
Hackers are not created equal, nor do they have the same purpose. Some hackers are paid to scrutinize security systems, find loopholes, fix weaknesses, and ultimately protect organizations and people. Others exploit those same gaps for profit, power, or disruption. What separates hackers isn’t just skill level or tactics; it’s intent.
The purpose behind an attack changes everything about how hackers shape their tactics and how the hacking process unfolds: who is targeted, which methods and tools are used, how patient the attacker is, and the kind of damage they want to cause.
The primary motivations behind these cyberattacks fall into several categories, from financial gain to recognition, and sometimes even coercion. Each driver creates different risk scenarios for your digital life, from your home banking sessions to your workplace communications. Understanding a hacker’s motivations will enable you to better protect yourself and recognize potential threats in both your personal and professional life.
In this article, we’ll look at the main types of hackers you might encounter, the core motivations and mindset that drive these cyberattacks, and finally, how you can protect yourself against these attacks.
From its beginnings as an intellectual exploration in universities, hacking was driven by curiosity, learning, and the thrill of solving complex problems. Today, it has become industrialized with organized criminal groups and state-sponsored actors entering the scene.
Modern hacking has seen the emergence of advanced persistent threats and nation-state campaigns targeting critical infrastructure and combining traditional techniques with artificial intelligence. To better understand the types of hackers, here is a window into what they do and why:
These are the good guys, typically computer security experts who specialize in penetration testing and other methodologies to ensure that a company’s information systems are secure. These IT security professionals rely on a constantly evolving arsenal of technology to battle hackers.
These are the bad guys, who are typically referred to as just plain hackers. The term is often used specifically for hackers who break into networks or computers, or create computer viruses. Unfortunately, black hat hackers continue to technologically outpace white hats, often finding the path of least resistance, whether due to human error or laziness, or with a new type of attack. Hacking purists often use the term “crackers” to refer to black hat hackers, whose motivation is generally to get paid.
This is a derogatory term for black hat hackers who use borrowed programs to attack networks and deface websites in an attempt to make names for themselves. Script kiddies, sometimes called script kitties, might be beginners, but don’t be fooled by their newbie status. With the right tools and right targets, they can wreak as much havoc as a seasoned hacker.
Some hacker activists are motivated by politics or religion, while others aim to expose wrongdoing or exact revenge. Activists typically target government agencies, public services, and organizations involved in controversial issues related to defense, elections, wars, finance, or social movements. They also attack high-profile individuals, such as executives, public figures, journalists, and activists.
State-sponsored hackers have limitless time and funding to target civilians, corporations, other governments, or even prominent citizens connected to a larger objective. Their motivations are driven by their government’s strategic goals: gathering intelligence, stealing sensitive research or intellectual property, influencing public perception, or disrupting critical infrastructure. Because they are playing a long game, state-sponsored hackers are stealthy and persistent, quietly embedding themselves in systems, mapping networks, and waiting for the right moment to act.
Corporations hire hackers to infiltrate their competitors and steal trade secrets, including product designs, source code, pricing plans, customer lists, legal documents, and merger or acquisition strategies. They may hack from the outside or gain employment in order to act as a mole, impersonating recruiters, partners, or vendors to get insiders to share access. They also take advantage of weak internal controls, such as excessive permissions, unsecured file-sharing links, or poor offboarding practices. Spy hackers may use similar tactics as hacktivists or state-sponsored espionage on a smaller scale: stealthy entry, careful privilege escalation, and long-term persistence to avoid triggering alarms. The stolen data is often not leaked publicly but delivered directly to the client and used behind the scenes.
These hackers, generally motivated by religious or political beliefs, attempt to create terror, chaos, and real-world harm by disrupting critical infrastructures such as power grids, water systems, transportation networks, hospitals, emergency services, and government operations. They combine cyber operations with propaganda campaigns and physical attacks on the systems people rely on to live safely to create turmoil far beyond the screen.
Cybercriminals aren’t just faceless entities; they’re driven by specific goals that shape their tactics and targets. Understanding their motivations empowers you to recognize potential threats and better protect yourself, your family, and colleagues.
Money remains the most common motivator. These profit-driven attacks directly impact your personal finances through methods such as ransomware, credit card fraud, and identity theft. In your home, financially motivated hackers target your banking apps, shopping accounts, and personal devices to steal payment information or hold your data hostage. In the workplace, they focus on payroll systems, customer databases, and business banking credentials.
Ideologically driven hackers, called hacktivists, pursue political or social causes through cyber means. These attacks can disrupt services that you rely on daily, from public utilities to private organizations that provide essential services or take public stances on divisive issues. Your best defense involves staying informed about potential disruptions and maintaining backup communication methods for essential services.
Many hackers begin their journey with genuine curiosity about how systems work. They might probe your home network, test website security, or experiment with app vulnerabilities, not necessarily for malicious purposes, but their activities can still expose your data or disrupt services. In professional environments, these individuals might target systems or databases simply to see if they can gain access.
Some hackers seek fame, respect within hacker communities, or professional advancement rather than immediate financial benefit. They often target high-profile individuals, popular websites, or well-known companies to maximize the visibility for their exploits. If you have a significant social media following, your accounts could become targets for these attacks. They might also focus on defacing company or government websites, or leaking non-sensitive but embarrassing information.
Nation-state and corporate espionage are some of the most sophisticated threats in cyberspace, making it a top national security concern for both government and private sector. These operations compromise daily services and infrastructure such as internet service providers, email platforms, or cloud storage services to gather intelligence such as intellectual property, customer lists, or strategic planning documents.
Some hackers use cyber capabilities to intimidate or coerce victims into specific actions. In the FBI’s Internet Crime Complaint Center report for 2024, extortion was the 2nd top cybercrime by number of complaints, demonstrating the growing prevalence of coercion-based attacks. Coercion might involve compromising personal photos, social media accounts, or private communications to demand payment or behavioral changes. Workplace coercion could target executives with embarrassing information or threaten to leak sensitive business data unless demands are met.
Many real-world attacks combine multiple motivations—a financially driven criminal might also seek recognition within hacker communities, or an ideological hacker might generate revenue through ransomware. The contrast between ethical hacker motivations and malicious ones often lies in the permission, legality, and intent. Understanding why people become hackers helps you recognize that not all hacking activity is inherently malicious, although all unauthorized access ultimately poses risks to your security and privacy.
Understanding the psychology behind cyberattacks gives you a powerful advantage in protecting yourself. When you know what drives hackers, you can better spot their tactics and stay one step ahead.
Many hackers operate with the goal of achieving high reward for perceived low risk. This risk-reward imbalance motivates attackers because they can potentially access valuable personal or financial information while remaining physically distant from their victims. This means hackers often target easy opportunities, such as when you click on suspicious links or download questionable attachments, to gain access with minimal effort. For instance, a hacker would rather send 10,000 phishing emails hoping for a few bites than attempt one complex, risky attack.
Hackers exploit well-known psychological shortcuts your brain takes. They understand that you’re more likely to trust familiar-looking emails, act quickly under pressure, or follow authority figures without question. These aren’t weaknesses, these are normal human responses that attackers deliberately manipulate. For example, urgent messages claiming your account will be closed create an artificial time pressure, making you more likely to click without thinking.
Many successful cyberattacks leverage the human tendency to follow what others are doing. Hackers create fake social media profiles, forge customer reviews, or impersonate colleagues to make their requests seem legitimate and widely accepted. In ransomware attacks targeting businesses, criminals often research company hierarchies and communication styles to make their demands appear to come from trusted sources within the organization.
Modern hacking has elements that make it feel like a game to perpetrators. Some online forums award points for successful attacks, creating competition and recognition among criminals. This helps explain why some hackers target individuals rather than large corporations, as every successful phishing attempt becomes a score, and why attacks continue to evolve.
Hackers don’t all use the same tricks, but most successful attacks rely on a familiar toolkit of methods that exploit common technical gaps and human habits. Recognizing these common techniques will help you avoid danger earlier on.
Your strongest defense against hacking combines technical safeguards, security awareness, and some consistent habits that shut down the most common paths attackers use. Here’s how to put those defenses in place and make your digital life a much harder target.
Now that you understand hackers’ motivations and psychological drivers, you can flip the script and turn it to your advantage. Instead of being the target, become the informed defender who recognizes manipulation tactics and responds thoughtfully rather than reactively. This knowledge empowers you to spot potential threats earlier, choose stronger protective measures, and navigate the digital world with greater confidence.
When someone pressures you to act immediately, that’s your cue to slow down and verify the request. Question familiar-looking messages, even if they look official. Check the sender’s address and contact the company through official channels. Trust your instincts and investigate before acting. Stay curious and keep learning from reputable cybersecurity resources that publish current research and threat intelligence. Share these tips with your family members and friends, especially those who might be less technologically savvy.
McAfee+ includes proactive identity surveillance to monitor subscribers’ credit and personal information, as well as access to live fraud resolution agents who can help subscribers work through the process of resolving identity theft issues.
The post 7 Types of Hacker Motivations appeared first on McAfee Blog.

It’s no longer possible to deny that your life in the physical world and your digital life are one and the same. Coming to terms with this reality will help you make better decisions in many aspects of your life.
The same identity you use at work, at home, and with friends also exists in apps, inboxes, accounts, devices, and databases, whether you actively post online or prefer to stay quiet. Every purchase, login, location ping, and message leaves a trail. And that trail shapes what people, companies, and scammers can learn about you, how they can reach you, and what they might try to take.
That’s why digital security isn’t just an IT or a “tech person” problem. It’s a daily life skill. When you understand how your digital life works, what information you’re sharing, where it’s stored, and how it can be misused, you make better decisions. This guide is designed to help you build that awareness and translate it into practical habits: protecting your data, securing your accounts, and staying in control of your privacy in a world that’s always connected.
Being digitally secure doesn’t mean hiding from the internet or using complicated tools you don’t understand. It means having intentional control over your digital life to reduce risks while still being able to live, work, and communicate online safely. A digitally secure person focuses on four interconnected areas:
Your personal data is the foundation of your digital identity. Protecting it includes limiting how much data you share, understanding where it’s stored, and reducing how easily it can be collected, sold, or stolen. At its heart, personal information falls into two critical categories that require different levels of protection:
Account security ensures that only you can access them. Strong, unique passwords, multi-factor authentication, and secure recovery options prevent criminals from hijacking your email, banking, cloud storage, social media, and other online accounts, often the gateway to everything else in your digital life.
Privacy control means setting boundaries and deciding who can see what about you, and under what circumstances. This includes managing social media visibility, app permissions, browser tracking, and third-party access to your data.
Digital security is an ongoing effort as threats evolve, platforms change their policies, and new technologies introduce new risks. Staying digitally secure requires periodic check-ins, learning to recognize scams and manipulation, and adjusting your habits as the digital landscape changes.
Your personal information faces exposure risks through multiple channels during routine digital activities, often without your explicit knowledge.
Implementing comprehensive personal data protection requires a systematic approach that addresses the common exposure points. These practical steps provide layers of security that work together to minimize your exposure to identity theft and fraud.
Start by conducting a thorough audit of your online accounts and subscriptions to identify where you have unnecessarily shared more data than needed. Remove or minimize details that aren’t essential for the service to function. Moving forward, provide only the minimum required information to new accounts and avoid linking them across different platforms unless necessary.
Be particularly cautious with loyalty programs, surveys, and promotional offers that ask for extensive personal information, as they may share it with third parties. Read privacy policies carefully, focusing on sections that describe data sharing, retention periods, and your rights regarding your personal information.
If possible, consider using separate email addresses for different accounts to limit cross-platform tracking and reduce the impact if one account is compromised. Create dedicated email addresses for shopping, social media, newsletters, and important accounts like banking and healthcare.
Privacy protection requires regular attention to your account settings across all platforms and services you use. Social media platforms frequently update their privacy policies and settings, often defaulting to less private configurations that allow them to collect and share your data. For this reason, it is a good idea to review your privacy settings at least quarterly. Limit who can see your posts, contact information, and friend lists. Disable location tracking, facial recognition, and advertising customization features that rely on your personal data. Turn off automatic photo tagging and prevent search engines from indexing your profile.
On Google accounts, visit your Activity Controls and disable Web & App Activity, Location History, and YouTube History to stop this data from being saved. You can even opt out of ad personalization entirely if desired by adjusting Google Ad Settings. If you are more tech savvy, Google Takeout allows you to export and review what data Google has collected about you.
For Apple ID accounts, you can navigate to System Preferences on Mac or Settings on iOS devices to disable location-based Apple ads, limit app tracking, and review which apps have access to your contacts, photos, and other personal data.
Meanwhile, Amazon accounts store extensive purchase history, voice recordings from Alexa devices, and browsing behavior. Review your privacy settings to limit data sharing with third parties, delete voice recordings, and manage your advertising preferences.
Regularly audit the permissions you’ve granted to installed applications. Many apps request far more permissions to your location, contacts, camera, and microphone even though they don’t need them. Cancel these unnecessary permissions, and be particularly cautious about granting access to sensitive data.
Create passwords that actually protect you; they should be long and complex enough that even sophisticated attacks can’t easily break them. Combine uppercase letters, lowercase letters, numbers, and special characters to make it harder for attackers to crack.
Aside from passwords, enable multi-factor authentication (MFA) on your most critical accounts: banking and financial services, email, cloud storage, social media, work, and healthcare. Use authenticator apps such as Google Authenticator, Microsoft Authenticator, or Authy rather than SMS-based authentication when possible, as text messages can be intercepted through SIM swapping attacks. When setting up MFA, ensure you save backup codes in a secure location and register multiple devices when possible to keep you from being locked out of your accounts if your primary authentication device is lost, stolen, or damaged.
Alternatively, many services now offer passkeys which use cryptographic keys stored on your device, providing stronger security than passwords while being more convenient to use. Consider adopting passkeys for accounts that support them, particularly for your most sensitive accounts.
Device encryption protects your personal information if your smartphone, tablet, or laptop is lost, stolen, or accessed without authorization. Modern devices typically offer built-in encryption options that are easy to enable and don’t noticeably impact performance.
You can implement automatic backup systems such as secure cloud storage services, and ensure backup data is protected. iOS users can utilize encrypted iCloud backups, while Android users should enable Google backup with encryption. Regularly test your backup systems to ensure they’re working correctly and that you can successfully restore your data when needed.
Identify major data brokers that likely have your information and look for their privacy policy or opt-out procedures, which often involves submitting a request with your personal information and waiting for confirmation that your data has been removed.
In addition, review your subscriptions and memberships to identify services you no longer use. Request account deletion rather than simply closing accounts, as many companies retain data from closed accounts. When requesting deletion, ask specifically for all personal data to be removed from their systems, including backups and archives.
Keep records of your opt-out and deletion requests, and follow up if you don’t receive confirmation within the stated timeframe. In the United States, key data broker companies include Acxiom, LexisNexis, Experian, Equifax, TransUnion, Whitepages, Spokeo, BeenVerified, and PeopleFinder. Visit each company’s website.
Connect only to trusted, secure networks to reduce the risk of your data being intercepted by attackers lurking behind unsecured or fake Wi-Fi connections. Avoid logging into sensitive accounts on public networks in coffee shops, airports, or hotels, and use encrypted connections such as HTTPS or a virtual private network to hide your IP address and block third parties from monitoring your online activities.
Rather than using a free VPN service that often collects and sells your data to generate revenue, it is better to choose a premium, reputable VPN service that doesn’t log your browsing activities and offers servers in multiple locations.
Cyber threats evolve constantly, privacy policies change, and new services collect different types of personal information, making personal data protection an ongoing process rather than a one-time task. Here are measures to help regularly maintain your personal data protection:
By implementing these systematic approaches and maintaining regular attention to your privacy settings and data sharing practices, you significantly reduce your risk of identity theft and fraud while maintaining greater control over your digital presence and personal information.
You don’t need to dramatically overhaul your entire digital security in one day, but you can start making meaningful improvements right now. Taking action today, even small steps, builds the foundation for stronger personal data protection and peace of mind in your digital life. Choose one critical account, update its password, enable multi-factor authentication, and you’ll already be significantly more secure than you were this morning. Your future self will thank you for taking these proactive steps to protect what matters most to you.
Every step you take toward better privacy protection strengthens your overall digital security and reduces your risk of becoming a victim of scams, identity theft, or unwanted surveillance. You’ve already taken the first step by learning about digital security risks and solutions. Now it’s time to put that knowledge into action with practical steps that fit seamlessly into your digital routine.
The post What Does It Take To Be Digitally Secure? appeared first on McAfee Blog.

Some years ago, a highly infectious computer worm called W32/Autorun was discovered to be infecting Windows computers. Unlike a virus, a worm such as W32/Autorun doesn’t steal anything from your computer. Instead, it spreads rapidly and opens as many security holes as possible to allow hackers to install a different form of malware that will eventually steal information, money, or both.
While this worm is less widespread today, it continues to infect older Windows operating systems that are not regularly updated. This guide will take a closer look at how the worm spreads and outline preventive measures to avoid infection.
Autorun worms primarily affect older Windows systems such as Windows XP, Vista, and early versions of Windows 7, which had AutoRun enabled by default. Microsoft recognized this security vulnerability and significantly restricted AutoRun capabilities in newer Windows versions, but millions of older systems remain at risk if they haven’t been properly updated or configured.
When an autorun worm infects your system, it can compromise both your files and privacy in several ways by stealing personal documents, capturing passwords and banking information, or installing additional malware that monitors your online activities. Some variants encrypt your files for ransom, while others turn your computer into part of a botnet used for spam or cyberattacks. The infection can also spread to family members, friends, or colleagues when you share USB drives or connect to shared networks.
While this worm is less common today due to security updates in newer Windows operating systems, the concept of autorun malware is still relevant, often evolving into new forms that spread via malicious downloads, USB drives, or network shares. These forms use clever file drops and social engineering, with detection still relying on robust antivirus and user caution.
W32/Autorun is effective because it exploits everyday behaviors and outdated system features. Instead of forcing its way into your computer, it relies on built-in Windows functionality and simple tricks to get users to let it in, slip past basic defenses, and infect systems.
An autorun worm spreads, as its name suggests, automatically through removable storage devices such as USB drives, external hard drives, and network shares. It takes advantage of Windows’ AutoRun and AutoPlay features to secretly execute itself when you connect the removable device to your computer that has AutoRun. A dialog box then pops up asking if you want to automatically run whatever is on the device. When you unsuspectingly click “run,” you’ve authorized the W32/Autorun worm. Once active, the worm copies itself to other connected drives and network locations, rapidly spreading to any system. While this feature was not included in Windows 8 for security reasons just like this, it still exists on many older machines that haven’t been updated in a while.
Even if you don’t have Windows AutoRun enabled in your device, W32/Autorun disguises itself as interesting imposter files and folders with names like “porn” and “sexy” in infected flash drives or shared internet connections to trick you into downloading the worm. Once you click on the malicious file, it executes AutoRun and infects your computer.
The worm can also change your computer’s settings to allow it to run every time you boot up. Some variants even disable Windows updates to prevent the system from downloading security patches and ensure the worm can do its job of infecting every device your computer comes into contact with, opening the door for any virus a hacker wants to install at your expense.
A W32/Autorun worm infection works quietly in the background, spreading to connected devices and weakening your system’s defenses without triggering immediate alarms. However, there are subtle signs that indicate the infection. Recognizing these early symptoms can help you take action to block the worm’s activities before it causes irreparable damage to your device and network:
The impact of the W32/Autorun worm can vary depending on the specific variant, ranging from minor annoyances to severe system compromise:
Preventing a W32/Autorun infection is largely about closing the simple security gaps the worm relies on to spread. By taking these steps, you can significantly reduce the chances of this worm gaining access to your computer.
If your computer is still prompting you to automatically run applications each time you insert a CD, connect to a new network, or plug in a flash drive, update your computer as soon as possible. Visit the Microsoft website to learn how to disable AutoRun for your specific version of Windows.
Remember that this worm is highly infectious. If you share a flash drive with a friend whose computer is infected, that flash drive will carry the worm to your computer. If you do need to share a device, make sure AutoRun is disabled before you plug it in, and check that your security protection has the capability to scan new drives to prevent you from clicking on infected files.
While the first two tips focus on prevention, a reliable security solution will not only prevent a W32/Autorun infection, but also remove it from your computer. Solutions like McAfee+ will catch the W32/Autorun worm bug and other similar malware, protecting you from accidentally spreading it to friends and family.
Autorun worms represent a persistent threat that combines old vulnerabilities with modern attack techniques. Newer security measures may have reduced their impact, but these worms continue to target systems with outdated configurations through the continued use of removable media. This is why keeping systems updated and being cautious with external devices are important habits to apply.
In addition, you can protect yourself with proper security practices: disable AutoRun on older systems, keep your antivirus software updated, scan external devices before accessing their contents, and avoid connecting unknown USB drives to your computer.
The post Crush that Worm before It Creeps into Your Computer appeared first on McAfee Blog.

The holidays are just around the corner and amid the hustle and bustle, many of us will fire up our devices to go online, order gifts, plan travel, and spread cheer. But while we’re getting festive, the cybercriminals are getting ready to take advantage of the influx of your good cheer to spread scams and malware.
With online shopping expected to grow by 7.9% year-on-year in the U.S. alone in 2025, according to Mastercard, and more people than ever using social media and mobile devices to connect, the cybercriminals have a lot of opportunities to spoil our fun. Using multiple devices provides the bad guys with more ways to access your valuable “digital assets,” such as personal information and files, especially if the devices are under-protected.
In this guide, let’s look into the 12 most common cybercrimes and scams of Christmas, and what you can do to keep your money, information, and holiday spirit safe.
The festive atmosphere, continued increase in online shopping activity, and charitable spirit that define the holidays create perfect conditions for scammers to exploit your generosity and urgency.
Not surprisingly, digital criminals become more active and professional during this period, driven even more by the increasing power of artificial intelligence. A new McAfee holiday shopping report revealed that 86% of consumers surveyed receive a daily average of 11 shopping-related text or email messages that seem suspicious. This includes 3 scam texts, 5 emails, and 3 social media messages. Meanwhile, 22% admit they have been scammed during a holiday season in the past.
Their scams succeed because they exploit the psychological and behavioral patterns that are rife during the holidays. The excitement and time pressure of holiday shopping often prevail over our usual caution, while the emotional aspects of gift-giving and charitable donations can be exploited and move us to be more generous. Meanwhile, scammers understand that you’re more likely to make quick purchasing decisions when the fear of missing out on limited-time offers overtakes your judgment or when you’re rushing to find the perfect gift before it’s too late.
Overall, the frenzied seasonal themes create an environment where criminals can misuse the urgency of their fake offers and cloud our judgment, making fraudulent emails and websites appear more legitimate, while you’re already operating under the stress of holiday deadlines and budget concerns. After all, holiday promotions and charity appeals are expected during this time of year.
Now that you understand the psychology behind the scams, it’s time to become more aware of the common scams that cybercriminals run during the holiday season.
As you head online this holiday season, stay on guard and stay aware of scammers’ attempts to steal your money and your information. Familiarize yourself with the “12 Scams of Christmas” to ensure a safe and happy holiday season:
Many of us use social media sites to connect with family, friends, and co-workers over the holidays, and the cybercriminals know that this is a good place to catch you off guard because we’re all “friends,” right? Here are some ways that criminals will use these channels to obtain shoppers gift money, identity or other personal information:
As the popularity of smartphone apps has grown, so have the chances of you downloading a malicious application that steals your information or sends premium-rate text messages without your knowledge. Apps ask for more permissions than they need, such as access to your contacts or location.
If you unwrap a new smartphone this holiday season, make sure that you only download applications from official app stores and check other users’ reviews, as well as the app’s permission policies, before downloading. Software, such as McAfee Mobile Security, can also help protect you against dangerous apps.
Many of us travel to visit family and friends over the holidays. We begin our journey online by looking for deals on airfare, hotels, and rental cars. Before you book, keep in mind that scammers are looking to hook you with phony travel webpages with too-fantastic deals—beautiful pictures and rock-bottom prices—to deceive you into handing over your financial details and money.
Even when you’re already on the road, you need to be careful. Sometimes, scammers who have gained unauthorized access to hotel Wi-Fi will release a malicious pop-up ad on your device screen, and prompt you to install software before connecting. If you agree to the installation, it downloads malware onto your machine. To thwart such an attempt, it’s important that you perform a security software update before traveling.
You are probably already familiar with email phishing and SMiShing messages containing questionable offers and links. The scammer will mimic a legitimate organization offering cheap Rolex watches and luxury products as the “perfect gift” for that special someone, or send a message posing as your bank with a holiday promo and try to lure you into revealing information or direct you to a fake webpage. Never respond to these scams or click on an included link. Be aware that real banks won’t ask you to divulge personal information via text message. If you have any questions about your accounts, you should contact your bank directly.
QR code phishing, or “quishing,” has emerged as a significant new threat during holiday shopping seasons. In this scam method, cybercriminals place malicious QR codes in holiday advertisements posted on social media or printed flyers, parking meters and payment kiosks at shopping centers, or at restaurant tables during holiday dining. They could also email attachments claiming to offer exclusive holiday deals or fake shipping labels placed over legitimate tracking QR codes.
The kind of excitement and buzz surrounding Apple’s new iPad and iPhone is just what cybercrooks dream of when they plot their scams. They will mention must-have holiday gifts in dangerous links, phony contests, and phishing emails to grab your attention. Once they’ve caught your eye, they will again try to get you to reveal personal information or click on a dangerous link that could download malware onto your machine. Be suspicious of any deal mentioning hot holiday gift items—especially at extremely low prices—and try to verify the offer with the real retailer involved.
Cybercriminals exploit employee expectations of year-end communications by creating fake emails that appear to come from your HR department. These messages often claim to contain annual bonus information, updated benefits packages, or mandatory holiday attendance announcements. These scams are particularly effective because they prey on legitimate employee concerns about compensation, benefits, and personal time off during the holiday season. The emails often feature real-looking company logos, proper formatting, and even references to company policies to increase their credibility.
Gift cards are probably the perfect gift for some people on your holiday list. Given their popularity, cybercriminals can’t help but want to get in on the action by offering bogus gift cards online. Be wary of buying gift cards from third parties. It’s best to buy from the official retailer. Just imagine how embarrassing it would be to find out that the gift card you gave your mother-in-law was fraudulent!
No matter what gift you’re looking for, chances are you can find it quickly and easily online, but you still want to be careful in selecting which site to shop. By promoting great deals, phony e-commerce sites will try to convince you to type in your credit card number and other personal details. After obtaining your money and information, you never receive the merchandise, and your personal information is put at risk. To prevent falling victim to bogus e-commerce stores, shop only at trusted and well-known e-commerce sites. If you’re shopping on a site for the first time, check other users’ reviews and verify that the phone number listed on the site is legitimate.
This is one of the biggest scams of every holiday season. As we open our hearts and wallets, the bad guys will send spam emails and pretend to be a real charity in the hope of getting in on the giving. Their emails will sport a stolen logo and copycat text, or come from an entirely invented charity. If you want to give, it’s always safer to visit the charity’s legitimate website, and do a little research about the charity before you donate.
E-cards are a popular way to send a quick “thank you” or holiday greeting. While most e-cards are safe, some are malicious and may contain spyware or viruses that download onto your computer once you click on the link to view the greeting. Before clicking, look for clues that the e-card is legitimate. Make sure it comes from a well-known e-card site by checking the domain name of the included link. Also check to see that the sender is someone you actually know, and that there are no misspellings or other red flags that the card is a fake.
With increased package deliveries during the holiday season, fake shipping notifications have become a common attack. These messages claim to be from legitimate shipping companies such as UPS, FedEx, or DHL, informing you of package delivery attempts or shipping delays. To complete the delivery, these notices will ask you to click on malicious links or attachments that will download malware or direct you to fake websites that will steal personal information. The timing of these attacks coincides with legitimate increased shipping activity, making them harder to distinguish from authentic communications. To track your deliveries, it is best to check the shipping company’s real website or through the trusted platform from which you ordered the product.
Knowing about these common scam tactics is only the first step toward protecting yourself and those you care about. The next step is for you to learn and implement practical, effective strategies to stay safe while still enjoying digital holiday shopping and giving.
The holiday season brings joy and connection, but it’s also a time when scammers work hardest to exploit your festive but rushed and distracted spirit. Effective Christmas scam prevention starts with awareness. By slowing down and taking a moment to verify before you click or buy, and using layered cybersecurity protections, you can worry about one less thing and focus on what matters most this season.
Stay security-conscious without letting fear diminish your holiday enjoyment and pursue your digital holiday activities with the right knowledge and tools. We hope that the specific, actionable protections will help you identify red flags, verify legitimate offers, secure your devices and accounts, and respond effectively to suspicious activity. Stay informed by following trusted sources for the latest cybersecurity tips during the holidays, and make this season about celebrating safely with the people you care about most.
Send the link to this page to your family and friends to increase their awareness and take steps to protect themselves.
The post The Top 12 Scams Of Christmas To Watch Out For appeared first on McAfee Blog.

Thanksgiving—not before Halloween as we see things in stores and online now. It seems like the holiday season and decorations start earlier and earlier every year.
But one thing that hasn’t changed is that Black Friday is still a big shopping day. With the advent of online shopping has emerged Cyber Monday, another big sale day for online shoppers on the first Monday after Thanksgiving.
Although many of us may take advantage of these great deals that the holidays offer, we also need to be aware of the risks. Online shopping is a fun and convenient way to make purchases, locate hard-to-find items, and discover bargains, but we need to take steps to protect ourselves.
This guide looks at the methods and warning signs behind online shopping scams, shows you how to recognize fake shopping apps and websites, and shares tips for staying safe online.
Online shopping has become a cornerstone of American life. CapitalOne Shopping projects American online spending to reach $1.34 trillion in 2024 and exceed $2.5 trillion in 2030.
With such a massive sum at stake, cybercriminals are laser-focused on taking a share of it, posing financial risk to the 288 million Americans who shop online. As e-commerce grows, so does fraud. In 2024, e-commerce fraud was valued at $44.3 billion, a number seen to grow by 141% to $107 billion in 2029.
Be that as it may, there are many smart shopping habits you can apply to dramatically reduce your risk of becoming a victim of online shopping fraud and enjoy the convenience and benefits of online commerce.
Online shopping scams are designed to look normal—at first glance—especially during busy sale seasons when we’re distracted by a million preparations, moving fast, and chasing deals. These are the very circumstances that fraudsters bank on to victimize you into taking the bait. Being aware of the common scam indicators will help you pause and think, recognize trouble early, and protect both your money and your personal information.
Safe online shopping starts with recognizing the hallmarks of legitimate retailers. Before you enter any payment details, take a moment to verify that the website you’re shopping on is genuine. Scam stores can look polished and convincing, but they often leave behind subtle clues. Here are quick ways to check their authenticity:
 trustmark, indicating that the site has been scanned and verified as secure by a trusted third party. This security seal indicates that the site will help protect you from identity theft, credit card fraud, spam, and other malicious threats.
trustmark, indicating that the site has been scanned and verified as secure by a trusted third party. This security seal indicates that the site will help protect you from identity theft, credit card fraud, spam, and other malicious threats.The FTC also recommends these additional tips so you can enjoy all the advantages that online shopping has to offer and prevent risking your personal information.
Online shopping should feel exciting, not a dangerous undertaking you have to brace for, especially during the season of giving. It can be, with a few simple steps—checking the URL, looking for HTTPS, verifying the seller, paying with a credit card or virtual number, and trusting your gut when something feels suspicious. These small habits will keep your money and your identity where they belong: with you.
For increased safety while shopping online, seek out the help of a trusted security solution such as McAfee+ that will alert you of risky links and compromised websites to prevent identity theft or malware infection.
If this guide helps you, pass it along to someone you care about. Scams don’t just target individuals—they cascade into families and friend groups. The more we normalize safe shopping habits and increase our vigilance, the harder it is for fraudsters to win. If you ever feel unsure mid-purchase, take a breath and double-check. A few extra seconds now can save you a lot of stress later. Stay safe, and happy shopping!
The post Helpful Tips for Safe Online Shopping appeared first on McAfee Blog.

New online threats emerge every day, putting our personal information, money and devices at risk. In its 2024 Internet Crime Report, the Federal Bureau of Investigation reports that 859,532 complaints of suspected internet crime—including ransomware, viruses and malware, data breaches, denials of service, and other forms of cyberattack—resulted in losses of over $16 billion—a 33% increase from 2023.
That’s why it is essential to stay ahead of these threats. One way to combat these is by conducting virus scans using proven software tools that constantly monitor and check your devices while safeguarding your sensitive information. In this article, we’ll go through everything you need to know to run a scan effectively to keep your computers, phones and tablets in tip-top shape.
Whether you think you might have a virus on your computer or devices or just want to keep them running smoothly, it’s easy to do a virus scan.
Each antivirus program works a little differently, but in general the software will look for known malware with specific characteristics, as well as their variants that have a similar code base. Some antivirus software even checks for suspicious behavior. If the software comes across a dangerous program or piece of code, the antivirus software removes it. In some cases, a dangerous program can be replaced with a clean one from the manufacturer.
Before doing a virus scan, it is useful to know the telltale signs of viral presence in your device. Is your device acting sluggish or having a hard time booting up? Have you noticed missing files or a lack of storage space? Have you noticed emails or messages sent from your account that you did not write? Perhaps you’ve noticed changes to your browser homepage or settings? Maybe you’re seeing unexpected pop-up windows, or experiencing crashes and other program errors. These are just some signs that your device may have a virus, but don’t get too worried yet because many of these issues can be resolved with a virus scan.
Free virus scanner tools, both in web-based and downloadable formats, offer a convenient way to perform a one-time check for malware. They are most useful when you need a second opinion or are asking yourself, “do I have a virus?” after noticing something suspect.
However, it’s critical to be cautious. For one, cybercriminals often create fake “free” virus checker tools that are actually malware in disguise. If you opt for free scanning tools, it is best to lean on highly reputable cybersecurity brands. On your app store or browser, navigate to a proven online scanning tool with good reviews or a website whose URL starts with “https” to confirm you are in a secure location.
Secondly, free tools are frequently quite basic and perform only the minimum required service. If you choose to go this path, look for free trial versions that offer access to the full suite of premium features, including real-time protection, a firewall, and a VPN. This will give you a glimpse of a solution’s comprehensive, multi-layered security capability before you commit to a subscription.
If safeguarding all your computers and mobile devices individually sounds overwhelming, you can opt for comprehensive security products that protect computers, smartphones and tablets from a central, cloud-based hub, making virus prevention a breeze. Many of these modern antivirus solutions are powered by both local and cloud-based technologies to reduce the strain on your computer’s resources.
This guide will walk you through the simple steps to safely scan your computer using reliable online tools, helping you detect potential threats, and protect your personal data.
When selecting the right antivirus software, look beyond a basic virus scan and consider these key features:
The process of checking for viruses depends on the device type and its operating system. Generally, however, the virus scanner will display a “Scan” button to start the process of checking your system’s files and apps.
Here are more specific tips to help you scan your computers, phones and tablets:
If you use Windows 11, go into “Settings” and drill down to the “Privacy & Security > Windows Security > Virus & Threat Protection” tab, which will indicate if there are actions needed. This hands-off function is Microsoft’s own basic antivirus solution called Windows Defender. Built directly into the operating system and enabled by default, this solution provides a baseline of protection at no extra cost for casual Windows users. However, Microsoft is the first to admit that it lags behind specialized paid products in detecting the very latest zero-day threats.
Mac computers don’t have a built-in antivirus program, so you will have to download security software to do a virus scan. As mentioned, free antivirus applications are available online, but we recommend investing in trusted software that is proven to protect you from cyberthreats.
If you decide to invest in more robust antivirus software, running a scan is usually straightforward and intuitive. For more detailed instructions, we suggest searching the software’s help menu or going online and following their step-by-step instructions.
Smartphones and tablets are powerful devices that you likely use for nearly every online operation in your daily life from banking, emailing, messaging, connecting, and storing personal information. This opens your mobile device to getting infected through malicious apps, especially those downloaded from unofficial stores, phishing links sent via text or email, or by connecting to compromised wi-fi networks.
Regular virus scans with a mobile security software are crucial for protecting your devices. Be aware, however, that Android and IOS operating systems merit distinct solutions.
Antivirus products for Android devices abound due to this system’s open-source foundation. However, due to Apple’s strong security model, which includes app sandboxing, traditional viruses are rare on iPhones and iPads. However, these devices are not immune to all threats. You can still fall victim to phishing scams, insecure Wi-Fi networks, and malicious configuration profiles. Signs of a compromise can include unusual calendar events, frequent browser redirects, or unexpected pop-ups.
Apple devices, however, closed platform doesn’t easily accommodate third-party applications, especially unvetted ones. You will most likely find robust and verified antivirus scanning tools on Apple’s official app store.
Before you open any downloaded file or email attachment, it’s wise to check it for threats. To perform a targeted virus scan on a single file, simply right-click the file in Windows Explorer or macOS Finder and select the “Scan” option from the context menu to run the integrated virus checker on a suspicious item.
For an added layer of security, especially involving files from unknown sources, you can use a web-based file-checking service that scans for malware. These websites let you upload a file, which is then analyzed by multiple antivirus engines. Many security-conscious email clients also automatically scan incoming attachments, but a manual scan provides crucial, final-line defense before execution.
Once the scan is complete, the tool will display a report of any threats it found, including the name of the malware and the location of the infected file. If your antivirus software alerts you to a threat, don’t panic—it means the program is doing its job.
The first and most critical step is to follow the software’s instructions. It might direct you to quarantine the malicious file to isolate the file in a secure vault where it can no longer cause harm. You can then review the details of the threat provided by your virus scanner and choose to delete the file permanently, which is usually the safest option.
After the threat is handled, ensure your antivirus software and operating system are fully updated. Finally, run a new, full system virus scan to confirm that all traces of the infection have been eliminated. Regularly backing up your important data to an external drive or cloud service can also be a lifesaver in the event of a serious infection.
The most effective way to maintain your device’s security is to automate your defenses. A quality antivirus suite allows you to easily schedule a regular virus scan so you’re always protected without having to do it manually. A daily quick scan is a great habit for any user; it’s fast and checks the most vulnerable parts of your system. Most antivirus products regularly scan your computer or device in the background, so a manual scan is only needed if you notice something dubious, like crashes or excessive pop-ups. You can also set regular scans on your schedule, but a weekly full scan is ideal.
These days, it is essential to stay ahead of the wide variety of continuously evolving cyberthreats. Your first line of defense against these threats is to regularly conduct a virus scan. You can choose among the many free yet limited-time products or comprehensive, cloud-based solutions.
While many free versions legitimately perform their intended function, it’s critical to be cautious as these are more often baseline solutions while some are malware in disguise. They also lack the continuous, real-time protection necessary to block threats proactively.
A better option is to invest in verified, trustworthy, and all-in-one antivirus products like McAfee+ that, aside from its accurate virus scanning tool, also offers a firewall, a virtual private network, and identity protection. For complete peace of mind, upgrading to a paid solution like McAfee Total Protection is essential for proactively safeguarding your devices and data in real-time, 24/7.
The post How to Scan for Viruses and Confirm Your Device Is Safe appeared first on McAfee Blog.

Private tech companies gather tremendous amounts of user data. These companies can afford to let you use social media platforms free of charge because it’s paid for by your data, attention, and time.
Big tech derives most of its profits by selling your attention to advertisers — a well-known business model. Various documentaries (like Netflix’s “The Social Dilemma”) have tried to get to the bottom of the complex algorithms that big tech companies employ to mine and analyze user data for the benefit of third-party advertisers.
Tech companies benefit from personal info by being able to provide personalized ads. When you click “yes” at the end of a terms and conditions agreement found on some web pages, you might be allowing the companies to collect the following data:
For someone unfamiliar with privacy issues, it is important to understand the extent of big tech’s tracking and data collection. After these companies collect data, all this info can be supplied to third-party businesses or used to improve user experience.
The problem with this is that big tech has blurred the line between collecting customer data and violating user privacy in some cases. While tracking what content you interact with can be justified under the garb of personalizing the content you see, big tech platforms have been known to go too far. Prominent social networks like Facebook and LinkedIn have faced legal trouble for accessing personal user data like private messages and saved photos.
The info you provide helps build an accurate character profile and turns it into knowledge that gives actionable insights to businesses. Private data usage can be classified into three cases: selling it to data brokers, using it to improve marketing, or enhancing customer experience.
To sell your info to data brokers
Along with big data, another industry has seen rapid growth: data brokers. Data brokers buy, analyze, and package your data. Companies that collect large amounts of data on their users stand to profit from this service. Selling data to brokers is an important revenue stream for big tech companies.
Advertisers and businesses benefit from increased info on their consumers, creating a high demand for your info. The problem here is that companies like Facebook and Alphabet (Google’s parent company) have been known to mine massive amounts of user data for the sake of their advertisers.
To personalize marketing efforts
Marketing can be highly personalized thanks to the availability of large amounts of consumer data. Tracking your response to marketing campaigns can help businesses alter or improve certain aspects of their campaign to drive better results.
The problem is that most AI-based algorithms are incapable of assessing when they should stop collecting or using your info. After a point, users run the risk of being constantly subjected to intrusive ads and other unconsented marketing campaigns that pop up frequently.
To cater to the customer experience
Analyzing consumer behavior through reviews, feedback, and recommendations can help improve customer experience. Businesses have access to various facets of data that can be analyzed to show them how to meet consumer demands. This might help improve any part of a consumer’s interaction with the company, from designing special offers and discounts to improving customer relationships.
For most social media platforms, the goal is to curate a personalized feed that appeals to users and allows them to spend more time on the app. When left unmonitored, the powerful algorithms behind these social media platforms can repeatedly subject you to the same kind of content from different creators.
Here are the big tech companies that collect and mine the most user data.
Users need a comprehensive data privacy solution to tackle the rampant, large-scale data mining carried out by big tech platforms. While targeted advertisements and easily found items are beneficial, many of these companies collect and mine user data through several channels simultaneously, exploiting them in several ways.
It’s important to ensure your personal info is protected. Protection solutions like McAfee’s Personal Data Cleanup feature can help. It scours the web for traces of your personal info and helps remove it for your online privacy.
McAfee+ provides antivirus software for all your digital devices and a secure VPN connection to avoid exposure to malicious third parties while browsing the internet. Our Identity Monitoring and personal data removal solutions further remove gaps in your devices’ security systems.
With our data protection and custom guidance (complete with a protection score for each platform and tips to keep you safer), you can be sure that your internet identity is protected.
The post What Personal Data Do Companies Track? appeared first on McAfee Blog.

For millions of people, it’s not a workday without it — video conferencing. And plenty of business gets done that way, which has made conferencing a target for hackers. That then begs the important question, how secure is video conferencing?
The answer is pretty secure if you’re using a reputable service. Yet you can take further steps to keep hackers and party crashers out of your meetings.
Hackers and party crashers are likely motivated by one of two things: financial gain or mischief.
Given that some meetings involve confidential or sensitive info, someone might have financial motivation to join in, spy on, or record the meeting. Recently, we saw the lengths at least one AI company went to when it spied on a competitor’s video conference call.[i]
And of course, some bad actors want to cause a disruption. As we saw in recent years, they’ll barge right into a meeting and create a ruckus with rude speech and other antics.
Falling somewhere in between, some hackers might try to intrude on a meeting and slip a malware-laden attachment into chat.[ii] For one, that can lead to a major disruption. And in a business context, financial disruption as well.
How do they pull it off? The typical avenues of attack apply. They might use stolen or hijacked accounts. The meeting was inadvertently set to “public,” allowing anyone with a link to join. Otherwise, they might compromise a victim’s device to piggyback their way in.
Use a service with end-to-end encryption.
Put simply, end-to-end encryption provides a solid defense against prying eyes. With it in place, this form of encryption makes it particularly difficult for hackers to tap into the call and the data shared within it. Secure video conferencing should use 256-bit AES GCM encryption for audio and video, and for sharing of screens, whiteboard apps, and the like. On a related note, read the service’s privacy policy and ensure that its privacy, security, and data measures fit your needs.
Make your meetings private and protect them with a password.
Keep the uninvited out. First, setting your meeting to private (invitees only) will help keep things secure. Some apps also provide a notification to the meeting organizer when an invite gets forwarded. Use that feature if it’s available. Also, a password provides another hurdle for a hacker or bad actor to clear. Use a fresh one for each meeting.
Use the waiting room.
Many services put attendees into a waiting room before they enter the meeting proper. Use this feature to control who comes in and out.
Block users from taking control of the screen.
Welcome or unwelcome, you can keep guests from taking over the screen. Select the option to block everyone except the host (you) from screen sharing.
Turn on automatic updates on your conferencing app.
By turning on automatic updates, you’ll get the latest security patches and enhancements for your video conferencing tool as soon as they become available.
Get wise to phishing scams.
Some interlopers make it into meetings by impersonating others. Just as bad actors use phishing emails and texts to steal personal financial info, they’ll use them to steal company credentials as well. Our Phishing Scam Protection Guide can show you how to steer clear of these attacks.
Use online protection software.
Comprehensive online protection software like ours can make for safer calls in several ways. For one, it protects you against malware attacks, such as if a bad actor tries to slip a sketchy download into your meeting. Further, it includes a password manager that creates and stores strong, unique passwords securely. This can help increase the security of your video conferencing account.
This is a new one. AI deepfake technology continues to evolve, we find ourselves at the point where scammers can create AI imposters in real time.
We’ve seen them use this technology in romance scams, where scammers take on entirely new looks and voices on video calls. And we’ve seen at least one group of scammers bilk a company out of $25 million with deepfaked executives on a call.[iii]
Strange as it might sound, this kind of deepfake technology is possible today. And realizing that fact is the first step toward prevention. Next, that calls for extra scrutiny.
Any time-sensitive info or sums of money are involved, get confirmation of the request. Place a phone call to the person after receiving the request to ensure it’s indeed legitimate. Better yet, meet the individual in person if possible. In all, contact them outside the email, message, or call that initially made the request to ensure you’re not dealing with an imposter.
With the right provider and right steps in place, video calls can be quite secure. Use a solution that offers end-to-end encryption, keep your app updated for the latest security measures, and lock down the app’s security settings. Also, recognize that AI has changed the way we look at just about everything online — including people on the other side of the screen. As we’ve seen, AI imposters on calls now fall into the realm of possibility. A costly one at that.
[i] https://www.nytimes.com/2023/08/07/technology/ai-start-ups-competition.html
[ii] https://www.pcmag.com/news/hackers-circulate-malware-by-breaking-into-microsoft-teams-meetings
[iii] https://www.cnn.com/2024/02/04/asia/deepfake-cfo-scam-hong-kong-intl-hnk/index.html
The post How Secure is Video Conferencing? appeared first on McAfee Blog.

How do you protect yourself when you use public Wi-Fi on your phone? For the 40% of people who say they use public Wi-Fi that way, it’s a good question to ask.
A recent study from Forbes found that plenty of people use public Wi-Fi — with 35% saying they use it at least four times a month.[i]
People have plenty of reasons for using public Wi-Fi on their phones. First off, they might want to save their cellular data usage. Maybe they want the speed it offers over a cell connection, like when they hop on a video call. In other cases, they might have a lousy cell signal indoors and want a better connection with Wi-Fi.
All are valid reasons for using public Wi-Fi. And all are reasons for knowing how to play it safe when you do.
In an ideal world, public Wi-Fi is quite safe. The operator has it set up with the latest protection protocols, like the WP3 standard. The operator also has current, updated network equipment. You’re using it to connect to a site that uses “https” for security. And there’s no hackers or snoops in the network mix.
Of course, you can’t count on any of that every time you use public Wi-Fi.
So, what are your options if you want or need a public Wi-Fi connection?
The readiest answer is to use a VPN. As a “virtual private network,” it runs your data connection through a secure, encrypted tunnel exclusive to you. This way, it shields you and what you do from any prying eyes on public Wi-Fi.
The important bit here is to go with a trusted VPN provider. Ironically, many VPNs out there put you at risk. Some collect user info, particularly free VPNs. This gets bought and sold, and sometimes falls victim to data breaches — putting all kinds of personal info at risk.[ii] Moreover, some so-called VPNs install malware on phones instead. Others serve up ads in return for the free service.
With that, choosing a secure and trustworthy VPN provider is a must. A VPN like ours has both your security and privacy in mind. In a VPN, look for:
Not every VPN offers these features. Selecting one that does gives you the protection you want paired with the privacy you want.
Turn off automatic connections.
Be choosy about the networks you connect to. Turning off automatic connections on your phone allows you to select the trusted networks you know best.
Keep your phone updated.
Set your operating system and apps to update automatically. Updates often include security fixes that shore up recently discovered shortcomings.
Watch out for extra taps to log in.
Hackers set up sketchy public Wi-Fi as bait. With it, they might siphon off personal info as you browse, bank, and shop. Others use it to install malware, like spyware that also steals personal info. Avoid any public Wi-Fi that asks you to download extra software or apps.
Prevent third parties from collecting your info.
Some internet service providers (ISPs) offer public Wi-Fi networks in various places. However, many ISPs track, gather, and sometimes share connection info. A VPN can put a stop to plenty of that, which makes this one more good reason to use one on public Wi-Fi.
Skip public Wi-Fi altogether.
If possible, use your data connection instead. Most mobile phone providers encrypt the traffic between cell towers and your device.
[i] https://www.forbes.com/advisor/business/public-wifi-risks/
[ii] https://www.cpomagazine.com/cyber-security/free-vpn-data-leak-exposed-over-360-million-user-records/
The post How Do I Protect Myself When Using Wi-Fi? appeared first on McAfee Blog.

Are smartphones less secure than PCs? The answer to that is, they’re different. They face different security threats. Yet they certainly share one thing in common — they both need protection.
So, what makes a smartphone unique when it comes to security? And how do you go about protecting it? We’ll cover both here.
Several facts of life about smartphones set them apart when it comes to keeping your devices safer. A quick rundown looks like this:
First off, people keep lots of apps on their phones. Old ones, new ones, ones they practically forgot they had. The security issue that comes into play there is that any app on a phone is subject to vulnerabilities.
A vulnerability in just one of the dozens of apps on a phone can lead to problems. The adage of “the weakest link” applies here. The phone is only as secure as its least secure app. And that goes for the phone’s operating system as well.
Additionally, app permissions can also introduce risks. Apps often request access to different parts of your phone to work — such as when a messenger app asks for access to contacts and photos. In the case of malicious apps, they’ll ask for far more permissions than they need. A classic example involves the old “flashlight apps” that invasively asked for a wide swath of permissions. That gave the hackers all kinds of info on users, including things like location info. Today, the practice of malicious, permission-thirsty apps continues with wallpaper apps, utility apps, games, and more.
As for other malicious apps, sometimes people download them without knowing. This often happens when shopping in third-party app stores, yet it can happen in legit app stores as well — despite rigorous review processes from Apple and Google. Sometimes, hackers sneak them through the review process for approval. These apps might include spyware, ransomware, and other forms of malware.
Many people put their smartphones to personal and professional use.[i] That might mean the phone has access to corporate apps, networks, and data. If the phone gets compromised, those corporate assets might get compromised too. And it can work in the other direction. A corporate compromise might affect an employee’s smartphone.
More and more, our phones are our wallets. Digital wallets and payment apps have certainly gained popularity. They speed up checkout and make splitting meals with friends easy. That makes the prospect of a lost or stolen phone all the more serious. An unsecured phone in the hands of another is like forking over your wallet.
Lastly, spam texts. Unique to phones are the sketchy links that crop up in texting and messaging apps. These often lead to scam sites and other sites that spread malware.
With a good sense of what makes securing your smartphone unique, let’s look at several steps you can take to protect it.
Keeping your phone’s apps and operating system up to date can greatly improve your security. Updates can fix vulnerabilities that hackers rely on to pull off their malware-based attacks. it’s another tried and true method of keeping yourself safer — and for keeping your phone running great too.
With all that you keep and conduct on your phone, a lock is a must. Whether you have a PIN, passcode, or facial recognition available, put it into play. The same goes for things like your payment, banking, and financial apps. Ensure you have them locked too.
As mentioned above, app stores have measures in place to review and vet apps that help ensure they’re safe and secure. Third-party sites might very well not, and they might intentionally host malicious apps as part of a front. Further, legitimate app stores are quick to remove malicious apps from their stores once discovered, making shopping there safer still.
Check out the developer — have they published several other apps with many downloads and good reviews? A legit app typically has many reviews. In contrast, malicious apps might have only a handful of (phony) five-star reviews. Lastly, look for typos and poor grammar in both the app description and screenshots. They could be a sign that a hacker slapped the app together and quickly deployed it.
Yet better than combing through user reviews yourself is getting a recommendation from a trusted source, like a well-known publication or app store editors themselves. In this case, much of the vetting work has been done for you by an established reviewer. A quick online search like “best fitness apps” or “best apps for travelers” should turn up articles from legitimate sites that can suggest good options and describe them in detail before you download.
Another way hackers weasel their way into your device is by getting permissions to access things like your location, contacts, and photos — and they’ll use malicious apps to do it. If an app asks for way more than you bargained for, like a simple puzzle game that asks for access to your camera or microphone, it might be a scam. Delete the app.
So what happens if your phone ends up getting lost or stolen? A combination of device tracking, device locking, and remote erasing can help protect your phone and the data on it. Different device manufacturers have different ways of going about it, but the result is the same — you can prevent others from using your phone. You can even erase it if you’re truly worried that it’s gone for good. Apple provides iOS users with a step-by-step guide, and Google offers a guide for Android users as well.
Comprehensive online protection software can secure your phone in the same ways that it secures your laptops and computers. Installing it can protect your privacy, and keep you safe from attacks on public Wi-Fi, just to name a few things it can do. Ours also includes Text Scam Detector that blocks sketchy links in texts, messages, and email before they do you any harm. And if you tap that link by mistake, Text Scam Detector still blocks it.
[i] https://www.statista.com/statistics/1147490/share-adults-use-personal-smartphone-business-activities-by-country/
The post Are Mobile Devices Less Secure than PCs? appeared first on McAfee Blog.

“Vishing” occurs when criminals cold-call victims and attempt to persuade them to divulge personal information over the phone. These scammers are generally after credit card numbers and personal identifying information, which can then be used to commit financial theft. Vishing can occur both on your landline phone or via your cell phone.
The term is a combination of “voice,” and “phishing,” which is the use of spoofed emails to trick targets into clicking malicious links. Rather than email, vishing generally relies on automated phone calls that instruct targets to provide account numbers. Techniques scammers use to get your phone numbers include:
Once vishers have phone numbers, they employ various strategies to deceive their targets and obtain valuable personal information:
To protect yourself from vishing scams, you should:
Staying vigilant and informed is your best defense against vishing scams. By verifying caller identities, being skeptical of unsolicited requests for personal information, and using call-blocking tools, you can significantly reduce your risk of falling victim to these deceptive practices. Additionally, investing in identity theft protection services can provide an extra layer of security. These services monitor your personal information for suspicious activity and offer assistance in recovering from identity theft, giving you peace of mind in an increasingly digital world. Remember, proactive measures and awareness are key to safeguarding your personal information against vishing threats.
The post How to Protect Yourself from Vishing appeared first on McAfee Blog.

My mother recently turned 80, so of course a large celebration was in order. With 100 plus guests, entertainment, and catering to organise, the best way for me to keep everyone updated (and share tasks) was to use Google Docs. Gee, it worked well. My updates could immediately be seen by everyone, the family could access it from all the devices, and it was free to use! No wonder Google has a monopoly on drive and document sharing.
But here’s the thing – hackers know just how much both individuals and businesses have embraced Google products. So, it makes complete sense that they use reputable companies such as Google to devise phishing emails that are designed to extract our personal information. In fact, the Google Docs phishing scam was widely regarded as one of the most successful personal data extraction scams to date. They know that billions of people worldwide use Google so an invitation to click a link and view a document does not seem like an unreasonable email to receive. But it caused so much grief for so many people.
Emails designed to trick you into sharing your personal information are a scammer’s bread and butter. This is essentially what phishing is. It is by far the most successful tool they use to get their hands on your personal data and access your email.
‘But why do they want my email logins?’ – I hear you ask. Well, email accounts are what every scammer dreams of – they are a treasure trove of personally identifiable material that they can either steal or exploit. They could also use your email to launch a wide range of malicious activities from spamming and spoofing to spear phishing. Complicated terms, I know but in essence these are different types of phishing strategies. So, you can see why they are keen!!
But successful phishing emails usually share a few criteria which is important to know. Firstly, the email looks like it has been sent from a legitimate company e.g. Microsoft, Amex, or Google. Secondly, the email has a strong ‘call to action’ e.g. ‘your password has been changed, if this is not the case, please click here’. And thirdly, the email does not seem too out of place or random from the potential victim’s perspective.
Despite the fact that scammers are savvy tricksters, there are steps you can take to maximise the chances your email remains locked away from their prying eyes. Here’s what I suggest:
Never respond to an unexpected email or website that asks you for personal information or your login details no matter how professional it looks. If you have any doubts, always contact the company directly to verify.
Make sure you have super-duper internet security software that includes all the bells and whistles. Not only does internet security software McAfee+ include protection for daily browsing but it also has a password manager, a VPN, and a social privacy manager that will lock down your privacy settings on your social media accounts. A complete no-brainer!
Avoid using public Wi-Fi to log into your email from public places. It takes very little effort for a hacker to position themselves between you and the connection point. So, it’s entirely possible for them to be in receipt of all your private information and logins which clearly you don’t want. If you really need to use it, invest in a Virtual Private Network (VPN) which will ensure everything you share via Wi-Fi will be encrypted. Your McAfee+ subscription includes a VPN.
Public computers should also be avoided even just to ‘check your email’. Not only is there a greater chance of spyware on untrusted computers but some of them sport key-logging programs which can both monitor and record the keys you strike on the keyboard – a great way of finding out your password!
Ensuring each of your online accounts has its own unique, strong, and complex password is one of the best ways of keeping hackers out of your life. I always suggest at least 10-12 characters with a combination of upper and lower case letters, symbols, and numbers. A crazy nonsensical sentence is a great option here but better still is a password manager that will remember and generate passwords that no human could! A password manager is also part of your McAfee+ online security pack.
Even if you have taken all the necessary steps to protect your email from hackers, there is the chance that your email logins may be leaked in a data breach. A data breach happens when a company’s data is accessed by scammers and customers’ personal information is stolen. You may remember the Optus, Medibank and Latitude hacks of 2022/23?
If you have had your personal information stolen, please be assured that there are steps you can take to remedy this. The key is to act fast. Check out my recent blog post here for everything you need to know.
So, next time you’re organising a big gathering don’t hesitate to use Google Docs to plan or Microsoft Teams to host your planning meetings. While the thought of being hacked might make you want to withdraw, please don’t. Instead, cultivate a questioning mindset in both yourself and your kids, and always have a healthy amount of suspicion when going about your online life. You’ve got this!!
Till next time,
Stay safe!
Alex
The post How To Prevent Your Emails From Being Hacked appeared first on McAfee Blog.
For years now, the popularity of online dating has been on the rise—and so have the number of online romance scams that leave people with broken hearts and empty wallets.
In a recent CBS News story, one Texan woman was scammed out of $3,200 by a scammer claiming to be a German Cardiologist. After months of exchanging messages and claiming to be in love with her, he said that he’d been robbed while on a business trip in Nigeria and needed her help.
According to the U.S. Federal Trade Commission (FTC), the reported cost of online romance scams was $1.14 billion in 2023.
Dating and romance scams aren’t limited to online dating apps and sites, they’ll happen on social media and in online games as well. However, the FTC reports that the scam usually starts the same way, typically through an unexpected friend request or a message that comes out of the blue.
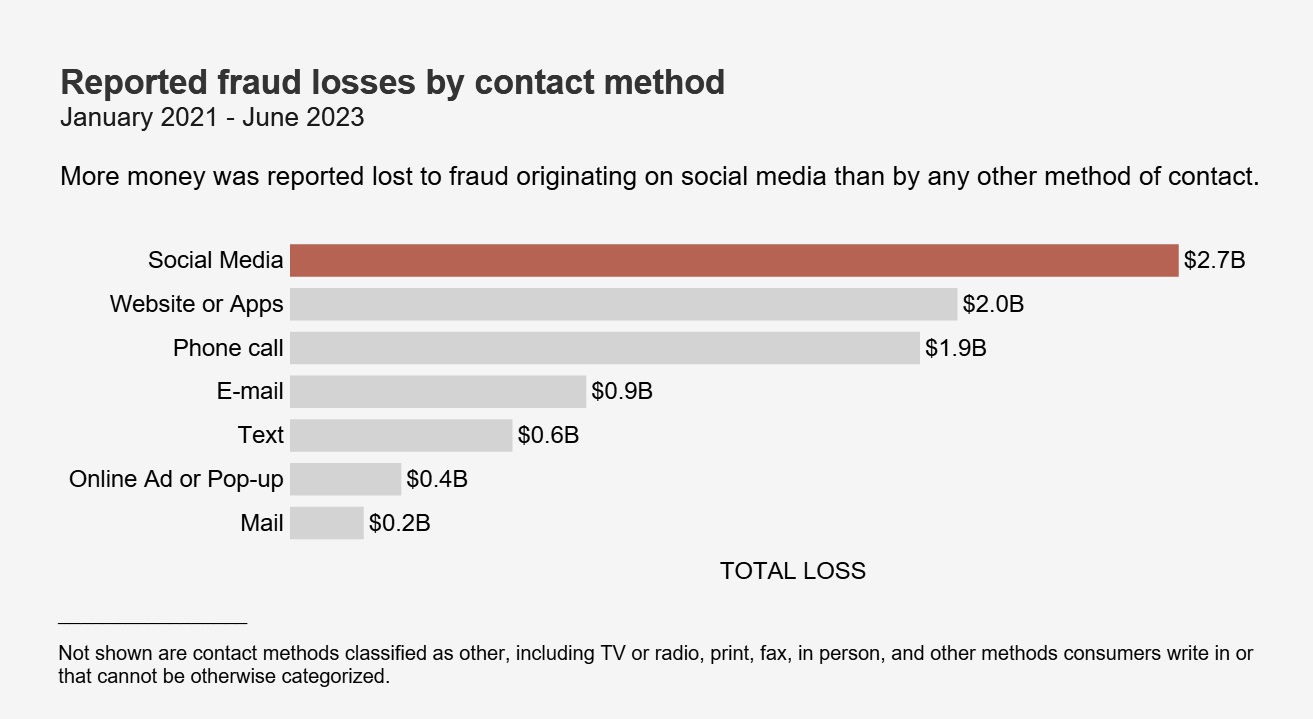
With the phony relationship established, the scammer starts asking for money. The FTC reports that they’ll ask for money for several bogus reasons, usually revolving around some sort of hardship where they need a “little help” so that they can pay:
The list goes on, yet that’s the general gist. Scammers often employ a story with an intriguing complication that seems just reasonable enough, one where the romance scammer makes it sound like they could really use the victim’s financial help.
People who have filed fraud reports say they’ve paid their scammer in a few typical ways.
One is by wiring money, often through a wire transfer company. The benefit of this route, for the scammer anyway, is that this is as good as forking over cash. Once it’s gone, it’s gone. The victim lacks the protections they have with other payment forms, such as a credit card that allows the holder to cancel or contest a charge.
Another way is through gift cards. Scammers of all stripes, not just romance scammers, like these because they effectively work like cash, whether it’s a gift card for a major online retailer or a chain of brick-and-mortar stores. Like a wire transfer, once that gift card is handed over, the money on it is highly difficult to recover, if at all.
One more common payment is through reloadable debit cards. A scammer may make an initial request for such a card and then make several follow-on requests to load it up again.
In all, a romance scammer will typically look for the easiest payment method that’s the most difficult to contest or reimburse, leaving the victim in a financial lurch once the scam ends.
When it comes to meeting new people online, the FTC suggests the following:
Scammers, although arguably heartless, are still human. They make mistakes. The stories they concoct are just that. Stories. They may jumble their details, get their times and dates all wrong, or simply get caught in an apparent lie. Also, keep in mind that some scammers may be working with several victims at once, which is yet another opportunity for them to get confused and slip up.
As mentioned above, some romance scammers troll social media and reach out through direct messages or friend requests. With that, there are three things you can do to cut down your chances of getting caught up with a scammer:
Social media platforms like Facebook, Instagram, and others give you the option of making your profile and posts visible to friends only. Choosing this setting keeps the broader internet from seeing what you’re doing, saying, and posting, which can help protect your privacy and give a romance scammer less information to exploit.
Be critical of the invitations you receive. Out-and-out strangers could be more than a romance scammer, they could be a fake account designed to gather information on users for purposes of cybercrime, or they can be an account designed to spread false information. There are plenty of them too. In fact, in Q4 of 2023 alone, Facebook took action on 693 million fake accounts. Reject such requests.
Online protection software like ours can help you spot fakes and scams. Features like Text Scam Detector use advanced AI to detect scam links in texts, email, and social media messages before you click. Our Personal Data Cleanup can keep you safer still by removing your personal info from sketchy data broker sites — places where scammers go to harvest useful info on their victims. And if the unfortunate happens, we offer $2 million in identity theft coverage and identity restoration support.
If you suspect that you’re being scammed, put an end to the relationship and report it, as difficult as that may feel.
Notify the FTC at ReportFraud.ftc.gov for support and next steps to help you recover financially as much as possible. Likewise, notify the social media site, app, or service where the scam occurred as well. In some cases, you may want to file a police report, which we cover in our broader article on identity theft and fraud.
If you sent funds via a gift card, the FTC suggests filing a claim with the company as soon as possible. They offer further advice on filing a claim here, along with a list of contact numbers for gift card brands that scammers commonly use.
Lastly, go easy on yourself. If you find yourself a victim of online dating or romance fraud, know that you won’t be the first or last person to be taken advantage of this way. By reporting your case, you in fact may help others from falling victim too.
The post How to Spot Dating Scams appeared first on McAfee Blog.