Reading view
GTA cheat service Atlas Menu hacked as attacker alleges screenshot spying
⚡ Weekly Recap: New Linux Flaw, PAN-OS Exploit, AI-Powered Attacks, OAuth Phishing and More

r/netsec monthly discussion & tool thread
Questions regarding netsec and discussion related directly to netsec are welcome here, as is sharing tool links.
Rules & Guidelines
- Always maintain civil discourse. Be awesome to one another - moderator intervention will occur if necessary.
- Avoid NSFW content unless absolutely necessary. If used, mark it as being NSFW. If left unmarked, the comment will be removed entirely.
- If linking to classified content, mark it as such. If left unmarked, the comment will be removed entirely.
- Avoid use of memes. If you have something to say, say it with real words.
- All discussions and questions should directly relate to netsec.
- No tech support is to be requested or provided on r/netsec.
As always, the content & discussion guidelines should also be observed on r/netsec.
Feedback
Feedback and suggestions are welcome, but don't post it here. Please send it to the moderator inbox.
[link] [comments]
Why I built my own DIY cyberdeck straight out of 80s sci-fi - and how you can too
Are Your World Cup Tickets Legit? 40% of Fans May Risk Unofficial Sellers

Whether you’re planning a once-in-a-lifetime trip or just hoping to catch a match while it’s in your city, the 2026 FIFA World Cup is already driving a surge in ticket searches, travel bookings, and last-minute plans.
But where there’s high demand and big money, scammers aren’t far behind.
Let’s break down the new McAfee research, what scams to watch for, and how McAfee’s tools help you stay safe.
New McAfee Research Finds a Gap Between Awareness and Risk
New research from McAfee shows that while most fans are aware of World Cup-related scams, many are still willing to take risks to secure tickets.
In fact, 40% say they would consider buying from an unofficial source if they can’t get tickets through the official FIFA site, as many expect tickets to sell out and hope to find affordable resale options.
That tension is what makes events like the World Cup especially vulnerable for scams.
With limited ticket availability, rising prices, and the pressure to act quickly, even informed fans can find themselves making decisions they normally wouldn’t, like buying tickets from a reseller on TikTok.
And scammers are counting on it.
Survey takeaways:
- 76% of fans are interested in getting World Cup tickets
- 35% have already started searching online
- 43% are willing to spend over $500 on tickets
- 66% say they’re aware of World Cup-related scams
- 66% say they’re concerned about being scammed
- 40% would consider buying tickets from unofficial sources
The Most Common World Cup Scams to Watch For
Below is a comprehensive breakdown of the most common scams tied to major global sporting events like the World Cup, including how they work and what to look for.
McAfee’s Scam Detector, Safe Browsing tools, VPN, and Password Manager work together to help you spot scams like these as they happen by flagging suspicious messages, blocking risky websites, and helping you make safer decisions before you click, pay, or share information.
 Scam Type Scam Type |
What It Is | How It Works | Red Flags |
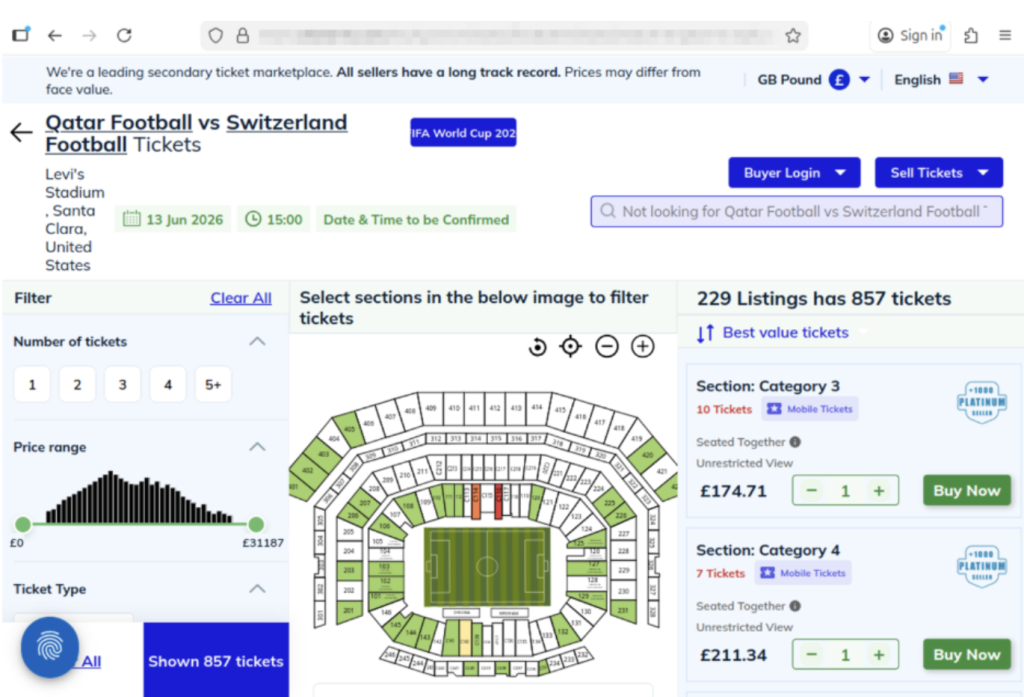
| Fake Ticket Resale Scam | Fraudulent tickets sold through unofficial sites or individuals | Scammers create fake listings or duplicate real tickets and sell them to multiple buyers | Prices far below or above market, refusal to use official transfer systems, pressure to act fast |
| Social Media Ticket Scam | Tickets sold through platforms like Instagram, Facebook, TikTok, or X | Fake or hacked accounts post “last-minute” ticket offers and move conversations to DMs | Urgent language (“only 2 left”), new or suspicious profiles, requests to pay outside the platform |
| Duplicate QR Code Scam | One legitimate ticket is resold multiple times | Multiple buyers receive the same QR code, but only the first scan works | Screenshots instead of official transfers, identical tickets sold repeatedly |
| Fake Ticket Website Scam | Websites designed to look like official ticket platforms | Victims enter payment info or purchase tickets that don’t exist | Slightly misspelled URLs, unfamiliar domains, lack of official branding verification |
| Travel & Accommodation Scam | Fake hotels, rentals, or travel packages | Listings appear legitimate but either don’t exist or are already booked | Prices that seem unusually low, requests for upfront payment, lack of verified reviews |
| Booking Impersonation Scam | Fraudsters pose as airlines, hotels, or booking platforms | Victims receive messages about “issues” with bookings and are asked to click links or provide info | Unexpected messages, requests for login or payment details, links that don’t match official sites |
| Public Wi-Fi & Phishing Scam | Data theft through unsecured networks while traveling | Scammers intercept data or create fake login portals on public Wi-Fi | Open networks with no password, login pages asking for unnecessary information |
| Fake Giveaway Scam | Promotions claiming free tickets or VIP access | Victims are asked to enter personal data, click links, or pay “processing fees” | “You’ve won” messages you didn’t enter, requests for payment to claim prizes |
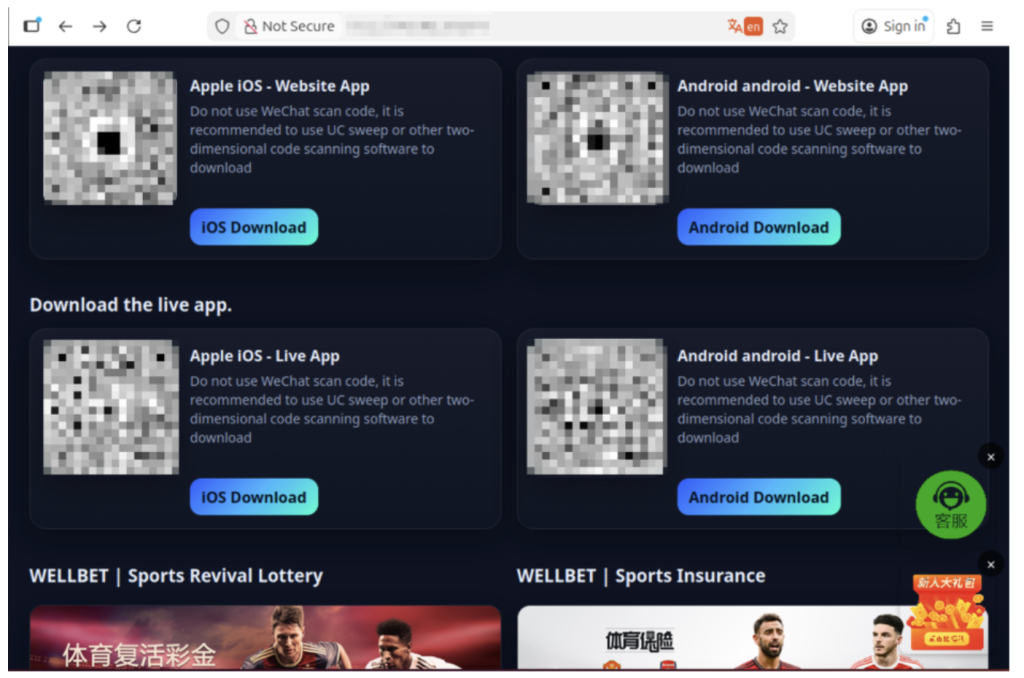
| Betting & Prediction Scam | Fake betting tips or “guaranteed wins” tied to matches | Scammers sell fake predictions or direct users to malicious betting sites | Claims of guaranteed outcomes, requests for upfront payment, unfamiliar platforms |
| Merchandise Scam | Counterfeit World Cup gear sold online | Buyers receive low-quality or no product at all | Unverified sellers, poor site quality, deals that seem too good to be true |
How AI is Making These Scams More Convincing
Unfortunately, with the continued improvement of AI, these scams are becoming more convincing.
AI tools allow scammers to create:
- More realistic websites and messages
- Personalized outreach that feels legitimate
- Fake endorsements, images, or promotions
That means traditional advice like “look for typos” is no longer enough on its own.
Today’s scams often look polished, professional, and believable.
What “Official” Actually Means (and Why It Matters)
For the World Cup, official ticket sales happen through designated FIFA sales phases and platforms.
Buying outside those channels increases the risk of:
- Invalid or duplicate tickets
- Inflated pricing without guarantees
- No recourse if something goes wrong
Even if a ticket looks legitimate, it may be:
- Sold to multiple buyers
- Already voided
- Rejected at the gate
When in doubt, go directly to the official FIFA website instead of clicking links from messages or ads. You can also visit their comprehensive FAQ section for all your ticket and event questions.
How to Stay Safe When Buying Tickets or Traveling
Here are practical steps fans can take to reduce risk:
| Safety Check | What To Do |
| Buy from official sources | Use FIFA’s official ticket platform whenever possible |
| Avoid clicking links in messages | Navigate directly to official websites instead. McAfee’s Safe Browing tools help prevent you from opening malicious links. |
| Be cautious with resale offers | Verify platforms and avoid direct peer-to-peer payments |
| Check QR codes before you scan them | You can check for QR code scams on-demand with Scam Detector |
| Don’t pay with untraceable methods | Avoid wire transfers, gift cards, or crypto-only payments |
| Double-check URLs | Look for misspellings or unusual domains |
| Use secure connections | Avoid making purchases on public Wi-Fi, or use a VPN like McAfee’s. |
| Protect your accounts | Use strong passwords and enable two-factor authentication. Consider a password manager like McAfee’s. |
| Verify before you buy | If something feels off, pause and check before sending money |
What to Do If You Think You’ve Been Scammed
If you think you may have purchased a fraudulent ticket, clicked a suspicious link, or shared information with a scammer, acting quickly can help limit the impact.
Immediate steps to take
Stop communication immediately
Do not send additional money or information, even if the sender claims you need to “complete” a transaction. It’s also a good idea to take screenshots of messages in case the scammer disappears.
Contact your bank or payment provider
Report the transaction as soon as possible. Many institutions can help reverse charges or flag fraudulent activity if caught early.
Secure your accounts
Change passwords for any accounts that may be affected, especially email, banking, and ticketing platforms. Our password manager and free password generator help create unique passwords every time.
Enable two-factor authentication (2FA)
Adding an extra layer of security can help prevent unauthorized access, even if your password was exposed.
Scan your device for threats
If you clicked a suspicious link or downloaded a file, run a security scan to check for malware or malicious software. Check out our free security scan.
Monitor for unusual activity
Keep an eye on financial accounts, email logins, and any services tied to your personal information. Our free WebAdvisor helps protect you from malware and phishing attempts while you surf.
How McAfee Helps You Spot Scams in the Moment
McAfee offers more than traditional antivirus, combining multiple layers of digital protection in one app to help you stay safer while searching, clicking, and buying online.
Scam Detector helps flag suspicious texts, emails, and videos automatically, so you can spot a scam before it hits you and your wallet
Safe Browsing tools help block risky websites, alert you to phishing attempts, and guide you away from malicious links
VPN helps keep your connection private on public Wi-Fi, protecting your personal and payment information
Password Manager helps create and store strong, unique passwords to reduce the risk of account takeover
Identity Monitoring and Alerts notify you if your personal information appears where it shouldn’t, so you can quickly take steps to fix it
Personal info removal helps find and remove your personal info from data broker sites and close out old forgotten accounts
Device and Account Security helps protect the devices and accounts you use every day
Final Thoughts
The World Cup isn’t just another event, it’s a moment when millions of people are making fast decisions involving real money, travel plans, and personal information.
What McAfee’s research makes clear is that the biggest risk isn’t a lack of awareness. Most fans already know scams exist. The risk is what happens next.
When tickets are scarce, prices are high, and the pressure to act is real, even informed consumers may take chances they normally wouldn’t. That’s where scammers succeed: not by tricking people who aren’t paying attention, but by catching people in moments of urgency.
As demand continues to build toward the tournament, more fans will be searching, comparing, and purchasing online.
The takeaway is simple: Staying safe isn’t just about knowing scams exist. It’s about slowing down, verifying before you buy, and using tools that help you make informed decisions in the moment.
*McAfee is not affiliated with or endorsed by FIFA.
The post Are Your World Cup Tickets Legit? 40% of Fans May Risk Unofficial Sellers appeared first on McAfee Blog.
Palo Alto VPN bug graduates from advisory to active exploitation

Cisco Secure Access and Microsoft Purview Integration for Simplified Data Protection
Cisco Secure Access and Island Browser Enable Zero Trust Everywhere
Finding what lives between the alerts: Announcing Cisco Talos Threat Hunting
From Log Flood to Threat Signal: Cisco and Splunk Bring Context to Modern Defense
China-Aligned Groups Ramp Up Attacks: Dragon Weave Hits Czech Republic & Taiwan

The Security Growth Platform: Why MSPs Are Moving Beyond vCISO Tools

Password manager Dashlane suspends customer accounts amid brute-force attacks

Putin sends submarines to survey Britain's subsea cables. UK deploys Royal Navy, mobilizes parliamentary draftsmen

The Romance Scammer Who Made a Small Fortune Posing as a WWE Superstar
OpenAI Codex Authentication Tokens Stolen in codexui-android npm Supply Chain Attack

Websites Can Now Spy on You Through Your Hard Drive
