The U.S. government is reportedly preparing to ban the sale of wireless routers and other networking gear from TP-Link Systems, a tech company that currently enjoys an estimated 50% market share among home users and small businesses. Experts say while the proposed ban may have more to do with TP-Link’s ties to China than any specific technical threats, much of the rest of the industry serving this market also sources hardware from China and ships products that are insecure fresh out of the box.

A TP-Link WiFi 6 AX1800 Smart WiFi Router (Archer AX20).
The Washington Post recently reported that more than a half-dozen federal departments and agencies were backing a proposed ban on future sales of TP-Link devices in the United States. The story said U.S. Department of Commerce officials concluded TP-Link Systems products pose a risk because the U.S.-based company’s products handle sensitive American data and because the officials believe it remains subject to jurisdiction or influence by the Chinese government.
TP-Link Systems denies that, saying that it fully split from the Chinese TP-Link Technologies over the past three years, and that its critics have vastly overstated the company’s market share (TP-Link puts it at around 30 percent). TP-Link says it has headquarters in California, with a branch in Singapore, and that it manufactures in Vietnam. The company says it researches, designs, develops and manufactures everything except its chipsets in-house.
TP-Link Systems told The Post it has sole ownership of some engineering, design and manufacturing capabilities in China that were once part of China-based TP-Link Technologies, and that it operates them without Chinese government supervision.
“TP-Link vigorously disputes any allegation that its products present national security risks to the United States,” Ricca Silverio, a spokeswoman for TP-Link Systems, said in a statement. “TP-Link is a U.S. company committed to supplying high-quality and secure products to the U.S. market and beyond.”
Cost is a big reason TP-Link devices are so prevalent in the consumer and small business market: As this February 2025 story from Wired observed regarding the proposed ban, TP-Link has long had a reputation for flooding the market with devices that are considerably cheaper than comparable models from other vendors. That price point (and consistently excellent performance ratings) has made TP-Link a favorite among Internet service providers (ISPs) that provide routers to their customers.
In August 2024, the chairman and the ranking member of the House Select Committee on the Strategic Competition Between the United States and the Chinese Communist Party called for an investigation into TP-Link devices, which they said were found on U.S. military bases and for sale at exchanges that sell them to members of the military and their families.
“TP-Link’s unusual degree of vulnerabilities and required compliance with PRC law are in and of themselves disconcerting,” the House lawmakers warned in a letter (PDF) to the director of the Commerce Department. “When combined with the PRC government’s common use of SOHO [small office/home office] routers like TP-Link to perpetrate extensive cyberattacks in the United States, it becomes significantly alarming.”
The letter cited a May 2023 blog post by Check Point Research about a Chinese state-sponsored hacking group dubbed “Camaro Dragon” that used a malicious firmware implant for some TP-Link routers to carry out a sequence of targeted cyberattacks against European foreign affairs entities. Check Point said while it only found the malicious firmware on TP-Link devices, “the firmware-agnostic nature of the implanted components indicates that a wide range of devices and vendors may be at risk.”
In a report published in October 2024, Microsoft said it was tracking a network of compromised TP-Link small office and home office routers that has been abused by multiple distinct Chinese state-sponsored hacking groups since 2021. Microsoft found the hacker groups were leveraging the compromised TP-Link systems to conduct “password spraying” attacks against Microsoft accounts. Password spraying involves rapidly attempting to access a large number of accounts (usernames/email addresses) with a relatively small number of commonly used passwords.
TP-Link rightly points out that most of its competitors likewise source components from China. The company also correctly notes that advanced persistent threat (APT) groups from China and other nations have leveraged vulnerabilities in products from their competitors, such as Cisco and Netgear.
But that may be cold comfort for TP-Link customers who are now wondering if it’s smart to continue using these products, or whether it makes sense to buy more costly networking gear that might only be marginally less vulnerable to compromise.
Almost without exception, the hardware and software that ships with most consumer-grade routers includes a number of default settings that need to be changed before the devices can be safely connected to the Internet. For example, bring a new router online without changing the default username and password and chances are it will only take a few minutes before it is probed and possibly compromised by some type of Internet-of-Things botnet. Also, it is incredibly common for the firmware in a brand new router to be dangerously out of date by the time it is purchased and unboxed.
Until quite recently, the idea that router manufacturers should make it easier for their customers to use these products safely was something of an anathema to this industry. Consumers were largely left to figure that out on their own, with predictably disastrous results.
But over the past few years, many manufacturers of popular consumer routers have begun forcing users to perform basic hygiene — such as changing the default password and updating the internal firmware — before the devices can be used as a router. For example, most brands of “mesh” wireless routers — like Amazon’s Eero, Netgear’s Orbi series, or Asus’s ZenWifi — require online registration that automates these critical steps going forward (or at least through their stated support lifecycle).
For better or worse, less expensive, traditional consumer routers like those from Belkin and Linksys also now automate this setup by heavily steering customers toward installing a mobile app to complete the installation (this often comes as a shock to people more accustomed to manually configuring a router). Still, these products tend to put the onus on users to check for and install available updates periodically. Also, they’re often powered by underwhelming or else bloated firmware, and a dearth of configurable options.
Of course, not everyone wants to fiddle with mobile apps or is comfortable with registering their router so that it can be managed or monitored remotely in the cloud. For those hands-on folks — and for power users seeking more advanced router features like VPNs, ad blockers and network monitoring — the best advice is to check if your router’s stock firmware can be replaced with open-source alternatives, such as OpenWrt or DD-WRT.
These open-source firmware options are compatible with a wide range of devices, and they generally offer more features and configurability. Open-source firmware can even help extend the life of routers years after the vendor stops supporting the underlying hardware, but it still requires users to manually check for and install any available updates.
Happily, TP-Link users spooked by the proposed ban may have an alternative to outright junking these devices, as many TP-Link routers also support open-source firmware options like OpenWRT. While this approach may not eliminate any potential hardware-specific security flaws, it could serve as an effective hedge against more common vendor-specific vulnerabilities, such as undocumented user accounts, hard-coded credentials, and weaknesses that allow attackers to bypass authentication.
Regardless of the brand, if your router is more than four or five years old it may be worth upgrading for performance reasons alone — particularly if your home or office is primarily accessing the Internet through WiFi.
NB: The Post’s story notes that a substantial portion of TP-Link routers and those of its competitors are purchased or leased through ISPs. In these cases, the devices are typically managed and updated remotely by your ISP, and equipped with custom profiles responsible for authenticating your device to the ISP’s network. If this describes your setup, please do not attempt to modify or replace these devices without first consulting with your Internet provider.
Security researchers recently revealed that the personal information of millions of people who applied for jobs at McDonald’s was exposed after they guessed the password (“123456”) for the fast food chain’s account at Paradox.ai, a company that makes artificial intelligence based hiring chatbots used by many Fortune 500 firms. Paradox.ai said the security oversight was an isolated incident that did not affect its other customers, but recent security breaches involving its employees in Vietnam tell a more nuanced story.

A screenshot of the paradox.ai homepage showing its AI hiring chatbot “Olivia” interacting with potential hires.
Earlier this month, security researchers Ian Carroll and Sam Curry wrote about simple methods they found to access the backend of the AI chatbot platform on McHire.com, the McDonald’s website that many of its franchisees use to screen job applicants. As first reported by Wired, the researchers discovered that the weak password used by Paradox exposed 64 million records, including applicants’ names, email addresses and phone numbers.
Paradox.ai acknowledged the researchers’ findings but said the company’s other client instances were not affected, and that no sensitive information — such as Social Security numbers — was exposed.
“We are confident, based on our records, this test account was not accessed by any third party other than the security researchers,” the company wrote in a July 9 blog post. “It had not been logged into since 2019 and frankly, should have been decommissioned. We want to be very clear that while the researchers may have briefly had access to the system containing all chat interactions (NOT job applications), they only viewed and downloaded five chats in total that had candidate information within. Again, at no point was any data leaked online or made public.”
However, a review of stolen password data gathered by multiple breach-tracking services shows that at the end of June 2025, a Paradox.ai administrator in Vietnam suffered a malware compromise on their device that stole usernames and passwords for a variety of internal and third-party online services. The results were not pretty.
The password data from the Paradox.ai developer was stolen by a malware strain known as “Nexus Stealer,” a form grabber and password stealer that is sold on cybercrime forums. The information snarfed by stealers like Nexus is often recovered and indexed by data leak aggregator services like Intelligence X, which reports that the malware on the Paradox.ai developer’s device exposed hundreds of mostly poor and recycled passwords (using the same base password but slightly different characters at the end).
Those purloined credentials show the developer in question at one point used the same seven-digit password to log in to Paradox.ai accounts for a number of Fortune 500 firms listed as customers on the company’s website, including Aramark, Lockheed Martin, Lowes, and Pepsi.
Seven-character passwords, particularly those consisting entirely of numerals, are highly vulnerable to “brute-force” attacks that can try a large number of possible password combinations in quick succession. According to a much-referenced password strength guide maintained by Hive Systems, modern password-cracking systems can work out a seven number password more or less instantly.

Image: hivesystems.com.
In response to questions from KrebsOnSecurity, Paradox.ai confirmed that the password data was recently stolen by a malware infection on the personal device of a longtime Paradox developer based in Vietnam, and said the company was made aware of the compromise shortly after it happened. Paradox maintains that few of the exposed passwords were still valid, and that a majority of them were present on the employee’s personal device only because he had migrated the contents of a password manager from an old computer.
Paradox also pointed out that it has been requiring single sign-on (SSO) authentication since 2020 that enforces multi-factor authentication for its partners. Still, a review of the exposed passwords shows they included the Vietnamese administrator’s credentials to the company’s SSO platform — paradoxai.okta.com. The password for that account ended in 202506 — possibly a reference to the month of June 2025 — and the digital cookie left behind after a successful Okta login with those credentials says it was valid until December 2025.
Also exposed were the administrator’s credentials and authentication cookies for an account at Atlassian, a platform made for software development and project management. The expiration date for that authentication token likewise was December 2025.
Infostealer infections are among the leading causes of data breaches and ransomware attacks today, and they result in the theft of stored passwords and any credentials the victim types into a browser. Most infostealer malware also will siphon authentication cookies stored on the victim’s device, and depending on how those tokens are configured thieves may be able to use them to bypass login prompts and/or multi-factor authentication.
Quite often these infostealer infections will open a backdoor on the victim’s device that allows attackers to access the infected machine remotely. Indeed, it appears that remote access to the Paradox administrator’s compromised device was offered for sale recently.
In February 2019, Paradox.ai announced it had successfully completed audits for two fairly comprehensive security standards (ISO 27001 and SOC 2 Type II). Meanwhile, the company’s security disclosure this month says the test account with the atrocious 123456 username and password was last accessed in 2019, but somehow missed in their annual penetration tests. So how did it manage to pass such stringent security audits with these practices in place?
Paradox.ai told KrebsOnSecurity that at the time of the 2019 audit, the company’s various contractors were not held to the same security standards the company practices internally. Paradox emphasized that this has changed, and that it has updated its security and password requirements multiple times since then.
It is unclear how the Paradox developer in Vietnam infected his computer with malware, but a closer review finds a Windows device for another Paradox.ai employee from Vietnam was compromised by similar data-stealing malware at the end of 2024 (that compromise included the victim’s GitHub credentials). In the case of both employees, the stolen credential data includes Web browser logs that indicate the victims repeatedly downloaded pirated movies and television shows, which are often bundled with malware disguised as a video codec needed to view the pirated content.
Microsoft on Tuesday released software updates to fix at least 70 vulnerabilities in Windows and related products, including five zero-day flaws that are already seeing active exploitation. Adding to the sense of urgency with this month’s patch batch from Redmond are fixes for two other weaknesses that now have public proof-of-concept exploits available.

Microsoft and several security firms have disclosed that attackers are exploiting a pair of bugs in the Windows Common Log File System (CLFS) driver that allow attackers to elevate their privileges on a vulnerable device. The Windows CLFS is a critical Windows component responsible for logging services, and is widely used by Windows system services and third-party applications for logging. Tracked as CVE-2025-32701 & CVE-2025-32706, these flaws are present in all supported versions of Windows 10 and 11, as well as their server versions.
Kev Breen, senior director of threat research at Immersive Labs, said privilege escalation bugs assume an attacker already has initial access to a compromised host, typically through a phishing attack or by using stolen credentials. But if that access already exists, Breen said, attackers can gain access to the much more powerful Windows SYSTEM account, which can disable security tooling or even gain domain administration level permissions using credential harvesting tools.
“The patch notes don’t provide technical details on how this is being exploited, and no Indicators of Compromise (IOCs) are shared, meaning the only mitigation security teams have is to apply these patches immediately,” he said. “The average time from public disclosure to exploitation at scale is less than five days, with threat actors, ransomware groups, and affiliates quick to leverage these vulnerabilities.”
Two other zero-days patched by Microsoft today also were elevation of privilege flaws: CVE-2025-32709, which concerns afd.sys, the Windows Ancillary Function Driver that enables Windows applications to connect to the Internet; and CVE-2025-30400, a weakness in the Desktop Window Manager (DWM) library for Windows. As Adam Barnett at Rapid7 notes, tomorrow marks the one-year anniversary of CVE-2024-30051, a previous zero-day elevation of privilege vulnerability in this same DWM component.
The fifth zero-day patched today is CVE-2025-30397, a flaw in the Microsoft Scripting Engine, a key component used by Internet Explorer and Internet Explorer mode in Microsoft Edge.
Chris Goettl at Ivanti points out that the Windows 11 and Server 2025 updates include some new AI features that carry a lot of baggage and weigh in at around 4 gigabytes. Said baggage includes new artificial intelligence (AI) capabilities, including the controversial Recall feature, which constantly takes screenshots of what users are doing on Windows CoPilot-enabled computers.
Microsoft went back to the drawing board on Recall after a fountain of negative feedback from security experts, who warned it would present an attractive target and a potential gold mine for attackers. Microsoft appears to have made some efforts to prevent Recall from scooping up sensitive financial information, but privacy and security concerns still linger. Former Microsoftie Kevin Beaumont has a good teardown on Microsoft’s updates to Recall.
In any case, windowslatest.com reports that Windows 11 version 24H2 shows up ready for downloads, even if you don’t want it.
“It will now show up for ‘download and install’ automatically if you go to Settings > Windows Update and click Check for updates, but only when your device does not have a compatibility hold,” the publication reported. “Even if you don’t check for updates, Windows 11 24H2 will automatically download at some point.”
Apple users likely have their own patching to do. On May 12 Apple released security updates to fix at least 30 vulnerabilities in iOS and iPadOS (the updated version is 18.5). TechCrunch writes that iOS 18.5 also expands emergency satellite capabilities to iPhone 13 owners for the first time (previously it was only available on iPhone 14 or later).
Apple also released updates for macOS Sequoia, macOS Sonoma, macOS Ventura, WatchOS, tvOS and visionOS. Apple said there is no indication of active exploitation for any of the vulnerabilities fixed this month.
As always, please back up your device and/or important data before attempting any updates. And please feel free to sound off in the comments if you run into any problems applying any of these fixes.
Microsoft today released updates to plug at least 121 security holes in its Windows operating systems and software, including one vulnerability that is already being exploited in the wild. Eleven of those flaws earned Microsoft’s most-dire “critical” rating, meaning malware or malcontents could exploit them with little to no interaction from Windows users.

The zero-day flaw already seeing exploitation is CVE-2025-29824, a local elevation of privilege bug in the Windows Common Log File System (CLFS) driver. Microsoft rates it as “important,” but as Chris Goettl from Ivanti points out, risk-based prioritization warrants treating it as critical.
This CLFS component of Windows is no stranger to Patch Tuesday: According to Tenable’s Satnam Narang, since 2022 Microsoft has patched 32 CLFS vulnerabilities — averaging 10 per year — with six of them exploited in the wild. The last CLFS zero-day was patched in December 2024.
Narang notes that while flaws allowing attackers to install arbitrary code are consistently top overall Patch Tuesday features, the data is reversed for zero-day exploitation.
“For the past two years, elevation of privilege flaws have led the pack and, so far in 2025, account for over half of all zero-days exploited,” Narang wrote.
Rapid7’s Adam Barnett warns that any Windows defenders responsible for an LDAP server — which means almost any organization with a non-trivial Microsoft footprint — should add patching for the critical flaw CVE-2025-26663 to their to-do list.
“With no privileges required, no need for user interaction, and code execution presumably in the context of the LDAP server itself, successful exploitation would be an attractive shortcut to any attacker,” Barnett said. “Anyone wondering if today is a re-run of December 2024 Patch Tuesday can take some small solace in the fact that the worst of the trio of LDAP critical RCEs published at the end of last year was likely easier to exploit than today’s example, since today’s CVE-2025-26663 requires that an attacker win a race condition. Despite that, Microsoft still expects that exploitation is more likely.”
Among the critical updates Microsoft patched this month are remote code execution flaws in Windows Remote Desktop services (RDP), including CVE-2025-26671, CVE-2025-27480 and CVE-2025-27482; only the latter two are rated “critical,” and Microsoft marked both of them as “Exploitation More Likely.”
Perhaps the most widespread vulnerabilities fixed this month were in web browsers. Google Chrome updated to fix 13 flaws this week, and Mozilla Firefox fixed eight bugs, with possibly more updates coming later this week for Microsoft Edge.
As it tends to do on Patch Tuesdays, Adobe has released 12 updates resolving 54 security holes across a range of products, including ColdFusion, Adobe Commerce, Experience Manager Forms, After Effects, Media Encoder, Bridge, Premiere Pro, Photoshop, Animate, AEM Screens, and FrameMaker.
Apple users may need to patch as well. On March 31, Apple released a huge security update (more than three gigabytes in size) to fix issues in a range of their products, including at least one zero-day flaw.
And in case you missed it, on March 31, 2025 Apple released a rather large batch of security updates for a wide range of their products, from macOS to the iOS operating systems on iPhones and iPads.
Earlier today, Microsoft included a note saying Windows 10 security updates weren’t available but would be released as soon as possible. It appears from browsing askwoody.com that this snafu has since been rectified. Either way, if you run into complications applying any of these updates please leave a note about it in the comments below, because the chances are good that someone else had the same problem.
As ever, please consider backing up your data and or devices prior to updating, which makes it far less complicated to undo a software update gone awry. For more granular details on today’s Patch Tuesday, check out the SANS Internet Storm Center’s roundup. Microsoft’s update guide for April 2025 is here.
For more details on Patch Tuesday, check out the write-ups from Action1 and Automox.
Microsoft today released updates to plug at least 70 security holes in Windows and Windows software, including one vulnerability that is already being exploited in active attacks.

The zero-day seeing exploitation involves CVE-2024-49138, a security weakness in the Windows Common Log File System (CLFS) driver — used by applications to write transaction logs — that could let an authenticated attacker gain “system” level privileges on a vulnerable Windows device.
The security firm Rapid7 notes there have been a series of zero-day elevation of privilege flaws in CLFS over the past few years.
“Ransomware authors who have abused previous CLFS vulnerabilities will be only too pleased to get their hands on a fresh one,” wrote Adam Barnett, lead software engineer at Rapid7. “Expect more CLFS zero-day vulnerabilities to emerge in the future, at least until Microsoft performs a full replacement of the aging CLFS codebase instead of offering spot fixes for specific flaws.”
Elevation of privilege vulnerabilities accounted for 29% of the 1,009 security bugs Microsoft has patched so far in 2024, according to a year-end tally by Tenable; nearly 40 percent of those bugs were weaknesses that could let attackers run malicious code on the vulnerable device.
Rob Reeves, principal security engineer at Immersive Labs, called special attention to CVE-2024-49112, a remote code execution flaw in the Lightweight Directory Access Protocol (LDAP) service on every version of Windows since Windows 7. CVE-2024-49112 has been assigned a CVSS (badness) score of 9.8 out of 10.
“LDAP is most commonly seen on servers that are Domain Controllers inside a Windows network and LDAP must be exposed to other servers and clients within an enterprise environment for the domain to function,” Reeves said. “Microsoft hasn’t released specific information about the vulnerability at present, but has indicated that the attack complexity is low and authentication is not required.”
Tyler Reguly at the security firm Fortra had a slightly different 2024 patch tally for Microsoft, at 1,088 vulnerabilities, which he said was surprisingly similar to the 1,063 vulnerabilities resolved in 2023 and the 1,119 vulnerabilities resolved in 2022.
“If nothing else, we can say that Microsoft is consistent,” Reguly said. “While it would be nice to see the number of vulnerabilities each year decreasing, at least consistency lets us know what to expect.”
If you’re a Windows end user and your system is not set up to automatically install updates, please take a minute this week to run Windows Update, preferably after backing up your system and/or important data.
System admins should keep an eye on AskWoody.com, which usually has the details if any of the Patch Tuesday fixes are causing problems. In the meantime, if you run into any problems applying this month’s fixes, please drop a note about in the comments below.
The United States today unveiled sanctions and indictments against the alleged proprietor of Joker’s Stash, a now-defunct cybercrime store that peddled tens of millions of payment cards stolen in some of the largest data breaches of the past decade. The government also indicted and sanctioned a top Russian cybercriminal known as Taleon, whose cryptocurrency exchange Cryptex has evolved into one of Russia’s most active money laundering networks.
A 2016 screen shot of the Joker’s Stash homepage. The links have been redacted.
The U.S. Department of Justice (DOJ) today unsealed an indictment against a 38-year-old man from Novosibirsk, Russia for allegedly operating Joker’s Stash, an extremely successful carding shop that came online in late 2014. Joker’s sold cards stolen in a steady drip of breaches at U.S. retailers, including Saks Fifth Avenue, Lord and Taylor, Bebe Stores, Hilton Hotels, Jason’s Deli, Whole Foods, Chipotle, Wawa, Sonic Drive-In, the Hy-Vee supermarket chain, Buca Di Beppo, and Dickey’s BBQ.
The government believes the brains behind Joker’s Stash is Timur Kamilevich Shakhmametov, an individual who is listed in Russian incorporation documents as the owner of Arpa Plus, a Novosibirsk company that makes mobile games.
Early in his career (circa 2000) Shakhmametov was known as “v1pee” and was the founder of the Russian hacker group nerf[.]ru, which periodically published hacking tools and exploits for software vulnerabilities.
The Russian hacker group Nerf as described in a March 2006 article in the Russian hacker magazine xakep.ru.
By 2004, v1pee had adopted the moniker “Vega” on the exclusive Russian language hacking forum Mazafaka, where this user became one of the more reliable vendors of stolen payment cards.
In the years that followed, Vega would cement his reputation as a top carder on other forums, including Verified, DirectConnection, and Carder[.]pro.
Vega also became known as someone who had the inside track on “unlimited cashouts,” a globally coordinated cybercrime scheme in which crooks hack a bank or payment card processor and use cloned cards at cash machines to rapidly withdraw millions of dollars in just a few hours.
“Hi, there is work on d+p, unlimited,” Vega wrote in a private message to another user on Verified in Dec. 2012, referring to “dumps and PINs,” the slang term for stolen debit cards with the corresponding PINs that would allow ATM withdrawals.
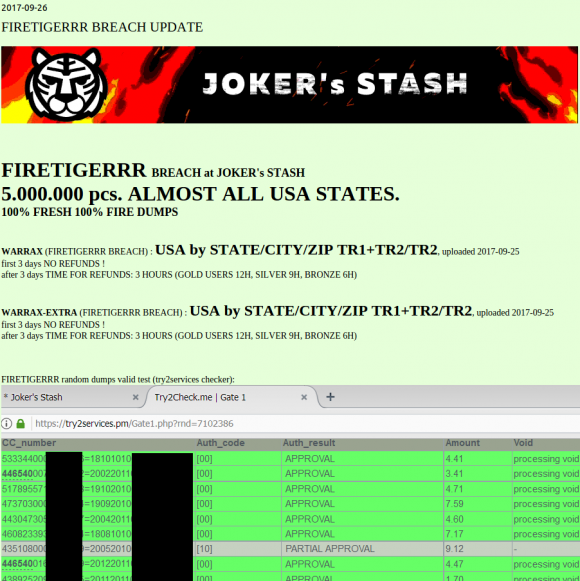
This batch of some five million cards put up for sale Sept. 26, 2017 on the now-defunct carding site Joker’s Stash has been tied to a breach at Sonic Drive-In.
Joker’s Stash came online in the wake of several enormous card breaches at retailers like Target and Home Depot, and the resulting glut of inventory had depressed prices for stolen cards. But Joker’s would distinguish itself by catering to high-roller customers — essentially street gangs in the United States that would purchase thousands of stolen payment cards in one go.
Faced with a buyer’s market, Joker’s Stash set themselves apart by focusing on loyalty programs, frequent buyer discounts, money-back guarantees, and just plain good customer service. Big spenders were given access to the most freshly hacked payment cards, and were offered the ability to get free replacement cards if any turned out to be duds.
Joker’s Stash also was unique because it claimed to sell only payment cards that its own hackers had stolen directly from merchants. At the time, card shops typically resold payment cards that were stolen and supplied by many third-party hackers of unknown reliability or reputation.
In January 2021, Joker’s Stash announced it was closing up shop, after European authorities seized a number of servers for the fraud store, and its proprietor came down with the Coronavirus.
A DOJ statement credits the U.S. Secret Service for leading the years-long investigations (the Service’s original mandate was not protecting the president; it was pursuing counterfeiters, and modern-day carders definitely qualify as that). Prosecutors allege Joker’s Stash earned revenues of at least $280 million, but possibly more than $1 billion (the broad range is a consequence of several variables, including the rapid fluctuation in the price of bitcoin and the stolen goods they were peddling).
The proprietors of Joker’s Stash may have sold tens of millions of stolen payment cards, but Taleon is by far the bigger fish in this law enforcement action because his various cryptocurrency and cash exchanges have allegedly helped to move billions of dollars into and out of Russia over the past 20 years.
An indictment unsealed today names Taleon as Sergey Sergeevich Ivanov, 44, of Saint Petersburg, Russia. The government says Ivanov, who likely changed his surname from Omelnitskii at some point, laundered money for Joker’s Stash, among many other cybercrime stores.
In a statement today, the Treasury Department said Ivanov has laundered hundreds of millions of dollars’ worth of virtual currency for ransomware actors, initial access brokers, darknet marketplace vendors, and other criminal actors for approximately the last 20 years.
First appearing on Mazafaka in the early 2000s, Taleon was known on the forums as someone who could reliably move large amounts of physical cash. Sources familiar with the investigation said Taleon’s service emerged as one of the few remaining domestic cash delivery services still operating after Russia invaded Ukraine in Feb. 2022.
Taleon set up his service to facilitate transfers between Moscow, St. Petersburg and financial institutions in the West. Taleon’s private messages on some hacker forums have been leaked over the years and indexed by the cyber intelligence platform Intel 471. Those messages indicate Taleon worked on many of the same ATM cashouts as Vegas, so it’s clear the two had an established business relationship well before Joker’s Stash came into being.
Sometime around 2013, Taleon launched a partnership with a money transfer business called pm2btc[.]me. PM2BTC allowed customers to convert funds from the virtual currency Perfect Money (PM) into bitcoin, and then have the balance (minus a processing fee) available on a physical debit card that could be used at ATMs, for shopping online, or at retail stores.
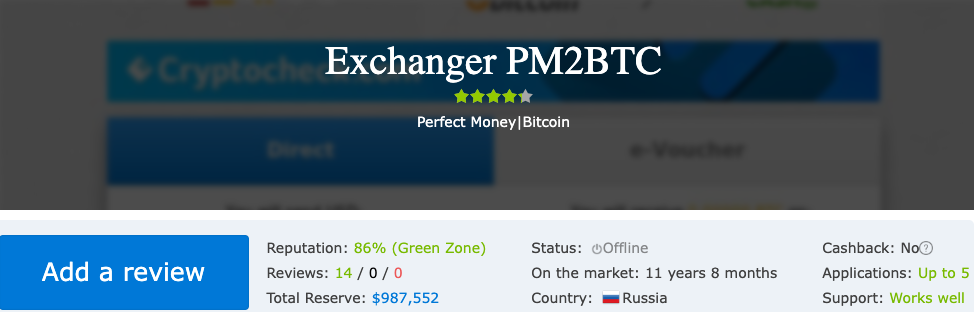
A screenshot of a website reviewing PM2BTC.
The U.S. government itself set things in motion for Taleon’s nascent cryptocurrency exchange business in 2013 after the DOJ levied money laundering charges against the proprietors of Liberty Reserve, one of the largest virtual currencies in operation at the time. Liberty Reserve was heavily used by cybercriminals of all stripes. The government said the service had more than a million users worldwide, and laundered in excess of $6 billion in suspected criminal proceeds.
In the days following the takedown of Liberty Reserve, KrebsOnSecurity ran a story that examined discussions across multiple top Russian cybercrime forums about where crooks could feel safe parking their stolen funds. The answer involved Bitcoin, but also Taleon’s new service.
Part of the appeal of Taleon’s exchange was that it gave its vetted customers an “application programming interface” or API that made it simple for dodgy online shops selling stolen goods and cybercrime services to accept cryptocurrency deposits from their customers, and to manage payouts to any suppliers and affiliates.
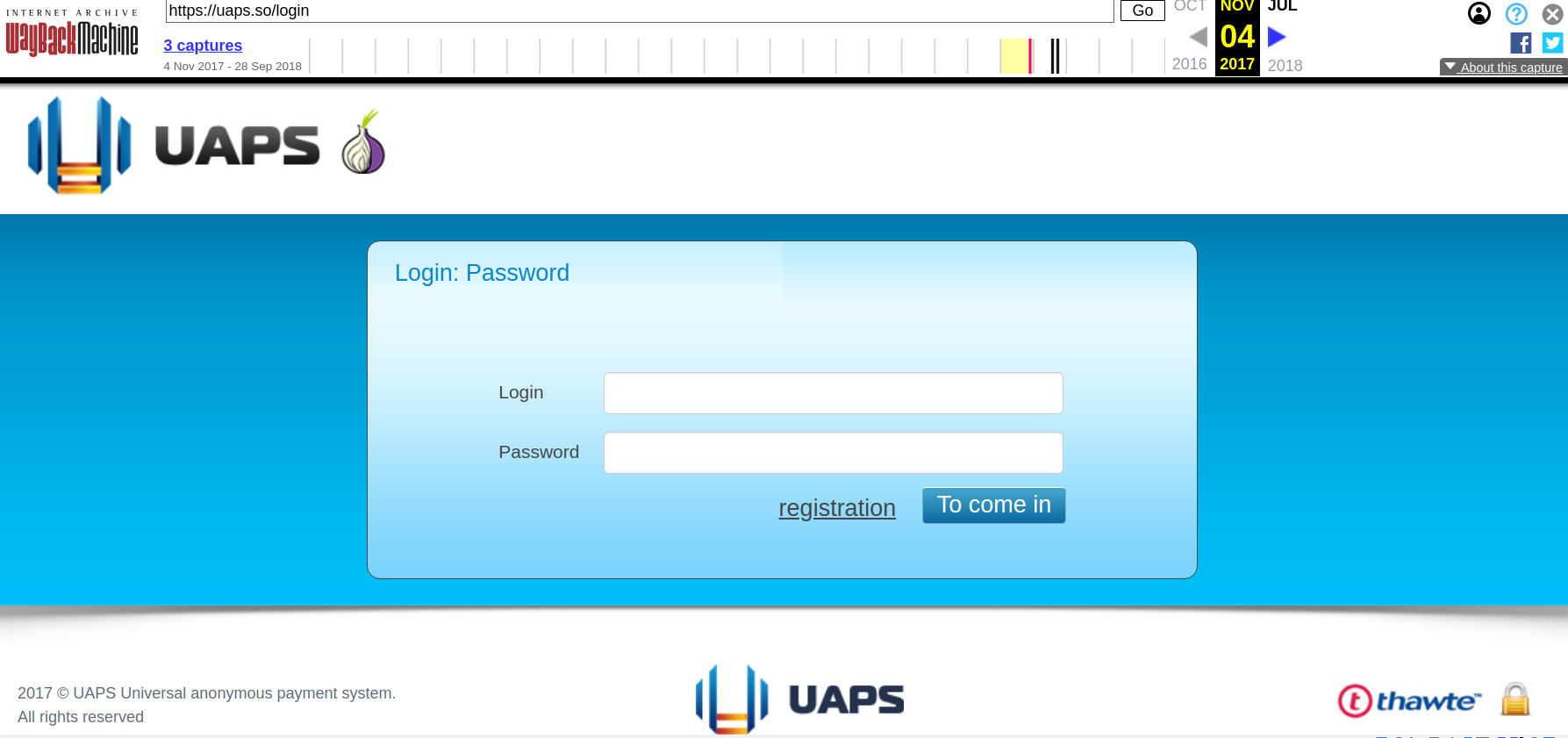
This API is synonymous with a service Taleon and friends operate in the background called UAPS, short for “Universal Anonymous Payment System.” UAPS has gone by several other names including “Pinpays,” and in October 2014 it landed Joker’s Stash as its first big client.
A source with knowledge of the investigation told KrebsOnSecurity that Taleon is a pilot who owns and flies around in his own helicopter.
Ivanov appears to have little to no social media presence, but the 40-year-old woman he lives with in St. Petersburg does, and she has a photo on her Vktontake page that shows the two of them in 2019 flying over Lake Ladoga, a large body of water directly north of St. Petersburg.

Sergey “Taleon” Ivanov (right) in 2019 in his helicopter with the woman he lives with, flying over a lake north of St. Petersburg, Russia.
In late 2015, a major competitor to Joker’s Stash emerged using UAPS for its back-end payments: BriansClub. BriansClub sullies this author’s name, photos and reputation to peddle millions of credit and debit cards stolen from merchants in the United States and around the world.
An ad for BriansClub has been using my name and likeness for years to peddle millions of stolen credit cards.
In 2019, someone hacked BriansClub and relieved the fraud shop of more than 26 million stolen payment cards — an estimated one-third of the 87 million payment card accounts that were on sale across all underground shops at that time. An anonymous source shared that card data with KrebsOnSecurity, which ultimately shared it with a consortium of financial institutions that issued most of the cards.
After that incident, the administrator of BriansClub changed the site’s login page so that it featured a copy of my phone bill, Social Security card, and a link to my full credit report [to this day, random cybercriminals confuse Yours Truly with the proprietor of BriansClub].
Alex Holden is founder of the Milwaukee-based cybersecurity firm Hold Security. Holden has long maintained visibility into cryptocurrency transactions made by BriansClub.
Holden said those records show BriansClub sells tens of thousands of dollars worth of stolen credit cards every day, and that in the last two years alone the BriansClub administrator has removed more than $242 million worth of cryptocurrency revenue from the UAPS platform.
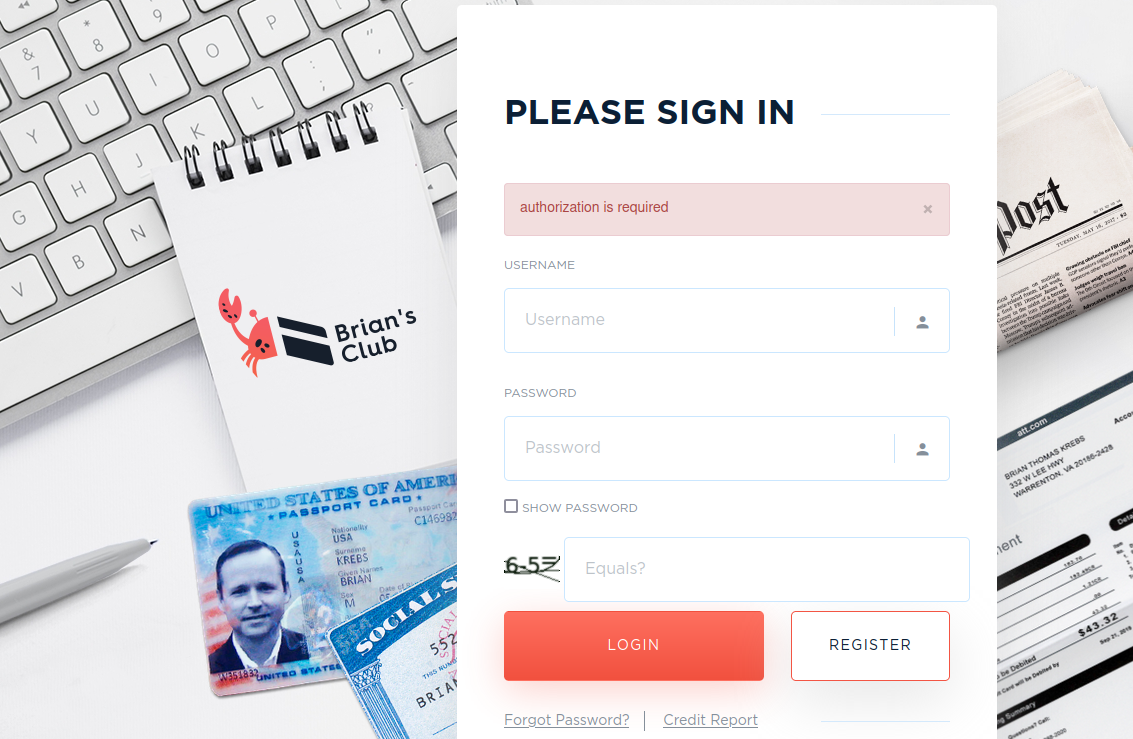
The BriansClub login page, as it looked from late 2019 until recently.
Passive domain name system (DNS) records show that in its early days BriansClub shared a server in Lithuania along with just a handful of other domains, including secure.pinpays[.]com, the crime forum Verified, and a slew of carding shops operating under the banner Rescator.
As KrebsOnSecurity detailed in December 2023, the Rescator shops were directly involved in some of the largest payment card breaches of the past decade. Those include the 2013 breach at Target and the 2014 breach at Home Depot, intrusions that exposed more than 100 million payment card records.
In early 2018, Taleon and the proprietors of UAPS launched a cryptocurrency exchange called Cryptex[.]net that has emerged as a major mover of ill-gotten crypto coins.
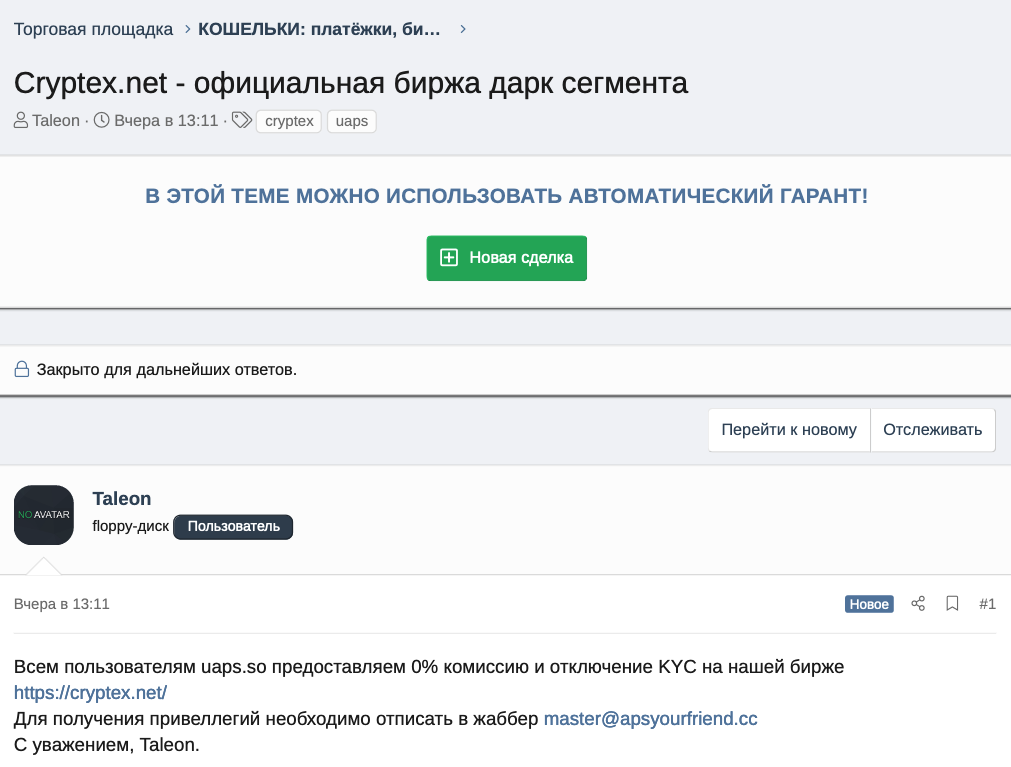
Taleon reminds UAPS customers they will enjoy 0% commission and no “know your customer” (KYC) requirements “on our exchange Cryptex.”
Cryptex has been associated with quite a few ransomware transactions, including the largest known ransomware payment to date. In February 2024, a Fortune 50 ransomware victim paid a record $75 million ransom to a Russian cybercrime group that calls themselves the Dark Angels. A source with knowledge of the investigation said an analysis of that payment shows roughly half of it was processed through Cryptex.
That source provided a screen shot of Cryptex’s sending and receiving exposure as viewed by Chainalysis, a company the U.S. government and many cryptocurrency exchanges rely on to flag transactions associated with suspected money laundering, ransomware payouts, or facilitating payments for darknet websites.
Chainalysis finds that Cryptex has received more than $1.6 billion since its inception, and that this amount is roughly equal to its sending exposure (although the total number of outflows is nearly half of the inflows).
The graphic indicates a great deal of money flowing into Cryptex — roughly a quarter of it — is coming from bitcoin ATMs around the world. Experts say most of those ATM inflows to Cryptex are bitcoin ATM cash deposits from customers of carding websites like BriansClub and Jokers Stash.
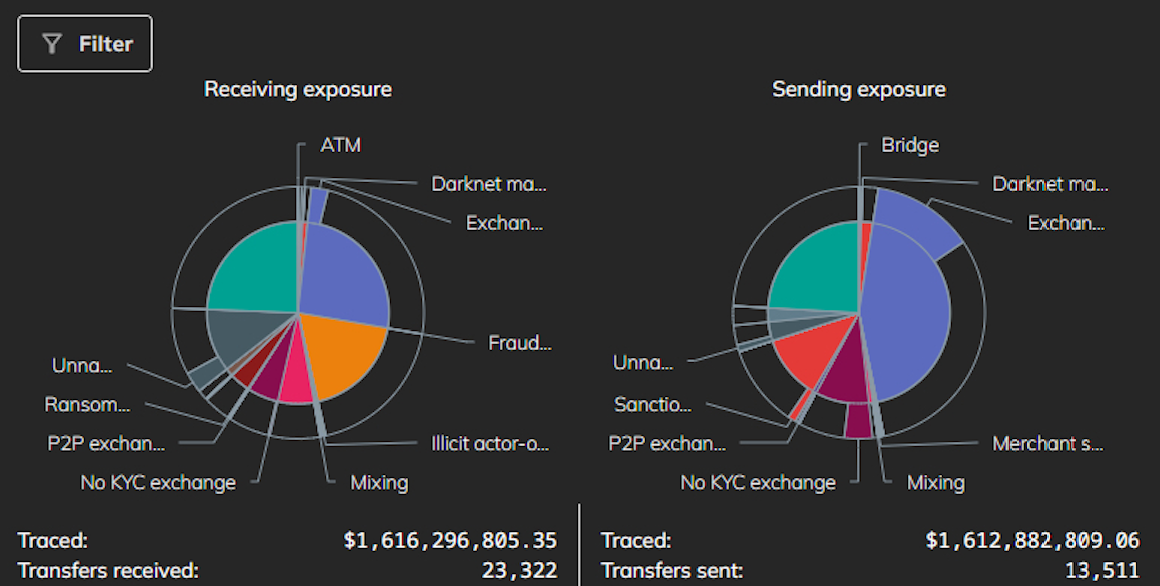
A screenshot of Chainalysis’s summary of illicit activity on Cryptex since the exchange’s inception in 2018.
The indictments released today do not definitively connect Taleon to Cryptex. However, PM2BTC (which teamed up with Taleon to launch UAPS and Pinpays) and Cryptex have now been sanctioned by the U.S. Department of the Treasury.
Treasury’s Financial Crimes Enforcement Network (FinCEN) levied sanctions today against PM2BTC under a powerful new “Section 9714” authority included in the Combating Russian Money Laundering Act, changes enacted in 2022 to make it easier to target financial entities involved in laundering money for Russia.
Treasury first used this authority last year against Bitzlato, a cryptocurrency exchange operating in Russia that became a money laundering conduit for ransomware attackers and dark market dealers.
An investigation into the corporate entities behind UAPS and Cryptex reveals an organization incorporated in 2012 in Scotland called Orbest Investments LP. Records from the United Kingdom’s business registry show the owners of Orbest Investments are two entities: CS Proxy Solutions CY, and RM Everton Ltd.
Public business records further reveal that CS Proxy Solutions and RM Everton are co-owners of Progate Solutions, a holding company that featured prominently in a June 2017 report from Bellingcat and Transparency International (PDF) on money laundering networks tied to the Kremlin.
“Law enforcement agencies believe that the total amount laundered through this process could be as high as US$80 billion,” the joint report reads. “Although it is not clear where all of this money came from, investigators claim it includes significant amounts of money that were diverted from the Russian treasury and state contracts.”
Their story built on reporting published earlier that year by the Organized Crime and Corruption Project (OCCRP) and Novaya Gazeta, which found that at least US$20.8 billion was secretly moved out of Russia between 2010 and 2014 through a vast money laundering machine comprising over 5,000 legal entities known as “The Laundromat.”

Image: occrp.org
“Using company records, reporters tracked the names of some clients after executives refused to give them out,” the OCCRP report explains. “They found the heavy users of the scheme were rich and powerful Russians who had made their fortunes from dealing with the Russian state.”
Rich Sanders is a blockchain analyst and investigator who advises the law enforcement and intelligence community. Sanders just returned from a three-week sojourn through Ukraine, traveling with Ukrainian soldiers while mapping out dodgy Russian crypto exchanges that are laundering money for narcotics networks operating in the region. Sanders said today’s sanctions by the Treasury Department will likely have an immediate impact on Cryptex and its customers.
“Whenever an entity is sanctioned, the implications on-chain are immense,” Sanders told KrebsOnSecurity. “Regardless of whether an exchange is actually compliant or just virtue signals it, it is the case across the board that exchanges will pay attention to these sanctions.”
“This action shows these payment processors for illicit platforms will get attention eventually,” Sanders continued. “Even if it took way too long in this case, Cryptex knew the majority of their volume was problematic, knew why it was problematic, and did it anyway. And this should be a wake up call for other exchanges that know full well that most of their volume is problematic.”
The U.S. Department of State is offering a reward of up to $10 million each for information leading to the arrests and/or convictions of Shakhmametov and Ivanov. The State announcement says separate rewards of up to $1 million each are being offered for information leading to the identification of other leaders of the Joker’s Stash criminal marketplace (other than Shakhmametov), as well as the identification of other key leaders of the UAPS, PM2BTC, and PinPays transnational criminal groups (other than Ivanov).
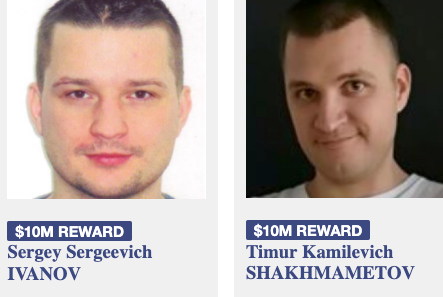
Image: U.S. Secret Service.
The U.S. government is warning that “smart locks” securing entry to an estimated 50,000 dwellings nationwide contain hard-coded credentials that can be used to remotely open any of the locks. The lock’s maker Chirp Systems remains unresponsive, even though it was first notified about the critical weakness in March 2021. Meanwhile, Chirp’s parent company, RealPage, Inc., is being sued by multiple U.S. states for allegedly colluding with landlords to illegally raise rents.
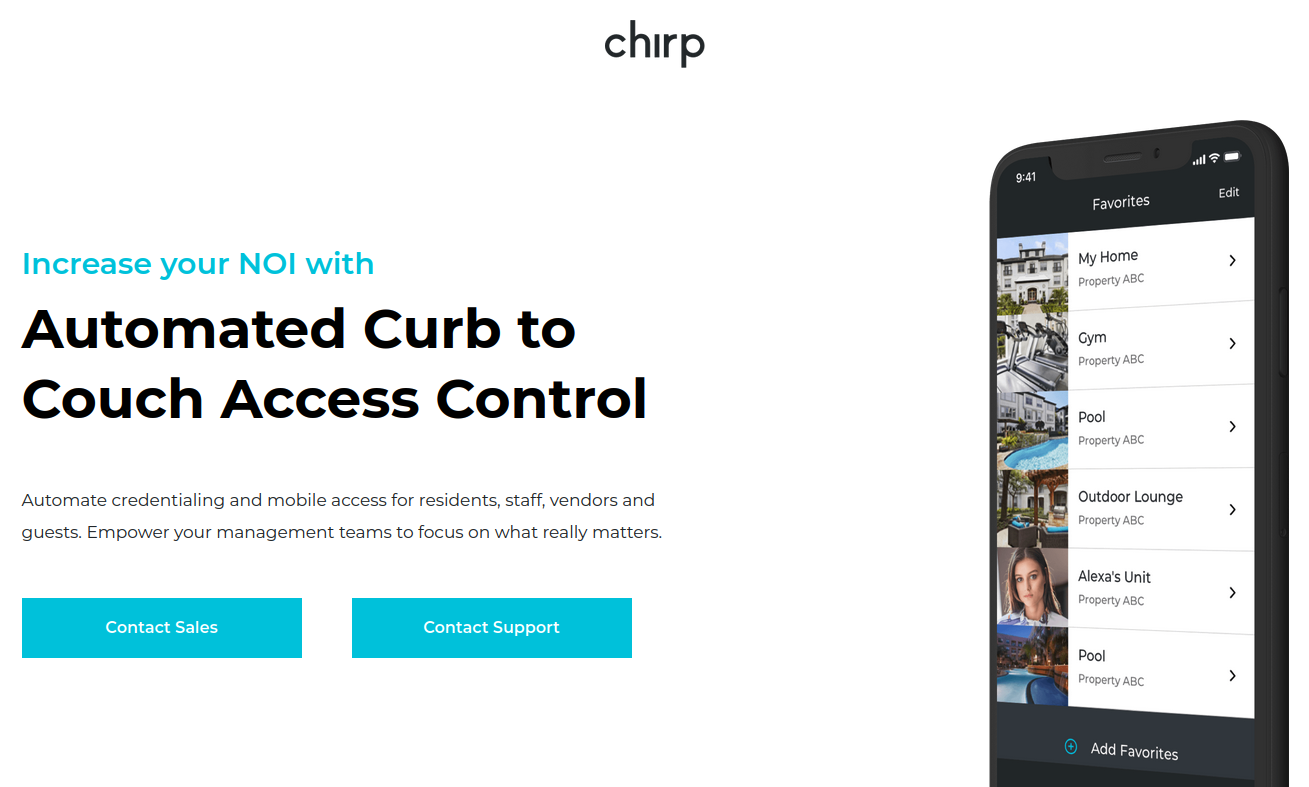
On March 7, 2024, the U.S. Cybersecurity & Infrastructure Security Agency (CISA) warned about a remotely exploitable vulnerability with “low attack complexity” in Chirp Systems smart locks.
“Chirp Access improperly stores credentials within its source code, potentially exposing sensitive information to unauthorized access,” CISA’s alert warned, assigning the bug a CVSS (badness) rating of 9.1 (out of a possible 10). “Chirp Systems has not responded to requests to work with CISA to mitigate this vulnerability.”
Matt Brown, the researcher CISA credits with reporting the flaw, is a senior systems development engineer at Amazon Web Services. Brown said he discovered the weakness and reported it to Chirp in March 2021, after the company that manages his apartment building started using Chirp smart locks and told everyone to install Chirp’s app to get in and out of their apartments.
“I use Android, which has a pretty simple workflow for downloading and decompiling the APK apps,” Brown told KrebsOnSecurity. “Given that I am pretty picky about what I trust on my devices, I downloaded Chirp and after decompiling, found that they were storing passwords and private key strings in a file.”
Using those hard-coded credentials, Brown found an attacker could then connect to an application programming interface (API) that Chirp uses which is managed by smart lock vendor August.com, and use that to enumerate and remotely lock or unlock any door in any building that uses the technology.
Update, April 18, 11:55 a.m. ET: August has provided a statement saying it does not believe August or Yale locks are vulnerable to the hack described by Brown.
“We were recently made aware of a vulnerability disclosure regarding access control systems provided by Chirp, using August and Yale locks in multifamily housing,” the company said. “Upon learning of these reports, we immediately and thoroughly investigated these claims. Our investigation found no evidence that would substantiate the vulnerability claims in either our product or Chirp’s as it relates to our systems.”
Update, April 25, 2:45 p.m. ET: Based on feedback from Chirp, CISA has downgraded the severity of this flaw and revised their security advisory to say that the hard-coded credentials do not appear to expose the devices to remote locking or unlocking. CISA says the hardcoded credentials could be used by an attacker within the range of Bluetooth (~30 meters) “to change the configuration settings within the Bluetooth beacon, effectively removing Bluetooth visibility from the device. This does not affect the device’s ability to lock or unlock access points, and access points can still be operated remotely by unauthorized users via other means.”
Brown said when he complained to his leasing office, they sold him a small $50 key fob that uses Near-Field Communications (NFC) to toggle the lock when he brings the fob close to his front door. But he said the fob doesn’t eliminate the ability for anyone to remotely unlock his front door using the exposed credentials and the Chirp mobile app.
Also, the fobs pass the credentials to his front door over the air in plain text, meaning someone could clone the fob just by bumping against him with a smartphone app made to read and write NFC tags.
Neither August nor Chirp Systems responded to requests for comment. It’s unclear exactly how many apartments and other residences are using the vulnerable Chirp locks, but multiple articles about the company from 2020 state that approximately 50,000 units use Chirp smart locks with August’s API.
Roughly a year before Brown reported the flaw to Chirp Systems, the company was bought by RealPage, a firm founded in 1998 as a developer of multifamily property management and data analytics software. In 2021, RealPage was acquired by the private equity giant Thoma Bravo.
Brown said the exposure he found in Chirp’s products is “an obvious flaw that is super easy to fix.”
“It’s just a matter of them being motivated to do it,” he said. “But they’re part of a private equity company now, so they’re not answerable to anybody. It’s too bad, because it’s not like residents of [the affected] properties have another choice. It’s either agree to use the app or move.”
In October 2022, an investigation by ProPublica examined RealPage’s dominance in the rent-setting software market, and that it found “uses a mysterious algorithm to help landlords push the highest possible rents on tenants.”
“For tenants, the system upends the practice of negotiating with apartment building staff,” ProPublica found. “RealPage discourages bargaining with renters and has even recommended that landlords in some cases accept a lower occupancy rate in order to raise rents and make more money. One of the algorithm’s developers told ProPublica that leasing agents had ‘too much empathy’ compared to computer generated pricing.”
Last year, the U.S. Department of Justice threw its weight behind a massive lawsuit filed by dozens of tenants who are accusing the $9 billion apartment software company of helping landlords collude to inflate rents.
In February 2024, attorneys general for Arizona and the District of Columbia sued RealPage, alleging RealPage’s software helped create a rental monopoly.
Introducing Tiny File Manager [WH1Z-Edition], the compact and efficient solution for managing your files and folders with enhanced privacy and security features. Gone are the days of relying on external resources – I've stripped down the code to its core, making it truly lightweight and perfect for deployment in environments without internet access or outbound connections.
Designed for simplicity and speed, Tiny File Manager [WH1Z-Edition] retains all the essential functionalities you need for storing, uploading, editing, and managing your files directly from your web browser. With a single-file PHP setup, you can effortlessly drop it into any folder on your server and start organizing your files immediately.
What sets Tiny File Manager [WH1Z-Edition] apart is its focus on privacy and security. By removing the reliance on external domains for CSS and JS resources, your data stays localized and protected from potential vulnerabilities or leaks. This makes it an ideal choice for scenarios where data integrity and confidentiality are paramount, including RED TEAMING exercises or restricted server environments.
Download ZIP with latest version from master branch.
Simply transfer the "tinyfilemanager-wh1z.php" file to your web hosting space – it's as easy as that! Feel free to rename the file to whatever suits your needs best.
The default credentials are as follows: admin/WH1Z@1337 and user/WH1Z123.
:warning: Caution: Before use, it is imperative to establish your own username and password within the $auth_users variable. Passwords are encrypted using password_hash().
ℹ️ You can generate a new password hash accordingly: Login as Admin -> Click Admin -> Help -> Generate new password hash
:warning: Caution: Use the built-in password generator for your privacy and security. 😉
To enable/disable authentication set $use_auth to true or false.
zip, tar)150+ languages and a selection of 35+ themesPDF/DOC/XLS/PPT/etc. Files up to 25 MB can be previewed using the Google Drive viewerdatatable js for efficient file filteringA bash script to retrieve user's .plist files on a macOS system and to convert the data inside it to a crackable hash format. (to use with John The Ripper or Hashcat)
Useful for CTFs/Pentesting/Red Teaming on macOS systems.
sudo)sudo ./osx_password_cracker.sh OUTPUT_FILE /path/to/save/.plistStealing and Duplicating SYSTEM tokens for fun & profit! We duplicate things, make twin copies, and then ride away.
You have used Metasploit's getsystem and SysInternals PSEXEC for getting system privs, correct? Well, here's a similar standalone version of that...but without the AV issues...at least for now
This tool also enables you to become TrustedInstaller, similar to what Process Hacker/System Informer can do. This functionality is very new and added in the latest code release and binary release as of 8/12/2023!
If you like this tool and would like to help support me in my efforts improving this solution and others like it, please feel free to hit me up on Patreon! https://patreon.com/G3tSyst3m
quick rundown on commands
Bypass UAC and escalate from medium integrity to high (must be member of local admin group)
Become Trusted Installer!
Duplicate Process Escalation Method
Duplicate Thread Escalation Method
Named Pipes Escalation method
Create Remote Thread injection method
ElevationStation is a privilege escalation tool. It works by borrowing from commonly used escalation techniques involving manipulating/duplicating process and thread tokens.
This was a combined effort between avoiding AV alerts using Metasploit and furthering my research into privilege escalation methods using tokens. In brief: My main goal here was to learn about token management and manipulation, and to effectively bypass AV. I knew there were other tools out there to achieve privilege escalation using token manip but I wanted to learn for myself how it all works.
Looking through the terribly organized code, you'll see I used two primary methods to get SYSTEM so far; stealing a Primary token from a SYSTEM level process, and stealing an Impersonation thread token to convert to a primary token from another SYSTEM level process. That's the general approach at least.
This was another driving force behind furthering my research. Unless one resorts to using named pipes for escalation, or inject a dll into a system level process, I couldn't see an easy way to spawn a SYSTEM shell within the same console AND meet token privilege requirements.
Let me explain...
When using CreateProcessWithToken, it ALWAYS spawns a separate cmd shell. As best that I can tell, this "bug" is unavoidable. It is unfortunate, because CreateProcessWithToken doesn't demand much as far as token privileges are concerned. Yet, if you want a shell with this Windows API you're going to have to resort to dealing with a new SYSTEM shell in a separate window
That leads us to CreateProcessAsUser. I knew this would spawn a shell within the current shell, but I needed to find a way to achieve this without resorting to using a windows service to meet the token privilege requirements, namely:
I found a way around that...stealing tokens from SYSTEM process threads :) We duplicate the thread IMPERSONATION token, set the thread token, and then convert it to primary and then re-run our enable privileges function. This time, the enabling of the two privileges above succeeds and we are presented with a shell within the same console using CreateProcessAsUser. No dll injections, no named pipe impersonations, just token manipulation/duplication.
This has come a long way so far...and I'll keep adding to it and cleaning up the code as time permits me to do so. Thanks for all the support and testing!