t need to dramatically overhaul your entire digital security in one day, but you can start making meaningful improvements right now. Taking action today, even small steps, builds the foundation for stronger personal data protection and peace of mind in your digital life. Choose one critical account, update its password, enable multi-factor authentication, and you’ll already be significantly more secure than you were this morning. Your future self will thank you for taking these proactive steps to protect what matters most to you.
Every step you take toward better privacy protection strengthens your overall digital security and reduces your risk of becoming a victim of scams, identity theft, or unwanted surveillance. You’ve already taken the first step by learning about digital security risks and solutions. Now it’s time to put that knowledge into action with practical steps that fit seamlessly into your digital routine.
The post What Does It Take To Be Digitally Secure? appeared first on McAfee Blog.

The holidays are just around the corner and amid the hustle and bustle, many of us will fire up our devices to go online, order gifts, plan travel, and spread cheer. But while we’re getting festive, the cybercriminals are getting ready to take advantage of the influx of your good cheer to spread scams and malware.
With online shopping expected to grow by 7.9% year-on-year in the U.S. alone in 2025, according to Mastercard, and more people than ever using social media and mobile devices to connect, the cybercriminals have a lot of opportunities to spoil our fun. Using multiple devices provides the bad guys with more ways to access your valuable “digital assets,” such as personal information and files, especially if the devices are under-protected.
In this guide, let’s look into the 12 most common cybercrimes and scams of Christmas, and what you can do to keep your money, information, and holiday spirit safe.
The festive atmosphere, continued increase in online shopping activity, and charitable spirit that define the holidays create perfect conditions for scammers to exploit your generosity and urgency.
Not surprisingly, digital criminals become more active and professional during this period, driven even more by the increasing power of artificial intelligence. A new McAfee holiday shopping report revealed that 86% of consumers surveyed receive a daily average of 11 shopping-related text or email messages that seem suspicious. This includes 3 scam texts, 5 emails, and 3 social media messages. Meanwhile, 22% admit they have been scammed during a holiday season in the past.
Their scams succeed because they exploit the psychological and behavioral patterns that are rife during the holidays. The excitement and time pressure of holiday shopping often prevail over our usual caution, while the emotional aspects of gift-giving and charitable donations can be exploited and move us to be more generous. Meanwhile, scammers understand that you’re more likely to make quick purchasing decisions when the fear of missing out on limited-time offers overtakes your judgment or when you’re rushing to find the perfect gift before it’s too late.
Overall, the frenzied seasonal themes create an environment where criminals can misuse the urgency of their fake offers and cloud our judgment, making fraudulent emails and websites appear more legitimate, while you’re already operating under the stress of holiday deadlines and budget concerns. After all, holiday promotions and charity appeals are expected during this time of year.
Now that you understand the psychology behind the scams, it’s time to become more aware of the common scams that cybercriminals run during the holiday season.
As you head online this holiday season, stay on guard and stay aware of scammers’ attempts to steal your money and your information. Familiarize yourself with the “12 Scams of Christmas” to ensure a safe and happy holiday season:
Many of us use social media sites to connect with family, friends, and co-workers over the holidays, and the cybercriminals know that this is a good place to catch you off guard because we’re all “friends,” right? Here are some ways that criminals will use these channels to obtain shoppers gift money, identity or other personal information:
As the popularity of smartphone apps has grown, so have the chances of you downloading a malicious application that steals your information or sends premium-rate text messages without your knowledge. Apps ask for more permissions than they need, such as access to your contacts or location.
If you unwrap a new smartphone this holiday season, make sure that you only download applications from official app stores and check other users’ reviews, as well as the app’s permission policies, before downloading. Software, such as McAfee Mobile Security, can also help protect you against dangerous apps.
Many of us travel to visit family and friends over the holidays. We begin our journey online by looking for deals on airfare, hotels, and rental cars. Before you book, keep in mind that scammers are looking to hook you with phony travel webpages with too-fantastic deals—beautiful pictures and rock-bottom prices—to deceive you into handing over your financial details and money.
Even when you’re already on the road, you need to be careful. Sometimes, scammers who have gained unauthorized access to hotel Wi-Fi will release a malicious pop-up ad on your device screen, and prompt you to install software before connecting. If you agree to the installation, it downloads malware onto your machine. To thwart such an attempt, it’s important that you perform a security software update before traveling.
You are probably already familiar with email phishing and SMiShing messages containing questionable offers and links. The scammer will mimic a legitimate organization offering cheap Rolex watches and luxury products as the “perfect gift” for that special someone, or send a message posing as your bank with a holiday promo and try to lure you into revealing information or direct you to a fake webpage. Never respond to these scams or click on an included link. Be aware that real banks won’t ask you to divulge personal information via text message. If you have any questions about your accounts, you should contact your bank directly.
QR code phishing, or “quishing,” has emerged as a significant new threat during holiday shopping seasons. In this scam method, cybercriminals place malicious QR codes in holiday advertisements posted on social media or printed flyers, parking meters and payment kiosks at shopping centers, or at restaurant tables during holiday dining. They could also email attachments claiming to offer exclusive holiday deals or fake shipping labels placed over legitimate tracking QR codes.
The kind of excitement and buzz surrounding Apple’s new iPad and iPhone is just what cybercrooks dream of when they plot their scams. They will mention must-have holiday gifts in dangerous links, phony contests, and phishing emails to grab your attention. Once they’ve caught your eye, they will again try to get you to reveal personal information or click on a dangerous link that could download malware onto your machine. Be suspicious of any deal mentioning hot holiday gift items—especially at extremely low prices—and try to verify the offer with the real retailer involved.
Cybercriminals exploit employee expectations of year-end communications by creating fake emails that appear to come from your HR department. These messages often claim to contain annual bonus information, updated benefits packages, or mandatory holiday attendance announcements. These scams are particularly effective because they prey on legitimate employee concerns about compensation, benefits, and personal time off during the holiday season. The emails often feature real-looking company logos, proper formatting, and even references to company policies to increase their credibility.
Gift cards are probably the perfect gift for some people on your holiday list. Given their popularity, cybercriminals can’t help but want to get in on the action by offering bogus gift cards online. Be wary of buying gift cards from third parties. It’s best to buy from the official retailer. Just imagine how embarrassing it would be to find out that the gift card you gave your mother-in-law was fraudulent!
No matter what gift you’re looking for, chances are you can find it quickly and easily online, but you still want to be careful in selecting which site to shop. By promoting great deals, phony e-commerce sites will try to convince you to type in your credit card number and other personal details. After obtaining your money and information, you never receive the merchandise, and your personal information is put at risk. To prevent falling victim to bogus e-commerce stores, shop only at trusted and well-known e-commerce sites. If you’re shopping on a site for the first time, check other users’ reviews and verify that the phone number listed on the site is legitimate.
This is one of the biggest scams of every holiday season. As we open our hearts and wallets, the bad guys will send spam emails and pretend to be a real charity in the hope of getting in on the giving. Their emails will sport a stolen logo and copycat text, or come from an entirely invented charity. If you want to give, it’s always safer to visit the charity’s legitimate website, and do a little research about the charity before you donate.
E-cards are a popular way to send a quick “thank you” or holiday greeting. While most e-cards are safe, some are malicious and may contain spyware or viruses that download onto your computer once you click on the link to view the greeting. Before clicking, look for clues that the e-card is legitimate. Make sure it comes from a well-known e-card site by checking the domain name of the included link. Also check to see that the sender is someone you actually know, and that there are no misspellings or other red flags that the card is a fake.
With increased package deliveries during the holiday season, fake shipping notifications have become a common attack. These messages claim to be from legitimate shipping companies such as UPS, FedEx, or DHL, informing you of package delivery attempts or shipping delays. To complete the delivery, these notices will ask you to click on malicious links or attachments that will download malware or direct you to fake websites that will steal personal information. The timing of these attacks coincides with legitimate increased shipping activity, making them harder to distinguish from authentic communications. To track your deliveries, it is best to check the shipping company’s real website or through the trusted platform from which you ordered the product.
Knowing about these common scam tactics is only the first step toward protecting yourself and those you care about. The next step is for you to learn and implement practical, effective strategies to stay safe while still enjoying digital holiday shopping and giving.
The holiday season brings joy and connection, but it’s also a time when scammers work hardest to exploit your festive but rushed and distracted spirit. Effective Christmas scam prevention starts with awareness. By slowing down and taking a moment to verify before you click or buy, and using layered cybersecurity protections, you can worry about one less thing and focus on what matters most this season.
Stay security-conscious without letting fear diminish your holiday enjoyment and pursue your digital holiday activities with the right knowledge and tools. We hope that the specific, actionable protections will help you identify red flags, verify legitimate offers, secure your devices and accounts, and respond effectively to suspicious activity. Stay informed by following trusted sources for the latest cybersecurity tips during the holidays, and make this season about celebrating safely with the people you care about most.
Send the link to this page to your family and friends to increase their awareness and take steps to protect themselves.
The post The Top 12 Scams Of Christmas To Watch Out For appeared first on McAfee Blog.

Thanksgiving—not before Halloween as we see things in stores and online now. It seems like the holiday season and decorations start earlier and earlier every year.
But one thing that hasn’t changed is that Black Friday is still a big shopping day. With the advent of online shopping has emerged Cyber Monday, another big sale day for online shoppers on the first Monday after Thanksgiving.
Although many of us may take advantage of these great deals that the holidays offer, we also need to be aware of the risks. Online shopping is a fun and convenient way to make purchases, locate hard-to-find items, and discover bargains, but we need to take steps to protect ourselves.
This guide looks at the methods and warning signs behind online shopping scams, shows you how to recognize fake shopping apps and websites, and shares tips for staying safe online.
Online shopping has become a cornerstone of American life. CapitalOne Shopping projects American online spending to reach $1.34 trillion in 2024 and exceed $2.5 trillion in 2030.
With such a massive sum at stake, cybercriminals are laser-focused on taking a share of it, posing financial risk to the 288 million Americans who shop online. As e-commerce grows, so does fraud. In 2024, e-commerce fraud was valued at $44.3 billion, a number seen to grow by 141% to $107 billion in 2029.
Be that as it may, there are many smart shopping habits you can apply to dramatically reduce your risk of becoming a victim of online shopping fraud and enjoy the convenience and benefits of online commerce.
Online shopping scams are designed to look normal—at first glance—especially during busy sale seasons when we’re distracted by a million preparations, moving fast, and chasing deals. These are the very circumstances that fraudsters bank on to victimize you into taking the bait. Being aware of the common scam indicators will help you pause and think, recognize trouble early, and protect both your money and your personal information.
Safe online shopping starts with recognizing the hallmarks of legitimate retailers. Before you enter any payment details, take a moment to verify that the website you’re shopping on is genuine. Scam stores can look polished and convincing, but they often leave behind subtle clues. Here are quick ways to check their authenticity:
 trustmark, indicating that the site has been scanned and verified as secure by a trusted third party. This security seal indicates that the site will help protect you from identity theft, credit card fraud, spam, and other malicious threats.
trustmark, indicating that the site has been scanned and verified as secure by a trusted third party. This security seal indicates that the site will help protect you from identity theft, credit card fraud, spam, and other malicious threats.The FTC also recommends these additional tips so you can enjoy all the advantages that online shopping has to offer and prevent risking your personal information.
Online shopping should feel exciting, not a dangerous undertaking you have to brace for, especially during the season of giving. It can be, with a few simple steps—checking the URL, looking for HTTPS, verifying the seller, paying with a credit card or virtual number, and trusting your gut when something feels suspicious. These small habits will keep your money and your identity where they belong: with you.
For increased safety while shopping online, seek out the help of a trusted security solution such as McAfee+ that will alert you of risky links and compromised websites to prevent identity theft or malware infection.
If this guide helps you, pass it along to someone you care about. Scams don’t just target individuals—they cascade into families and friend groups. The more we normalize safe shopping habits and increase our vigilance, the harder it is for fraudsters to win. If you ever feel unsure mid-purchase, take a breath and double-check. A few extra seconds now can save you a lot of stress later. Stay safe, and happy shopping!
The post Helpful Tips for Safe Online Shopping appeared first on McAfee Blog.

Even as passkeys and biometric sign-ins become more common, nearly every service still relies on a password somewhere in the process—email, banking, social media, health portals, streaming, work accounts, and device logins.
Most people, however, don’t realize the many ways we make our accounts vulnerable due to weak passwords, enabling hackers to easily crack them. In truth, password security isn’t complicated once you understand what attackers do and what habits stop them.
In this guide, we will look into the common mistakes we make in creating passwords and offer tips on how you can improve your password security. With a few practical changes, you can make your accounts dramatically harder to compromise.
Modern password strength comes down to three truths. First, length matters more than complexity. Every extra character multiplies the number of guesses an attacker must make. Second, unpredictability matters because attack tools prioritize the most expected human choices first. Third, usability matters because rules that are painful to follow lead to workarounds like reuse, tiny variations, or storing written passwords in unsafe ways. Strong password security is a system you can sustain, not a heroic one-time effort.
Strong passwords serve as digital barriers that are more difficult for attackers to compromise. Mathematically, password strength works in your favor when you choose well. A password containing 12 characters with a mix of uppercase letters, lowercase letters, numbers, and symbols creates over 95 trillion possible combinations. Even with advanced computing power, testing all these combinations requires substantial time and resources that most attackers prefer to invest in easier targets.
This protection multiplies when you use a unique password for each account. Instead of one compromised password providing access to multiple services, attackers must overcome several independent security challenges, dramatically reducing your overall risk profile.
Developing strong password security habits offers benefits beyond protecting your accounts. These habits contribute to your overall digital security posture and create positive momentum for other security improvements, such as:
On the other hand, weak passwords are not just a mild inconvenience. They enable account takeovers and identity theft, and can become the master key to your other accounts. Here’s a closer look at the consequences:
Account takeover happens when cybercriminals gain unauthorized access to your online accounts using compromised credentials. They could impersonate you across your entire digital presence, from email to social media. For instance, they can send malicious messages to your contacts, make unauthorized purchases, and change your account recovery information to lock you out permanently.
The effects of an account takeover can persist for years. You may discover that attackers used your accounts to create new accounts in your name, resulting in damaged relationships and credit scores, contaminated medical records, employment difficulties, and legal complications with law enforcement.
Financial losses from password-related breaches aren’t limited to money stolen from your accounts. Additional costs often include:
The stress and time required to resolve these issues also affect your overall well-being and productivity.
Your passwords also guard your personal communications, private photos, confidential documents, and intimate details about your life. When these barriers fail, you could find your personal photos and messages shared without consent, confidential business information in competitors’ hands. The psychological, emotional, and professional impact of violated trust can persist long after the immediate crisis passes.
You can dramatically improve your password security with relatively small changes. No need to invest in expensive or highly technical tools to substantially improve your security. Here are some simple tips for better password security:
If you take away only one insight from this article, let it be this: password length is your biggest advantage. A long password creates a search effort that brute force tools will take a long time to finish. Instead of trying to remember short strings packed with symbols, use passphrases made of several unrelated words. Something like “candle-river-planet-tiger-47” is both easy to recall and extremely hard to crack. For most accounts, 12–16 characters is a solid minimum; for critical accounts, longer is even better.
Password reuse is the reason credential stuffing works. When one site is breached, attackers immediately test those leaked credentials on other services. If you reuse those credentials, you have effectively given the keys to your kingdom. Unique passwords can block that entry. Even if a shopping site leaks your password, your email and banking stay protected because their passwords are different.
Attackers always try the obvious human choices first: names, birthdays, pets, favorite teams, cities, schools, and anything else that could be pulled from social media or public records. Even combinations that feel “creative,” such as a pet name plus a year, tend to be predictable to cracking tools. Your password should be unrelated to your life.
In the past, security experts encouraged people to replace letters with symbols such as turning “password” into “P@ssw0rd” and calling it secure. That advice no longer holds today, as attack tools catch these patterns instantly. The same goes for keyboard walks (qwerty, asdfgh), obvious sequences (123456), and small variations like “MyPassword1” and “MyPassword2.” If your password pattern makes sense to a human, a modern cracking tool will decipher it in seconds.
Humans think they’re random, but they aren’t. We pick symbols and words that look good together, follow habits, and reuse mental templates. Two reliable ways to break that habit are using Diceware—an online dice-rolling tool that selects words from a list—and password generators, which create randomness better than your human brain. In addition, the variety of characters in your password impacts its strength. Using only lowercase letters gives you 26 possible characters per position, while combining uppercase, lowercase, numbers, and symbols expands this to over 90 possibilities.
Not every account needs the same level of complexity, but every account needs to be better than weak. For email, banking, and work systems, use longer passphrases or manager-generated passwords of 20 characters or more. For daily convenience accounts such as shopping or social media, a slightly shorter but still unique passphrase is fine. For low-stakes logins you rarely use, still keep at least a 12-character unique password. This keeps your accounts secure without being mentally exhausting.
Multi-factor authentication (MFA) adds a second checkpoint in your security, stopping most account takeovers even if your password leaks. Authenticator apps are stronger than SMS codes, which can be intercepted in SIM-swap attacks. Hardware or physical security keys are even stronger. Start with your email and financial accounts, then expand to everything that offers MFA.
A perfect password is useless if you type it into the wrong place. Phishing attacks work by imitating legitimate login pages or sending urgent messages that push you to click. Build the habit of checking URLs in unsolicited emails or texts, being wary of pressure tactics, and taking a moment to question the message. When in doubt, open a fresh tab and navigate to the service directly.
You may not know it, but shared computers may carry keyloggers, unsafe browser extensions, or saved sessions from other users. If you have no choice but to sign in using a shared device, don’t allow the browser to save your log-in details, log out fully afterward, and change the password later from your own device.
On public networks in places like such as cafes or airports, cybercriminals could be prowling for their next victim. Attackers sometimes create fake hotspots with familiar names to trick people into connecting. Even on real public Wi-Fi, traffic can be intercepted. The safest choice is to avoid logging into sensitive accounts on public networks. If you must use public Wi-Fi, protect yourself by using a reputable virtual private network and verify the site uses HTTPS.
Many password thefts happen as a result of compromised devices and software. Outdated operating systems and browsers can contain security vulnerabilities known to hackers, leading to malware invasion, session hijacking, or credential harvesting. The best recourse is to set up automatic updates for your OS, browser, and antivirus tool to remove a huge chunk of risk with no additional effort from you.
Password managers solve two hard problems at once: creating strong unique passwords and remembering them. They store credentials in an encrypted vault protected by a master password, generate high-entropy passwords automatically, and often autofill only on legitimate sites (which also helps against phishing). In practice, password managers are what make “unique passwords everywhere” feasible.
Among all others, your master password that opens your password manager is the one credential you must memorize. Make it long, passphrase-style, and make sure you have never reused it anywhere else. Then add MFA to the manager itself. This makes it extremely difficult for someone to get into your vault even if they somehow learn your master password.
The old “change every 90 days no matter what” guideline could backfire, leading to password-creation fatigue and encouraging people to make only tiny predictable tweaks. A smarter approach is to update only when something changes in your risk: a breach, a suspicious login alert, or a health warning from your password manager. For critical accounts, doing a yearly review is a reasonable rhythm.
Unused accounts are easy to forget and easy to compromise. Delete services you don’t use anymore, and review which third-party apps are connected to your Google, Apple, Microsoft, or social logins. Each unnecessary connection is another doorway you don’t need open.
As mentioned in the tips above, passphrases have become the better, more secure alternative to traditional passwords. A passphrase is essentially a long password made up of multiple words, forming a phrase or sentence that’s meaningful to you but not easily guessed by others.
Attackers use sophisticated programs that can guess billions of predictable password combinations per second using common passwords, dictionary words, and patterns. But when you string together four random words, you create over 1.7 trillion possible combinations, even though the vocabulary base contains only 2,000 common words.
Your brain, meanwhile, is great at remembering stories and images. When you think “Coffee Bicycle Mountain 47,” you might imagine riding your bike up a mountain with your morning coffee, stopping at mile marker 47. That mental image sticks with you in ways that “K7#mQ9$x” never could.
The approach blending unpredictability and the human ability to remember stories offers the ideal combination of security and usability.
To help you create more effective passphrases, here are a few principles you can follow:
Password managers are encrypted digital vaults that store all your login credentials behind a single master password. They are your personal security assistant that never forgets, never sleeps, and constantly works to keep your accounts protected with unique, complex passwords.
Modern password managers create passwords that are truly random, combining uppercase and lowercase letters, numbers, and special characters in patterns that are virtually impossible for cybercriminals to guess or crack through brute force attacks. These passwords typically range from 12 to 64 characters long, exceeding what most people could realistically remember or type consistently.
The encrypted format scrambles your passwords using advanced cryptographic algorithms before being saved. This means that even if someone gained access to your password manager’s servers, your actual passwords would appear as meaningless strings of random characters without the encryption key. Only you possess this key through your master password.
The auto-fill functionality also offers convenience, recognizing the login page of your account and instantly filling in your username and password with a single click or keystroke. This seamless process happens across operating systems, browsers, and devices—your computer, smartphone, and tablet—keeping your credentials synchronized and accessible wherever you need them.
Selecting the right password manager requires careful consideration of several factors that directly impact your security and user experience.
The reputation and track record of the company offering the password manager should be your first consideration. Look for companies that have been operating in the security space for several years and have a transparent approach to security practices.
Reputable companies regularly undergo independent security audits by third-party cybersecurity firms to examine the password manager’s code, encryption methods, and overall security architecture. Companies that publish these audit results demonstrate transparency and commitment to security.
Also consider password managers that use AES-256 encryption, currently the gold standard for data protection used by government agencies and financial institutions worldwide. Additionally, ensure the password manager employs zero-knowledge architecture, meaning the company cannot access your passwords even if they wanted to.
Intuitive user interface, reliable auto-fill functionality, responsive customer support, and ease of use should be checked as well. A password manager that is confusing to navigate or constantly malfunctions will likely be abandoned, defeating the purpose of improved password security.
Choose a solution that offers other features aside from the basic password storage. Modern password managers often include secure note storage for sensitive information such as Social Security numbers, passport details, password sharing capabilities for family accounts, and dark web monitoring that alerts you if your credentials appear in data breaches.
Strong password security doesn’t have to be complicated. Small changes you make today can dramatically improve your digital security. By creating unique, lengthy passwords or passphrases for each account and enabling multi-factor authentication on your most important services, you’re taking control of your online safety.
Consider adopting a reputable password manager to simplify the process while maximizing your protection. It’s one of the smartest investments you can make for your digital security.
The post 15 Vital Tips To Better Password Security appeared first on McAfee Blog.

Social media platforms connect you to thousands of people worldwide. But while these platforms offer incredible opportunities for bonding, learning, and entertainment, they also present personal security challenges. Navigating them safely requires being aware of risks and proactively protecting your accounts.
The three most common risks you’ll encounter are privacy exposure, account takeover, and scams. Privacy exposure occurs when your personal information becomes visible to unintended audiences, potentially leading to identity theft, stalking, or professional damage. You have control over your social media security. By implementing safe social media practices, you can dramatically reduce your risk exposure.
This guide rounds up 15 practical, everyday tips to help you secure your accounts and use them more safely. It covers smart posting habits, safer clicking and app-permission choices, stronger privacy settings, and core security basics like using updated browsers, reliable protection tools, and identity-theft safeguards—so you can enjoy social media without making yourself an easy target.
Before we dive in, we want to remind you first that our strongest recommendation amid anything and everything unsolicited, unusual, or suspicious on social media is this: verify, verify, verify through separate communication channels such as phone, email, and official websites.
Not a day goes by when we don’t hear about a new hack. With 450,000 new pieces of malware released to the internet every day, security never sleeps. For your increased awareness, here’s a short list of the most common social media scams:
Social media is quite engaging, with all the funny status updates, photos, and comments. However, all these bits of information can reveal more about you than you intended to disclose. The examples below might be extreme, but they are real-world scenarios that continue to happen to real people daily on social media:
Oversharing on social media creates significant risks that extend beyond embarrassment or regret. Identity thieves actively monitor social platforms for personal information they can use to answer security questions, predict passwords, or impersonate you in social engineering attacks.
Avoid publicly answering questionnaires with details like your middle name, as this is the type of information financial institutions—and identity thieves—may use to verify your identity.
Third-party apps with excessive permissions can access your personal data, post to social media at any time on your behalf, or serve as entry points for attackers, regardless of whether you’re using the application. To limit app access and reduce your attack surface significantly, review all apps and services connected to your social media accounts. Revoke permissions to applications you no longer use or don’t remember authorizing.
Shortened links can be exploited in social media phishing attacks as they hide the final destination URL, making it difficult for you to determine where it actually leads. These tactics mimic legitimate communications from trusted sources and come in the form of direct messages, comments, sponsored posts, and fake verification alerts, all in an effort to steal your personal information, login credentials, or financial details. Often, these attacks appear as urgent messages claiming your account will be suspended or fake prize notifications.
When you identify phishing attempts, immediately report and block the suspicious accounts using the platform’s built-in reporting features. This will protect not only you but other users on the platform.
If the link is posted by a product seller or service provider, it is a good idea to:
You might think the video or link relates directly to you. But when you click it, you get a message saying that you need to upgrade your video player in order to see the clip. When you attempt to download the “upgrade,” the malicious page will instead install malware that tracks and steals your data. As mentioned, don’t click suspicious links or download files from unknown sources before verifying independently. Visit the official websites by directly typing the URL yourself or using trusted search engines.
This also brings us to the related topic of being tagged on other people’s content. If you don’t want certain content to be associated with you, adjust the settings that enable you to review posts and photos before they appear on your profile. This allows you to maintain control over your digital presence and prevents embarrassing or inappropriate content associations.
If one of your friends posts, “We’re stuck in Cambodia and need money,” keep your radar up as it’s most likely a scam. It is possible that a scammer has taken over your friend’s account, and is using it to impersonate them, spread malicious content, or extract sensitive information from their contacts, including you. Don’t engage with this post or the fraudster, otherwise the next account takeover could be yours.
In this kind of scam, some critical areas of your life are affected:
When you encounter suspicious activity, always use official support pages rather than responding to questionable messages. Major social media platforms provide dedicated help centers and verified contact methods.
Select the most secure options and check periodically for changes that can open up your profile to the public. Depending on your preference and the privacy level you are comfortable with, you can choose from these options:
We suggest that you review your privacy settings every three months, as platforms frequently update their policies and default settings. While you are at it, take the opportunity to audit your friend lists and remove inactive or suspicious accounts.
Posting real-time locations or check-ins can alert potential stalkers to your whereabouts and routine patterns, while geo-tagged photos can reveal where you live, study, work, shop, or work out. Location sharing creates patterns that criminals can exploit for security threats such as stalking, harassment, and other physical crimes.
To avoid informing scammers of your whereabouts, turn off location tagging in your social media apps and avoid posting about your routine. You might also consider disabling “last seen” or “active now” indicators that show when you’re online. This prevents others from monitoring your social media activity patterns and reduces unwanted contact attempts, significantly improving your personal and family safety while maintaining your ability to share experiences.
Older browsers tend to have more security flaws and often don’t recognize newer scam patterns, while updated versions are crucial for security by patching vulnerabilities. Updates add or improve privacy controls such as tracking prevention, cookie partitioning, third-party cookie blocking, stronger HTTPS enforcement, transparent permission prompts. They also support newer HTML/CSS/JavaScript features, video and audio codecs, payment and login standards, and accessibility features.
In terms of performance, new browser versions offer faster performance, better memory management, and more efficient rendering, so you get fewer freezes, less fan noise, and longer battery life and better extension compatibility.
Consider using password managers, which can create and store secure passwords for you. Never reuse passwords across platforms. This practice ensures that if one account is compromised, your other accounts remain secure. Password managers also help you monitor for breached credentials and update passwords regularly.
In addition, implement multi-factor authentication (MFA)on every social media account using authenticator apps. This single step can protect social media accounts from 99% of automated attacks. MFA enforcement should be non-negotiable for both personal and business accounts, as it adds critical security that makes account takeovers exponentially more difficult.
Scammers build fake login pages that look identical to real ones. The only obvious difference is usually the domain. They want you to type your username/password into their site, so they can steal it. So if you’re visiting a Facebook page, make sure you look for the https://www.facebook.com address.
The rule is to read the domain from right to left because the real domain is usually the last two meaningful segments before the slash. For instance, https://security.facebook.com—read from right to left—is legitimate because the main domain is facebook.com, and “security” is just a subdomain.
Watch out for scam patterns such as:
Within the social media platform, scammers often insert a “second” sign-in step to capture your credentials. A common trick is sending you to a page that looks like a normal email, business, or bank website but then suddenly asks you to log in again “to continue,” “to verify your identity,” or “because your session expired.” That extra login prompt is frequently a fake overlay or a malicious look-alike page designed to steal passwords.
Clicking a shared document link, viewing a receipt, or checking a delivery status usually shouldn’t require you to re-enter your email and password—especially if you’re already signed in elsewhere. Another example is a fake security notification claiming your account has been compromised, directing you to another page or website that requires a new login. Attackers usually rely on urgency, panic, and habit; you might be so used to logging in all the time, that you could do it automatically without noticing the context is wrong.
A safer habit is to stop and reset the flow. If something unexpectedly asks for another login, don’t use the embedded prompt. Instead, open a new tab, type the site’s official address yourself, check account status, and log in there if needed. If the request was legitimate, it will still work once you’re signed in through the official site; if it was a trap, you’ve just avoided handing over your credentials.
Your suite should include an antivirus, anti-spyware, anti-spam, a firewall, and a website safety advisor. Keeping your security suite up to date is essential as threats evolve daily, and outdated protection can miss new malware, phishing kits, ransomware variants, and scam techniques. Updates also patch security weaknesses in the software itself, improve detection technologies, and add protections for newer attack methods.
The McAfee Social Privacy Manager extends “security updates” beyond your device and into your social media footprint by scanning your privacy settings across supported platforms, flagging exposures, and recommending safer configurations. Because social platforms frequently change their settings and defaults, Social Privacy Manager also needs to stay updated to recognize and apply the right privacy protections.
Regardless of how careful you may be or any security systems you put in place, there is always a chance that you can be compromised in some way. It’s nice to have identity theft protection watching your back.
McAfee+ combines every day device security with identity monitoring in one suite. Depending on the plan, McAfee+ can watch for your personal info on the dark web and breach databases, monitor financial and credit activity, and send real-time alerts for anomalies. The Advanced and Ultimate plans add wider support such as credit monitoring and tracking for bank or investment accounts, as well as tools that reduce your exposure such as Personal Data Cleanup that removes your info from data broker sites. It doesn’t just warn you after a breach; it helps shrink the chances your data gets misused in the first place.
Social media brings incredible opportunities, but privacy exposure, scams, and account takeovers remain real challenges that can impact your finances, reputation, and personal security. The tips outlined above give you practical ways to recognize the risks and protect your social media accounts. By raising your level of awareness and applying safe social media practices, you are building a stronger defense against evolving threats.
Make security a family affair by sharing these safe social media practices with everyone in your household—especially children and teens who use social media—so they can enjoy a safer experience.
The post 15 Critical Tips to Stay Safe on Social Media appeared first on McAfee Blog.

A determined cybercriminal can find ways to guess or predict an individual’s Social Security number, which increases the risk of identity theft for all of us.
In 2009, researchers from Carnegie Mellon University revealed that a reliable method for predicting Social Security numbers was discovered using information from social networking sites, data brokers, voter registration lists, online white pages, and the publicly available Social Security Administration’s Death Master File.
Originally, the first three numbers on a Social Security card represented the state in which a person had initially applied for their card. Numbers started in the Northeast and moved westward. This meant that people born on the East Coast were assigned the lowest numbers and those born on the West Coast were assigned the highest numbers. Before 1986, people were rarely assigned a Social Security number until age 14 or so, since the numbers were used for income tracking purposes.
The Carnegie Mellon researchers were able to guess the first five digits of a Social Security number on their first attempt for 44% of people born after 1988. For those in less populated states, the researchers had a 90% success rate. In fewer than 1,000 attempts, the researchers could identify a complete Social Security number, “making SSNs akin to 3-digit financial PINs.” The researchers concluded, “Unless mitigating strategies are implemented, the predictability of SSNs exposes people born after 1988 to risks of identity theft on mass scales.”
To address this security gap, the Social Security Administration in 2011 changed the way SSNs are issued by randomizing number assignment to make predicting patterns more difficult. While this is certainly an accomplishment, the potential to predict Social Security numbers is the least of our problems. Social Security numbers can be found in unprotected file cabinets and databases in thousands of government offices, corporations, and educational institutions, exposing people to identity theft and other related risks. With the growing losses from all identity theft cases, protecting SSNs is a serious concern.
Your Social Security number might be only nine digits, but in the wrong hands, it can act like a master key that unlocks far more. It can reveal details about your life, serving as a powerful linking tool for cybercriminals to access or verify other personal details and build a more comprehensive profile of your identity.
Your Social Security number is one of your most private identifiers, but in today’s data economy, it can quietly slip into criminal marketplaces on the dark web. Even if you’re careful with your information, you can’t control how organizations protect the data they collect from you. These exposures often result from data breaches, scams, or systems you had to trust — employers, hospitals, banks, schools, and even government agencies. When your SSN shows up there, it’s usually bundled with your other information—name, birthdate, address—making it far more valuable and dangerous than a random number on its own.
Being familiar with the common paths that take your SSN to the dark web will help you recognize and avoid the risks earlier, and act fast if your information is ever compromised.
Once criminals have your SSN, they can do a range of fraudulent activities that can compromise your relationships, health, career, financial standing, and even your freedom. A single SSN can fuel everything from credit and loan scams to tax fraud, medical identity theft, and even long-term schemes like synthetic identities. Here are some examples:
Social Security identity theft isn’t always obvious right away. In many cases, people don’t realize their SSN has been compromised until weeks or months later. If you want to know if your SSN has been misused, there are clear warning signs and reliable ways to check. By reviewing a few key records, you can spot red flags early and shut down fraud before it snowballs into a long, expensive recovery process.
If you discover that someone has been using your SSN, take these steps immediately:
Since your SSN can’t be easily changed and is still treated like a universal ID, the safest approach is to put up barriers that make it harder for criminals to use, even if they get it. Aside from the steps listed above, here are additional measures you can follow to protect your SSN from the start:
Federal law requires SSN disclosure in specific situations. Organizations can legally require your SSN when no reasonable alternative exists and when they have a specific legal requirement or legitimate business need, such as:
When an organization requests your SSN, they must provide what’s called a disclosure statement, as clarified under the updated Privacy Act of the Department of Justice’s Office of Privacy and Civil Liberties. Legitimate organizations requesting your SSN must tell you:
If an organization can’t provide clear answers to these questions, that’s a red flag. The FTC’s consumer guidance emphasizes that you have the right to understand why your SSN is needed before you provide it.
You can typically decline when it’s not a necessity, alternative identification exists, it seems excessive, and there is no clear legal requirement. Common situations where you can often say no include gym memberships, retail purchases, job applications that don’t require credit checks, and various service sign-ups.
When you need to verify your identity but want to minimize SSN exposure, several alternatives can work depending on the situation:
While it’s concerning that Social Security numbers can be predicted or leaked through data breaches, you’re not powerless against SSN identity theft. The practical steps we’ve outlined put you firmly in control of your personal information security—from placing credit freezes and setting up IRS IP PINs to securing your Social Security Administration account with strong authentication. Take action today by implementing these protective measures to reduce your risk significantly.
For added security, consider a McAfee Identity Protection plan to experience proactive identity surveillance, lost wallet protection, and alerts when suspicious activity is detected on your financial accounts.
The post Smart Ways to Keep Your Social Security Number from Being Cracked appeared first on McAfee Blog.

With the rise in digital banking and online transactions, the number of automated teller machines (ATMs) worldwide declined to 2.95 million in 2025, according to the finance and crypto resource site CoinLaw. Despite this decline, ATM fraud continues to victimize innocent consumers, with global losses estimated at $2.4 billion in 2025.
Among the ATM-related security issues, card skimming accounted for almost 60% of all reported global ATM fraud cases in 2025, according to CoinLaw. Other ATM-related security threats include malware (21%) and cryptocurrency ATM scams. AI-driven ATM fraud, although still in its infancy (0.11% in 2025), is gaining traction as cybercriminals develop new phishing techniques.
In this guide, we will explore some of the security threats associated with ATMs, with a focus on skimming, and provide tips on protecting your data and money in your bank account.
ATM skimming is a form of payment card fraud where criminals secretly install illegal devices on card readers, fuel pumps, or point-of-sale terminals, which then steal your debit or credit card information. These devices, called skimmers, capture the magnetic stripe data from your card while hidden cameras or fake PIN pads record your personal identification number. With both pieces of information, criminals can create counterfeit cards or make unauthorized online purchases using your account.
Skimming devices have become increasingly sophisticated and harder to detect. Traditional overlay skimmers sit on top of legitimate card readers, but newer “shimmer” devices are inserted more deeply into the card slot, making them virtually invisible to casual inspection. These devices can store data from hundreds of cards before criminals retrieve them, often using Bluetooth technology to wirelessly download stolen information without physically accessing the skimmer.
ATMs remain the most common target for skimming attacks, but criminals also target gas station fuel pumps, which often have weaker security systems and less frequent maintenance checks. Point-of-sale terminals at retail locations, restaurants, and other businesses also present opportunities for skimming, particularly when employees are involved in the scheme.
The threat persists for several interconnected reasons. Payment card fraud is quite a profitable business and can be scaled across states or countries. Technology gaps also contribute to the problem, as many ATMs and payment terminals continue to use legacy magnetic stripe technology despite the introduction of more secure EMV chips in newer cards. Criminals also exploit legacy systems, especially if the ATM does not receive regular security updates.
Additionally, decommissioned ATMs can be freely gathered from junkyards or casually bought from online marketplaces, giving criminals the chance to collect personal data stored in the computer and study the discarded machine’s security features to improve their skimming techniques.
In some cases, used ATMs are purchased on eBay or Craigslist and then installed in areas with ample foot traffic. These machines, which can be powered by car batteries or simply plugged into a nearby outlet, are programmed to read and copy credit card data.
When your card information is compromised through skimming, the financial and personal consequences can be significant. Criminals may drain your account through ATM withdrawals or fraudulent purchases, potentially leaving you unable to access your own money. Since debit card transactions often clear immediately, unauthorized withdrawals can cause overdraft fees and bounced check charges before you even realize your account has been compromised.
Beyond the financial losses, ATM skimming can lead to identity theft, where the personal information captured becomes part of larger criminal databases used in other fraud schemes.
Consequently, your credit score and banking relationships may also suffer if fraudulent accounts are opened in your name or if you’re unable to resolve unauthorized charges quickly. While the law gives you limited liability for fraudulent transactions, the process of restoring your accounts can be time-consuming and stressful.
Criminals use a range of devices—some obvious, others nearly invisible—to steal card data and PINs right at the machine. Knowing the main types of skimmers, what they look like, and where they’re usually placed can help you recognize them and avoid a compromised ATM.
The most common type of skimming device, overlay card readers are fake attachments that criminals place directly over the legitimate card slot of an ATM. As you insert your card, it passes through the skimmer first, which captures the magnetic stripe data from your card before it reaches the actual card reader.
An evolution of skimming technology, shimmer devices are extremely thin circuit boards that criminals insert deep into the card slot, making them nearly impossible to detect through visual inspection alone. When you insert your card, you might notice increased resistance, unusual vibrations, or your card feeling momentarily stuck.
Criminals use tiny cameras to capture your PIN as you enter it on the keypad. They are so small they can be hidden in seemingly innocent locations around the ATM. Look for a small camera attached to the top of the screen, hidden in a brochure holder, or even concealed in a fake security sign.
These devices are placed over the legitimate ATM keypad to capture your PIN as you enter it. The keypad may feel spongier than usual, have a different texture, or seem thicker than normal. You might notice the numbers are printed differently, the buttons don’t press down as far as expected, or there’s a slight color difference between the keypad and the rest of the ATM. If the keypad feels loose, raised, or different from other ATMs you’ve used, don’t enter your PIN.
Considered an advanced skimming technique, wireless Bluetooth-enabled skimmers can wirelessly transmit your stolen card and PIN data to criminals, eliminating the need for them to return to retrieve the device. You could detect them by checking your phone’s Bluetooth settings for unusual device names appearing in the area, though many criminals use generic names to avoid detection. If you notice people loitering near ATMs with mobile devices, especially if they seem to be monitoring ATM users, this could indicate that a Bluetooth skimming operation is in progress.
Criminals often combine multiple types of skimming devices to maximize their data capture. A typical combination attack might involve an overlay card reader paired with a pinhole camera, or a shimmer device combined with a fake PIN pad. This is why security experts recommend following all protective measures when you use an ATM.
Recent advances in skimming technologies include devices that can be inserted through existing openings in ATMs without requiring external attachments, as well as skimmers that use near-field communication (NFC) technology to capture contactless payment information.
Your safest bet is to use ATMs inside bank branches or those clearly operated by major financial institutions. These locations have better security measures, such as surveillance cameras and regular checks that detect tampering. At outdoor ATMs, select machines in well-lit, high-traffic areas where criminal activity is less likely to occur unnoticed. Avoid ATMs in dimly lit, isolated locations where skimmers can be easily installed.
Before inserting your card, closely inspect the card insertion slot. Legitimate ATM card readers should have a uniform appearance with smooth edges and consistent coloring. Look for unusual attachments or devices that seem to have been added on top of the original reader. The card slot should align perfectly with the surrounding ATM fascia. Any gaps, misalignments, or signs that something has been glued or attached should raise immediate red flags. Trust your gut.
One of the most effective ways to detect fake card readers on ATMs is through tactile inspection. Gently grasp the card reader and try to wiggle it. A legitimate card reader should feel solid and permanently attached. If the reader or the housing feels loose, this is a strong indicator of a skimmer. If anything moves when it shouldn’t, do not use that ATM and report it to the bank immediately.
Examine the keypad carefully for any signs of modification or overlay devices. Overlay keypads often appear slightly thicker or misaligned with the surrounding area. When pressing the buttons, each one should have consistent resistance and feel. Any button that sticks or seems higher than others could indicate tampering. Pay attention to the area around the keypad for adhesive residue or scratches. Legitimate ATM keypads have consistent button spacing, uniform coloring, and should feel solid when pressed.
The ATM’s outer casing and bezel should have a uniform appearance with no obvious modifications such as loose panels, extra pieces of plastic, or areas with different coloring or texture from the rest of the machine. Check for any unusual wiring, small cameras, or devices that appear out of place. The area around the screen should be examined for any tiny cameras or recording devices that capture PIN entry. All text, logos, and branding should appear professional and consistent with the bank’s standard ATM design.
Before using any ATM, check the area for any unusual objects that could house cameras or recording equipment, including fake brochure holders, unusual signage, or any items that seem out of place. Check for people loitering nearby who seem to be watching ATM users or vehicles parked unusually close to outdoor ATMs with passengers or drivers who appear to be monitoring ATM activity.
Before using an ATM, check your smartphone’s Bluetooth settings to scan for nearby devices with suspicious names, such as those with generic or random characters, or names that don’t correspond to legitimate businesses in the area. An unusual concentration of unknown devices near an ATM could be a warning sign. This technique works best in areas where there are typically few Bluetooth devices, such as standalone ATMs.
Enable contactless withdrawals through your bank’s mobile app to authenticate and authorize QR code-based transactions and reduce your need to use an ATM. This technology uses tap-to-pay functionality or near-field communication (NFC) features, providing the same convenient access to your funds. Contact your bank to learn about contactless ATM options and how to activate these features on your accounts.
Bank websites or mobile apps usually show the locations of their legitimate ATMs. If you’re unsure about an ATM’s authenticity, check these official resources to confirm the machine is listed as a legitimate location. This step can help you avoid both skimming devices and other fraudulent ATM operations entirely. Be particularly cautious of ATMs in unusual areas. When traveling, stick to ATMs inside recognizable financial institutions.
Even when ATMs appear legitimate, always protect your PIN entry from potential observation. Use your free hand, body, or a purse to cover the keypad while entering your PIN to guard against both hidden cameras and shoulder-surfing by nearby criminals. Consider changing your PIN regularly and never write it down. If you suspect your PIN may have been compromised, change it immediately through secure channels.
Implement robust account monitoring to detect and address any skimming-related fraud as quickly as possible. Set up real-time account alerts through your bank’s mobile app to receive immediate notifications of all transactions. Review your account statements regularly and report any unauthorized activity immediately. Consider setting daily withdrawal limits to match your usage patterns to minimize losses if your card information is compromised.
If you notice signs of tampering or suspicious activity at an ATM, report it immediately to the bank to protect other customers from becoming victims and to help law enforcement track down the perpetrators. Contact the bank’s customer service line using the phone number on the back of your card, rather than the numbers displayed on the potentially compromised ATM. Document the ATM’s location, including the address and any identifying numbers or codes visible on the machine.
Stay informed about the latest ATM skimming techniques and prevention strategies through reputable sources. Consumer alerts provide updated guidance on protecting yourself from these crimes, as do major credit card networks such as Visa and Mastercard. Following your bank’s security updates and fraud alerts helps you stay aware of new threats in your area and emerging criminal techniques to watch for during ATM transactions.
Be highly cautious of anyone offering to help you with ATM troubles, even if they appear well-intentioned, especially if they suggest using their phone to call the bank or offer to show you how to complete your transaction. If you encounter problems with an ATM, cancel your transaction, retrieve your card, and contact your bank directly.
Criminals usually install skimming devices when fewer people are around to witness their actions. Daytime transactions in high-traffic areas increase the likelihood of suspicious behavior being noticed and reported. If you must use an ATM at night, choose one in a well-lit area with good visibility, preferably near businesses that are still open and have staff and customers present. Consider using indoor ATMs exclusively.
Always take your ATM receipts and store them securely until you have verified the transaction on your statement. Don’t leave them at the machine or throw them away in nearby trash cans where criminals might retrieve them to gather information about your account; even partial account numbers and transaction details could be useful to identity thieves. You can shred the receipts once you’ve confirmed the transactions.
Familiarize yourself with your bank’s policies regarding ATM fraud and your rights under federal law. The Electronic Fund Transfer Act provides specific protections for consumers who experience unauthorized ATM transactions. These protections offer you up to 60 days to report unauthorized transactions to limit your liability, but reporting within two business days provides the strongest protection.
Reduce your ATM usage by planning your cash needs and making larger, less frequent withdrawals to reduce your overall exposure to potential skimming attempts. Consider getting cash back during purchases at grocery stores, pharmacies, and trusted retailers, rather than using unfamiliar ATMs, especially when traveling or in unfamiliar areas.
ATM skimming attempts surge during peak shopping and travel periods when foot traffic increases at malls, airports, hotel lobbies, and other commercial or tourist locations. Increased cash withdrawals, crowded shopping areas, and travelers using unfamiliar ATMs create ideal conditions for skimming operations. In addition, criminals know that holiday shoppers are often distracted, rushed, and less vigilant about using ATMs. That’s why it’s important for you to be extra cautious. If you must use an ATM, take a breath and slow down to thoroughly inspect the machine and your surroundings before inserting your card.
The guidance below walks you through exactly what to do in the moment and right after, so you can limit risk to yourself and prevent others from becoming victims, too.
Protecting yourself from ATM skimming requires ongoing attention, but you’re now equipped with the knowledge to use ATMs confidently and securely—perform a visual inspection, do the wiggle test, review the keypad, and be aware of your surroundings. Trust your instincts. If something feels wrong or looks suspicious about an ATM, consider finding an alternative location. Your intuition is a valuable tool in recognizing potentially compromised machines.
Share these ATM safety practices with your family members and friends to strengthen their security as well. Take a moment to revisit your bank’s fraud protection guidelines and ensure you understand their notification procedures for suspicious activity. Your financial institution can partner with you in preventing fraud, so don’t hesitate to reach out with questions about their latest security features.
The post Essential Tips to Avoid ATM Skimming appeared first on McAfee Blog.

This is a critical time for our personal security, particularly in terms of privacy and personal information. A battle is being waged over our data by multiple parties, from criminal hackers to advertisers and data brokers. This article provides essential tips to help you protect the personal details you want to keep private and stay safe online.
Criminal hackers and identity thieves want to use your name to open new accounts, which they can turn into cash. They may try to obtain credit cards, utility services, or mobile phones using your good credit. In other cases, these same thieves take over existing bank or credit card accounts and completely empty them out. Identity theft affects millions of Americans each year, with over 1.4 million reports filed to the FTC in recent years and an estimated 15 million victims annually.
Online, advertisers and marketers use tracking cookies and sophisticated technologies to gather information about you and your web browsing habits. They can then offer you products or services based on the profile they’ve developed. Almost every major website contains cookies, and they are changing the way advertising is created and targeted.
The Federal Trade Commission (FTC) has explored options, such as “Do Not Track” mechanisms, to allow consumers to opt out of data collection; however, these efforts have faced significant challenges. Browser-based solutions have been proposed, but the advertising industry’s partnerships with major media and tech companies have made comprehensive opt-out mechanisms difficult to implement effectively.
Social media companies compete for your attention and your information because user data is valuable to advertisers and marketers. Whatever you post in your profile is broken down, cataloged, and disseminated. Your name, age, address, email, phone number, contacts, income status, job description, and other personal details are of use to anyone targeting your wallet.
However, legitimate advertisers aren’t the only ones targeting social networks. Criminal hackers and identity thieves are accessing your data, either through the public portion of these sites or by hacking through the back door. The bad guy is using your profile information to come up with an answer to your password reset question, or to trick you into opening your wallet or entering login credentials that might allow them to take over your existing accounts.
Amid all these developments, the National Cyber Security Alliance established Data Privacy Day, an annual awareness event observed every January 28, which encourages you to take control of your personal information and understand your online privacy rights. Initially launched in 2008, this important day coincides with the anniversary of the signing of Convention 108, the first legally binding international treaty dealing with privacy and data protection.
As a U.S. consumer, Data Privacy Day matters to you more than ever because your personal information has become incredibly valuable and, unfortunately, increasingly vulnerable. Every day, you share personal details through social media, shopping websites, mobile apps, and online services, often without realizing how this information is collected, used, or shared.
The observance of this day highlights several key risks that affect your daily digital life. Data misuse occurs when companies collect more information than necessary or use your personal details in ways you haven’t explicitly approved. Identity theft remains a significant threat, with criminals using stolen personal information to open fraudulent accounts, make unauthorized purchases, or even file fake tax returns. Additionally, data breaches continue to expose millions of Americans’ personal information each year, from social security numbers to financial details.
What makes Data Privacy Day empowering is its focus on actionable steps you can take immediately. Rather than feeling overwhelmed by privacy concerns, you can use this day as motivation to review and strengthen your digital privacy habits. The day is a reminder that privacy and data protection aren’t just technical concepts. They’re fundamental rights that help you maintain control over your digital life.
Before delving deeper into regulations and best practices, let’s take a look at the core concepts. The Federal Trade Commission defines data privacy as the reasonable expectation that your personal information will be handled appropriately by the organizations that collect it. It is your fundamental right to control how your personal information is collected, used, shared, and retained by the companies and services you interact with every day. At its heart, data privacy ensures that you have a say in what happens to details about your life, from your name and email address to your online shopping preferences, videos watched, social media usage, and down to your browsing habits and location data.
Your data follows a path that starts with collection, when companies gather information directly from you, such as when you fill out a form, or indirectly through cookies and tracking pixels. The use phase refers to how organizations process your information, whether to improve their services, target advertisements, or analyze user behavior. Sharing involves passing your data to third parties, from business partners to data brokers. Retention determines how long your information stays in their systems, often well beyond the end of your active relationship with the service.
Throughout this process, your information is governed by three principles of modern data privacy:
When Netflix asks if you want to share viewing data to improve recommendations, that’s consent in action. When Google lets you download your search history or delete location tracking, you’re exercising control. When Apple’s privacy labels show exactly what data an app collects, that’s transparency working for you.
Under these newly instituted state privacy laws, you have several key rights that put you in control of your personal information:
Data protection and data privacy are sometimes used interchangeably, but they serve different but complementary roles in keeping your personal information safe:
Here are some everyday scenarios that show how these concepts work differently:
As a consumer, your data privacy rights translate into real, actionable benefits you can use today. However, the effectiveness of these protections often depends on enforcement and your own awareness of the tools available to you.
U.S. state privacy laws are increasingly giving you the right to know what personal information companies collect, the right to delete your data, and the right to opt out of having your information sold or shared.
America’s privacy framework is built on sector-specific federal regulations combined with increasingly robust state legislation. This approach means your rights and protections can vary significantly depending on where you live and what type of data is being collected.
At the federal level, key laws include the Health Insurance Portability and Accountability Act (HIPAA) for healthcare data, the Fair Credit Reporting Act (FCRA) for credit information, and the Children’s Online Privacy Protection Act (COPPA) for children under 13 years. While these provide important protections in specific areas, they leave significant gaps in comprehensive consumer data privacy protection.
To fill these gaps, California established crucial precedents through the California Consumer Privacy Act (CCPA) and its successor, the California Privacy Rights Act (CPRA). Other states are also now enacting comprehensive privacy laws, including Virginia’s Consumer Data Protection Act, Colorado Privacy Act, Connecticut’s Data Privacy Act, and Utah’s Consumer Privacy Act. Each provides residents with fundamental rights over their personal data while requiring businesses to implement stronger protection measures.
Sensitive personal data represents the most valuable and vulnerable information about you—the details that, if compromised, could cause significant harm to your finances, safety, and peace of mind. Unlike basic contact information, sensitive data requires stronger legal protections and your extra vigilance because of its potential for misuse.
Your health information deserves particular care because it reveals intimate details about your physical and mental well-being. HIPAA protections cover medical records, but health data collected by fitness apps, mental health platforms, or wellness websites may not receive the same legal safeguards.
Biometric data—your unique physical characteristics such as fingerprints, voice patterns, or facial features—can’t be changed if stolen, making this information particularly precious.
Children’s data receives special attention under privacy laws because minors can’t meaningfully consent to data collection. The Children’s Online Privacy Protection Act requires explicit parental consent before companies can collect information from children under 13, while some state laws extend these protections to older teens.
Meanwhile, global services such as Google, Facebook, or Netflix apply the Europe-established General Data Protection Regulation (GDPR) laws worldwide to maintain consistent data practices.
GDPR personal data includes obvious identifiers such as your name, email address, phone number, and Social Security number. But it also covers less obvious information, such as IP addresses, device IDs, location data, and even your online shopping habits or social media activity. Essentially, if data points can be combined to create a profile of you, they qualify as personal data under GDPR standards. This broader definition gives you stronger control over your information and has influenced many U.S. companies to offer the same rights to all users, not just those in the European Union.
Whether a company follows GDPR, California’s privacy laws, or other frameworks, the core principle remains the same: you deserve transparency and control over your personal information.
Your privacy rights are expanding, but exercising them effectively requires staying informed and taking proactive steps. As we celebrate Data Privacy Day, we recommend you participate by taking simple, practical steps to exercise your data privacy rights.
Start with the platforms and services you use most frequently. Look for the privacy or data protection section in your account settings and review the information being collected and shared.
Many major companies now provide online forms or dedicated email addresses for privacy requests. Take advantage of these to understand what data they have about you. Popular platforms such as Google, Facebook, and Amazon have streamlined processes for data downloads.
Look for “Do Not Sell My Personal Information” links on websites, typically found in footers or privacy policy pages. You can also use opt-out tools such as the Global Privacy Control browser setting that automatically signals your opt-out preferences.
Many data brokers now offer opt-out mechanisms, though the process can be time-consuming. Consider using privacy services that handle multiple opt-out requests on your behalf.
Regularly search for your name and personal information online. Set up Google Alerts for your name and key personal details to stay informed about new appearances of your information. In addition, monitor your credit reports for unauthorized changes, and use identity monitoring services that watch for your personal information appearing in data breaches or on the dark web.
When sharing sensitive information online, verify that websites use https:// in the address bar and read privacy policies before providing personal details. Only use well-established, privacy-focused health, financial, and communication platforms with a strong track record of privacy and data protection.
For children’s data, maintaining active oversight will help you stay ahead of potential problems in their online activities. Review the apps and websites they use, understand what information these platforms collect, and use parental controls to limit data sharing. Teach your children about privacy and the risks of sharing personal information online.
Protecting your personal data doesn’t have to feel like a giant, technical project. Most privacy wins come from small, repeatable habits that you can do in minutes to shrink your digital footprint, and use the internet on your terms.
Your personal information has value, so make sure you’re getting a fair return through services that respect your privacy.
Personal data includes any information that can directly or indirectly identify you. This covers obvious details such as your name, email, and Social Security number, but also extends to IP addresses, device identifiers, location data, browsing history, and even inferences about your preferences or behavior.
On company websites, look for “Do Not Sell My Personal Information” or “Your Privacy Choices” links, usually found in the footer. You can also use the Global Privacy Control browser signal to send opt-out requests automatically. Services such as DeleteMe or manual removal requests can help you reclaim control of your information from data brokers and multiple platforms.
First, change passwords for affected accounts and enable two-factor authentication. Next, monitor your credit reports and bank statements for unusual activity. If Social Security numbers or financial data were involved, place a credit freeze with all three major credit bureaus. Sign up for identity monitoring services if offered by the breached company. Be sure to document everything and report identity theft to the FTC if you notice fraudulent activity.
Watch for manipulative design tricks that push you toward sharing more data. Red flags include pre-checked boxes for marketing emails, making privacy-friendly options harder to find or understand, using confusing language that hides the intent, or making it much easier to accept all cookies than to customize your preferences. Legitimate consent should be freely given, specific, informed, and easily withdrawn.
Depending on your location, you may have the right to know what data companies collect about you, request copies of your data, correct inaccurate information, delete your data, and opt out of its sale or use for targeted advertising. Some laws also give you the right to data portability and protect you from discrimination for exercising these rights. Check if your state has comprehensive privacy laws or if you’re covered by GDPR.
To stay current with your privacy rights and the evolving legal landscape, bookmark these authoritative resources:
Data Privacy Day serves as an important annual reminder, but your commitment to privacy and data protection shouldn’t end when January 28th passes. The digital threats we face continue to evolve throughout the year, making ongoing vigilance essential to protect your personal details.
Small, consistent habits can make a profound difference in your digital security. By regularly updating your passwords, enabling multi-factor authentication, reviewing privacy settings on your accounts, and staying informed about emerging threats, you create layers of protection that work together to safeguard your information.
Invest in McAfee+ identity protection, which includes proactive identity surveillance to monitor subscribers’ credit and personal information, as well as access to live fraud resolution agents who help subscribers work through the process of resolving identity theft issues.
The post Celebrate Data Privacy Day by Applying These Best Practices appeared first on McAfee Blog.

Unfortunately, scammers today are coming at us from all angles, trying to trick us into giving up our hard-earned money. We all need to be vigilant in protecting ourselves online. If you aren’t paying attention, even if you know what to look for, they can still catch you off guard. There are numerous ways to detect fake sites, phishing, and other scams, including emails.
Before we delve into the signs of fake websites, we will first take a closer look at the common types of scams that use websites, what happens when you accidentally access a fake website, and what you can do in case you unknowingly purchased items from it.
Fake or scam websites are fraudulent sites that look legitimate while secretly attempting to steal your personal information, money, or account access.
These deceptive platforms masquerade as trustworthy businesses or organizations, sending urgent messages that appear to be from popular shopping websites offering fantastic limited-time deals, banking websites requesting immediate account verification, government portals claiming you owe taxes or are eligible for refunds, and shipping companies asking for delivery fees.
The urgency aims to trick you into logging in and sharing sensitive information, such as credit card numbers, Social Security details, login credentials, and personal data. Once you submit your data, the scammers will steal your identity, drain your accounts, or sell your details to other criminals on the dark web.
These scam websites have become increasingly prevalent because they’re relatively inexpensive to create and can reach millions of potential victims quickly through email and text campaigns, social media ads, and search engine manipulation.
Cybersecurity researchers and consumer protection agencies discover these fraudulent sites through various methods, including monitoring suspicious domain registrations, analyzing reported phishing attempts, and tracking unusual web traffic patterns. According to the FBI’s Internet Crime Complaint Center, losses from cyber-enabled fraud totaled $13.7 billion, with fake websites accounting for a significant portion of these losses.
Visiting a fake website, accidentally or intentionally, can expose you to several serious security risks that can impact your digital life and financial well-being:
Scammers employ various tactics to create fake websites that appear authentic, but most of these techniques follow familiar patterns. Knowing the main types of scam sites helps you recognize danger faster. This section lists the most common categories of scam websites, explains how they operate, and identifies the red flags that alert you before they can steal your information or money.
Understanding these common scam types helps you recognize fake sites before they can steal your information or money. When in doubt, verify legitimacy by visiting official websites directly through bookmarks or search engines rather than clicking suspicious links.
For the latest warnings and protection guidance, check resources from the Federal Trade Commission and the FBI’s Internet Crime Complaint Center.
You can protect yourself by learning to recognize the warning signs of fake sites. By understanding what these scams look like and how they operate, you’ll be better equipped to shop, bank, and browse online with confidence. Remember, legitimate companies will never pressure you to provide sensitive information through unsolicited emails or urgent pop-up messages.
Most scams typically start with social engineering tactics, such as phishing, smishing, and fake social media messages containing suspicious links, before directing you to a fake website.
From these communications, the scammers impersonate legitimate organizations before finally executing their malevolent intentions. To avoid being tricked, it is essential to recognize the warning signs wherever you encounter them.
Fake emails are among the most common phishing attempts you’ll encounter. If you see any of these signs in an unsolicited email, it is best not to engage:
Smishing messages bear the same signs as phishing emails and have become increasingly sophisticated. These fake messages often appear to come from delivery services, banks, or government agencies. Common tactics include fake package delivery notifications, urgent banking alerts, or messages claiming you’ve won prizes or need to verify account information.
Legitimate organizations typically don’t include clickable links in unsolicited text messages, especially for account-related actions. When in doubt, don’t click the link—instead, open your banking app directly or visit the official website by typing the URL manually.
Social media platforms give scammers new opportunities to create convincing fake profiles and pages. They might impersonate customer service accounts, create fake giveaways, or send direct messages requesting personal information. These fake sites often use profile pictures and branding that closely resemble legitimate companies.
Unusual sender behavior is another indicator of a scam across all platforms. This includes messages from contacts you haven’t heard from in years, communications from brands you don’t typically interact with, or requests that seem out of character for the supposed sender.
Scammers have become increasingly cunning in creating fake websites that closely mimic legitimate businesses and services. Here are some real-life examples of how cybercriminals use fake websites to victimize consumers:
Scammers exploit your trust in the United States Postal Service (USPS), designing sophisticated fake websites to steal your personal information, payment details, or money. They know you’re expecting a package or need to resolve a delivery issue, making you more likely to enter sensitive information without carefully verifying the site’s authenticity.
USPS-themed smishing attacks arrive as text messages stating your package is delayed, undeliverable, or requires immediate action. Common phrases include “Pay $1.99 to reschedule delivery” or “Your package is held – click here to release.”
Scammers use various URL manipulation techniques to make their fake sites appear official. Watch for these red flags:
Always verify package information and delivery issues through official USPS channels before taking any action on suspicious websites or messages:
Reporting fake USPS websites helps protect others from falling victim to these scams and assists law enforcement in tracking down perpetrators.
Remember that legitimate USPS services are free for standard delivery confirmation and tracking. Any website demanding payment for basic package tracking or delivery should be treated as suspicious and verified through official USPS channels before providing any personal or financial information.
According to the Federal Trade Commission, tech support scams cost Americans nearly $1.5 billion in 2024. These types of social engineering attacks are increasingly becoming sophisticated, making it more important than ever to verify security alerts through official channels.
Sadly, many scammers are misusing the McAfee name to create fake tech support pop-up scams and trick you into believing your computer is infected or your protection has expired, and hoping you’ll act without thinking.
These pop-ups typically appear while you’re browsing and claim your computer is severely infected with viruses, malware, or other threats. They use official-looking McAfee logos, colors, and messaging to appear legitimate to get you to call a fake support number, download malicious software, or pay for unnecessary services.
Learning to detect fake sites and pop-ups protects you from scams. Be on the lookout for these warning signs:
If you see a suspicious pop-up claiming to be from McAfee, here’s exactly what you should do:
To check if your McAfee protection is genuinely active and up-to-date:
Remember, legitimate McAfee software updates and notifications come through the installed program itself, not through random browser pop-ups. Your actual McAfee protection works quietly in the background without bombarding you with alarming messages.
Stay protected by trusting your installed McAfee software and always verifying security alerts through official McAfee channels, such as your installed McAfee dashboard or the official website.
Be prepared and know how to respond quickly when something doesn’t feel right. If you suspect you’ve encountered a fake website, trust your instincts and take these protective steps immediately.
Recognizing fake sites and emails becomes easier with practice. The key is to trust your instincts—if something feels suspicious or too good to be true, take a moment to verify through official channels. With the simple verification techniques covered in this guide, you can confidently navigate the digital world and spot fake sites and emails before they cause harm.
Your best defense is to make these quick security checks a regular habit—verify URLs, look for secure connections, and trust your instincts when something feels off. Go directly to the source or bookmark your most frequently used services and always navigate to them. Enable two-factor authentication on important accounts, and remember that legitimate companies will never ask for sensitive information via email. Maintaining healthy skepticism about unsolicited communications will protect not only your personal information but also help create a safer online environment for everyone.
For the latest information on fake websites and scams and to report them, visit the Federal Trade Commission’s scam alerts or the FBI’s Internet Crime Complaint Center.
The post Ways to Tell if a Website Is Fake appeared first on McAfee Blog.

Chances are, you have more personal information posted online than you think.
In 2024, the U.S. Federal Trade Commission (FTC) reported that 1.1 million identity theft complaints were filed, where $12.5 billion was lost to identity theft and fraud overall—a 25% increase over the year prior.
What fuels all this theft and fraud? Easy access to personal information.
Here’s one way you can reduce your chances of identity theft: remove your personal information from the internet.
Scammers and thieves can get a hold of your personal information in several ways, such as information leaked in data breaches, phishing attacks that lure you into handing it over, malware that steals it from your devices, or by purchasing your information on dark web marketplaces, just to name a few.
However, scammers and thieves have other resources and connections to help them commit theft and fraud—data broker sites, places where personal information is posted online for practically anyone to see. This makes removing your info from these sites so important, from both an identity and privacy standpoint.
Data broker sites are massive repositories of personal information that also buy information from other data brokers. As a result, some data brokers have thousands of pieces of data on billions of individuals worldwide.
What kind of data could they have on you? A broker may know how much you paid for your home, your education level, where you’ve lived over the years, who you’ve lived with, your driving record, and possibly your political leanings. A broker could even know your favorite flavor of ice cream and your preferred over-the-counter allergy medicine thanks to information from loyalty cards. They may also have health-related information from fitness apps. The amount of personal information can run that broadly, and that deeply.
With information at this level of detail, it’s no wonder that data brokers rake in an estimated $200 billion worldwide every year.
Your personal information reaches the internet through six primary methods, most of which are initiated by activities you perform on a daily basis. Understanding these channels can help you make more informed choices about your digital footprint.
When you buy a home, register to vote, get married, or start a business, government agencies create public records that contain your personal details. These records, once stored in filing cabinets, are now digitized, accessible online, and searchable by anyone with an internet connection.
Every photo you post, location you tag, and profile detail you share contributes to your digital presence. Even with privacy settings enabled, social media platforms collect extensive data about your behavior, relationships, and preferences. You may not realize it, but every time you share details with your network, you are training algorithms that analyze and categorize your information.
You create accounts with retailers, healthcare providers, employers, and service companies, trusting them to protect your information. However, when hackers breach these systems, your personal information often ends up for sale on dark web marketplaces, where data brokers can purchase it. The Identity Theft Research Center Annual Data Breach Report revealed that 2024 saw the second-highest number of data compromises in the U.S. since the organization began recording incidents in 2005.
When you browse, shop, or use apps, your online behavior is recorded by tracking pixels, cookies, and software development kits. The data collected—such as your location, device usage, and interests—is packaged and sold to data brokers who combine it with other sources to build a profile of you.
Grocery store cards, coffee shop apps, and airline miles programs offer discounts in exchange for detailed purchasing information. Every transaction gets recorded, analyzed, and often shared with third-party data brokers, who then create detailed lifestyle profiles that are sold to marketing companies.
Data brokers act as the hubs that collect information from various sources to create comprehensive profiles that may include over 5,000 data points per person. Seemingly separate pieces of information become a detailed digital dossier that reveals intimate details about your life, relationships, health, and financial situation.
Legally, your aggregated information from data brokers is used by advertisers to create targeted ad campaigns. In addition, law enforcement, journalists, and employers may use data brokers because the time-consuming pre-work of assembling your data has largely been done.
Currently, the U.S. has no federal laws that regulate data brokers or require them to remove personal information if requested. Only a few states, such as Nevada, Vermont, and California, have legislation that protects consumers. In the European Union, the General Data Protection Regulation (GDPR) has stricter rules about what information can be collected and what can be done with it.
On the darker side, scammers and thieves use personal information for identity theft and other forms of fraud. With enough information, they can create a high-fidelity profile of their victims to open new accounts in their name. For this reason, cleaning up your personal information online makes a great deal of sense.
Understanding efforts to remove personal information, which data types pose the greatest threat, can help you prioritize your removal efforts. Here are the high-risk personal details you should target first, ranked by their potential for harm.
When prioritizing your personal information removal efforts, focus on combinations of data rather than individual pieces. For example, your name alone poses minimal risk, but when combined with your address, phone number, and date of birth, it creates a comprehensive profile that criminals can exploit. Tools such as McAfee Personal Data Cleanup can help you identify and systematically remove these high-risk combinations from data broker sites.
This process takes time and persistence, but services such as McAfee Personal Data Cleanup can continuously monitor for new exposures and manage opt-out requests on your behalf. The key is to first understand the full scope of your online presence before beginning the removal process.
Let’s review some ways you can remove your personal information from data brokers and other sources on the internet.
Once you have found the sites that have your information, the next step is to request that it be removed. You can do this yourself or employ services such as McAfee’s Personal Data Cleanup, which can help manage the removal for you depending on your subscription. It also monitors those sites, so if your info gets posted again, you can request its removal again.
You can request to remove your name from Google search to limit your information from turning up in searches. You can also enable “Auto Delete” in your privacy settings to ensure your data is regularly deleted. Occasionally, deleting your cookies or browsing in incognito mode prevents websites from tracking you. If Google denies your initial request, you can appeal using the same tool, providing more context, documentation, or legal grounds for removal. Google’s troubleshooter tool may explain why your request was denied—either legitimate public interest or newsworthiness—and how to improve your appeal.
It’s important to know that the original content remains on the source website. You’ll still need to contact website owners directly to have your actual content removed. Additionally, the information may still appear in other search engines.
If you have old, inactive accounts that have become obsolete, such as Myspace or Tumblr, you may want to deactivate or delete them entirely. For social media platforms that you use regularly, such as Facebook and Instagram, consider adjusting your privacy settings to keep your personal information to the bare minimum.
If you’ve ever published articles, written blogs, or created any content online, it is a good time to consider taking them down if they no longer serve a purpose. If you were mentioned or tagged by other people, it is worth requesting them to take down posts with sensitive information.
Another way to tidy up your digital footprint is to delete phone apps you no longer use, as hackers are able to track personal information on these and sell it. As a rule, share as little information with apps as possible using your phone’s settings.
After sending your removal request, give the search engine or source website 7 to 10 business days to respond initially, then follow up weekly if needed. If a website owner doesn’t respond within 30 days or refuses your request, you have several escalation options:
For comprehensive guidance on website takedown procedures and your legal rights, visit the FTC’s privacy and security guidance for the most current information on consumer data protection. Direct website contact can be time-consuming, but it’s often effective for removing information from smaller sites that don’t appear on major data broker opt-out lists. Stay persistent, document everything, and remember that you have legal rights to protect your privacy online.
After you’ve cleaned up your data from websites and social platforms, your web browsers may still save personal information, such as your browsing history, cookies, autofill data, saved passwords, and even payment methods. Clearing this information and adjusting your privacy settings helps prevent tracking, reduces targeted ads, and limits the amount of personal data websites can collect about you.
When your home address is publicly available, it can expose you to risks like identity theft, stalking, or targeted scams. Taking steps to remove or mask your address across data broker sites, public records, and even old social media profiles helps protect your privacy, reduce unwanted contact, and keep your personal life more secure.
The cost to remove your personal information from the internet varies, depending on whether you do it yourself or use a professional service. Read the guide below to help you make an informed decision:
Removing your information on your own primarily requires time investment. Expect to spend 20 to 40 hours looking for your information online and submitting removal requests. In terms of financial costs, most data brokers may not charge for opting out; however, other expenses could include certified mail fees for formal removal requests, which range from $3 to $8 per letter, and possibly notarization fees for legal documents. In total, this effort can be substantial when dealing with dozens of sites.
Depending on which paid removal and monitoring service you employ, basic plans typically range from $8 to $25 monthly, while annual plans, which often provide better value, range from $100 to $600. Premium services that monitor hundreds of data broker sites and provide ongoing removal can cost $1,200-$2,400 annually.
The difference in pricing is driven by several factors. This includes the number of data broker sites to be monitored, which could cover more than 200 sites, and the scope of removal requests, which may include basic personal information or comprehensive family protection. The monitoring frequency and additional features, such as dark web monitoring, credit protection, identity restoration support, and insurance coverage, typically command higher prices.
The upfront cost may seem significant, but continuous monitoring provides essential value. A McAfee survey revealed that 95% of consumers’ personal information ends up on data broker sites without their consent. It is possible that after the successful removal of your information, it may reappear on data broker sites without ongoing monitoring. This makes continuous protection far more cost-effective than repeated one-time cleanups.
Services such as McAfee Personal Data Cleanup can prove invaluable, as it handles the initial removal process, as well as ongoing monitoring to catch when your information resurfaces, saving you time and effort while offering long-term privacy protection.
Aside from the services above, comprehensive protection software can help safeguard your privacy and minimize your exposure to cybercrime with these offerings, such as:
So while it may seem like all this rampant collecting and selling of personal information is out of your hands, there’s plenty you can do to take control. With the steps outlined above and strong online protection software in place, you can keep your personal information more private and secure.
Unlike legitimate data broker sites, the dark web operates outside legal boundaries where takedown requests don’t apply. Rather than trying to remove information that’s already circulating, you can take immediate steps to reduce the potential harm and focus on preventing future exposure. A more effective approach is to treat data breaches as ongoing security issues rather than one-time events.
Both the FTC and Cybersecurity and Infrastructure Security Agency have released guidelines on proactive controls and continuous monitoring. Here are the key steps of those recommendations:
As you go about removing your information from the internet, it is important to set realistic expectations. Several factors may limit how completely you can remove personal data from internet sources:
While some states like California have stronger consumer privacy rights, most data removal still depends on voluntary compliance from companies.
Removing your personal information from the internet takes effort, but it’s one of the most effective ways to protect yourself from identity theft and privacy violations. The steps outlined above provide you with a clear roadmap to systematically reduce your online exposure, from opting out of data brokers to tightening your social media privacy settings.
This isn’t a one-time task but an ongoing process that requires regular attention, as new data appears online constantly. Rather than attempting to completely erase your digital presence, focus on reducing your exposure to the most harmful uses of your personal information. Services like McAfee Personal Data Cleanup can help automate the most time-consuming parts of this process, monitoring high-risk data broker sites and managing removal requests for you.
The post How to Remove Your Personal Information From the Internet appeared first on McAfee Blog.

Data Privacy Week is here, and there’s no better time to shine a spotlight on one of the biggest players in the personal information economy: data brokers. These entities collect, buy, and sell hundreds—sometimes thousands—of data points on individuals like you. But how do they manage to gather so much information, and for what purpose? From your browsing habits and purchase history to your location data and even more intimate details, these digital middlemen piece together surprisingly comprehensive profiles. The real question is: where are they getting it all, and why is your personal data so valuable to them? Let’s unravel the mystery behind the data broker industry.
Data brokers aggregate user info from various sources on the internet. They collect, collate, package, and sometimes even analyze this data to create a holistic and coherent version of you online. This data then gets put up for sale to nearly anyone who’ll buy it. That can include marketers, private investigators, tech companies, and sometimes law enforcement as well. They’ll also sell to spammers and scammers. (Those bad actors need to get your contact info from somewhere — data brokers are one way to get that and more.)
And that list of potential buyers goes on, which includes but isn’t limited to:
These companies and social media platforms use your data to better understand target demographics and the content with which they interact. While the practice isn’t unethical in and of itself (personalizing user experiences and creating more convenient UIs are usually cited as the primary reasons for it), it does make your data vulnerable to malicious attacks targeted toward big-tech servers.
Most of your online activities are related. Devices like your phone, laptop, tablets, and even fitness watches are linked to each other. Moreover, you might use one email ID for various accounts and subscriptions. This online interconnectedness makes it easier for data brokers to create a cohesive user profile.
Mobile phone apps are the most common way for data brokerage firms to collect your data. You might have countless apps for various purposes, such as financial transactions, health and fitness, or social media.
A number of these apps usually fall under the umbrella of the same or subsidiary family of apps, all of which work toward collecting and supplying data to big tech platforms. Programs like Google’s AdSense make it easier for developers to monetize their apps in exchange for the user information they collect.
Data brokers also collect data points like your home address, full name, phone number, and date of birth. They have automated scraping tools to quickly collect relevant information from public records (think sales of real estate, marriages, divorces, voter registration, and so on).
Lastly, data brokers can gather data from other third parties that track your cookies or even place trackers or cookies on your browsers. Cookies are small data files that track your online activities when visiting different websites. They track your IP address and browsing history, which third parties can exploit. Cookies are also the reason you see personalized ads and products.
Data brokers collate your private information into one package and sell it to “people search” websites. As mentioned above, practically anyone can access these websites and purchase extensive consumer data, for groups of people and individuals alike.
Next, marketing and sales firms are some of data brokers’ biggest clients. These companies purchase massive data sets from data brokers to research your data profile. They have advanced algorithms to segregate users into various consumer groups and target you specifically. Their predictive algorithms can suggest personalized ads and products to generate higher lead generation and conversation percentages for their clients.
We tend to accept the terms and conditions that various apps ask us to accept without thinking twice or reading the fine print. You probably cannot proceed without letting the app track certain data or giving your personal information. To a certain extent, we trade some of our privacy for convenience. This becomes public information, and apps and data brokers collect, track, and use our data however they please while still complying with the law.
There is no comprehensive privacy law in the U.S. on a federal level. This allows data brokers to collect personal information and condense it into marketing insights. While not all methods of gathering private data are legal, it is difficult to track the activities of data brokers online (especially on the dark web). As technology advances, there are also easier ways to harvest and exploit data.
As of March 2024, 15 states in the U.S. have data privacy laws in place. That includes California, Virginia, Connecticut, Colorado, Utah, Iowa, Indiana, Tennessee, Oregon, Montana, Texas, Delaware, Florida, New Jersey, and New Hampshire.[i] The laws vary by state, yet generally, they grant rights to individuals around the collection, use, and disclosure of their personal data by businesses.
However, these laws make exceptions for certain types of data and certain types of collectors. In short, these laws aren’t absolute.
Some data brokers let you remove your information from their websites. There are also extensive guides available online that list the method by which you can opt-out of some of the biggest data brokering firms. For example, a guide by Griffin Boyce, the systems administrator at Harvard University’s Berkman Klein Center for Internet and Society, provides detailed information on how to opt-out of a long list of data broker companies.
Yet the list of data brokers is long. Cleaning up your personal data online can quickly eat up your time, as it requires you to reach out to multiple data brokers and opt-out.
Rather than removing yourself one by one from the host of data broker sites out there, you have a solid option: our Personal Data Cleanup.
Personal Data Cleanup scans data broker sites and shows you which ones are selling your personal info. It also provides guidance on how you can remove your data from those sites. And if you want to save time on manually removing that info, you have options. Our McAfee+ Advanced and Ultimate plans come with full-service Personal Data Cleanup, which sends requests to remove your data automatically.
If the thought of your personal info getting bought and sold in such a public way bothers you, our Personal Data Cleanup can put you back in charge of it.
[i] https://pro.bloomberglaw.com/insights/privacy/state-privacy-legislation-tracker/
The post How Data Brokers Sell Your Identity appeared first on McAfee Blog.

McAfee threat researchers have identified several consumer brands and product categories most frequently used by cybercriminals to trick consumers into clicking on malicious links in the first weeks of this holiday shopping season. As holiday excitement peaks and shoppers hunt for the perfect gifts and amazing deals, scammers are taking advantage of the buzz. The National Retail Federation projects holiday spending will reach between $979.5 and $989 billion this year, and cybercriminals are capitalizing by creating scams that mimic the trusted brands and categories consumers trust. From October 1 to November 12, 2024, McAfee safeguarded its customers from 624,346 malicious or suspicious URLs tied to popular consumer brand names – a clear indication that bad actors are exploiting trusted brand names to deceive holiday shoppers.
McAfee’s threat research also reveals a 33.82% spike in malicious URLs targeting consumers with these brands’ names in the run-up to Black Friday and Cyber Monday. This rise in fraudulent activity aligns with holiday shopping patterns during a time when consumers may be more susceptible to clicking on offers from well-known brands like Apple, Yeezy, and Louis Vuitton, especially when deals seem too good to be true – pointing to the need for consumers to stay vigilant, especially with offers that seem unusually generous or come from unverified sources.
McAfee threat researchers have identified a surge in counterfeit sites and phishing scams that use popular luxury brands and tech products to lure consumers into “deals” on fake e-commerce sites designed to appear as official brand pages. While footwear and handbags were identified as the top two product categories exploited by cybercrooks during this festive time, the list of most exploited brands extends beyond those borders:
By mimicking trusted brands like these, offering unbelievable deals, or posing as legitimate customer service channels, cybercrooks create convincing traps designed to steal personal information or money. Here are some of the most common tactics scammers are using this holiday season:
With holiday shopping in full swing, it’s essential for consumers to stay one step ahead of scammers. By understanding the tactics cybercriminals use and taking a few precautionary measures, shoppers can protect themselves from falling victim to fraud. Here are some practical tips for safe shopping this season:
McAfee’s threat research team analyzed malicious or suspicious URLs that McAfee’s web reputation technology identified as targeting customers, by using a list of key company and product brand names—based on insights from a Potter Clarkson report on frequently faked brands—to query the URLs. This methodology captures instances where users either clicked on or were directed to dangerous sites mimicking trusted brands. Additionally, the team queried anonymized user activity from October 1st through November 12th.
The image below is a screenshot of a fake / malicious / scam site: Yeezy is a popular product brand formerly from Adidas found in multiple Malicious/Suspicious URLs. Often, they present themselves as official Yeezy and/or Adidas shopping sites.
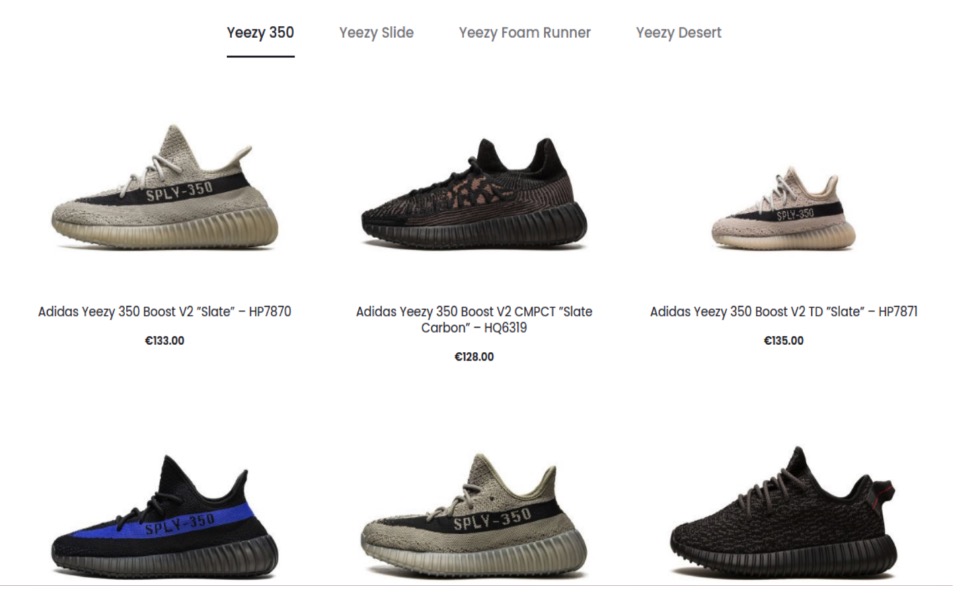
The image below is a screenshot of a fake / malicious / scam site: The Apple brand was a popular target for scammers. Many sites were either knock offs, scams, or in this case, a fake customer service page designed to lure users into a scam.
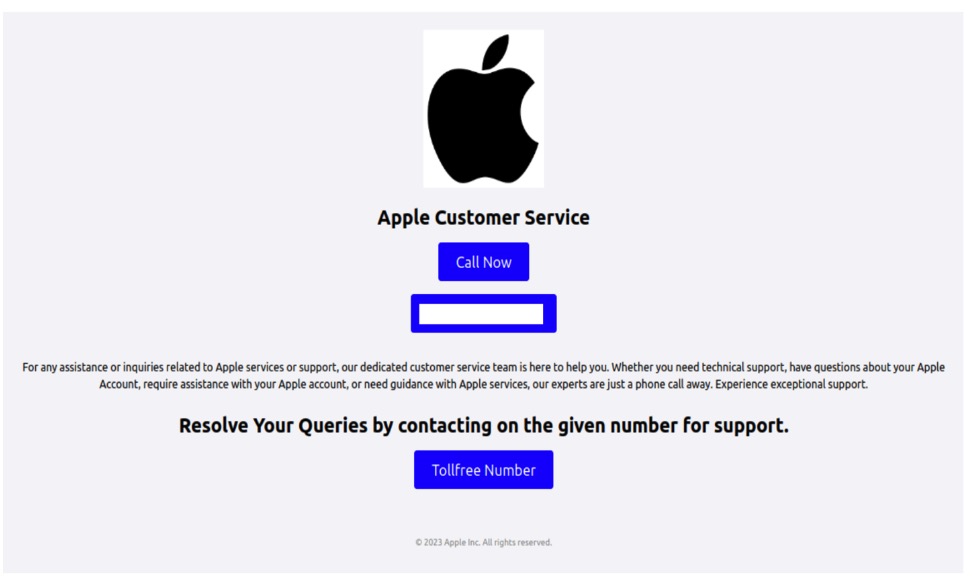
The image below is a screenshot of a fake / malicious / scam site: This particular (fake) Apple sales site used Apple within its URL and name to appear more official. Oddly, this site also sells Samsung Android phones.
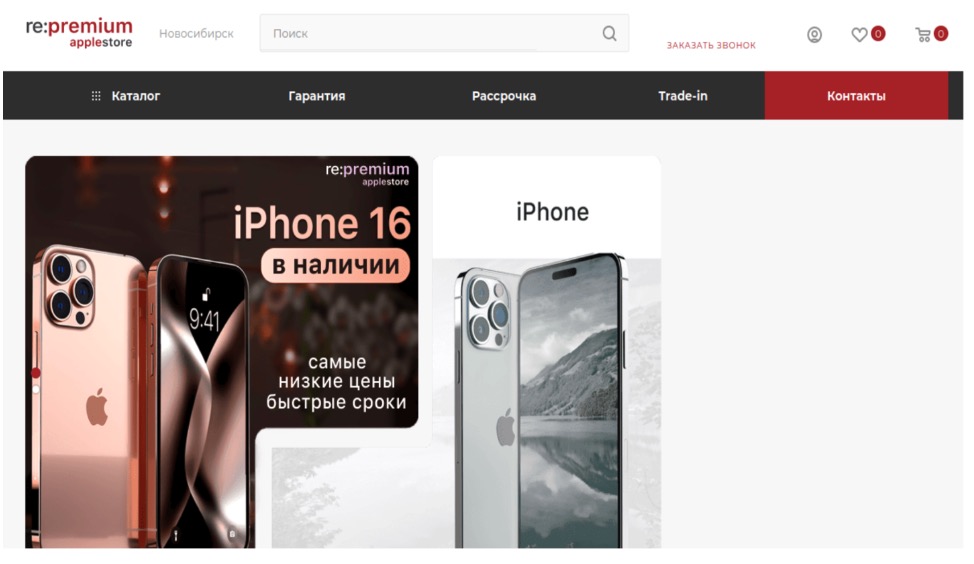
The image below is a screenshot of a fake / malicious / scam site: This site, now taken down, is a scam site purporting to sell Nike shoes.
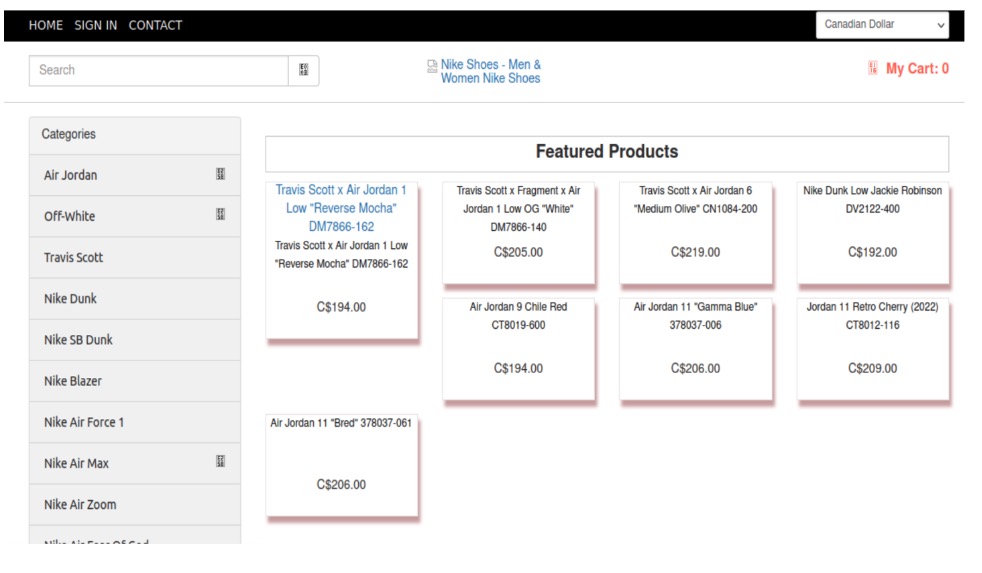
The image below is a screenshot of a fake / malicious / scam site: Louis Vuitton is a popular brand for counterfeit and scams. Particularly their handbags. Here is one site that was entirely focused on Louis Vuitton Handbags.
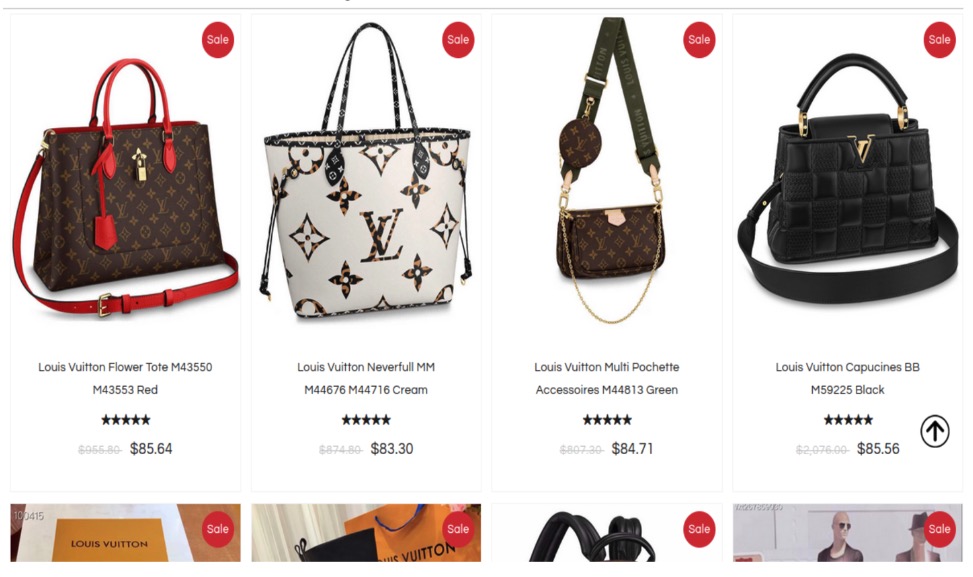
The image below is a screenshot of a fake / malicious / scam site: This site presents itself as the official Louis Vuitton site selling handbags and clothes.
The image below is a screenshot of a fake / malicious / scam site: This site uses too-good-to-be-true deals on branded items including this Louis Vuitton Bomber jacket.

The image below is a screenshot of a fake / malicious / scam site: Rolex is a popular watch brand for counterfeits and scams. This site acknowledges it sells counterfeits and makes no effort to indicate this on the product.
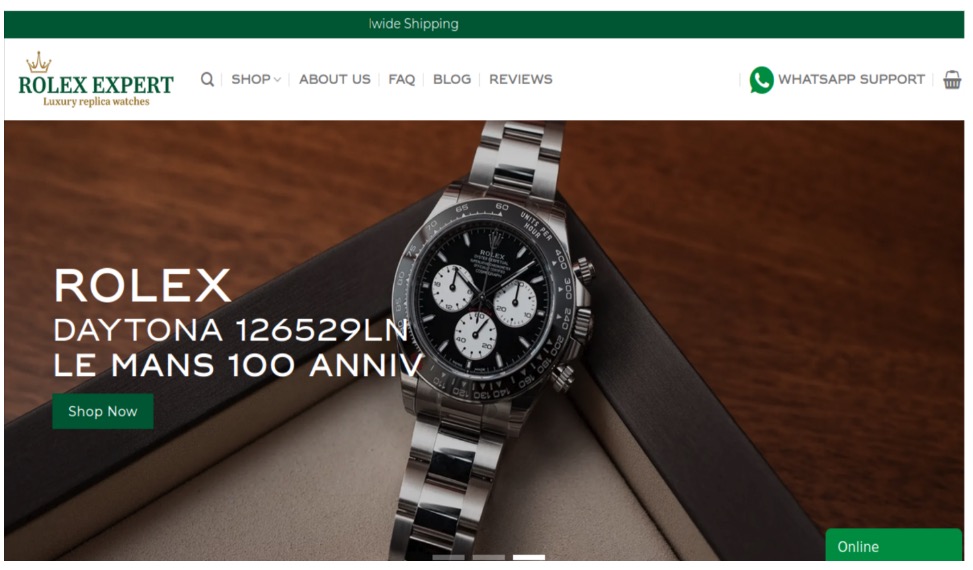
The post This Holiday Season, Watch Out for These Cyber-Grinch Tricks Used to Scam Holiday Shoppers appeared first on McAfee Blog.

If you think your Gmail account’s been hacked, you’ll want to act. And act quickly.
The fact is that your email has all manner of personal info in there. Receipts, tax correspondence, medical info, and so on. With a hacked account, that info might get deleted, shared, or used against you for identity theft.
Luckily, Google has mechanisms in place to restore a hacked Gmail account. We’ll walk through the steps here — and a few others that can keep you secure in the long term after you have your account back.
Several things can tip you off, including:
With varying degrees of certainty, those are some signs that your account has been hacked.
Also, many people have a Google Account linked with their Gmail password and login. Beyond email, that might include files in Google Drive, photos, a YouTube account, and other features that contain personal info. In those cases, that only increases the potential harm of a hacked account.
Additionally, services like Google Pay and Google Play complicate matters more in the event of a hacked account because they contain financial info.
If you see any unusual changes in those apps or services, that might be a sign of a hacked account as well.
If you think someone else has changed your password or deleted your account, head to Google’s account recovery page. It’ll take you through a multi-step process to restore your account.
With that, you’ll want to do some quick prep. First, do your best to begin the recovery process with a device that you typically use to access your account. Also, if possible, do it in a location where you typically access your account. This provides Google with identifiers that you are who you say you are.
After that, gather up your Gmail account passwords, old and current. The recovery page will ask for them, along with other questions. Do your best to answer each question the very best you can. There’s no penalty for a wrong answer and the more info you can provide, the better.
If you can log into your account, yet worry it’s been hacked, take these steps:
Next, run a virus scan on your device. Your password might have gotten compromised in one of several ways, including malware. This can remove any malware that might be spying on your device (and your passwords).
At this point, create a new password that’s strong and unique. Use at least 14 characters using a mix of upper- and lowercase letters, symbols, and numbers. Or have a password manager do that work for you.
And finally, set two-factor verification on your account if you aren’t already using it. This makes your account far tougher to hack, as two-factor verification requires a unique code to log in. One that only you receive. And just like with your password, never share your unique code. Anyone asking for it is a scammer.
By taking the steps we just covered, you’ve done two important things that can protect you moving forward. One is setting up a strong, unique password. The second is using two-factor verification.
The next thing is to get comprehensive online protection in place. Protection like you’ll find in our McAfee+ plans offers several features that can keep you and your accounts safe.
Once again, your password got compromised one way or another. It could have been spyware on your device. It could have been a phishing attack. It could have been a data breach. The list goes on. However, we refer to it as comprehensive online protection because it’s exactly that. In addition to antivirus, our McAfee+ plans have dozens of features that can protect your devices, identity, and privacy.
For example:
The important thing is this: if you think your Gmail account got hacked, act quickly. You might have much more than just your email linked to that account. Files, photos, and finances might be tied to it as well.
Even if something looks just slightly off, act as if your account got hacked. Log in, change your password, establish two-step verification if you haven’t, and take the other steps mentioned above. Above and beyond your email and all the personal info packed in there, your account can give a hacker access to plenty more.
The post How to Reset Your Gmail Password After Being Hacked appeared first on McAfee Blog.

You crack open your credit card statement and something seems … off. Maybe it’s a couple of small online purchases that make you think, “Hmm, that’s strange.” Or maybe a statement shows up in your mailbox — one for a card that you don’t own at all. That calls for a huge “What the heck???” Sure enough, you’re looking at cases of identity fraud and theft.
And there’s a difference between identity fraud and identity theft. It’s subtle. And because of that, they often get used interchangeably. Each one can really sting but in different ways.
So, put simply, identity fraud involves stealing from an existing account. Identity theft means that someone used your personal info to impersonate you in some way, such as opening new accounts in your name.
Each year, the U.S. Federal Trade Commission (FTC) publishes a data book that collects consumer reports of fraud, identity theft, and other similar crimes. Using the most recent data from the FTC, we can plot what the top forms of identity theft and fraud look like.
Credit cards
By far the top form of identity theft and fraud. As mentioned in the examples above, these can include crooks who string out several small purchases over time. All in the hope that the cardholder will overlook it. It can also include a one-whopper of a purchase for a big-ticket item. Here, the crook knows the card will likely get canceled quickly afterward. It’s a one-and-done deal.
Loans and leases
Second, we have loans and leases. This can range from student loans, personal loans, and auto loans, and to real estate rentals as well. Common across them all is someone impersonating you to take them out or tap into their funds in some way.
Bank accounts
Here, the creation of totally new accounts leads the way in this category. As we described above, that’s a form of identity theft. Yet identity fraud accounts for a noticeable chuck, which includes account takeovers. In these cases, crooks siphon off funds via debit cards, Electronic Funds Transfer (ETF), and other forms of withdrawal and transfer.
ID and government benefits
This covers cases where crooks use stolen personal info to get IDs. That includes driver’s licenses, passports, and other government documentation. Further, this category also encompasses the theft of government-issued benefits ranging from medical assistance to veteran’s pay.
Tax returns
While all forms of identity theft and fraud can pack a punch, this type hits particularly hard because it involves your SSN. Around tax time, scammers with access to SSNs will file bogus returns, all with the aim of claiming the refund for themselves.
Utilities
Largely, this involves people buying cell phones and opening new mobile accounts along with them. Yet it also includes people opening other utilities in other people’s names. Indeed, crooks will scam their way into getting free electricity, water, gas, and yes…cable TV.
Although these forms don’t top the list in terms of reports, they still bear mentioning. They’re serious enough, and they can go undetected for some time before their victims find out.
Medical identity theft
In this form, an imposter receives care, medications, or medical devices in someone else’s name. They might pass off phony documentation to the care provider involved, the insurance company that pays for the care, or a combination of the two. A few things can happen as a result. It can impact the care you can get and the benefits you can use. In extreme cases, the thief’s health info can get mixed in with yours and impact your care. Medical identity theft is a good reason to closely review all the medical and insurance statements you get.
Child identity theft
Imagine your child about to rent a first apartment. The property management company runs a credit check, only to find a horrendous credit rating. But how? An identity thief has been using your child’s identity for years now. After all, what parent thinks, “I really should run a credit report on my kindergartener.” And that’s fair. However, signing up your child for identity is a sound move. It can help spot if your child’s identity got stolen.
1) Notify the companies and institutions involved and consider a credit freeze.
Whether you spot a curious charge on your bank statement or you discover what looks like a fraudulent account in your credit monitoring service, let the bank or business involved know you suspect fraud. With a visit to their website, you can track down the appropriate number to call and get the investigation process started.
In the meantime, consider putting a security freeze in place. A security freeze service prevents others from opening new credit, bank, and utility accounts in your name. It won’t hit your credit score, and you can unfreeze it when needed. You’ll find this feature in our McAfee+ plans as well.
2) File a police report.
Some businesses will require you to file a local police report to acquire a case number to complete your claim. Beyond that, filing a report is still a good idea. Identity theft is still theft, and reporting it provides an official record of it.
Should your case of identity theft lead to someone impersonating you or committing a crime in your name, filing a police report right away can help you clear your name down the road. Likewise, save any evidence you have, such as statements or documents associated with the theft. They can help you clean up your record as well.
3) Contact the Federal Trade Commission (FTC).
The FTC’s identity theft website is a fantastic resource should you find yourself in need. Above and beyond simply reporting the theft, the FTC can provide you with a step-by-step recovery plan—and even walk you through the process if you create an account with them. Additionally, reporting theft to the FTC can prove helpful if debtors come knocking to collect on any bogus charges in your name. You can provide them with a copy of your FTC report and ask them to stop.
4) Contact the IRS, if needed.
If you receive a notice from the IRS that someone used your identity to file a tax return in your name, follow the information provided by the IRS in the notice. From there, you can file an identity theft affidavit with the IRS. If the notice mentions that you were paid by an employer you don’t know, contact that employer as well and let them know of possible fraud — namely that someone has stolen your identity and that you don’t truly work for them.
Also, be aware that the IRS has specific guidelines as to how and when they will contact you. As a rule, they will most likely contact you via physical mail delivered by the U.S. Postal Service. (They won’t call, nor will they call and apply harassing pressure tactics — only scammers do that.) Identity-based tax scams are a topic all of their own, and for more on it, you can check out this article on tax scams and how to avoid them.
5) Continue to monitor your credit report, invoices, and statements.
Another downside of identity theft is that it can mark the start of a long, drawn-out affair. One instance of theft can possibly lead to another, so even what may appear to be an isolated bad charge on your credit card calls for keeping an eye on your identity. Many of the tools you would use up to this point still apply, such as checking up on your credit reports, maintaining fraud alerts as needed, in addition to reviewing your accounts closely.
Several features in our McAfee+ plans can do this work, and quite a bit more, for you:
The post What Are the 6 Types of Identity Theft appeared first on McAfee Blog.

For millions of people, it’s not a workday without it — video conferencing. And plenty of business gets done that way, which has made conferencing a target for hackers. That then begs the important question, how secure is video conferencing?
The answer is pretty secure if you’re using a reputable service. Yet you can take further steps to keep hackers and party crashers out of your meetings.
Hackers and party crashers are likely motivated by one of two things: financial gain or mischief.
Given that some meetings involve confidential or sensitive info, someone might have financial motivation to join in, spy on, or record the meeting. Recently, we saw the lengths at least one AI company went to when it spied on a competitor’s video conference call.[i]
And of course, some bad actors want to cause a disruption. As we saw in recent years, they’ll barge right into a meeting and create a ruckus with rude speech and other antics.
Falling somewhere in between, some hackers might try to intrude on a meeting and slip a malware-laden attachment into chat.[ii] For one, that can lead to a major disruption. And in a business context, financial disruption as well.
How do they pull it off? The typical avenues of attack apply. They might use stolen or hijacked accounts. The meeting was inadvertently set to “public,” allowing anyone with a link to join. Otherwise, they might compromise a victim’s device to piggyback their way in.
Use a service with end-to-end encryption.
Put simply, end-to-end encryption provides a solid defense against prying eyes. With it in place, this form of encryption makes it particularly difficult for hackers to tap into the call and the data shared within it. Secure video conferencing should use 256-bit AES GCM encryption for audio and video, and for sharing of screens, whiteboard apps, and the like. On a related note, read the service’s privacy policy and ensure that its privacy, security, and data measures fit your needs.
Make your meetings private and protect them with a password.
Keep the uninvited out. First, setting your meeting to private (invitees only) will help keep things secure. Some apps also provide a notification to the meeting organizer when an invite gets forwarded. Use that feature if it’s available. Also, a password provides another hurdle for a hacker or bad actor to clear. Use a fresh one for each meeting.
Use the waiting room.
Many services put attendees into a waiting room before they enter the meeting proper. Use this feature to control who comes in and out.
Block users from taking control of the screen.
Welcome or unwelcome, you can keep guests from taking over the screen. Select the option to block everyone except the host (you) from screen sharing.
Turn on automatic updates on your conferencing app.
By turning on automatic updates, you’ll get the latest security patches and enhancements for your video conferencing tool as soon as they become available.
Get wise to phishing scams.
Some interlopers make it into meetings by impersonating others. Just as bad actors use phishing emails and texts to steal personal financial info, they’ll use them to steal company credentials as well. Our Phishing Scam Protection Guide can show you how to steer clear of these attacks.
Use online protection software.
Comprehensive online protection software like ours can make for safer calls in several ways. For one, it protects you against malware attacks, such as if a bad actor tries to slip a sketchy download into your meeting. Further, it includes a password manager that creates and stores strong, unique passwords securely. This can help increase the security of your video conferencing account.
This is a new one. AI deepfake technology continues to evolve, we find ourselves at the point where scammers can create AI imposters in real time.
We’ve seen them use this technology in romance scams, where scammers take on entirely new looks and voices on video calls. And we’ve seen at least one group of scammers bilk a company out of $25 million with deepfaked executives on a call.[iii]
Strange as it might sound, this kind of deepfake technology is possible today. And realizing that fact is the first step toward prevention. Next, that calls for extra scrutiny.
Any time-sensitive info or sums of money are involved, get confirmation of the request. Place a phone call to the person after receiving the request to ensure it’s indeed legitimate. Better yet, meet the individual in person if possible. In all, contact them outside the email, message, or call that initially made the request to ensure you’re not dealing with an imposter.
With the right provider and right steps in place, video calls can be quite secure. Use a solution that offers end-to-end encryption, keep your app updated for the latest security measures, and lock down the app’s security settings. Also, recognize that AI has changed the way we look at just about everything online — including people on the other side of the screen. As we’ve seen, AI imposters on calls now fall into the realm of possibility. A costly one at that.
[i] https://www.nytimes.com/2023/08/07/technology/ai-start-ups-competition.html
[ii] https://www.pcmag.com/news/hackers-circulate-malware-by-breaking-into-microsoft-teams-meetings
[iii] https://www.cnn.com/2024/02/04/asia/deepfake-cfo-scam-hong-kong-intl-hnk/index.html
The post How Secure is Video Conferencing? appeared first on McAfee Blog.

Before your phone gets lost or stolen, put some basic steps in place.
You’ll want to act quickly, so preparation is everything. With the right measures, you can find it, recover it, or even erase it if needed. These steps can get you set up so you can do exactly that.
Lock your phone.
Locking your phone is one of the most basic smartphone security measures you can take. Trouble is, few of us do it. Our recent global research showed that only 56% of adults said that they protect their smartphone with a password, passcode, or other form of lock.[i] In effect, an unlocked phone is an open book to anyone who finds or steals a phone
Setting up a lock screen is easy. It’s a simple feature found on iOS and Android devices. iPhones and Androids have an auto-lock feature that locks your phone after a certain period of inactivity. Keep this time on the low end, one minute or less, to help prevent unauthorized access.
We suggest using a six-digit PIN or passcode rather than using a gesture to unlock your phone. They’re more complex and secure. Researchers proved as much with a little “shoulder surfing” test. They looked at how well one group of subjects could unlock a phone after observing the way another group of subjects unlocked it.[ii]
Turn on “Find My Phone.”
Another powerful tool you have at your disposal is the Find My Phone feature made possible thanks to GPS technology. The “find my” feature can help you pinpoint your phone if your lost or stolen phone has an active data or Wi-Fi connection and has its GPS location services enabled. Even if the phone gets powered down or loses connection, it can guide you to its last known location.
Setting up this feature is easy. Apple offers a comprehensive web page on how to enable and use their “Find My” feature for phones (and other devices too). Android users can get a step-by-step walkthrough on Google’s Android support page as well.
Back up your stuff in the cloud.
Thanks to cloud storage, you might be able to recover your photos, files, apps, notes, contact info, and more if your phone is lost or stolen. Android owners can learn how to set up cloud backup with Google Drive here, and iPhone users can learn the same for iCloud here.
Write down your phone’s unique ID number.
Here are a couple of acronyms. IMEI (International Mobile Equipment Identity) or MEID (Mobile Equipment Identifier) are two types of unique ID numbers assigned to smartphones. Find yours and write it down. In case of loss or theft, your mobile carrier, police department, or insurance provider might ask for the info to assist in its return or reimbursement for loss.
Beyond digital security measures, plenty of loss and theft prevention falls on you. Treat your phone like the desirable item it is. That’s a big step when it comes to preventing theft.
Keep your phone close.
And by close, we mean on your person. It’s easy to leave your phone on the table at a coffee shop, on a desk in a shared workspace, or on a counter when you’re shopping. Thieves might jump on any of these opportunities for a quick snatch-and-grab. You’re better off with your phone in your pocket or zipped up in a bag that you keep close.
Secure your bags and the devices you carry in them.
Enterprising thieves will find a way. They’ll snatch your bag while you’re not looking. Or they might even slice into it with a knife to get what’s inside, like your phone.
Keep your bag or backpack close. If you’re stopping to grab a bite to eat, sling the handles through a chair leg. If you have a strong metal carabiner, you can use that too. Securing your bag like that can make it much tougher for a thief to walk by and swipe it. For extra security, look into a slash-resistant bag.
If you have a credit card and ID holder attached to the back of your phone, you might want to remove your cards from it. That way, if your phone gets snatched, those important cards won’t get snatched as well.
In the event of your phone getting lost or stolen, a combination of device tracking, device locking, and remote erasing can help protect your phone and the data on it.
Different device manufacturers have different ways of going about it. But the result is the same — you can prevent others from using your phone, and even erase it if you’re truly worried that it’s in the wrong hands or gone for good. Apple provides iOS users with a step-by-step guide, and Google offers up a guide for Android users as well.
Apple’s Find My app takes things a step further. Beyond locating a lost phone or wiping it, Find My can also mark the item as lost, notify you if you’ve left it behind, or trigger a sound to help you locate it. (A huge boon in that couch cushion scenario!) Drop by Apple’s page dedicated to the Find My app for more details on what you can do on what devices, along with instructions how.
With preparation and prevention, you can give yourself reassurance if your phone gets lost or stolen. You have plenty of recovery options, in addition to plenty of ways to prevent bad actors from getting their hands on the sensitive info you keep on it.
[i] https://www.mcafee.com/content/dam/consumer/en-us/docs/reports/rp-connected-family-study-2022-global.pdf
[ii] https://arxiv.org/abs/1709.04959
The post What Should I do If My Phone Gets Stolen or Lost? appeared first on McAfee Blog.

Ever take a look at an ATM and feel like something’s off? You might have come across an ATM skimmer.
It works like this… A crook tampers with an ATM by attaching a physical device that skims card info as cards people grab or deposit money. From there, a keypad overlay or tiny pinhole camera captures your PIN as people tap it in. And with that info, the crook has everything they need to create several counterfeit cards.
Of course, that thief has to transfer that info. In some cases, the thief creeps back, removes the skimming device, downloads your data, and burns it to a blank ATM card. More sophisticated skimmers are connected, so thieves can download stolen info from the skimmer and then use that info to buy stuff online. Either way, a skimmer can take a big chunk out of your bank account.
However, you have ways of spotting these sketchy ATMs. And yet, there are more ways to protect your finances if you fall victim to a carefully concealed skimmer.
Spotting a hacked ATM can get a bit tricky, yet you can look for a few signs. Generally speaking, ATMs are sturdy by design. If a card reader or keypad wiggles at all or the keypad feels too spongy or sticks when you tap the buttons, you might be looking at a hacked ATM. Also keep an eye out for extra pieces of plastic stuck to the ATM, which can be places where a crook has concealed a camera. Often, they’ll disguise cameras in brochure holders and overhead lights.
Another clue of a hacked ATM — scanners and other components that don’t match the color and style of the machine. In all, anything that looks tacked on or out of place gives you a good reason to use another ATM.
To protect yourself further, follow these tips:
Be choosy.
While out and about, consider using ATMs installed at a bank. These are watched more closely than ATMs in public places, which makes them harder to tamper with.
Cover the keypad when entering your PIN.
Thieves need your card number and your PIN to access your account with a copycat card. By covering the keypad, you prevent cameras and onlookers from seeing your PIN.
Check your bank and credit card statements often.
If your card does get skimmed, acting quickly counts. Thieves can quickly rack up purchases and out a chunk of your account. Banks typically watch for fraud and will contact you about unusual activity.
Better yet, you can keep a closer eye on your accounts yourself. Our McAfee+ plans offer several types of account and transaction monitoring. Together, they can alert to strange transactions across bank, credit, retirement, and other accounts. They can also alert you if any of your info at the bank gets changed, which helps prevent account takeovers.
The post What is ATM Skimming? appeared first on McAfee Blog.

Identity theft is a pervasive threat in today’s digital age, with various forms that can wreak havoc on individuals’ lives. In 2023, the Federal Trade Commission’s Consumer Sentinel Network received more than 5.39 million consumer reports, with 19% of those reports attributed to identity theft.
Understanding the types of identity theft is crucial for safeguarding personal information and financial well-being. From the insidious tactics of new account fraud to the alarming consequences of medical identity theft, each method poses distinct risks and challenges. Here are six types of the most common forms of identity theft.
New Account Fraud
Using another’s personal identifying information to obtain products and services using that person’s good credit standing. This fraud often requires the use of the victim’s Social Security number. Opening new utility, cell phone, and/or credit card accounts are the most prevalent forms of new account fraud.
Account Takeover Fraud
Using another person’s account numbers, such as a credit card number, to obtain products and services using that person’s existing accounts or extracting funds from a person’s bank account.
Criminal Identity Theft
Someone commits a crime under another person’s name. The thief, in the act of the crime or upon arrest, poses as the identity theft victim. Often the perpetrator will have a fake ID with the victim’s information but the imposter’s picture.
Medical Identity Theft
Medical identity theft occurs when someone uses a person’s name and/or insurance information—without the person’s knowledge or consent—to obtain medical services or goods, or to make false claims for medical goods or services. Medical identity theft frequently results in erroneous entries being put into the victim’s medical records, which in turn may lead to inappropriate and potentially life-threatening decisions by medical staff.
Business or Commercial Identity Theft
Using a business’s name to obtain credit or even billing those businesses’ clients for products and services. Perpetrators who commit business identity theft are often insiders — current or ex-employees — with direct access to operational documentation, who pad the books in favor of their scheming.
Identity Cloning
This type encompasses all forms of identity theft. The thief is actually living and functioning as the victim on purpose. They may be hiding in plain sight due to the fact they are running from the law, evading child support or they could be mentally ill.
It is important to observe basic security precautions to protect your identity. To protect your identity from theft, regularly monitor your financial accounts for suspicious activity and report any discrepancies immediately. Safeguard personal information by avoiding sharing sensitive data on insecure websites or over unsecured Wi-Fi networks. Utilize strong, unique passwords for each online account and enable multi-factor authentication whenever possible. Finally, be cautious of phishing attempts and never click on suspicious links or provide personal information in response to unsolicited communications.
Check out our blog post on the top signs of identity theft for further advice on what to do if you feel you may be at risk. Also consider an identity theft protection product, like McAfee+, that can provide greater peace of mind through 24/7 identity monitoring and alerts, plus up to $2 million in identity theft coverage.
The post How to Identify the Different Forms of Identity Theft appeared first on McAfee Blog.

In today’s interconnected world, our mobile devices serve as essential tools for communication, productivity, and entertainment. However, for some tech-savvy users, the allure of unlocking the full potential of their devices through jailbreaking (for iOS) or rooting (for Android) can be tempting. While these processes offer users greater control and customization over their devices, they also raise significant questions about security implications.
To “jailbreak” means to allow the phone’s owner to gain full access to the root of the operating system and access all the features. Jailbreaking is the process of removing the limitations imposed by Apple and associated carriers on devices running the iOS operating system. Jailbroken phones came into the mainstream when Apple first released their iPhone and it was only on AT&T’s network. Users who wanted to use an iPhone with other carriers were not able to unless they had a jailbroken iPhone.
Similar to jailbreaking, “rooting” is the term for the process of removing the limitations on a mobile or tablet running the Android operating system. By gaining privileged control, often referred to as “root access,” over an Android device’s operating system, users can modify system files, remove pre-installed bloatware, install custom ROMs, and unlock features not accessible on stock devices.
Rooting or jailbreaking grants users deeper access to the device’s operating system, allowing for extensive customization of the user interface, system settings, and even hardware functionality. Advanced users can optimize system performance, remove unnecessary bloatware, and tweak settings to improve battery life, speed, and responsiveness.
However, hacking your device potentially opens security holes that may have not been readily apparent or undermines the device’s built-in security measures. Jailbroken and rooted phones are much more susceptible to viruses and malware because users can avoid Apple and Google application vetting processes that help ensure users are downloading virus-free apps.
In addition to security vulnerabilities, hacking your device may lead to a voided manufacturer’s warranty, leaving you without official support for repairs or replacements. Altering the device’s operating system can also lead to instability, crashes, and performance issues, especially if incompatible software or modifications are installed.
While rooting or jailbreaking may offer users enticing opportunities for customization and optimization of their mobile devices, the associated risks cannot be overlooked. By circumventing built-in security measures, users expose their devices to potential security vulnerabilities, making them more susceptible to viruses and malware. Ultimately, the decision to root or jailbreak a mobile device should be made with careful consideration of the trade-offs involved, as the security risks often outweigh the benefits.
When thinking about mobile security risks, consider adding reputable mobile security software to your device to augment the built-in security measures. These security solutions provide real-time scanning and threat detection capabilities, helping to safeguard sensitive data and maintain the integrity of the device’s operating system.
The post How Does Jailbreaking Or Rooting Affect My Mobile Device Security? appeared first on McAfee Blog.

“Vishing” occurs when criminals cold-call victims and attempt to persuade them to divulge personal information over the phone. These scammers are generally after credit card numbers and personal identifying information, which can then be used to commit financial theft. Vishing can occur both on your landline phone or via your cell phone.
The term is a combination of “voice,” and “phishing,” which is the use of spoofed emails to trick targets into clicking malicious links. Rather than email, vishing generally relies on automated phone calls that instruct targets to provide account numbers. Techniques scammers use to get your phone numbers include:
Once vishers have phone numbers, they employ various strategies to deceive their targets and obtain valuable personal information:
To protect yourself from vishing scams, you should:
Staying vigilant and informed is your best defense against vishing scams. By verifying caller identities, being skeptical of unsolicited requests for personal information, and using call-blocking tools, you can significantly reduce your risk of falling victim to these deceptive practices. Additionally, investing in identity theft protection services can provide an extra layer of security. These services monitor your personal information for suspicious activity and offer assistance in recovering from identity theft, giving you peace of mind in an increasingly digital world. Remember, proactive measures and awareness are key to safeguarding your personal information against vishing threats.
The post How to Protect Yourself from Vishing appeared first on McAfee Blog.

By now you’ve probably heard of the term “phishing”—when scammers try to fool you into revealing your personal info or sending money, usually via email — but what about “vishing”? Vishing, or voice phishing, is basically the same practice, but done by phone.
There are a few reasons why it’s important for you to know about vishing. First off, voice phishing scams are prevalent and growing. A common example around tax season is the IRS scam, where fraudsters make threatening calls to taxpayers pretending to be IRS agents and demanding money for back taxes. Another popular example is the phony tech support scam, in which a scammer calls you claiming that they represent a security provider.
The scammers might say they’ve noticed a problem with your computer or device and want money to fix the problem, or even request direct access to your machine. They might also ask you to download software to do a “security scan” just so they can get you to install a piece of malware that steals your personal info. They might even try to sell you a worthless computer warranty or offer a phony refund.
These kinds of attacks can be very persuasive because the scammers employ “social engineering” techniques. This involves plays on emotion, urgency, authority, and even sometimes threats. The end result, scammers manipulate their victims into doing something for fraudulent purposes. Because scammers can reach you at any time on your most private device, your smartphone, it can feel more direct and personal.
Vishing scams don’t always require a phone call from a real person. Often, scammers use a generic or targeted recording, claiming to be from your bank or credit union. For instance, they might ask you to enter your bank account number or other personal details, which opens you up to identity theft.
Increasingly, scammers use AI tools in voice cloning attacks. With readily available voice cloning apps, scammers can replicate someone else’s voice with remarkable accuracy. While initially developed for benign purposes such as voice assistants and entertainment, scammers now use voice cloning tools to exploit unsuspecting victims.
The incoming number might even appear to have come from your bank, thanks to a trick called “caller ID spoofing,” which allows scammers to fake the origin of the call. They can do this by using Voice over Internet Protocol (VoIP) technology, which connects calls over the internet instead of traditional phone circuits, allowing them to easily assign incoming phone numbers.
Don’t risk losing your money or valuable personal info to these scams. Here’s how to avoid vishing attacks:
The post How to Avoid Being Phished by Your Phone appeared first on McAfee Blog.

I think I could count on one hand the people I know who have NOT had their email hacked. Maybe they found a four-leaf clover when they were kids! Email hacking is one of the very unfortunate downsides of living in our connected, digital world. And it usually occurs as a result of a data breach – a situation that even the savviest tech experts find themselves in.
In simple terms, a data breach happens when personal information is accessed, disclosed without permission, or lost. Companies, organisations, and government departments of any size can be affected. Data stolen can include customer login details (email addresses and passwords), credit card numbers, identifying IDs of customers e.g. driver’s license numbers and/or passport numbers, confidential customer information, company strategy, or even matters of national security.
Data breaches have made headlines, particularly over the last few years. When the Optus and Medibank data breaches hit the news in 2022 affecting almost 10 million Aussies apiece, we were all shaken. But then when Aussie finance company Latitude was affected in 2023 with a whopping 14 million people from both Australia and New Zealand, it almost felt inevitable that by now, most of us would have been impacted.
The reality is that data breaches have been happening for years. In fact, the largest data breach in Australian history happened in 2019 to the online design site Canva which affected 139 million users globally. In short, it can happen to anyone, and the chances are you may have already been affected.
The sole objective of a hacker is to get their hands on your data. Any information that you share in your email account can be very valuable to them. Why do they want your data, you ask? It’s simple really – so they can cash in!
Some will keep the juicy stuff for themselves – passwords or logins to government departments or large companies they may want to ’target’ with the aim of extracting valuable data and/or funds. The more sophisticated ones will sell your details including name, telephone, email address, and credit card details to cash in on the dark web. They often do this in batches. Some experts believe they can get as much as AU$250 for a full set of details including credit cards. So, you can see why they’d be interested in you.
The other reason why hackers will be interested in your email address and password is that many of us re-use our login details across our other online accounts. Once they’ve got their hands on your email credentials, they may be able to access your online banking and investment accounts, if you use the same credentials everywhere. So, you can see why I harp on about using a unique password for every online account!
There is a plethora of statistics on just how big this issue is – all of them concerning. According to the Australian Institute of Criminology, of all the country’s cybercrime reports in 2024, about 21.9% involved identity theft and misuse. The Australian Bureau of Statistics adds that the identity theft victimisation rate has steadily increased from 0.8% to 1.2% from 2021 to 2024, respectively.
Meanwhile, The Australian Government revealed that at least one cybercrime is reported every 6 minutes, with business email compromise alone costing the national economy up to $84 million in losses. Regardless of which statistic you choose to focus on, we have a big issue on our hands.
Hackers use a range of techniques—some highly sophisticated, others deceptively simple—to gain access. It is important to know how these attacks happen so you can stay ahead and prevent them.
Yes, absolutely. An email account is often the central hub of your digital life. Once a cybercriminal controls it, they can initiate password resets for your other online accounts, including banking, shopping, and social media. They can intercept sensitive information sent to you, such as financial statements or medical records.
With enough information gathered from your emails, they can commit identity theft, apply for credit in your name, or access other sensitive services. If you suspect your email was hacked, it’s crucial to monitor your financial statements and consider placing a fraud alert with credit bureaus.
If you find yourself a victim of email hacking, these are a few very important steps you need to take. Fast.
Using a separate, clean device, this is the very first thing you must do to ensure the hacker can’t get back into your account. It is essential that your new password is complex and totally unrelated to previous passwords. Always use random words and characters, a passphrase with a variety of upper and lower cases, and throw in some symbols and numbers.
I really like the idea of a crazy, nonsensical sentence – easier to remember and harder to crack! But, better still, get yourself a password manager that will create a password that no human would be capable of creating. If you find the hacker has locked you out of your account by changing your password, you will need to reset the password by clicking on the ‘Forgot My Password’ link.
This is time-consuming, but essential. Ensure you change any other accounts that use the same username and password as your compromised email. Hackers love the fact that many people use the same logins for multiple accounts, so it is guaranteed they will try your info in other email applications and sites such as PayPal, Amazon, Netflix – you name it!
Once the dust has settled, review your password strategy for all your online accounts. A best practice is to ensure every online account has its own unique and complex password.
Most email services have a security feature that lets you remotely log out of all active sessions. Once you’ve changed your password, signing out from your email account also signs out the hacker and forces them to log-in with the new password, which fortunately they do not know. These, combined with two- or multi-factor authentication, will help you to regain control of your account and prevent further compromise.
A big part of the hacker’s strategy is to get their claws into your address book to hook others as well. Send a message to all your email contacts as soon as possible so they know to avoid opening any emails—most likely loaded with malware—that have come from you.
Two-factor or multi-factor authentication may seem like an additional, inconvenient step to your login, but it also adds another layer of protection. Enabling this means you will need a special one-time-use code to log in, aside from your password. This is sent to your mobile phone or generated via an authenticator app. So worthwhile!
It is common for hackers to modify your email settings so that a copy of every email you receive is automatically forwarded to them. Not only can they monitor your logins to other sites; they can also keep a watchful eye on any particularly juicy personal information. So, check your mail forwarding settings to ensure no unexpected email addresses have been added.
Also, ensure your ‘reply to’ email address is actually yours. Hackers have been known to create an email address that looks similar to yours, so that when someone replies, it will go straight to their account, not yours.
Don’t forget to check your email signature to ensure nothing spammy has been added, as well as your recovery phone number and alternate email address. Hackers also change these to maintain control. Update them to your own secure details.
Regularly scanning your devices for unwanted invaders is essential. If you find anything, please ensure it is addressed, and then change your email password again. If you don’t have antivirus software, please invest in it.
Comprehensive security software will provide you with a digital shield for your online life, protecting all your devices – including your smartphone – from viruses and malware. Some services also include a password manager to help you generate and store unique passwords for all your accounts.
If you have been hacked several times and your email provider isn’t mitigating the amount of spam you are receiving, consider starting afresh. Do not, however, delete your old email address because email providers are known to recycle old email addresses. This means a hacker could spam every site they can find with a ‘forgot my password’ request and try to impersonate you and steal your identity.
Your email is an important part of your online identity so being vigilant and addressing any fallout from hacking is essential for your digital reputation. Even though it may feel that getting hacked is inevitable, you can definitely reduce your risk by installing some good-quality security software on all your devices.
Trusted and reliable comprehensive security software will alert you when visiting risky websites, warn you when a download looks dodgy, and block annoying and dangerous emails with anti-spam technology. It makes sense really – if you don’t receive the dodgy phishing email – you can’t click on it. Smart!
Finally, don’t forget that hackers love social media – particularly those of us who overshare on it. So, before you post details of your adorable new kitten, remember it may just provide the perfect clue for a hacker trying to guess your email password!
Reporting an email hack is a crucial step to create a necessary paper trail for disputes with banks or credit agencies. When reporting, gather evidence such as screenshots of suspicious activity, unrecognized login locations and times, and any phishing emails you received. This information can be vital for the investigation.
Generally, no. Deleting the account can cause more problems than it solves. Many online services are linked to that email, and deleting it means you lose the ability to receive password reset links and security notifications for those accounts.
More importantly, some email providers recycle deleted addresses, meaning a hacker could potentially re-register your old email address and use it to impersonate you and take over your linked accounts.
The better course of action is to regain control, thoroughly secure the account with a new password and multi-factor authentication, and clean up any damage. Only consider migrating to a new email address after you have fully secured the old one.
Each email provider has a specific, structured process for account recovery. It is vital to only use the official recovery pages provided by the service and be wary of scam websites or third-party services that claim they can recover your account for a fee. Below are the official steps of the major providers that you can follow.
Your email account is the master key to your digital kingdom, and protecting it is more critical than ever since many of your other accounts are connected with your email. Realizing “my email has been hacked” is a stressful experience, but taking swift and correct action can significantly limit the damage.
By following the recovery steps and adopting strong, ongoing security habits like using a password manager and enabling multi-factor authentication, you can turn a potential crisis into a lesson in digital resilience. Stay vigilant, stay proactive, and keep your digital front door securely locked.
To add another wall of defense, consider investing in a trusted and reliable comprehensive security software like McAfee+. Our solution will help you dodge hacking attempts by alerting you when visiting risky websites, or downloading questionable apps, and blocking malicious emails with anti-spam technology.
The post What to Do If Your Email Is Hacked appeared first on McAfee Blog.

There are now over 5 billion active social media users worldwide, representing 62.3% of the global population. While social networks serve as valuable tools for staying connected with loved ones and documenting life events, the ease of sharing information raises concerns. With a mere few clicks, posts and messages can inadvertently divulge significant personal details, potentially compromising privacy and leaving individuals vulnerable to identity theft. That’s why it’s crucial to make sure you’ve got the know-how to keep your privacy protected while using these platforms.
To empower you in this digital age, we’ve compiled a comprehensive guide featuring ten essential tips to fortify your online security and preserve your privacy on social networks:
Whether you’re a seasoned social media user or just dipping your toes into the digital waters, these strategies will equip you with the knowledge and tools needed to safeguard your online identity effectively. With the added support of McAfee+, you can ensure an extra layer of security to keep your online presence more secure and private through advanced privacy features, 24/7 identity monitoring and alerts, and real-time protection against viruses, hackers, and risky links.
The post How to Protect Yourself on Social Networks appeared first on McAfee Blog.

In the hands of a thief, your Social Security Number is the master key to your identity.
With a Social Security Number (SSN), a thief can unlock everything from credit history and credit line to tax refunds and medical care. In extreme cases, thieves can use it to impersonate others. So, if you suspect your number is lost or stolen, it’s important to report identity theft to Social Security right away.
Part of what makes an SSN so powerful in identity theft is that there’s only one like it. Unlike a compromised credit card, you can’t hop on the phone and get a replacement. No question, the theft of your SSN has serious implications. If you suspect it, report it. So, let’s take a look at how it can happen and how you can report identity theft to Social Security if it does.
Yes. Sort of. The Social Security Administration can assign a new SSN in a limited number of cases. However, per the SSA, “When we assign a different Social Security number, we do not destroy the original number. We cross-refer the new number with the original number to make sure the person receives credit for all earnings under both numbers.”
In other words, your SSN is effectively for forever, which means if it’s stolen, you’re still faced with clearing up any of the malicious activity associated with the theft potentially for quite some time. That’s yet another reason why the protection of your SSN deserves particular attention.
There are several ways an SSN can end up with a thief. Some involve physical theft, and others can take the digital route. To what extent are SSNs at risk? Notably, there was the Equifax breach of 2017, which exposed some 147 million SSNs. Yet just because an SSN has been potentially exposed does not mean that an identity crime has been committed with it.
So, let’s start with the basics: how do SSNs get stolen or exposed?
That’s quite the list. Broadly speaking, the examples above give good reasons for keeping your SSN as private and secure as possible. With that, it’s helpful to know that there are only a handful of situations where your SSN is required for legitimate purposes, which can help you make decisions about how and when to give it out. The list of required cases is relatively short, such as:
You’ll notice that places like doctor’s offices and other businesses are not listed here, though they’ll often request an SSN for identification purposes. While there’s no law preventing them from asking you for that information, they may refuse to work with you if you do not provide that info. In such cases, ask what the SSN would be used for and if there is another form of identification that they can use instead. In all, your SSN is uniquely yours, so be extremely cautious in order to minimize its potential exposure to theft.
Let’s say you spot something unusual on your credit report or get a notification that someone has filed a tax return on your behalf without your knowledge. These are possible signs that your identity, if not your SSN, is in jeopardy, which means it’s time to act right away using the steps below:
1. Report the theft to local and federal authorities.
File a police report and a Federal Trade Commission (FTC) Identity Theft Report. This will help in case someone uses your Social Security number to commit fraud since it will provide a legal record of the theft. The FTC can also assist by guiding you through the identity theft recovery process as well. Their site really is an excellent resource.
2. Contact the businesses involved.
Get in touch with the fraud department at each of the businesses where you suspect theft has taken place, let them know of your situation, and follow the steps they provide. With your police and FTC reports, you will already have a couple of vital pieces of information that can help you clear your name.
3. Reach the Social Security Administration and the IRS.
Check your Social Security account to see if someone has gotten a job and used your SSN for employment purposes. Reviewing earnings associated with your SSN can uncover fraudulent use. You can also contact the Social Security Fraud Hotline at (800) 269-0271 or reach out to your local SSA office for further, ongoing assistance. Likewise, contact the Internal Revenue Service at (800) 908-4490 to report the theft and help prevent someone from submitting a tax return in your name.
As we’ve talked about in some of my other blog posts, identity theft can be a long-term problem where follow-up instances of theft can crop up over time. However, there are a few steps you can take to minimize the damage and ensure it doesn’t happen again. I cover several of those steps in detail in this blog here, yet let’s take a look at a few of the top items as they relate to SSN theft:
Consider placing a fraud alert.
By placing a fraud alert, you can make it harder for thieves to open accounts in your name. Place it with one of the three major credit bureaus (Experian, TransUnion, Equifax), and they will notify the other two. During the year-long fraud alert period, it will require businesses to verify your identity before issuing new credit in your name.
Look into an all-out credit freeze.
A full credit freeze is in place until you lift it and will prohibit creditors from pulling your credit report altogether. This can help stop thieves dead in their tracks since approving credit requires pulling a report. However, this applies to legitimate inquiries, including any that you make, like opening a new loan or signing up for a credit card. If that’s the case, you’ll need to take extra steps as directed by the particular institution or lender. Unlike the fraud alert, you’ll need to notify each of the three major credit bureaus (Experian, TransUnion, Equifax) when you want the freeze lifted.
Monitor your credit reports.
Once a week you can access a free credit report from Experian, TransUnion, and Equifax. Doing so will allow you to spot any future discrepancies and offer you options for correcting them.
Sign up for an identity protection service.
Using a service to help protect your identity can monitor several types of personally identifiable information and alert you of potentially unauthorized use. Our own Identity Protection Service will do all this and more, like offering guided help to neutralize threats and prevent theft from happening again. You can set it up on your computers and smartphone to stay in the know, address issues immediately, and keep your identity secured.
Of all the forms of identity theft, the theft of a Social Security Number is certainly one of the most potentially painful because it can unlock so many vital aspects of your life. It’s uniquely you, even more than your name alone – at least in the eyes of creditors, banks, insurance companies, criminal records, etc. Your SSN calls for extra protection, and if you have any concerns that it may have been lost or stolen, don’t hesitate to spring into action.
The post How to Report Identity Theft to Social Security appeared first on McAfee Blog.

It’s that time of year again – tax season! Whether you’ve already filed in the hopes of an early refund or have yet to start the process, one thing is for sure: cybercriminals will certainly use tax season as a means to get victims to give up their personal and financial information. This time of year is advantageous for malicious actors since the IRS and tax preparers are some of the few people who actually need your personal data. As a result, consumers are targeted with various scams impersonating trusted sources like the IRS or DIY tax software companies. Fortunately, every year the IRS outlines the most prevalent tax scams, such as voice phishing, email phishing, and fake tax software scams. Let’s explore the details of these threats.
So, how do cybercriminals use voice phishing to impersonate the IRS? Voice phishing, a form of criminal phone fraud, uses social engineering tactics to gain access to victims’ personal and financial information. For tax scams, criminals will make unsolicited calls posing as the IRS and leave voicemails requesting an immediate callback. The crooks will then demand that the victim pay a phony tax bill in the form of a wire transfer, prepaid debit card or gift card. In one case outlined by Forbes, victims received emails in their inbox that allegedly contained voicemails from the IRS. The emails didn’t actually contain any voicemails but instead directed victims to a suspicious SharePoint URL. Last year, a number of SharePoint phishing scams occurred as an attempt to steal Office 365 credentials, so it’s not surprising that cybercriminals are using this technique to access taxpayers’ personal data now as well.
In addition to voice phishing schemes, malicious actors are also using email to try and get consumers to give up their personal and financial information. This year alone, almost 400 IRS phishing URLs have been reported. In a typical email phishing scheme, scammers try to obtain personal tax information like usernames and passwords by using spoofed email addresses and stolen logos. In many cases, the emails contain suspicious hyperlinks that redirect users to a fake site or PDF attachments that may download malware or viruses. If a victim clicks on these malicious links or attachments, they can seriously endanger their tax data by giving identity thieves the opportunity to steal their refund. What’s more, cybercriminals are also using subject lines like “IRS Important Notice” and “IRS Taxpayer Notice” and demanding payment or threatening to seize the victim’s tax refund.
Cybercriminals are even going so far as to impersonate trusted brands like TurboTax for their scams. In this case, DIY tax preparers who search for TurboTax software on Google are shown ads for pirated versions of TurboTax. The victims will pay a fee for the software via PayPal, only to have their computer infected with malware after downloading the software. You may be wondering, how do victims happen upon this malicious software through a simple Google search? Unfortunately, scammers have been paying to have their spoofed sites show up in search results, increasing the chances that an innocent taxpayer will fall victim to their scheme.
Money is a prime motivator for many consumers, and malicious actors are fully prepared to exploit this. Many people are concerned about how much they might owe or are predicting how much they’ll get back on their tax refund, and scammers play to both of these emotions. So, as hundreds of taxpayers are waiting for a potential tax return, it’s important that they navigate tax season wisely. Check out the following tips to avoid being spoofed by cybercriminals and identity thieves:
File before cybercriminals do it for you. The easiest defense you can take against tax season schemes is to get your hands on your W-2 and file as soon as possible. The more prompt you are to file, the less likely your data will be raked in by a cybercriminal.
Keep an eye on your credit and your identity. Keeping tabs on your credit report and knowing if your personal information has been compromised in some way can help prevent tax fraud. Together, they can let you know if someone has stolen your identity or if you have personal info on the dark web that could lead to identity theft.
Watch out for spoofed websites. Scammers have extremely sophisticated tools that help disguise phony web addresses for DIY tax software, such as stolen company logos and site designs. To avoid falling for this, go directly to the source. Type the address of a website directly into the address bar of your browser instead of following a link from an email or internet search. If you receive any suspicious links in your email, investigating the domain is usually a good way to tell if the source is legitimate or not.
Protect yourself from scam messages. Scammers also send links to scam sites via texts, social media messages, and email. Text Scam Detector can help you spot if the message you got is a fake. It uses AI technology that automatically detects links to scam URLs. If you accidentally click, don’t worry, it can block risky sites if you do.
Clean up your personal info online. Crooks and scammers have to find you before they can contact you. After all, they need to get your phone number or email from somewhere. Sometimes, that’s from “people finder” and online data brokers that gather and sell personal info to any buyer. Including crooks. McAfee Personal Data Cleanup can remove your personal info from the data broker sites scammers use to contact their victims.
Consider an identity theft protection solution. If for some reason your personal data does become compromised, be sure to use an identity theft solution such as McAfee Identity Theft Protection, which allows users to take a proactive approach to protect their identities with personal and financial monitoring and recovery tools to help keep their identities personal and secured.
The post How to Steer Clear of Tax Season Scams appeared first on McAfee Blog.

Tax season isn’t just busy for taxpayers—it’s prime time for scammers, too. As you gather your W-2s, 1099s, and other tax documents, cybercriminals are gearing up to exploit the flood of personal and financial data in circulation. From phishing emails posing as the IRS to fake tax preparers looking to steal your refund, these scams can lead to identity theft, fraudulent tax returns, and serious financial headaches.
The good news? IRS scams follow predictable patterns, and with a little awareness, you can spot the warning signs before falling victim. Let’s break down the most common tax scams and how you can safeguard your personal information this filing season.
A commonly used tactic involves hackers posing as collectors from the IRS, as tax preparers, or government bureaus. This tactic is pretty effective due to Americans’ concerns about misfiling their taxes or accidentally running into trouble with the IRS. Scammers take advantage of this fear, manipulating innocent users into providing sensitive information or money over the phone or by email. And in extreme cases, hackers may be able to infect computers with malware via malicious links or attachments sent through IRS email scams.
Another tactic used to take advantage of taxpayers is the canceled social security number scam. Hackers use robocalls claiming that law enforcement will suspend or cancel the victim’s Social Security number in response to taxes owed. Often, victims are scared into calling the fraudulent numbers back and persuaded into transferring assets to accounts that the scammer controls. Users need to remember that the IRS will only contact taxpayers through snail mail or in person, not over the phone.
Another scam criminals use involves emails impersonating the IRS. Victims receive a phishing email claiming to be from the IRS, reminding them to file their taxes or offering them information about their tax refund via malicious links. If a victim clicks on the link, they will be redirected to a spoofed site that collects the victim’s personal data, facilitating identity theft. What’s more, a victim’s computer can become infected with malware if they click on a link with malicious code, allowing fraudsters to steal more data.
Scammers also take advantage of the fact that many users seek out the help of a tax preparer or CPA during this time. These criminals will often pose as professionals, accepting money to complete a user’s taxes but won’t sign the return. This makes it look like the user completed the return themselves. However, these ghost tax preparers often lie on the return to make the user qualify for credits they haven’t earned or apply changes that will get them in trouble. Since the scammers don’t sign, the victim will then be responsible for any errors. This could lead to the user having to repay money owed, or potentially lead to an audit.
While these types of scams can occur at any time of the year, they are especially prevalent leading up to the April tax filing due date. Consumers need to be on their toes during tax season to protect their personal information and keep their finances secure. To avoid being spoofed by scammers and identity thieves, follow these tips:
File before cybercriminals do it for you. The easiest defense you can take against tax seasons schemes is to get your hands on your W-2 and file as soon as possible. The more prompt you are to file, the less likely your data will be raked in by a cybercriminal.
Keep an eye on your credit and your identity. Keeping tabs on your credit report and knowing if your personal information has been compromised in some way can help prevent tax fraud. Together, they can let you know if someone has stolen your identity or if you have personal info on the dark web that could lead to identity theft.
Beware of phishing attempts. It’s clear that phishing is the primary tactic crooks are leveraging this tax season, so it’s crucial you stay vigilant around your inbox. This means if any unfamiliar or remotely suspicious emails come through requesting tax data, double check their legitimacy with a manager or the security department before you respond. Remember: the IRS will not initiate contact with taxpayers by email, text messages, or social media channels to request personal or financial info. So someone contacts you that way, ignore the message.
Watch out for spoofed websites. Scammers have extremely sophisticated tools that help disguise phony web addresses for DIY tax software, such as stolen company logos and site designs. To avoid falling for this, go directly to the source. Type the address of a website directly into the address bar of your browser instead of following a link from an email or internet search. If you receive any suspicious links in your email, investigating the domain is usually a good way to tell if the source is legitimate or not.
Use a VPN, especially in public. Also known as a virtual private network, a VPN helps protect your vital personal info and other data with bank-grade encryption. The VPN encrypts your internet connection to keep your online activity private on any network, even public networks. Using a public network without a VPN can increase your risk because others on the network can potentially spy on your browsing and activity. If you’re new to the notion of using a VPN, check out this article on VPNs and how to choose one so that you can get the best protection and privacy possible. (Our McAfee+ plans offer a VPN as part of your subscription.)
Protect yourself from scam messages. Scammers also send links to scam sites via texts, social media messages, and email. Text Scam Detector can help you spot if the message you got is a fake. It uses AI technology that automatically detects links to scam URLs. If you accidentally click, don’t worry, it can block risky sites if you do.
Clean up your personal info online. Crooks and scammers have to find you before they can contact you. After all, they need to get your phone number or email from somewhere. Sometimes, that’s from “people finder” and online data brokers that gather and sell personal info to any buyer. Including crooks. McAfee Personal Data Cleanup can remove your personal info from the data broker sites scammers use to contact their victims.
Consider an identity theft protection solution. If for some reason your personal data does become compromised, be sure to use an identity theft solution such as McAfee Identity Theft Protection, which allows users to take a proactive approach to protect their identities with personal and financial monitoring and recovery tools to help keep their identities personal and secured.
The post Watch Out For IRS Scams and Avoid Identity Theft appeared first on McAfee Blog.

Before you take the fun-looking quiz that popped up in your social media feed, think twice. The person holding the answers may be a hacker.
Where people go, hackers are sure to follow. So it’s no surprise hackers have set up shop on social media. This has been the case for years, yet now social media-based crime is on the rise. Since 2021, total reported losses to this type of fraud reached $2.7 billion.
Among these losses are cases of identity theft, where criminals use social media to gather personal information and build profiles of potential victims they can target. Just as we discussed in our recent blog, “Can thieves steal identities with only a name and address?” these bits of information are important pieces in the larger jigsaw puzzle that is your overall identity.
Let’s uncover these scams these crooks use so that you can steer clear and stay safe.
“What’s your spooky Halloween name?” or “What’s your professional wrestler name?” You’ve probably seen a few of those and similar quizzes in your feed where you use the street you grew up on, your birthdate, your favorite song, and maybe the name of a beloved first pet to cook up a silly name or some other result. Of course, these are pieces of personal information, sometimes the answer to commonly used security questions by banks and other financial institutions. (Like, what was the model of your first car?) With this info in hand, a hacker could attempt to gain access to your accounts.
Similarly, scammers will also post surveys with the offer of a gift card to a popular retailer. All you have to do is fork over your personal info. Of course, there’s no gift card coming. Meanwhile, that scammer now has some choice pieces of personal info that they can potentially use against you.
How to avoid them: Simply put, don’t take those quizzes and surveys online.
The list here is long. These include posts and direct messages about phony relief funds, grants, and giveaways—along with bogus business opportunities that run the gamut from thinly veiled pyramid schemes and gifting circles to mystery shopper jobs. What they all have in common is that they’re run by scammers who want your information, money, or both. If this sounds familiar, like those old emails about transferring funds for a prince in some faraway nation, it is. Many of these scams simply made the jump from email to social media platforms.
How to avoid them: Research any offer, business opportunity, or organization that reaches out to you. A good trick is to do a search of the organization’s name plus the term “scam” or “review” or “complaint” to see if anything sketchy comes up.
If there’s one government official that scammers like to use to scare you, it’s the tax collector. These scammers will use social media messaging (and other mediums like emails, texts, and phone calls) to pose as an official who’s either demanding back taxes or offering a refund or credit—all of which are bogus and all of which involve you handing over your personal info, money, or both.
How to avoid them: Delete the message. In the U.S., the IRS and other government agencies will never reach out to you in this way or ask you for your personal information. Likewise, they won’t demand payment via wire transfer, gift cards, or cryptocurrency like Bitcoin. Only scammers will.
These are far more targeted than the scams listed above because they’re targeted and often rely upon specific information about you and your family. Thanks to social media, scammers can gain access to that info and use it against you. One example is the “grandkid scam” where a hacker impersonates a grandchild and asks a grandparent for money. Similarly, there are family emergency scams where a bad actor sends a message that a family member was in an accident or arrested and needs money quickly. In all, they rely on a phony story that often involves someone close to you who’s in need or trouble.
How to avoid them: Take a deep breath and confirm the situation. Reach out to the person in question or another friend or family member to see if there really is a concern. Don’t jump to pay right away.
This is one of the most targeted attacks of all—the con artist who strikes up an online relationship to bilk a victim out of money. Found everywhere from social media sites to dating apps to online forums, this scam involves creating a phony profile and a phony story to go with it. From there, the scammer will communicate several times a day, perhaps talking about their exotic job in some exotic location. They’ll build trust along the way and eventually ask the victim to wire money or purchase gift cards.
How to avoid them: Bottom line, if someone you’ve never met in person asks you for money online, it’s a good bet that it’s a scam. Don’t do it.
Now with an idea of what the bad actors are up to out there, here’s a quick rundown of things you can do to protect yourself further from the social media scams they’re trying to pull.
Above and beyond what we’ve covered so far, some online protection basics can keep you safer still. Comprehensive online protection software will help you create strong, unique passwords for all your accounts, help you keep from clicking links to malicious sites, and prevent you from downloading malware. Moreover, it can provide you with identity protection services like ours, which keep your personal info private with around-the-clock monitoring of your email addresses and bank accounts with up to $1M of ID theft insurance.
Together, with some good protection and a sharp eye, you can avoid those identity theft scams floating around on social media—and get back to enjoying time spent online with your true family and friends.
The post Quizzes and Other Identity Theft Schemes to Avoid on Social Media appeared first on McAfee Blog.

What’s the difference between identity fraud and identity theft? Well, it’s subtle, so much so that it’s easy to use them nearly interchangeably. While both can take a bite out of your wallet, they are different—and knowing the differences can help you understand what’s at stake.
Let’s start with an overview and a few examples of each.
So there’s that subtle difference we mentioned. Identity fraud involves the misuse of an existing account. Identity theft means the theft of your personal information, which is then used to impersonate you in some way, such as opening new accounts in your name.
Above and beyond those definitions and examples, a couple of real-life examples put the differences in perspective as well.
As for identity fraud, individual cases of fraud don’t always make the headlines, but that’s not to say you won’t hear about it in a couple of different ways.
The first way may be news stories about data breaches, where hackers gain things like names, emails, and payment information from companies or organizations. That info can then end up in the hands of a fraudster, who then accesses those accounts to drain funds or make purchases.
On a smaller scale, you may know someone who has had to get a new credit or debit card because theirs was compromised, perhaps by a breach or by mistakenly making a payment through an insecure website or by visiting a phony login page as part of a phishing attack. These can lead to fraud as well.
It usually starts with someone saying anything from, “That’s strange …” to “Oh, no!” There’ll be a strange charge on your credit card bill, a piece of mail from a bill collector, or a statement from an account you never opened—just to name a few things.
With that, I have a few recent blogs that help you spot all kinds of identity crime, along with advice to help keep it from happening to you in the first place:
While there are differences between identity fraud and identity theft, they do share a couple of things in common: you can take steps to prevent them, and you can take steps to limit their impact should you find yourself faced with one or the other.
The articles called out above will give you the details, yet staying safe begins with vigilance. Check on your accounts and credit reports regularly and really scrutinize what’s happening in them. Consider covering yourself with an identity monitoring solution — and act on anything that looks strange or outright fishy by reporting it to the company or institution in question.
The post How To Tell The Difference Between Identity Fraud and Identity Theft? appeared first on McAfee Blog.

When it comes to identity theft, trust your gut when something doesn’t feel right. Follow up. What you’re seeing could be a problem.
A missing bill or a mysterious charge on your credit card could be the tip of an identity theft iceberg, one that can run deep if left unaddressed. Here, we’ll look at several signs of identity theft that likely need some investigation and the steps you can take to take charge of the situation.
Unfortunately, it can happen in several ways.
In the physical world, it can happen simply because you lost your wallet or debit card. However, there are also cases where someone gets your information by going through your mail or trash for bills and statements. In other more extreme cases, theft can happen by someone successfully registering a change of address form in your name (although the U.S. Postal Service has security measures in place that make this difficult).
In the digital world, that’s where the avenues of identity theft blow wide open. It could come by way of a data breach, a thief “skimming” credit card information from a point-of-sale terminal, or by a dedicated crook piecing together various bits of personal information that have been gathered from social media, phishing attacks, or malware designed to harvest information. Additionally, thieves may eavesdrop on public Wi-Fi and steal information from people who are shopping or banking online without the security of a VPN.
Regardless of how crooks pull it off, identity theft is on the rise. According to the Federal Trade Commission (FTC), identity theft claims jumped up from roughly 650,000 claims in 2019 to 1 million in 2023. Of the reported fraud cases where a dollar loss was reported, the FTC calls out the following top three contact methods for identity theft:
However, phone calls, texts, and email remain the most preferred contact methods that fraudsters use, even if they are less successful in creating dollar losses than malicious websites, ads, and social media.
Identity thieves leave a trail. With your identity in hand, they can charge things to one or more of your existing accounts—and if they have enough information about you, they can even create entirely new accounts in your name. Either way, once an identity thief strikes, you’re probably going to notice that something is wrong. Possible signs include:
As you can see, the signs of possible identity theft can run anywhere from, “Well, that’s strange …” to “OH NO!” However, the good news is that there are several ways to check if someone is using your identity before it becomes a problem – or before it becomes a big problem that gets out of hand.
The point is that if you suspect fraud, you need to act right away. With identity theft becoming increasingly commonplace, many businesses, banks, and organizations have fraud reporting mechanisms in place that can assist you should you have any concerns. With that in mind, here are some immediate steps you can take:
Whether you spot a curious charge on your bank statement or you discover what looks like a fraudulent account when you get your free credit report, let the bank or business involved know you suspect fraud. With a visit to their website, you can track down the appropriate number to call and get the investigation process started.
Some businesses will require you to file a local police report to acquire a case number to complete your claim. Even beyond a business making such a request, filing a report is still a good idea. Identity theft is still theft and reporting it provides an official record of the incident. Should your case of identity theft lead to someone impersonating you or committing a crime in your name, filing a police report right away can help clear your name down the road. Be sure to save any evidence you have, like statements or documents that are associated with the theft. They can help clean up your record as well.
The FTC’s identity theft website is a fantastic resource should you find yourself in need. Above and beyond simply reporting the theft, the FTC can provide you with a step-by-step recovery plan—and even walk you through the process if you create an account with them. Additionally, reporting theft to the FTC can prove helpful if debtors come knocking to collect on any bogus charges in your name. You can provide them with a copy of your FTC report and ask them to stop.
You can place a free one-year fraud alert with one of the major credit bureaus (Experian, TransUnion, Equifax), and they will notify the other two. A fraud alert will make it tougher for thieves to open accounts in your name, as it requires businesses to verify your identity before issuing new credit in your name.
A credit freeze goes a step further. As the name implies, a freeze prohibits creditors from pulling your credit report, which is needed to approve credit. Such a freeze is in place until you lift it, and it will also apply to legitimate queries as well. Thus, if you intend to get a loan or new credit card while a freeze is in place, you’ll likely need to take extra measures to see that through. Contact each of the major credit bureaus (Experian, TransUnion, Equifax) to put a freeze in place or lift it when you’re ready.
This can run the gamut from closing any false accounts that were set up in your name, removing bogus charges, and correcting information in your credit report such as phony addresses or contact information. With your FTC report, you can dispute these discrepancies and have the business correct the record. Be sure to ask for written confirmation and keep a record of all documents and conversations involved.
If you receive a notice from the IRS that someone used your identity to file a tax return in your name, follow the information provided by the IRS in the notice. From there, you can file an identity theft affidavit with the IRS. If the notice mentions that you were paid by an employer you don’t know, contact that employer as well and let them know of possible fraud—namely that someone has stolen your identity and that you don’t truly work for them.
Also, be aware that the IRS has specific guidelines as to how and when they will contact you. As a rule, they will most likely contact you via physical mail delivered by the U.S. Postal Service. (They won’t call or apply harassing pressure tactics—only scammers do that.) Identity-based tax scams are a topic all of their own, and for more on it, you can check out this article on tax scams and how to avoid them.
Another downside of identity theft is that it can mark the start of a long, drawn-out affair. One instance of theft can possibly lead to another, so even what may appear to be an isolated bad charge on your credit card calls for keeping an eye on your identity. Many of the tools you would use up to this point still apply, such as checking up on your credit reports, maintaining fraud alerts as needed, and reviewing your accounts closely.
With all the time we spend online as we bank, shop, and simply surf, we create and share all kinds of personal information—information that can get collected and even stolen. The good news is that you can prevent theft and fraud with online protection software, such as McAfee+ Ultimate.
With McAfee+ Ultimate you can:
In all, it’s our most comprehensive privacy, identity, and device protection plan, built for a time when we rely so heavily on the internet to go about our day, whether that’s work, play, or simply getting things done.
Realizing that you’ve become a victim of identity theft carries plenty of emotion with it, which is understandable—the thief has stolen a part of you to get at your money, information, and even reputation. Once that initial rush of anger and surprise has passed, it’s time to get clinical and get busy. Think like a detective who’s building – and closing – a case. That’s exactly what you’re doing. Follow the steps, document each one, and build up your case file as you need. Staying cool, organized, and ready with an answer to any questions you’ll face in the process of restoring your identity will help you see things through.
Once again, this is a good reminder that vigilance is the best defense against identity theft from happening in the first place. While there’s no absolute, sure-fire protection against it, there are several things you can do to lower the odds in your favor. And at the top of the list is keeping consistent tabs on what’s happening across your credit reports and accounts.
The post How to Detect Signs of Identity Theft appeared first on McAfee Blog.

Can thieves steal identities with only a name and address?
In short, the answer is “no.” Which is a good thing, as your name and address are in fact part of the public record. Anyone can get a hold of them. However, because they are public information, they are still tools that identity thieves can use.
If you think of your identity as a jigsaw puzzle, your name and address are the first two pieces that they can use to build a bigger picture and ultimately put your identity at risk.
With that, let’s look at some other key pieces of your identity that are associated with your name and address—and what you can do to protect them.
For starters, this information is so general that it is of little value in and of itself to an identity thief. Yet a determined identity thief can do a bit of legwork and take a few extra steps to use them as a springboard for other scams.
For example, with your name and address a thief could:
There are volumes of public information that are readily available should someone want to add some more pieces to your identity jigsaw puzzle, such as:
In the U.S., the availability of such information will vary from state to state and different levels of government may have different regulations about what information gets filed—in addition to whether and how those reports are made public. Globally, different nations and regions will collect varying amounts of public information and have their own regulations in place as well. More broadly, though, many of these public databases are now online. Consequently, accessing them is easier than the days when getting a hold of that information required an in-person visit to a library or public office.
Cybercriminals can gain additional information about you from other online sources, such as data brokers. And data brokerage is a big business, a global economy estimated at $280 billion U.S. dollars a year. What fuels it? Personal information, representing thousands of data points on billions of people scraped from public records, social media, smartphone apps, shopper loyalty cards, third-party sources, and sometimes other data broker sites as well.
The above-the-board legal intent of data broker sites is to sell that information to advertisers so that they can create highly targeted campaigns based on people’s behaviors, travels, interests, and even political leanings. Others such as law enforcement officials, journalists, and others who are conducting background checks will use them too.
On the dark side, hackers, scammers, and thieves will buy this information as well, which they can use to commit identity theft and fraud. The thing is, data brokers will sell to anyone. They don’t discriminate.
Phishing attacks aren’t just for email, texts, and direct messages. In fact, thieves are turning to old tricks via old-fashioned physical mail. That includes sending phony offers or impersonating officials of government institutions, all designed to trick you into giving up your personally identifiable information (PII).
What might that look like in your mailbox? They can take the form of bogus lottery prizes that request bank information for routing (non-existent) winnings. Another favorite of scammers is bogus tax notifications that demand immediate payment. In all, many can look quite convincing at first blush, yet there are ready ways you can spot them. In fact, many of the tips for avoiding these physical mail phishing attacks are the same for avoiding phishing attacks online.
Recently, I’ve seen a few news stories like this where thieves reportedly abuse the change-of-address system with the U.S. Postal Service. Thieves will simply forward your mail to an address of their choosing, which can drop sensitive information like bank and credit card statements in their mailbox. From there, they could potentially have new checks sent to them or perhaps an additional credit card—both of which they can use to drain your accounts and run up your bills.
The Postal Service has mechanisms in place to prevent this, however. Among these, the Postal Service will send you a physical piece of mail to confirm the forwarding. So, if you ever receive mail from the Postal Service, open it and give it a close look. If you get such a notice and didn’t order the forwarding, visit your local post office to get things straightened out. Likewise, if it seems like you’re missing bills in the mail, that’s another good reason to follow up with your post office and the business in question to see if there have been any changes made in your mail forwarding.
So while your name and address are out there for practically all to see, they’re largely of little value to an identity thief on their own. But as mentioned above, they are key puzzle pieces to your overall identity. With enough of those other pieces in hand, that’s where an identity thief can cause trouble.
Other crucial pieces of your identity include:
Let’s start with the biggest one. This is the master key to your identity, as it is one of the most unique identifiers you have. As I covered in my earlier blog on Social Security fraud, a thief can unlock everything from credit history and credit line to tax refunds and medical care with your Social Security or tax ID number. In extreme cases, they can use it to impersonate you for employment, healthcare, and even in the event of an arrest.
You can protect your Social Security Number by keeping it locked in a safe place (rather than in your wallet) and by providing your number only when absolutely necessary. For more tips on keeping your number safe, drop by that blog on Social Security fraud I mentioned.
Thieves have figured out ways of getting around the fact that IDs like these include a photo. They may be able to modify or emulate these documents “well enough” to pull off certain types of fraud, particularly if the people requesting their bogus documents don’t review them with a critical eye.
Protecting yourself in this case means knowing where these documents are at any time. (With passports, you may want to store those securely like your Social Security or tax ID number.) Also be careful when you share this information, as the identifiers on these documents are highly unique. If you’re uncomfortable with sharing this information, you can ask if other forms of ID might work—or if this information is really needed at all. Also, take a moment to make copies of these documents and store them in a secure place. This can help you provide important info to the proper authorities if they’re lost or stolen.
With data breaches large and small making the news (and many more that do not), keeping a sharp eye on your accounts is a major part of identity theft prevention. We talk about this topic quite often, and it’s worth another mention because protecting these means protecting yourself from thieves who are after direct access to your finances and more.
Secure your digital accounts for banking, credit cards, financials, and shopping by using strong, unique passwords for each of your accounts that you change every 60 days. Sound like a lot of work? Let a password manager do it for you, which you can find in comprehensive online protection software. By changing your strong passwords and keeping them unique can help prevent you from becoming a victim if your account information is part of a breach—by the time a crook attempts to use it, you may have changed it and made it out of date.
In addition to protecting the core forms of identity mentioned above, a few other good habits go a long way toward keeping your identity secure.
By protecting your devices, you protect what’s on them, like your personal information. Comprehensive online protection software can protect your identity in several ways, like creating and managing the strong, unique passwords we talked about and providing further services that monitor and protect your identity—in addition to digital shredders that can permanently remove sensitive documents (simply deleting them won’t do that alone.) Further, it can monitor your identity and monitor your credit, further protecting you from theft and fraud.
Identity theft where thieves dig through trash or go “dumpster diving” for literal scraps of personal info in bills and statements, has been an issue for some time. You can prevent it by shredding up any paper medical bills, tax documents, and checks once you’re through with them. Paper shredders are inexpensive, and let’s face it, kind of fun too. Also, if you’re traveling, have a trusted someone collect your mail or have the post office put a temporary hold on your mail. Thieves still poach mail from mailboxes too.
Getting statements online cuts the paper out of the equation and thus removes another thing that a thief can physically steal and possibly use against you. Whether you use electronic statements through your bank, credit card company, medical provider, or insurance company, use a secure password and a secure connection provided by a VPN. Both will make theft of your personal info far tougher on identity thieves.
A VPN is a Virtual Private Network, a service that protects your data and privacy online. It creates an encrypted tunnel to keep you more anonymous online by masking your IP address, device information, and the data you’re passing along that connection. In this way, it makes it far more difficult for advertisers, data brokers, and bad actors to skim your private information—in addition to shielding your information from crooks and snoops while you’re banking, shopping, or handling any kind of sensitive information online.
Give your statements a close look each time they come around. While many companies and institutions have fraud detection mechanisms in place, they don’t always catch every instance of fraud. Look out for strange purchases or charges and follow up with your bank or credit card company if you suspect fraud. Even the smallest charge could be a sign that something shady is afoot.
This is a powerful tool for spotting identity theft. And in many cases, it’s free to do so. In the U.S., the Fair Credit Reporting Act (FCRA) requires the major credit agencies to provide you with a free credit check at least once every 12 months. Canada provides this service, and the UK has options to receive free reports as well, along with several other nations. It’s a great idea to check your credit report, even if you don’t suspect a problem.
If the thought of your personal info being bought and sold puts you off, there’s something you can do about it. Our Personal Data Cleanup service can scan some of the riskiest data broker sites and show you which ones are selling your personal info. It also provides guidance on how you can remove your data from those sites, and with select products, it can even manage the removal for you.
While thieves need more than just your name and address to commit the overwhelming majority of fraud, your name and address are centerpieces of the larger jigsaw puzzle that is your overall identity.
And the interesting thing is your puzzle gets larger and larger as time goes on. With each new account you create and service that you sign into, that’s one more piece added to the puzzle. Thieves love getting their hands on any pieces they can because with enough of them in place, they can try and pull a fast one in your name. By looking after each piece and knowing what your larger jigsaw puzzle looks like, you can help keep identity thieves out of your business and your life.
The post Can Thieves Steal Identities With Only a Name and Address? appeared first on McAfee Blog.

Did you just get word that your personal information may have been caught up in a data breach? If so, you can take steps to protect yourself from harm should your info get into the hands of a scammer or thief.
How does that information get collected in the first place? We share personal information with companies for multiple reasons simply by going about our day—to pay for takeout at our favorite restaurant, to check into a hotel, or to collect rewards at the local coffee shop. Of course, we use our credit and debit cards too, sometimes as part of an online account that tracks our purchase history.
In other words, we leave trails of data practically wherever we go these days, and that data is of high value to hackers. Thus, all those breaches we read about.
Whether it’s a major breach that exposes millions of records or one of many other smaller-scale breaches like the thousands that have struck healthcare providers, each one serves as a reminder that data breaches happen regularly and that we could find ourselves affected. Depending on the breach and the kind of information you’ve shared with the business or organization in question, information stolen in a breach could include:
What do crooks do with that data? Several things. Apart from using it themselves, they may sell that data to other criminals. Either way, this can lead to illicit use of credit and debit cards, draining of bank accounts, claiming tax refunds or medical expenses in the names of the victims, or, in extreme cases, assuming the identity of others altogether.
In all, data is a kind of currency in of itself because it has the potential to unlock several aspects of victim’s life, each with its own monetary value. It’s no wonder that big breaches like these have made the news over the years, with some of the notables including:
As mentioned, these are big breaches with big companies that we likely more than recognize. Yet smaller and mid-sized businesses are targets as well, with some 43% of data breaches involving companies of that size. Likewise, restaurants and retailers have seen their Point-of-Sale (POS) terminals compromised, right on down to neighborhood restaurants.
When a company experiences a data breach, customers need to realize that this could impact their online safety. If your favorite coffee shop’s customer database gets leaked, there’s a chance that your personal or financial information was exposed. However, this doesn’t mean that your online safety is doomed. If you think you were affected by a breach, you can take several steps to protect yourself from the potential side effects.
One of the most effective ways to determine whether someone is fraudulently using one or more of your accounts is to check your statements. If you see any charges that you did not make, report them to your bank or credit card company immediately. They have processes in place to handle fraud. While you’re with them, see if they offer alerts for strange purchases, transactions, or withdrawals.
Our credit monitoring service can help you keep an eye on this. It monitors changes to your credit score, report, and accounts with timely notifications and guidance so you can take action to tackle identity theft.
Breached and stolen information often ends up in dark web marketplaces where hackers, scammers, and thieves purchase it to commit yet more crime. Once it was difficult to know if your information was caught up in such marketplaces, yet now an identity monitoring service can do the detective work for you.
Our service monitors the dark web for your personal info, including email, government IDs, credit card and bank account info, and more. This can help keep your personal info safe with early alerts that show you if your data is found on the dark web, an average of 10 months ahead of similar services. From there, you’ll get guidance that you can act on, which can help protect your info and accounts from theft.
If you suspect that your data might have been compromised, place a fraud alert on your credit. This not only ensures that any new or recent requests undergo scrutiny, but also allows you to have extra copies of your credit report so you can check for suspicious activity. You can place one fraud alert with any of the three major credit reporting agencies (Equifax, Experian, TransUnion) and they will notify the other two. A fraud alert typically lasts for a year, although there are options for extending it as well.
Freezing your credit will make it highly difficult for criminals to take out loans or open new accounts in your name, as a freeze halts all requests to pull your credit—even legitimate ones. In this way, it’s a far stronger measure than placing a fraud alert. Note that if you plan to take out a loan, open a new credit card, or other activity that will prompt a credit report, you’ll need to take extra steps to see that through while the freeze is in place. (The organization you’re working with can assist with the specifics.) Unlike the fraud alert, you’ll need to contact each major credit reporting agency to put one in place. Also, a freeze lasts as long as you have it in place. You’ll have to remove it yourself, again with each agency.
You can centrally manage this process with our security freeze service, which stops companies from looking at your credit profile, and thus halts the application process for loans, credit cards, utilities, new bank accounts, and more. A security freeze won’t affect your credit score.
Ensure that your passwords are strong and unique. Many people utilize the same password or variations of it across all their accounts. Therefore, be sure to diversify your passcodes to ensure hackers cannot obtain access to all your accounts at once, should one password be compromised. You can also employ a password manager to keep track of your credentials, such as the one you’ll find in comprehensive online protection software.
If the unfortunate happens to you, an identity theft coverage & restoration service can help you get back on your feet. Ours offers $1 million in coverage for lawyer fees, travel expenses, and stolen funds reimbursement. It further provides support from a licensed recovery expert who can take the needed steps to repair your identity and credit. In all, it helps you recover the costs of identity theft along with the time and money it takes to recover from it.
You can take this step any time, even if you haven’t been caught up in a data breach. The fact is that data broker companies collect and sell thousands of pieces of information on millions and millions of people worldwide, part of a global economy estimated at $200 billion U.S. dollars a year. And they’ll sell it to anyone—from advertisers for their campaigns, to scammers who will use it for spammy emails, texts, and calls, and to thieves who use that information for identity theft.
Yet you can clean it up. Our personal data cleanup service can scan some of the riskiest data broker sites and show you which ones are selling your personal info. It also provides guidance on how you can remove your data from those sites and, with select products, even manage the removal for you.
Comprehensive online protection software will offer you the tools and services listed above, along with further features that can protect you online. That includes a VPN to keep your time online more private from online data collection while protecting it from thieves who’re out to steal credit card and account information. It also includes web browsing protection that can warn you of sketchy websites and malicious downloads that look to steal your information. In all, it’s thorough protection for your devices, privacy, and identity. And in a time of data breaches, that kind of protection has become essential.
The post How to Protect Yourself From Identity Theft After a Data Breach appeared first on McAfee Blog.