Reading view
Apple, Google, and Microsoft join Anthropic's Project Glasswing to defend world's most critical software
US cybercrime losses pass $20B for first time as AI boosts online fraud
Bots are now firmly in the toolbox, helping crooks scale old scams
Crims are taking advantage of AI to sharpen old scams. The FBI reported Monday that cybercrime losses hit a record $20.87 billion in 2025, with help from bots.…
Anthropic Opus 4.6 is less good at finding vulns than you might think
We benchmarked Opus 4.6's ability to find simple C vulns and found that the model flags about 1 in 4 flaws -- with a very high false positive rate and lots of inconsistency from run to run. Techniques like judge agents and requiring the model to justify its results improve the results to some extent, but they're still not great.
[link] [comments]
Russia Hacked Routers to Steal Microsoft Office Tokens
Hackers linked to Russia’s military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today. The spying campaign allowed state-backed Russian hackers to quietly siphon authentication tokens from users on more than 18,000 networks without deploying any malicious software or code.
Microsoft said in a blog post today it identified more than 200 organizations and 5,000 consumer devices that were caught up in a stealthy but remarkably simple spying network built by a Russia-backed threat actor known as “Forest Blizzard.”

How targeted DNS requests were redirected at the router. Image: Black Lotus Labs.
Also known as APT28 and Fancy Bear, Forest Blizzard is attributed to the military intelligence units within Russia’s General Staff Main Intelligence Directorate (GRU). APT 28 famously compromised the Hillary Clinton campaign, the Democratic National Committee, and the Democratic Congressional Campaign Committee in 2016 in an attempt to interfere with the U.S. presidential election.
Researchers at Black Lotus Labs, a security division of the Internet backbone provider Lumen, found that at the peak of its activity in December 2025, Forest Blizzard’s surveillance dragnet ensnared more than 18,000 Internet routers that were mostly unsupported, end-of-life routers, or else far behind on security updates. A new report from Lumen says the hackers primarily targeted government agencies—including ministries of foreign affairs, law enforcement, and third-party email providers.
Black Lotus Security Engineer Ryan English said the GRU hackers did not need to install malware on the targeted routers, which were mainly older Mikrotik and TP-Link devices marketed to the Small Office/Home Office (SOHO) market. Instead, they used known vulnerabilities to modify the Domain Name System (DNS) settings of the routers to include DNS servers controlled by the hackers.
As the U.K.’s National Cyber Security Centre (NCSC) notes in a new advisory detailing how Russian cyber actors have been compromising routers, DNS is what allows individuals to reach websites by typing familiar addresses, instead of associated IP addresses. In a DNS hijacking attack, bad actors interfere with this process to covertly send users to malicious websites designed to steal login details or other sensitive information.
English said the routers attacked by Forest Blizzard were reconfigured to use DNS servers that pointed to a handful of virtual private servers controlled by the attackers. Importantly, the attackers could then propagate their malicious DNS settings to all users on the local network, and from that point forward intercept any OAuth authentication tokens transmitted by those users.
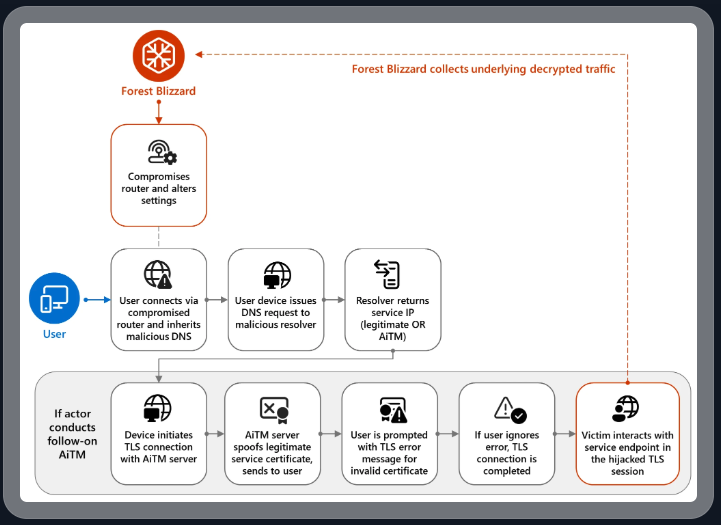
DNS hijacking through router compromise. Image: Microsoft.
Because those tokens are typically transmitted only after the user has successfully logged in and gone through multi-factor authentication, the attackers could gain direct access to victim accounts without ever having to phish each user’s credentials and/or one-time codes.
“Everyone is looking for some sophisticated malware to drop something on your mobile devices or something,” English said. “These guys didn’t use malware. They did this in an old-school, graybeard way that isn’t really sexy but it gets the job done.”
Microsoft refers to the Forest Blizzard activity as using DNS hijacking “to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains.” The software giant said while targeting SOHO devices isn’t a new tactic, this is the first time Microsoft has seen Forest Blizzard using “DNS hijacking at scale to support AiTM of TLS connections after exploiting edge devices.”
Black Lotus Labs engineer Danny Adamitis said it will be interesting to see how Forest Blizzard reacts to today’s flurry of attention to their espionage operation, noting that the group immediately switched up its tactics in response to a similar NCSC report (PDF) in August 2025. At the time, Forest Blizzard was using malware to control a far more targeted and smaller group of compromised routers. But Adamitis said the day after the NCSC report, the group quickly ditched the malware approach in favor of mass-altering the DNS settings on thousands of vulnerable routers.
“Before the last NCSC report came out they used this capability in very limited instances,” Adamitis told KrebsOnSecurity. “After the report was released they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable.”
Russia's Fancy Bear still attacking routers to boost fake sites, NCSC warns
200 orgs and 5,000 devices compromised so far in Vlad's latest intelligence grab, Microsoft reckons
The UK's National Cyber Security Centre (NCSC) has issued a fresh warning about Russia's ongoing targeting of routers to steal passwords and other secrets.…
Russian State-Linked APT28 Exploits SOHO Routers in Global DNS Hijacking Campaign

Love window snapping on Linux? You should try a tiling window manager - here's why
Why I returned to Enlightenment Linux after 30 years: Testing the new Elive beta
JavaScript runtime instrumentation via Chrome DevTools Protocol
I’ve been experimenting with Chrome DevTools Protocol primitives to build tools for reversing and debugging JavaScript at runtime.
The idea is to interact with execution by hooking functions without monkeypatching or modifying application code.
Conceptually, this is closer to a Frida-style instrumentation model (onEnter/onLeave handlers), but applied to the browser via CDP.
Early experiments include:
- attaching hooks to functions at runtime
- inspecting and modifying arguments and local variables
- overriding return values (unfortunately limited to sync functions due to CDP constraints)
- following return values to their consumer (best-effort / heuristic)
- conditional stepping (stepIn / stepOut / stepOver)
All implemented via CDP (debugger breakpoints + runtime evaluation), so this also works inside closures and non-exported code.
I’d really appreciate feedback — especially from people doing reverse engineering, bug bounty, or complex frontend debugging.
[link] [comments]
I tried Google Photos' new AI Enhance tool: How it crops, relights, and fixes your shots - sometimes
Docker CVE-2026-34040 Lets Attackers Bypass Authorization and Gain Host Access

How I calibrated my subwoofer placement for peak impact in awkward room setups
Asus' latest flagship laptop competes with the MacBook Air, but not how you'd think
I tested the AirPods Max 2, Sony XM6, and Bose Ultra 2: Why Bose is my top pick
Over 1,000 Exposed ComfyUI Instances Targeted in Cryptomining Botnet Campaign

[Webinar] How to Close Identity Gaps in 2026 Before AI Exploits Enterprise Risk

The Hidden Cost of Recurring Credential Incidents

New GPUBreach Attack Enables Full CPU Privilege Escalation via GDDR6 Bit-Flips
