ROPDump is a tool for analyzing binary executables to identify potential Return-Oriented Programming (ROP) gadgets, as well as detecting potential buffer overflow and memory leak vulnerabilities.
<binary>: Path to the binary file for analysis.-s, --search SEARCH: Optional. Search for specific instruction patterns.-f, --functions: Optional. Print function names and addresses.python3 ropdump.py /path/to/binary
python3 ropdump.py /path/to/binary -s "pop eax"
python3 ropdump.py /path/to/binary -f

Last week, a security researcher sent me 122GB of data scraped out of thousands of Telegram channels. It contained 1.7k files with 2B lines and 361M unique email addresses of which 151M had never been seen in HIBP before. Alongside those addresses were passwords and, in many cases, the website the data pertains to. I've loaded it into Have I Been Pwned (HIBP) today because there's a huge amount of previously unseen email addresses and based on all the checks I've done, it's legitimate data. That's the high-level overview, now here are the details:
Telegram is a popular messaging platform that makes it easy to stand up a "channel" and share information to those who wish to visit it. As Telegram describes the service, it's simple, private and secure and as such, has become very popular with those wishing to share content anonymously, including content related to data breaches. Many of the breaches I've previously loaded into HIBP have been distributed via Telegram as it's simple to publish this class of data to the platform. Here's what data posted to Telegram often looks like:
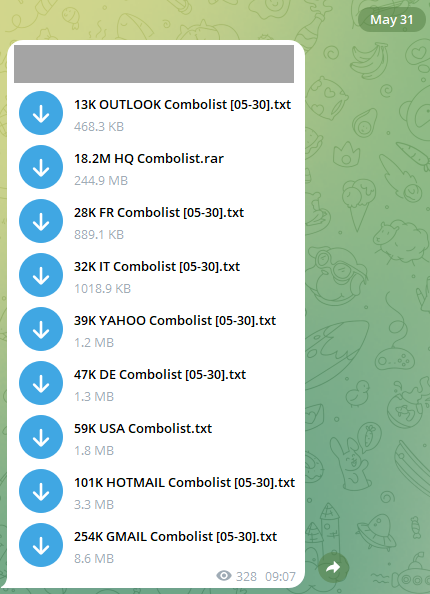
These are referred to as "combolists", that is they're combinations of email addresses or usernames and passwords. The combination of these is obviously what's used to authenticate to various services, and we often see attackers using these to mount "credential stuffing" attacks where they use the lists to attempt to access accounts en mass. The list above is simply breaking the combos into their respective email service providers. For example, that last Gmail example contains over a quarter of a million rows like this:
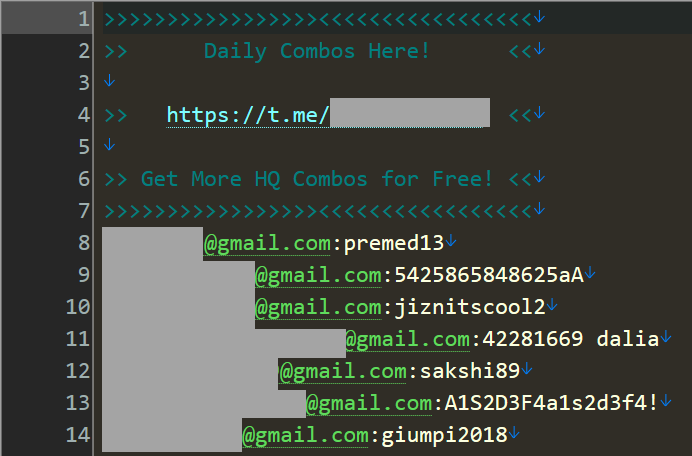
That's only one of many files across many different Telegram channels. The data that was sent to me last week was sourced from 518 different channels and amounted to 1,748 separate files similar to the one above. Some of the files have literally no data (0kb), others are many gigabytes with many tens of millions of rows. For example, the largest file starts like this:
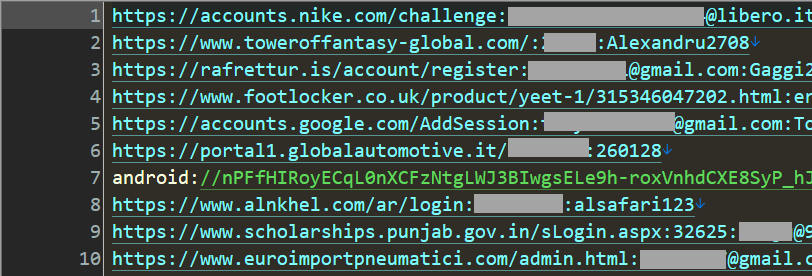
That looks very much like the result of info stealer malware that has obtained credentials as they were entered into websites on compromised machines. For example, the first record appears to have been snared when someone attempted to login to Nike. There's an easy way to get a sense of the accuracy of this data, just head over to the Nike homepage and click the login link which presents the following screen:
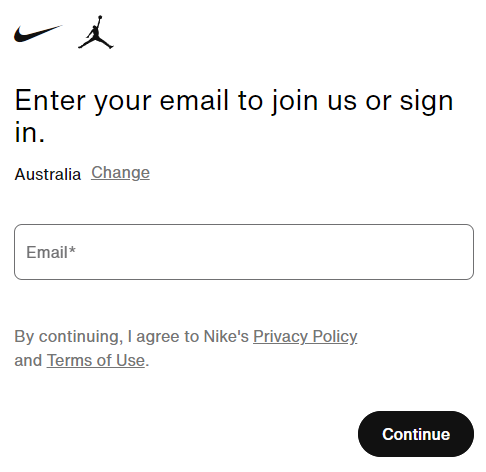
They serve the same page to both existing subscribers and new ones but then serve different pages depending on whether the email address already has an account (a classic enumeration vector). Mash the keyboard to create a fake email address and you'll be shown a registration form, but enter the address in the stealer log and, well, you get something different:
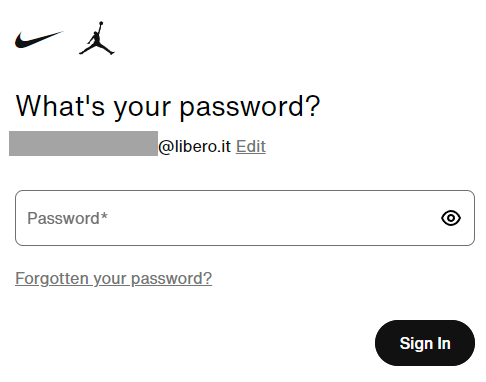
The email address has an account, hence the prompt for a password. I'm not going to test the password because that would constitute unauthorised access, but I also don't need to as the goal has already been achieved: I've demonstrated that the address has an account on Nike. (Also note that if the password didn't work it wouldn't necessarily mean it wasn't valid at some point in time at the past, it would simply mean it isn't valid now.)
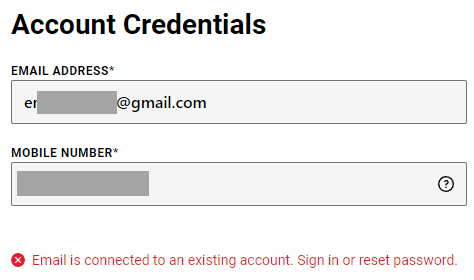
Footlocker tries to be a bit more clever in avoiding enumeration on password reset, but they'll happily tell you via the registration page if the email address you've entered already exists:
Even the Italian tyre retailer happily confirmed the existence of the tested account:
Time and time again, each service I tested confirmed the presence of the email address in the stealer log. But are (or were) the passwords correct? Again, I'm not going to test those myself, but I have nearly 5M subscribers in HIBP and there's always a handful of them in any new breach that are happy to help out. So, I emailed some of the most recent ones, asked if they could help with verification and upon confirmation, sent them their data.
In reaching out to existing subscribers, I expected some repetition in terms of them already appearing in existing data breaches. For one person already in 13 different breaches in HIBP, this was their response:
Thanks Troy. These details were leaked in previous data breaches.
So accurate, but not new, and several of the breaches for this one were of a similar structure to the one we're talking about today in terms of them being combolists used for credential stuffing attacks. Same with another subscriber who was in 7 prior breaches:
Yes that’s familiar. Most likely would have used those credentials on the previous data breaches.
That one was more interesting as of the 7 prior breaches, only 6 had passwords exposed and none of them were combolists. Instead, it was incidents including MyFitnessPal, 8fit, FlexBooker, Jefit, MyHeritage and ShopBack; have passwords been cracked out of those (most were hashed) and used to create new lists? Very possibly. (Sidenote: this unfortunate person is obviously a bit of a fitness buff and has managed to end up in 3 different "fit" breaches.)
Another subscriber had an entry in the following format, similar to what we saw earlier on in the stealer log:
https://accounts.epicgames.com/login:[email]:[password]They responded to my queries with the following:
I think that epic games account was for my daughter a couple of years ago but I cancelled it last year from memory. That sds like a password she may have chosen so I'll check with her in an hour or two when I see her again.
And then, a little bit later
My daughter doesn't remember if that was her password as it was 4-5 years ago when she was only 8-9 years old. However it does sound like something she would have chosen so in all probability, I would say that is a legitimate link. We believe it was used when she played a game called Fortnite which she did infrequently at that time hence her memory is sketchy.
I realised that whilst each of these responses confirmed the legitimacy of the data, they really weren't giving me much insight into the factor that made it worth loading into HIBP: the unseen addresses. So, I went through the same process of contacting HIBP subscribers again but this time, only the ones that I'd never seen in a breach before. This would then rule out all the repurposed prior incidents and give me a much better idea of how impactful this data really was. And that's when things got really interesting.
Let's start with the most interesting one and what you're about to see is two hundred rows of stealer logs:
https://steuer.check24.de/customer-center/aff/check24/authentication:[email]:[password]
https://www.disneyplus.com/de-de/reset-password:[email]:[password]
https://auth.rtl.de/auth/realms/rtlplus/protocol/openid-connect/auth:[email]:[password]
https://www.tink.de/checkout/login:[email]:[password]
https://signin.ebay.de/ws/eBayISAPI.dll:[email]:[password]
https://vrr-db-ticketshop.de/authentication/login:[email]:[password]
https://www.planet-sports.de/checkout/register:[email]:[password]
https://www.bstn.com/eu_de/checkout/:[email]:[password]
https://www.lico-nature.de/index.php:[email]:[password]
https://ticketshop.mobil.nrw/authentication/register:[email]:[password]
https://softwareindustrie24.de/checkout/confirm/as/customer:[email]:[password]
https://www.zurbrueggen.de/checkout/register:[email]:[password]
https://www.hertz247.de/ikeage/de-de/SignUp/Profile:[email]:[password]
https://www.bluemovement.com/de-de/checkout2:[email]:[password]
android://pfDvxsQIIXYFer6DxBcqXjgyr9X3z0_f4GlJfpZMErP2oGHX74fUnXpWA29CNgnCyZ_phC8IyV0exIV6hg3iyQ==@com.sixt.reservation/:[email]:[password]
https://members.persil-service.de/login/:[email]:[password]
https://www.nicotel.de/index.php:[email]:[password]
https://www.hellofresh.de/login:[email]:[password]
https://login.live.com/login.srf:[email]:[password]
https://accounts.login.idm.telekom.com/factorx:[email]:[password]
https://grillhaus-bei-reimann.order.dish.co/register:[email]:[password]
https://signup.sipgateteam.de/:[email]:[password]
https://www.baur.de/kasse/registrieren:[email]:[password]
https://buchung.carlundcarla.de/28572879/schritt-3:[email]:[password]
https://www.qvc.de/checkout/your-information.html:[email]:[password]
https://de.omio.com/app/search-frontend/booking/96720342-e20e-4de7-8b21-ddefc0fa44bd/passenger-details:[email]:[password]
https://www.shop-apotheke.com/nx/login/:[email]:[password]
https://druckmittel.de/checkout/confirm:[email]:[password]
https://www.global-carpet.de/checkout/confirm:[email]:[password]
https://software-hero.de/checkout/confirm:[email]:[password]
https://myenergykey.com/login:[email]:[password]
https://www.sixt.de/:[email]:[password]
https://www.wlan-shop24.de/Bestellvorgang:[email]:[password]
https://www.cyberport.de/checkout/anmelden.html:[email]:[password]
https://waschmal.de/registerCustomer:[email]:[password]
https://www.wgv.de/app/moped201802/rechner/abschluss/moped:[email]:[password]
https://www.persil-service.de/signup:[email]:[password]
https://nicotel.de/:[email]:[password]
https://temial.vorwerk.de/register/checkout:[email]:[password]
https://accounts.bahn.de/auth/realms/db/login-actions/required-action:[email]:[password].
https://www.petsdeli.de/login:[email]:[password]
https://www.netflix.com/de/login:[email]:[password]
https://login.live.com/login.srf:[email]:[password]
https://accounts.login.idm.telekom.com/factorx:[email]:[password]
https://www.netflix.com/de/login:[email]:[password]
https://www.zoll-portal.de/registrierung/benutzerkonto/daten:[email]:[password]
https://v3.account.samsung.com/iam/passwords/register:[email]:[password]
https://www.amazon.pl/ap/signin:[email]:[password]
https://www.amazon.de/:[email]:[password]
https://meinkonto.telekom-dienste.de/wiederherstellung/passwort/web-pw-setzen.xhtml:[email]:[password]
https://www.netflix.com/de/login:[email]:[password]
https://steuer.check24.de/customer-center/aff/check24/authentication [email]:[password]
https://www.disneyplus.com/de-de/reset-password [email]:[password]
https://auth.rtl.de/auth/realms/rtlplus/protocol/openid-connect/auth [email]:[password]
https://www.tink.de/checkout/login [email]:[password]
https://signin.ebay.de/ws/eBayISAPI.dll [email]:[password]
https://vrr-db-ticketshop.de/authentication/login [email]:[password]
https://www.planet-sports.de/checkout/register [email]:[password]
https://www.bstn.com/eu_de/checkout/ [email]:[password]
https://www.lico-nature.de/index.php [email]:[password]
https://ticketshop.mobil.nrw/authentication/register [email]:[password]
https://softwareindustrie24.de/checkout/confirm/as/customer [email]:[password]
https://www.zurbrueggen.de/checkout/register [email]:[password]
https://www.hertz247.de/ikeage/de-de/SignUp/Profile [email]:[password]
https://www.bluemovement.com/de-de/checkout2 [email]:[password]
android://pfDvxsQIIXYFer6DxBcqXjgyr9X3z0_f4GlJfpZMErP2oGHX74fUnXpWA29CNgnCyZ_phC8IyV0exIV6hg3iyQ==@com.sixt.reservation/[email]:[password]
https://members.persil-service.de/login/ [email]:[password]
https://www.nicotel.de/index.php [email]:[password]
https://www.hellofresh.de/login [email]:[password]
https://login.live.com/login.srf [email]:[password]
https://accounts.login.idm.telekom.com/factorx [email]:[password]
https://grillhaus-bei-reimann.order.dish.co/register [email]:[password]
https://signup.sipgateteam.de/ [email]:[password]
https://www.baur.de/kasse/registrieren [email]:[password]
https://buchung.carlundcarla.de/28572879/schritt-3 [email]:[password]
https://www.qvc.de/checkout/your-information.html [email]:[password]
https://de.omio.com/app/search-frontend/booking/96720342-e20e-4de7-8b21-ddefc0fa44bd/passenger-details [email]:[password]
https://www.shop-apotheke.com/nx/login/ [email]:[password]
https://druckmittel.de/checkout/confirm [email]:[password]
https://www.global-carpet.de/checkout/confirm [email]:[password]
https://software-hero.de/checkout/confirm [email]:[password]
https://myenergykey.com/login [email]:[password]
https://www.sixt.de/ [email]:[password]
https://www.wlan-shop24.de/Bestellvorgang [email]:[password]
https://www.cyberport.de/checkout/anmelden.html [email]:[password]
https://waschmal.de/registerCustomer [email]:[password]
https://www.wgv.de/app/moped201802/rechner/abschluss/moped [email]:[password]
https://www.persil-service.de/signup [email]:[password]
https://nicotel.de/ [email]:[password]
https://temial.vorwerk.de/register/checkout [email]:[password]
https://accounts.bahn.de/auth/realms/db/login-actions/required-action [email]:[password].
https://www.petsdeli.de/login [email]:[password]
https://www.netflix.com/de/login [email]:[password]
https://login.live.com/login.srf [email]:[password]
https://accounts.login.idm.telekom.com/factorx [email]:[password]
https://www.netflix.com/de/login [email]:[password]
https://www.zoll-portal.de/registrierung/benutzerkonto/daten [email]:[password]
https://v3.account.samsung.com/iam/passwords/register [email]:[password]
https://www.amazon.pl/ap/signin [email]:[password]
https://www.amazon.de/ [email]:[password]
https://meinkonto.telekom-dienste.de/wiederherstellung/passwort/web-pw-setzen.xhtml [email]:[password]
https://www.netflix.com/de/login [email]:[password]
https://steuer.check24.de/customer-center/aff/check24/authentication:[email]:[password]
https://www.disneyplus.com/de-de/reset-password:[email]:[password]
https://auth.rtl.de/auth/realms/rtlplus/protocol/openid-connect/auth:[email]:[password]
https://www.tink.de/checkout/login:[email]:[password]
https://signin.ebay.de/ws/eBayISAPI.dll:[email]:[password]
https://vrr-db-ticketshop.de/authentication/login:[email]:[password]
https://www.planet-sports.de/checkout/register:[email]:[password]
https://www.bstn.com/eu_de/checkout/:[email]:[password]
https://www.lico-nature.de/index.php:[email]:[password]
https://ticketshop.mobil.nrw/authentication/register:[email]:[password]
https://softwareindustrie24.de/checkout/confirm/as/customer:[email]:[password]
https://www.zurbrueggen.de/checkout/register:[email]:[password]
https://www.hertz247.de/ikeage/de-de/SignUp/Profile:[email]:[password]
https://www.bluemovement.com/de-de/checkout2:[email]:[password]
android://pfDvxsQIIXYFer6DxBcqXjgyr9X3z0_f4GlJfpZMErP2oGHX74fUnXpWA29CNgnCyZ_phC8IyV0exIV6hg3iyQ==@com.sixt.reservation/:[email]:[password]
https://members.persil-service.de/login/:[email]:[password]
https://www.nicotel.de/index.php:[email]:[password]
https://www.hellofresh.de/login:[email]:[password]
https://login.live.com/login.srf:[email]:[password]
https://accounts.login.idm.telekom.com/factorx:[email]:[password]
https://grillhaus-bei-reimann.order.dish.co/register:[email]:[password]
https://signup.sipgateteam.de/:[email]:[password]
https://www.baur.de/kasse/registrieren:[email]:[password]
https://buchung.carlundcarla.de/28572879/schritt-3:[email]:[password]
https://www.qvc.de/checkout/your-information.html:[email]:[password]
https://de.omio.com/app/search-frontend/booking/96720342-e20e-4de7-8b21-ddefc0fa44bd/passenger-details:[email]:[password]
https://www.shop-apotheke.com/nx/login/:[email]:[password]
https://druckmittel.de/checkout/confirm:[email]:[password]
https://www.global-carpet.de/checkout/confirm:[email]:[password]
https://software-hero.de/checkout/confirm:[email]:[password]
https://myenergykey.com/login:[email]:[password]
https://www.sixt.de/:[email]:[password]
https://www.wlan-shop24.de/Bestellvorgang:[email]:[password]
https://www.cyberport.de/checkout/anmelden.html:[email]:[password]
https://waschmal.de/registerCustomer:[email]:[password]
https://www.wgv.de/app/moped201802/rechner/abschluss/moped:[email]:[password]
https://www.persil-service.de/signup:[email]:[password]
https://nicotel.de/:[email]:[password]
https://temial.vorwerk.de/register/checkout:[email]:[password]
https://accounts.bahn.de/auth/realms/db/login-actions/required-action:[email]:[password].
https://www.petsdeli.de/login:[email]:[password]
https://www.netflix.com/de/login:[email]:[password]
https://login.live.com/login.srf:[email]:[password]
https://accounts.login.idm.telekom.com/factorx:[email]:[password]
https://www.netflix.com/de/login:[email]:[password]
https://www.zoll-portal.de/registrierung/benutzerkonto/daten:[email]:[password]
https://v3.account.samsung.com/iam/passwords/register:[email]:[password]
https://www.amazon.pl/ap/signin:[email]:[password]
https://www.amazon.de/:[email]:[password]
https://meinkonto.telekom-dienste.de/wiederherstellung/passwort/web-pw-setzen.xhtml:[email]:[password]
steuer.check24.de/customer-center/aff/check24/authentication:[email]:[password]
www.disneyplus.com/de-de/reset-password:[email]:[password]
auth.rtl.de/auth/realms/rtlplus/protocol/openid-connect/auth:[email]:[password]
www.tink.de/checkout/login:[email]:[password]
signin.ebay.de/ws/eBayISAPI.dll:[email]:[password]
vrr-db-ticketshop.de/authentication/login:[email]:[password]
www.planet-sports.de/checkout/register:[email]:[password]
www.bstn.com/eu_de/checkout/:[email]:[password]
www.lico-nature.de/index.php:[email]:[password]
ticketshop.mobil.nrw/authentication/register:[email]:[password]
softwareindustrie24.de/checkout/confirm/as/customer:[email]:[password]
www.zurbrueggen.de/checkout/register:[email]:[password]
www.hertz247.de/ikeage/de-de/SignUp/Profile:[email]:[password]
www.bluemovement.com/de-de/checkout2:[email]:[password]
members.persil-service.de/login/:[email]:[password]
www.nicotel.de/index.php:[email]:[password]
www.hellofresh.de/login:[email]:[password]
login.live.com/login.srf:[email]:[password]
accounts.login.idm.telekom.com/factorx:[email]:[password]
grillhaus-bei-reimann.order.dish.co/register:[email]:[password]
signup.sipgateteam.de/:[email]:[password]
www.baur.de/kasse/registrieren:[email]:[password]
buchung.carlundcarla.de/28572879/schritt-3:[email]:[password]
www.qvc.de/checkout/your-information.html:[email]:[password]
de.omio.com/app/search-frontend/booking/96720342-e20e-4de7-8b21-ddefc0fa44bd/passenger-details:[email]:[password]
www.shop-apotheke.com/nx/login/:[email]:[password]
druckmittel.de/checkout/confirm:[email]:[password]
www.global-carpet.de/checkout/confirm:[email]:[password]
software-hero.de/checkout/confirm:[email]:[password]
myenergykey.com/login:[email]:[password]
www.sixt.de/:[email]:[password]
www.wlan-shop24.de/Bestellvorgang:[email]:[password]
www.cyberport.de/checkout/anmelden.html:[email]:[password]
waschmal.de/registerCustomer:[email]:[password]
www.wgv.de/app/moped201802/rechner/abschluss/moped:[email]:[password]
www.persil-service.de/signup:[email]:[password]
nicotel.de/:[email]:[password]
temial.vorwerk.de/register/checkout:[email]:[password]
accounts.bahn.de/auth/realms/db/login-actions/required-action:[email]:[password].
www.petsdeli.de/login:[email]:[password]
login.live.com/login.srf:[email]:[password]
accounts.login.idm.telekom.com/factorx:[email]:[password]
www.netflix.com/de/login:[email]:[password]
www.zoll-portal.de/registrierung/benutzerkonto/daten:[email]:[password]
v3.account.samsung.com/iam/passwords/register:[email]:[password]
www.amazon.pl/ap/signin:[email]:[password]
www.amazon.de/:[email]:[password]
meinkonto.telekom-dienste.de/wiederherstellung/passwort/web-pw-setzen.xhtml:[email]:[password]
Even without seeing the email address and password, the commonality is clear: German websites. Whilst the email address is common, the passwords are not... at least not always. In 168 instances they were near identical with only a handful of them deviating by a character or two. There's some duplication across the lines (9 different rows of Netflix, 4 of Disney Plus, etc), but clearly this remains a significant volume of data. But is it real? Let's find out:
The data seems accurate so far. I have already changed some of the passwords as I was notified by the provider that my account was hacked. It is strange that the Telekom password was already generated and should not be guessable. I store my passwords in Firefox, so is it possible that they were stolen from there?
It's legit. Stealer malware explains both the Telekom password and why passwords in Firefox were obtained; there's not necessarily anything wrong with either service, but if a machine is infected with software that can grab passwords straight out of the fields they've been entered into in the browser, it's game over.
We started having some to-and-fro as I gathered more info, especially as it related to the timeframe:
It started about a month ago, maximum 6 weeks. I use a Macbook and an iPhone, only a Windows PC at work, maybe it happened there? About a week ago there was an extreme spam attack on my Gmail account, and several expensive items were ordered with my accounts in the same period, which fortunately could be canceled.
We had the usual discussion about password managers and of course before that, tracking down which device is infected and siphoning off secrets. This was obviously distressing for her to see all her accounts laid out like this, not to mention learning that they were being exchanged in channels frequented by criminals. But from the perspective of verifying both the legitimacy and uniqueness of the data (not to mention the freshness), this was an enormously valuable exchange.
Next up was another subscriber who'd previously dodged all the data breaches in HIBP yet somehow managed to end up with 53 rows of data in the corpus:
[email]:Gru[redacted password]
[email]:fux[redacted password]
[email]:zWi[redacted password]
[email]:6ii[redacted password]
[email]:qTM[redacted password]
[email]:Pre[redacted password]
[email]:i8$[redacted password]
[email]:9cr[redacted password]
[email]:fuc[redacted password]
[email]:kuM[redacted password]
[email]:Fuc[redacted password]
[email]:Pre[redacted password]
[email]:Vxt[redacted password]
[email]:%3r[redacted password]
[email]:But[redacted password]
[email]:1qH[redacted password]
[email]:^VS[redacted password]
[email]:But[redacted password]
[email]:Nbs[redacted password]
[email]:*W2[redacted password]
[email]:$aM[redacted password]
[email]:DA^[redacted password]
[email]:vPE[redacted password]
[email]:Z8u[redacted password]
[email]:But[redacted password]
[email]:aXi[redacted password]
[email]:rPe[redacted password]
[email]:b4F[redacted password]
[email]:2u&[redacted password]
[email]:5%f[redacted password]
[email]:Lmt[redacted password]
[email]:p
[email]:Tem[redacted password]
[email]:fuc[redacted password]
[email]:*e@[redacted password]
[email]:(k+[redacted password]
[email]:Ste[redacted password]
[email]:^@f[redacted password]
[email]:XT$[redacted password]
[email]:25@[redacted password]
[email]:Jav[redacted password]
[email]:U8![redacted password]
[email]:LsZ[redacted password]
[email]:But[redacted password]
[email]:g$V[redacted password]
[email]:M9@[redacted password]
[email]:!6D[redacted password]
[email]:Fac[redacted password]
[email]:but[redacted password]
[email]:Why[redacted password]
[email]:h45[redacted password]
[email]:blo[redacted password]
[email]:azT[redacted password]
I've redacted everything after the first three characters of the password so you can get a sense of the breadth of different ones here. In this instance, there was no accompanying website, but the data checked out:
Oh damn a lot of those do seem pretty accurate. Some are quite old and outdated too. I tend to use that gmail account for inconsequential shit so I'm not too fussed, but I'll defintely get stuck in and change all those passwords ASAP. This actually explains a lot because I've noticed some pretty suspicious activity with a couple of different accounts lately.
Another with 35 records of website, email and password triplets responded as follows (I'll stop pasting in the source data, you know what that looks like by now):
Thank you very much for the information, although I already knew about this (I think it was due to a breach in LastPass) and I already changed the passwords, your information is much more complete and clear. It helped me find some pages where I haven't changed the password.
The final one of note really struck a chord with me, not because of the thrirteen rows of records similar to the ones above, but because of what he told me in his reply:
Thank you for your kindness. Most of these I have been able to change the passwords of and they do look familiar. The passwords on there have been changed. Is there a way we both can fix this problem as seeing I am only 14?
That's my son's age and predictably, all the websites listed were gaming sites. The kid had obviously installed something nasty and had signed up to HIBP notifications only a week earlier. He explained he'd recently received an email attempting to extort him for $1.3k worth of Bitcoin and shared the message. It was clearly a mass-mailed, indiscriminate shakedown and I advised him that it in no way targeted him directly. Concerned, he countered with a second extortion email he'd received, this time it was your classic "we caught you watching porn and masturbating" scam, and this one really had him worried:
I have been stressed and scared about these scams (even though I shouldn’t be). I have been very stressed and scared today because of another one of those emails.
Imagine being a young teenage boy and receiving that?! That's the sort of thing criminals frequenting Telegram channels such as the ones in question are using this data for, and it's reprehensible. I gave him some tips (I see the sorts of things my son's friends randomly install!) and hopefully, that'll set him on the right course.
They were the most noteworthy responses, the others that were often just a single email address and password pair just simply reinforced the same message:
Yes, this is an old password that I have used in the past, and matches the password of my accounts that had been logged into recently.
And:
Yes that password is familiar and accurate. I used to practice password re-use with this password across many services 5+ years ago.This makes it impossible to correlate it to a particular service or breach. It is known to me to be out there already, I've received crypto extortion emails containing it.
I know that many people who find themselves in this incident will be confused; which breach is it? I've never used Telegram before, why am I there? Those questions came through during my verification process and I know from loading previous similar breaches, they'll come up over and over again in the coming days and I hope that the overview above sufficiently answers these.
The questions that are harder to answer (and again, I know these will come up based on prior experience), are what the password is that was exposed, what the website it appeared next to was and, indeed, if it appeared next to a website at all or just alongside an email address. Right at the beginning of this project more than a decade ago, I made the decision not to load the data that would answer these questions due to the risk it posed to individuals and by extension, the risk to my ability to continue running HIBP. We were reminded of how important this decision was earlier in the year when a service aggregating data breaches left the whole thing exposed and put everyone in there at even more risk.
So, if you're in here, what do you do? It's a repeat of the same old advice we've been giving in this industry for decades now, namely keeping devices patched and updated, running security software appropriate for your device (I use Microsoft Defender on my PCs), using strong and unique passwords (get a password manager!) and enabling 2FA wherever possible. Each HIBP subscriber I contacted wasn't doing at least one of these things, which was evident in their password selection. Time and time again, passwords consisted of highly predictable patterns and often included their name, year of birth (I assume) and common character substitutions, usually within a dozen characters of length too. It's the absolute basics that are going wrong here.
To the point one of the HIBP subscribers made above, loading this data will help many people explain why they've been seeing unusual behaviour on their accounts. It's also the wakeup call to lift everyone's security game per the previous paragraph. But this also isn't the end of it, and more combolists have been posted in more Telegram channels since loading this incident. Whilst I'm still of the view from years ago that I'm not going to continuously load endless lists, I do hope people recognise that their security posture is an ongoing concern and not just something you think about after appearing in a breach.
The data is now searchable in Have I Been Pwned.


Every day, there are tens of thousands of domain names registered across the globe – often as a key first step in creating a unique online presence. Making that experience possible for Verisign-operated top-level domains (TLDs) like .com and .net is a powerful and flexible technology platform first introduced 25 years ago.
Thanks to the Shared Registration System (SRS) – a hardware and software system conceptualized, designed, and launched by our teams 25 years ago – we’re able to successfully manage relationships with approximately 2,000 ICANN-accredited registrars who generally submit more than 100 million domain name transactions daily. Over the past quarter century, the SRS has thrived and grown with the global internet, in large part because we’ve continuously scaled and evolved the technology to meet exponentially increasing global demand, and a rapidly changing cyberthreat landscape.
In addition to enabling domain name registration, the usefulness of the technology extends beyond Verisign and its registry operations: many other companies subsequently adopted SRS concepts and implemented their own shared registration systems, making its impact far-reaching and long-lasting.
In this blog post, we commemorate the 25th anniversary of the launch of the Verisign SRS by reflecting on the insight and collaboration that went into developing a structure for domain name registration in those early days of the internet’s mainstream adoption.
Network Solutions, which Verisign acquired in 2000, had been functioning as both the sole registry and registrar for TLDs including .com, .net, and .org prior to 1999. The SRS was initially developed to make domain name registration more competitive and to encourage greater international participation, consistent with The Framework for Global Electronic Commerce, a directive to the U.S. Department of Commerce (DoC) to privatize the internet’s Domain Name System (DNS).
Work began in 1998 to develop and implement the SRS so that an unlimited number of registrars could provide domain name registration services, all under the administration of a common registry for each TLD. For several high-profile TLDs – including .com and .net – that registry was Network Solutions. That same year, the Internet Corporation for Assigned Names and Numbers (ICANN) – a multistakeholder not-for-profit organization dedicated to the management of key elements of the DNS – was formed.
Over a period of several months, Network Solutions designed and installed the system, which was officially deployed on April 3, 1999. Through a testing period that ran through the second half of 1999, the number of test registrars grew from an initial five – AOL, CORE, France Telecom/Oleane, Melbourne IT, and Register.com – to more than 20 by the end of that year.
That same year, Network Solutions implemented modifications to the SRS so that a registrar could accept registrations and renewals in one-year increments, as well as enable a registrar to add one year to a registrant’s registration period when transferring a domain from one registrar to another. Once the SRS was live, it was made accessible to all ICANN-accredited registrars, providing each one with equivalent access to register domain names in the TLDs.
When the SRS was first launched, a simple protocol called the Registry-Registrar Protocol (RRP) was deployed to handle the registration and management of domain names by many registrars in one TLD. However, we recognized that the use of this protocol could only be temporary given the growth of the internet and the need for a registration system with increased scalability. Work on a more sophisticated registration system began almost immediately – in 1999 – and that came in the form of the Extensible Provisioning Protocol, or EPP. EPP officially became an Internet Standard in 2009.
Today, EPP is used to register domain names and perform domain name-related functions, and there are over 2,000 ICANN-accredited registrars that all use EPP. EPP is central to the way that Verisign and many other authoritative registry operators do business: these registry operators work with domain name registrars to register domain names, and the registrars in turn offer a diverse range of domain name products to end users. Indeed, the simplicity of registering domains through EPP, and, for TLDs operated by Verisign, through the SRS, not only opened the door to easy access to domain name registration services, but also paved the way for new digital commerce and communications capabilities.
For the past 25 years, the SRS has been a critical component of the internet’s backend technology, even though it’s not widely known outside the DNS community. Thanks to the foresight and planning of many talented technologists, we built and evolved this system in such a way that it has successfully supported hundreds of millions of domain name registrations across the globe, serving as a first step for many on the path to establishing durable online identities. Along the way, we’ve added support for new technologies, including DNSSEC and Internationalized Domain Names (IDNs). We’ve made the system more secure by strengthening the domain name locking and transfer processes. We’ve also expanded the SRS to support additional TLDs administered by Verisign. In its own quiet way, the SRS has helped to support the dynamic growth of the internet, while prioritizing equivalent access to domain name registration.
Many of the people who worked on the launch of the SRS are still with Verisign today, myself included. We are fortunate to have the chance to continue working together – 25 years later – always with an eye toward the future and how we can continue to help the internet grow and prosper.
The post The Verisign Shared Registration System: A 25-Year Retrospective appeared first on Verisign Blog.

Following a whirlwind year of travel in 2023, 40% of Americans are gearing up for even more adventures in 2024. As the warmth of summer approaches and travel plans start to take shape, it’s crucial to prepare for often overlooked risks that may come up while traveling. The mix of unfamiliar surroundings, increased distraction, and reliance on public Wi-Fi creates an ideal environment for malicious actors to exploit. From impersonation tricks to oversharing on social media, attackers have plenty of ways to target unsuspecting travelers.
What are the most common scams you should watch out for, and how can you stay safe from them?
One of the most common social engineering threats while traveling is impersonation scams. Attackers may pose as hotel staff, tour guides, or even fellow travelers to gain access to personal information or valuable belongings. Always verify the identity of individuals before sharing any sensitive information or handing over personal belongings. If someone claims to be an employee of a hotel or a service provider, don’t hesitate to ask for official identification or contact the establishment directly to confirm their identity.
Public Wi-Fi networks are a convenient way to stay connected while traveling, but they also pose significant security risks. Hackers can easily intercept data transmitted over these networks, including login credentials, credit card information, and personal messages. Avoid accessing sensitive accounts or conducting financial transactions while connected to public Wi-Fi. Instead, use a virtual private network (VPN) to encrypt your internet connection and protect your data from prying eyes.
Sharing vacation photos and updates on social media may seem harmless, but it can inadvertently put you at risk. Posting your location in real time or sharing details about your travel itinerary can make you a target for thieves and cybercriminals. Avoid oversharing on social media, especially when it comes to your whereabouts, and consider waiting to post travel updates until you are home.
Take a deep dive into your privacy settings to ensure that bad actors can’t access your personal information through your social media accounts. Our Social Privacy Manager can do that work for you, automatically adjusting more than 100 privacy settings across all the accounts you choose.
Phishing emails and texts are a common tactic used by cybercriminals to trick travelers into revealing sensitive information or downloading malware onto their devices. Be wary of unsolicited messages claiming to be from airlines, hotels, or financial institutions, especially if they ask for personal information or prompt you to click on suspicious links. Verify the legitimacy of any unexpected communications by contacting the sender directly using official contact information obtained from their official website or a trusted source.
In addition to being aware of the risks, there are proactive steps you can take to protect your personal information before traveling:
By staying informed and vigilant, you can minimize the risk of falling victim to scams while traveling and enjoy a worry-free vacation experience. Remember to trust your instincts and err on the side of caution when encountering unfamiliar situations or individuals.
Having a complete set of online protection software is like having a team of cyber guardians watching over you on vacation. With the right precautions in place, you can focus on making memories and exploring new destinations without compromising your personal information or security. Safe travels!
The post How to Stay Safe Against Scams While Traveling appeared first on McAfee Blog.
This is a simple SBOM utility which aims to provide an insider view on which packages are getting executed.
The process and objective is simple we can get a clear perspective view on the packages installed by APT (currently working on implementing this for RPM and other package managers). This is mainly needed to check which all packages are actually being executed.
The packages needed are mentioned in the requirements.txt file and can be installed using pip:
pip3 install -r requirements.txt
Mount the image: Currently I am still working on a mechanism to automatically define a mount point and mount different types of images and volumes but its still quite a task for me.| Argument | Description |
|---|---|
--analysis-mode | Specifies the mode of operation. Default is static. Choices are static and chroot. |
--static-type | Specifies the type of analysis for static mode. Required for static mode only. Choices are info and service. |
--volume-path | Specifies the path to the mounted volume. Default is /mnt. |
--save-file | Specifies the output file for JSON output. |
--info-graphic | Specifies whether to generate visual plots for CHROOT analysis. Default is True. |
--pkg-mgr | Manually specify the package manager or dont add this option for automatic check. |
| APT: | |
| - Static Info Analysis: | |
| - This command runs the program in static analysis mode, specifically using the Info Directory analysis method. | |
- It analyzes the packages installed on the mounted volume located at /mnt. | |
- It saves the output in a JSON file named output.json. | |
| - It generates visual plots for CHROOT analysis. |
```bash
python3 main.py --pkg-mgr apt --analysis-mode static --static-type info --volume-path /mnt --save-file output.json
```
Static Service Analysis:
This command runs the program in static analysis mode, specifically using the Service file analysis method.
/custom_mount.output.json.It does not generate visual plots for CHROOT analysis. bash python3 main.py --pkg-mgr apt --analysis-mode static --static-type service --volume-path /custom_mount --save-file output.json --info-graphic False
Chroot analysis with or without Graphic output:
/mnt.output.json.--info-graphic as True else False bash python3 main.py --pkg-mgr apt --analysis-mode chroot --volume-path /mnt --save-file output.json --info-graphic True/False
RPM - Static Analysis: - Similar to how its done on apt but there is only one type of static scan avaialable for now. bash python3 main.py --pkg-mgr rpm --analysis-mode static --volume-path /mnt --save-file output.json
bash python3 main.py --pkg-mgr rpm --analysis-mode chroot --volume-path /mnt --save-file output.json --info-graphic True/False
Currently the tool works on Debian and Red Hat based images I can guarentee the debian outputs but the Red-Hat onces still needs work to be done its not perfect.
I am working on the pacman side of things I am trying to find a relaiable way of accessing the pacman db for static analysis.
For the workings and process related documentation please read the wiki page: Link
Ideas regarding this topic are welcome in the discussions page.
A Slack Attack Framework for conducting Red Team and phishing exercises within Slack workspaces.
This tool is intended for Security Professionals only. Do not use this tool against any Slack workspace without explicit permission to test. Use at your own risk.
Thousands of organizations utilize Slack to help their employees communicate, collaborate, and interact. Many of these Slack workspaces install apps or bots that can be used to automate different tasks within Slack. These bots are individually provided permissions that dictate what tasks the bot is permitted to request via the Slack API. To authenticate to the Slack API, each bot is assigned an api token that begins with xoxb or xoxp. More often than not, these tokens are leaked somewhere. When these tokens are exfiltrated during a Red Team exercise, it can be a pain to properly utilize them. Now EvilSlackbot is here to automate and streamline that process. You can use EvilSlackbot to send spoofed Slack messages, phishing links, files, and search for secrets leaked in slack.
In addition to red teaming, EvilSlackbot has also been developed with Slack phishing simulations in mind. To use EvilSlackbot to conduct a Slack phishing exercise, simply create a bot within Slack, give your bot the permissions required for your intended test, and provide EvilSlackbot with a list of emails of employees you would like to test with simulated phishes (Links, files, spoofed messages)
EvilSlackbot requires python3 and Slackclient
pip3 install slackclient
usage: EvilSlackbot.py [-h] -t TOKEN [-sP] [-m] [-s] [-a] [-f FILE] [-e EMAIL]
[-cH CHANNEL] [-eL EMAIL_LIST] [-c] [-o OUTFILE] [-cL]
options:
-h, --help show this help message and exit
Required:
-t TOKEN, --token TOKEN
Slack Oauth token
Attacks:
-sP, --spoof Spoof a Slack message, customizing your name, icon, etc
(Requires -e,-eL, or -cH)
-m, --message Send a message as the bot associated with your token
(Requires -e,-eL, or -cH)
-s, --search Search slack for secrets with a keyword
-a, --attach Send a message containing a malicious attachment (Requires -f
and -e,-eL, or -cH)
Arguments:
-f FILE, --file FILE Path to file attachment
-e EMAIL, --email EMAIL
Email of target
-cH CHANNEL, --channel CHANNEL
Target Slack Channel (Do not include #)
-eL EMAIL_LIST, --email_list EMAIL_LIST
Path to list of emails separated by newline
-c, --check Lookup and display the permissions and available attacks
associated with your provided token.
-o OUTFILE, --outfile OUTFILE
Outfile to store search results
-cL, --channel_list List all public Slack channels
To use this tool, you must provide a xoxb or xoxp token.
Required:
-t TOKEN, --token TOKEN (Slack xoxb/xoxp token)
python3 EvilSlackbot.py -t <token>
Depending on the permissions associated with your token, there are several attacks that EvilSlackbot can conduct. EvilSlackbot will automatically check what permissions your token has and will display them and any attack that you are able to perform with your given token.
Attacks:
-sP, --spoof Spoof a Slack message, customizing your name, icon, etc (Requires -e,-eL, or -cH)
-m, --message Send a message as the bot associated with your token (Requires -e,-eL, or -cH)
-s, --search Search slack for secrets with a keyword
-a, --attach Send a message containing a malicious attachment (Requires -f and -e,-eL, or -cH)
With the correct token permissions, EvilSlackbot allows you to send phishing messages while impersonating the botname and bot photo. This attack also requires either the email address (-e) of the target, a list of target emails (-eL), or the name of a Slack channel (-cH). EvilSlackbot will use these arguments to lookup the SlackID of the user associated with the provided emails or channel name. To automate your attack, use a list of emails.
python3 EvilSlackbot.py -t <xoxb token> -sP -e <email address>
python3 EvilSlackbot.py -t <xoxb token> -sP -eL <email list>
python3 EvilSlackbot.py -t <xoxb token> -sP -cH <Channel name>
With the correct token permissions, EvilSlackbot allows you to send phishing messages containing phishing links. What makes this attack different from the Spoofed attack is that this method will send the message as the bot associated with your provided token. You will not be able to choose the name or image of the bot sending your phish. This attack also requires either the email address (-e) of the target, a list of target emails (-eL), or the name of a Slack channel (-cH). EvilSlackbot will use these arguments to lookup the SlackID of the user associated with the provided emails or channel name. To automate your attack, use a list of emails.
python3 EvilSlackbot.py -t <xoxb token> -m -e <email address>
python3 EvilSlackbot.py -t <xoxb token> -m -eL <email list>
python3 EvilSlackbot.py -t <xoxb token> -m -cH <Channel name>
With the correct token permissions, EvilSlackbot allows you to search Slack for secrets via a keyword search. Right now, this attack requires a xoxp token, as xoxb tokens can not be given the proper permissions to keyword search within Slack. Use the -o argument to write the search results to an outfile.
python3 EvilSlackbot.py -t <xoxp token> -s -o <outfile.txt>
With the correct token permissions, EvilSlackbot allows you to send file attachments. The attachment attack requires a path to the file (-f) you wish to send. This attack also requires either the email address (-e) of the target, a list of target emails (-eL), or the name of a Slack channel (-cH). EvilSlackbot will use these arguments to lookup the SlackID of the user associated with the provided emails or channel name. To automate your attack, use a list of emails.
python3 EvilSlackbot.py -t <xoxb token> -a -f <path to file> -e <email address>
python3 EvilSlackbot.py -t <xoxb token> -a -f <path to file> -eL <email list>
python3 EvilSlackbot.py -t <xoxb token> -a -f <path to file> -cH <Channel name>
Arguments:
-f FILE, --file FILE Path to file attachment
-e EMAIL, --email EMAIL Email of target
-cH CHANNEL, --channel CHANNEL Target Slack Channel (Do not include #)
-eL EMAIL_LIST, --email_list EMAIL_LIST Path to list of emails separated by newline
-c, --check Lookup and display the permissions and available attacks associated with your provided token.
-o OUTFILE, --outfile OUTFILE Outfile to store search results
-cL, --channel_list List all public Slack channels
With the correct permissions, EvilSlackbot can search for and list all of the public channels within the Slack workspace. This can help with planning where to send channel messages. Use -o to write the list to an outfile.
python3 EvilSlackbot.py -t <xoxb token> -cL
Reaper is a proof-of-concept designed to exploit BYOVD (Bring Your Own Vulnerable Driver) driver vulnerability. This malicious technique involves inserting a legitimate, vulnerable driver into a target system, which allows attackers to exploit the driver to perform malicious actions.
Reaper was specifically designed to exploit the vulnerability present in the kprocesshacker.sys driver in version 2.8.0.0, taking advantage of its weaknesses to gain privileged access and control over the target system.
Note: Reaper does not kill the Windows Defender process, as it has a protection, Reaper is a simple proof of concept.
____
/ __ \___ ____ _____ ___ _____
/ /_/ / _ \/ __ `/ __ \/ _ \/ ___/
/ _, _/ __/ /_/ / /_/ / __/ /
/_/ |_|\___/\__,_/ .___/\___/_/
/_/
[Coded by MrEmpy]
[v1.0]
Usage: C:\Windows\Temp\Reaper.exe [OPTIONS] [VALUES]
Options:
sp, suspend process
kp, kill process
Values:
PROCESSID process id to suspend/kill
Examples:
Reaper.exe sp 1337
Reaper.exe kp 1337
You can compile it directly from the source code or download it already compiled. You will need Visual Studio 2022 to compile.
Note: The executable and driver must be in the same directory.

Authored by Dexter Shin
Many government agencies provide their services online for the convenience of their citizens. Also, if this service could be provided through a mobile app, it would be very convenient and accessible. But what happens when malware pretends to be these services?
McAfee Mobile Research Team found an InfoStealer Android malware pretending to be a government agency service in Bahrain. This malware pretends to be the official app of Bahrain and advertises that users can renew or apply for driver’s licenses, visas, and ID cards on mobile. Users who are deceived by advertisements that they are available on mobile will be provided with the necessary personal information for these services without a doubt. They reach users in various ways, including Facebook and SMS messages. Users who are not familiar with these attacks easily make the mistake of sending personal information.
In Bahrain, there’s a government agency called the Labour Market Regulatory Authority (LMRA). This agency operates with full financial and administrative independence under the guidance of a board of directors chaired by the Minister of Labour. They provide a variety of mobile services, and most apps provide only one service per app. However, this fake app promotes providing more than one service.

Figure 1. Legitimate official LMRA website
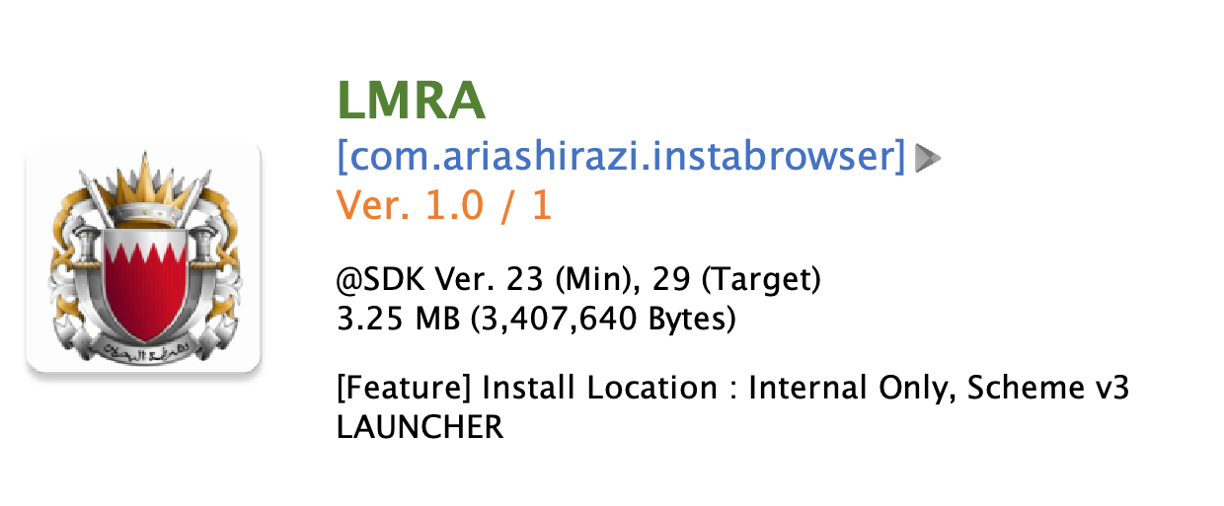
Figure 2. Fake app named LMRA
Excluding the most frequently found fake apps pretending LMRA, there are various fake apps included Bank of Bahrain and Kuwait (BBK), BenefitPay, a fintech company in Bahrain, and even apps pretending to be related to Bitcoin or loans. These apps use the same techniques as the LMRA fake apps to steal personal information.

Figure 3. Various fake apps using the same techniques
From the type of app that this malware pretends, we can guess that the purpose is financial fraud to use the personal information it has stolen. Moreover, someone has been affected by this campaign as shown in the picture below.
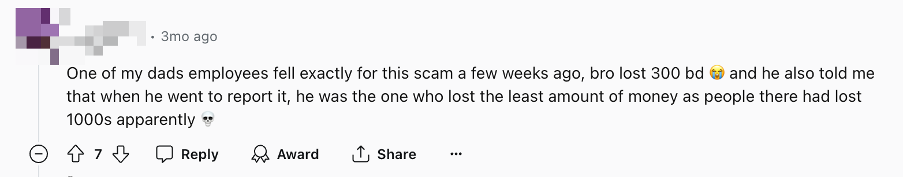
Figure 4. Victims of financial fraud (Source: Reddit)
They distribute these apps using Facebook pages and SMS messages. Facebook pages are fake and malware author is constantly creating new pages. These pages direct users to phishing sites, either WordPress blog sites or custom sites designed to download apps.
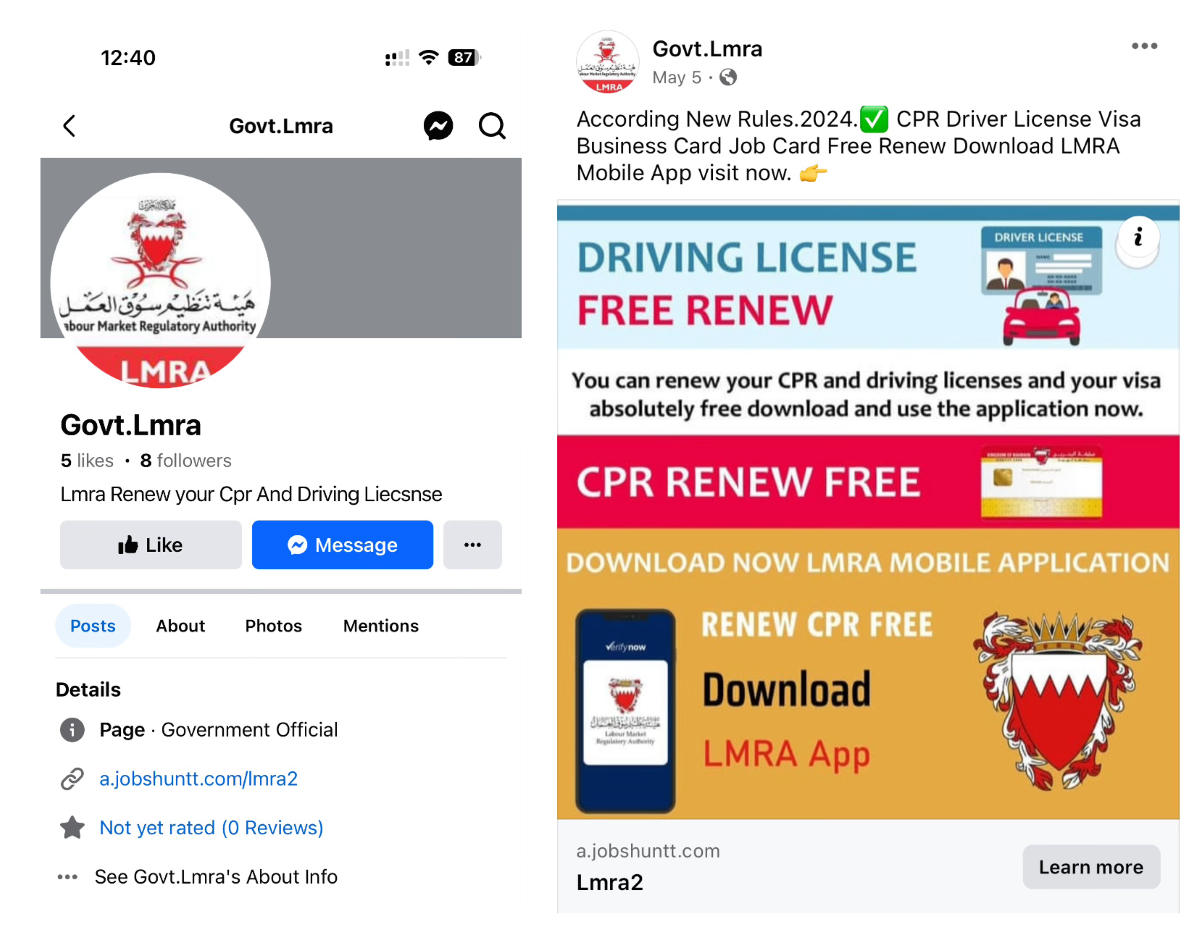
Figure 5. Facebook profile and page with a link to the phishing site

Figure 6. One of the phishing sites designed to download app
In the case of SMS, social engineering messages are sent to trick users into clicking a link so that they feel the need to urgently confirm.
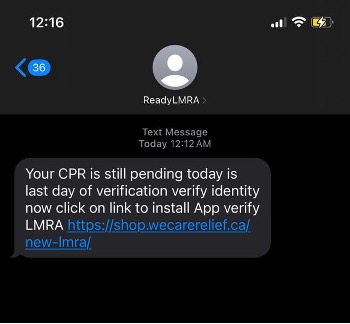
Figure 7. Phishing message using SMS (Source: Reddit)
When the user launches the app, the app shows a large legitimate icon for users to be mistaken. And it asks for the CPR and phone number. The CPR number is an exclusive 9-digit identifier given to each resident in Bahrain. There is a “Verify” button, but it is simply a button to send information to the C2 server. If users input their information, it goes directly to the next screen without verification. This step just stores the information for the next step.
Figure 8. The first screen (left) and next screen of a fake app (right)
There are various menus, but they are all linked to the same URL. The parameter value is the CPR and phone numbers input by the user on the first screen.
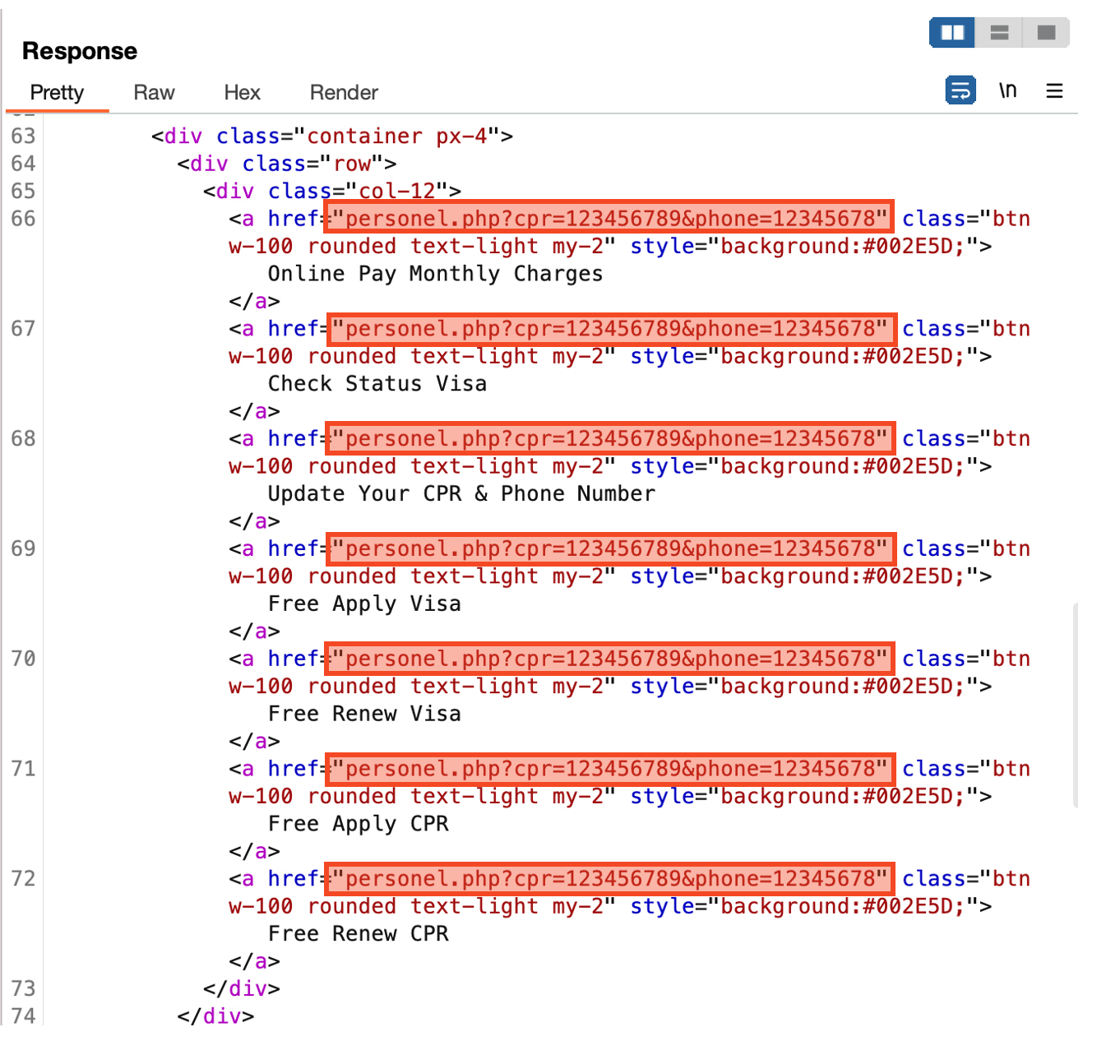
Figure 9. All menus are linked to the same URL
The last page asks for the user’s full name, email, and date of birth. After inputting everything and clicking the “Send” button, all information inputted so far will be sent to the malware author’s c2 server.
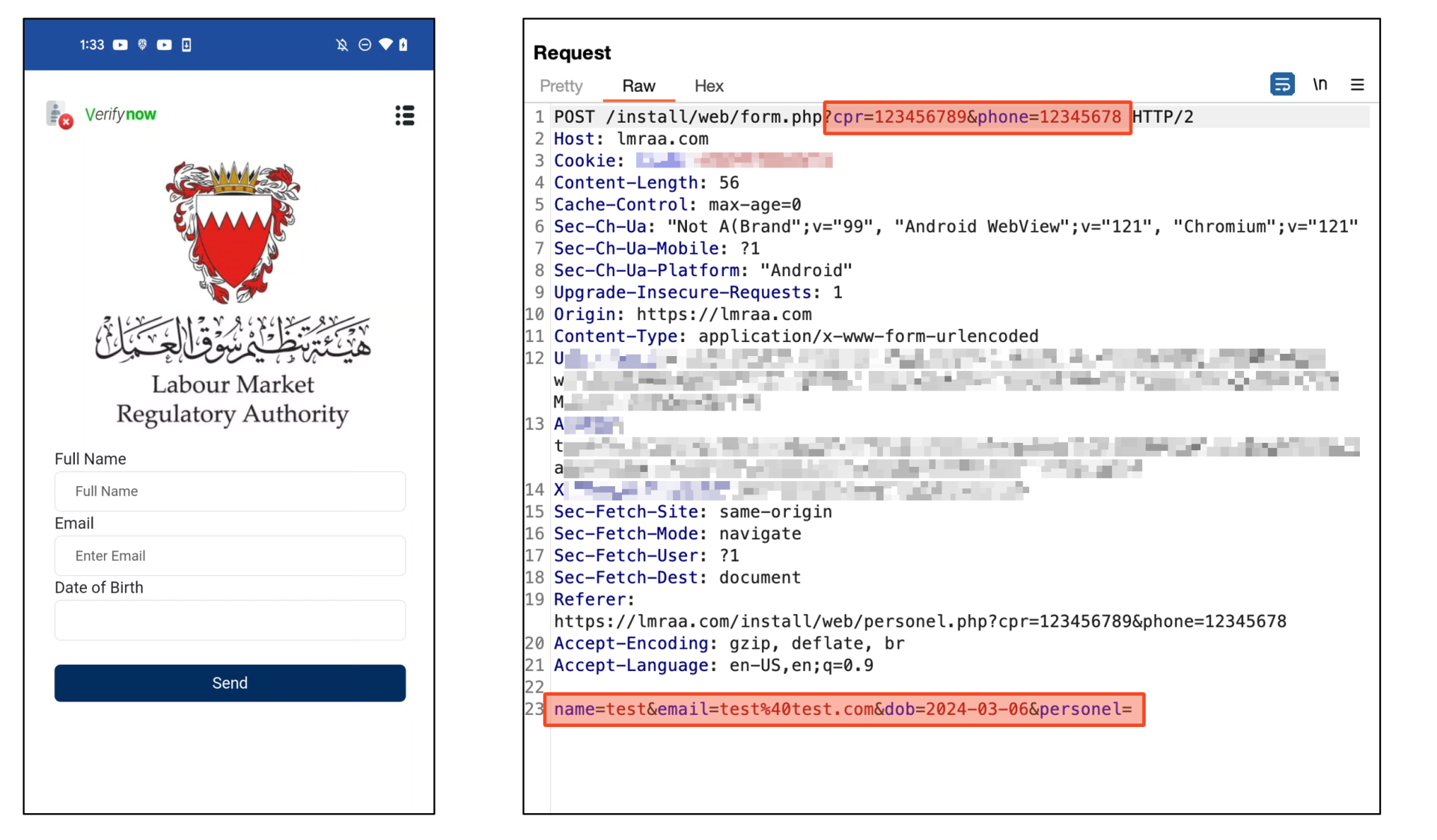
Figure 10. All data sent to C2 server
After sending, it shows a completion page to trick the user. It shows a message saying you will receive an email within 24 hours. But it is just a counter that decreases automatically. So, it does nothing after 24 hours. In other words, while users are waiting for the confirmation email for 24 hours, cybercriminals will exploit the stolen information to steal victims’ financial assets.
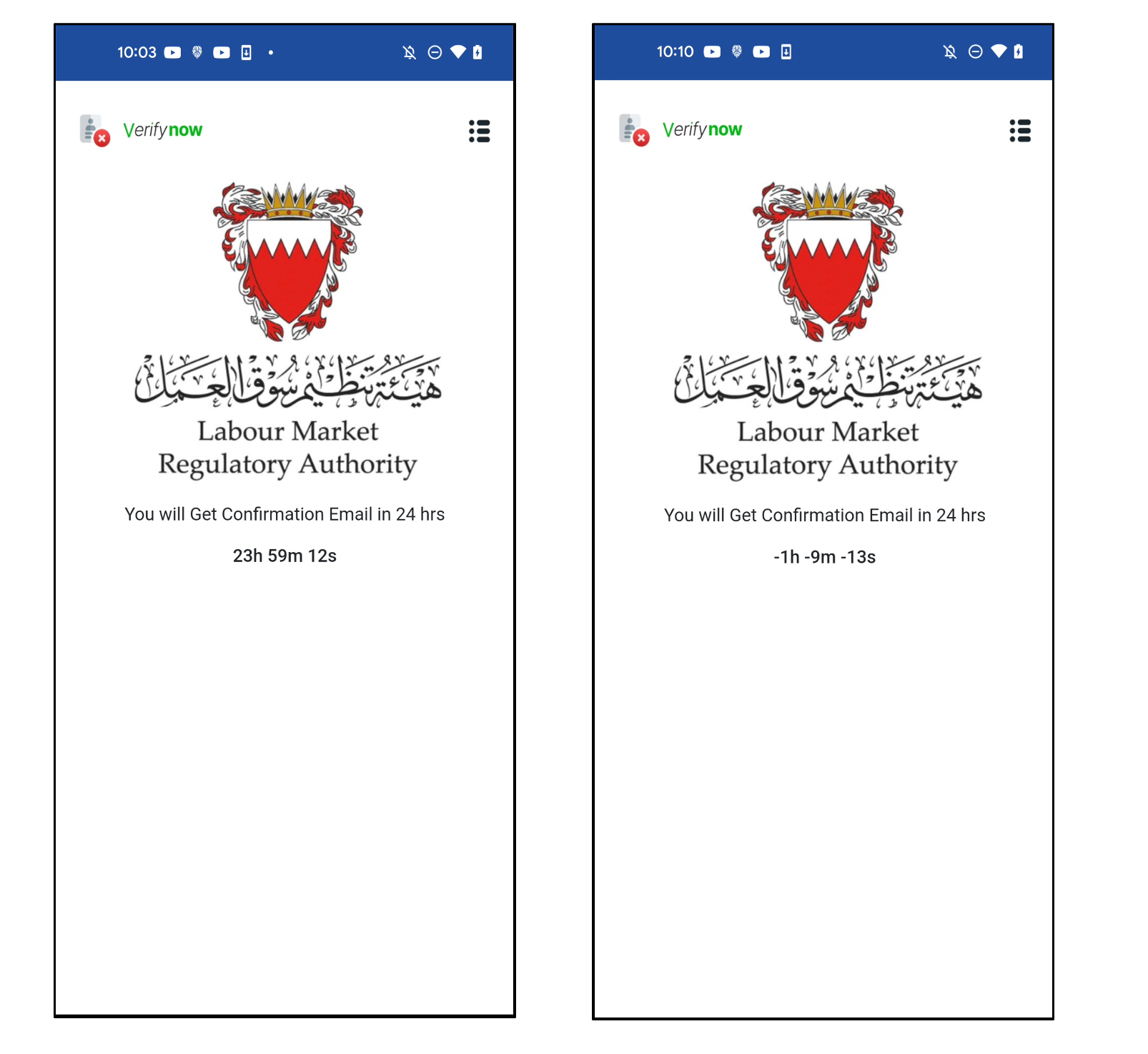
Figure 11. Completion page to trick users
In addition, they have a payload for stealing SMS. This app has a receiver that works when SMS is received. So as soon as SMS comes, it sends an SMS message to the C2 server without notifying the user.
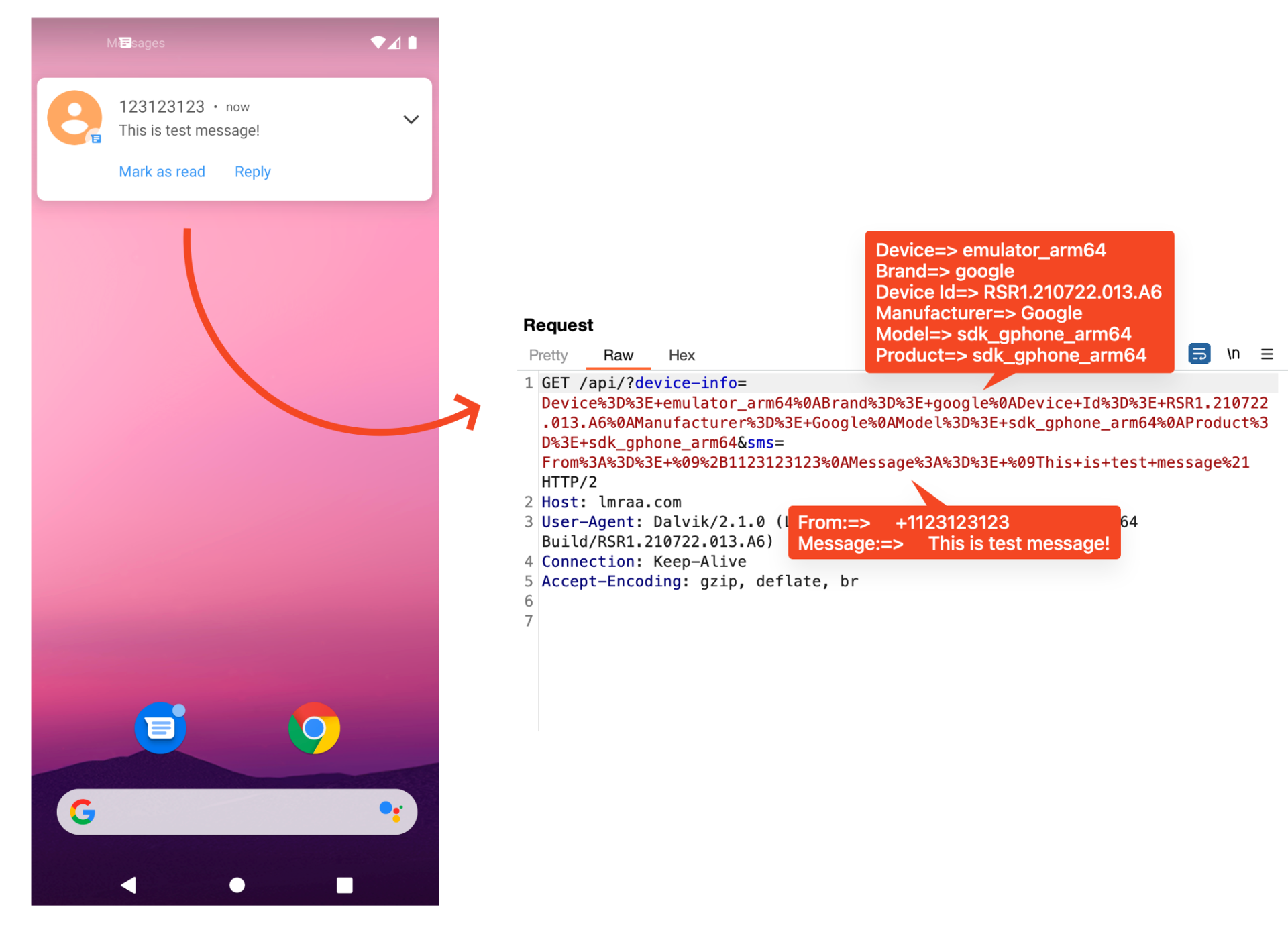
Figure 12. Payload for stealing SMS
We confirmed that there are two types of these apps. There is a type that implements a custom C2 server and receives data directly through web API, and another type is an app that uses Firebase. Firebase is a backend service platform provided by Google. Among many services, Firestore can store data as a database. This malware uses Firestore. Because it is a legitimate service provided by Google, it is difficult to detect as a malicious URL.
For apps that use Firebase, dynamically load phishing URLs stored in Firestore. Therefore, even if a phishing site is blocked, it is possible to respond quickly to maintain already installed victims by changing the URL stored in Firestore.
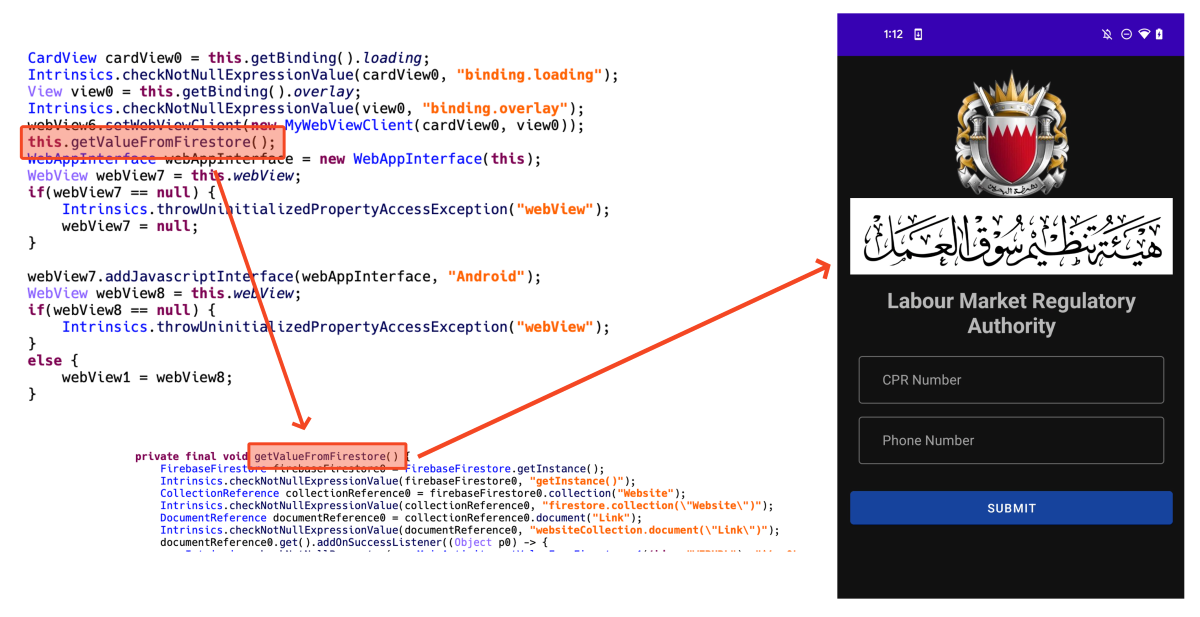
Figure 13. Dynamically loading phishing site loaded in webview
According to our detection telemetry data, there are 62 users have already used this app in Bahrain. However, since this data is a number at the time of writing, this number is expected to continue to increase, considering that new Facebook pages are still being actively created.
Recent malware tends to target specific countries or users rather than widespread attacks. These attacks may be difficult for general users to distinguish because malware accurately uses the parts needed by users living in a specific country. So we recommend users install secure software to protect their devices. Also, users are encouraged to download and use apps from official app stores like Google Play Store or Apple AppStore. If you can’t find an app in these stores, you must download the app provided on the official website.
McAfee Mobile Security already detects this threat as Android/InfoStealer. For more information, visit McAfee Mobile Security.
Samples:
| SHA256 | Package Name | App Name |
| 6f6d86e60814ad7c86949b7b5c212b83ab0c4da65f0a105693c48d9b5798136c | com.ariashirazi.instabrowser | LMRA |
| 5574c98c9df202ec7799c3feb87c374310fa49a99838e68eb43f5c08ca08392d | com.npra.bahrain.five | LMRA Bahrain |
| b7424354c356561811e6af9d8f4f4e5b0bf6dfe8ad9d57f4c4e13b6c4eaccafb | com.npra.bahrain.five | LMRA Bahrain |
| f9bdeca0e2057b0e334c849ff918bdbe49abd1056a285fed1239c9948040496a | com.lmra.nine.lmranine | LMRA |
| bf22b5dfc369758b655dda8ae5d642c205bb192bbcc3a03ce654e6977e6df730 | com.stich.inches | Visa Update |
| 8c8ffc01e6466a3e02a4842053aa872119adf8d48fd9acd686213e158a8377ba | com.ariashirazi.instabrowser | EasyLoan |
| 164fafa8a48575973eee3a33ee9434ea07bd48e18aa360a979cc7fb16a0da819 | com.ariashirazi.instabrowser | BTC Flasher |
| 94959b8c811fdcfae7c40778811a2fcc4c84fbdb8cde483abd1af9431fc84b44 | com.ariashirazi.instabrowser | BenefitPay |
| d4d0b7660e90be081979bfbc27bbf70d182ff1accd829300255cae0cb10fe546 | com.lymors.lulumoney | BBK Loan App |
Domains:
Firebase(for C2):
The post Fake Bahrain Government Android App Steals Personal Data Used for Financial Fraud appeared first on McAfee Blog.

Howdy! My name is Harrison Richardson, or rs0n (arson) when I want to feel cooler than I really am. The code in this repository started as a small collection of scripts to help automate many of the common Bug Bounty hunting processes I found myself repeating. Over time, I built a simple web application with a MongoDB connection to manage my findings and identify valuable data points. After 5 years of Bug Bounty hunting, both part-time and full-time, I'm finally ready to package this collection of tools into a proper framework.
The Ars0n Framework is designed to provide aspiring Application Security Engineers with all the tools they need to leverage Bug Bounty hunting as a means to learn valuable, real-world AppSec concepts and make 💰 doing it! My goal is to lower the barrier of entry for Bug Bounty hunting by providing easy-to-use automation tools in combination with educational content and how-to guides for a wide range of Web-based and Cloud-based vulnerabilities. In combination with my YouTube content, this framework will help aspiring Application Security Engineers to quickly and easily understand real-world security concepts that directly translate to a high paying career in Cyber Security.
In addition to using this tool for Bug Bounty Hunting, aspiring engineers can also use this Github Repository as a canvas to practice collaborating with other developers! This tool was inspired by Metasploit and designed to be modular in a similar way. Each Script (Ex: wildfire.py or slowburn.py) is basically an algorithm that runs the Modules (Ex: fire-starter.py or fire-scanner.py) in a specific patter for a desired result. Because of this design, the community is free to build new Scripts to solve a specific use-case or Modules to expand the results of these Scripts. By learning the code in this framework and using Github to contribute your own code, aspiring engineers will continue to learn real-world skills that can be applied on the first day of a Security Engineer I position.
My hope is that this modular framework will act as a canvas to help share what I've learned over my career to the next generation of Security Engineers! Trust me, we need all the help we can get!!
Paste this code block into a clean installation of Kali Linux 2023.4 to download, install, and run the latest stable Alpha version of the framework:
sudo apt update && sudo apt-get update
sudo apt -y upgrade && sudo apt-get -y upgrade
wget https://github.com/R-s0n/ars0n-framework/releases/download/v0.0.2-alpha/ars0n-framework-v0.0.2-alpha.tar.gz
tar -xzvf ars0n-framework-v0.0.2-alpha.tar.gz
rm ars0n-framework-v0.0.2-alpha.tar.gz
cd ars0n-framework
./install.sh
wget https://github.com/R-s0n/ars0n-framework/releases/download/v0.0.2-alpha/ars0n-framework-v0.0.2-alpha.tar.gz
tar -xzvf ars0n-framework-v0.0.2-alpha.tar.gz
rm ars0n-framework-v0.0.2-alpha.tar.gz
The Ars0n Framework includes a script that installs all the necessary tools, packages, etc. that are needed to run the framework on a clean installation of Kali Linux 2023.4.
Please note that the only supported installation of this framework is on a clean installation of Kali Linux 2023.3. If you choose to try and run the framework outside of a clean Kali install, I will not be able to help troubleshoot if you have any issues.
./install.sh
This video shows exactly what to expect from a successful installation.
If you are using an ARM Processor, you will need to add the --arm flag to all Install/Run scripts
./install.sh --arm
You will be prompted to enter various API keys and tokens when the installation begins. Entering these is not required to run the core functionality of the framework. If you do not enter these API keys and tokens at the time of installation, simply hit enter at each of the prompts. The keys can be added later to the ~/.keys directory. More information about how to add these keys manually can be found in the Frequently Asked Questions section of this README.
Once the installation is complete, you will be given the option to run the application by entering Y. If you choose not the run the application immediately, or if you need to run the application after a reboot, simply navigate to the root directly and run the run.sh bash script.
./run.sh
If you are using an ARM Processor, you will need to add the --arm flag to all Install/Run scripts
./run.sh --arm
The Ars0n Framework's Core Modules are used to determine the basic scanning logic. Each script is designed to support a specific recon methodology based on what the user is trying to accomplish.
At this time, the Wildfire script is the most widely used Core Module in the Ars0n Framework. The purpose of this module is to allow the user to scan multiple targets that allow for testing on any subdomain discovered by the researcher.
How it works:
Most Wildfire scans take between 8 and 48 hours to complete against a single domain if all Sub-Modules are being run. Variations in this timing can be caused by a number of factors, including the target application and the machine running the framework.
Also, please note that most data will not show in the GUI until the scan has completed. It's best to try and run the scan overnight or over a weekend, depending on the number of domains being scanned, and return once the scan has complete to move from Recon to Enumeration.
Running Wildfire:
Wildfire can be run from the GUI using the Wildfire button on the dashboard. Once clicked, the front-end will use the checkboxes on the screen to determine what flags should be passed to the scanner.
Please note that running scans from the GUI still has a few bugs and edge cases that haven't been sorted out. If you have any issues, you can simply run the scan form the CLI.
All Core Modules for The Ars0n Framework are stored in the /toolkit directory. Simply navigate to the directory and run wildfire.py with the necessary flags. At least one Sub-Module flag must be provided.
python3 wildfire.py --start --cloud --scan
Unlike the Wildfire module, which requires the user to identify target domains to scan, the Slowburn module does that work for you. By communicating with APIs for various bug bounty hunting platforms, this script will identify all domains that allow for testing on any discovered subdomain. Once the data has been populated, Slowburn will randomly choose one domain at a time to scan in the same way Wildfire does.
Please note that the Slowburn module is still in development and is not considered part of the stable alpha release. There will likely be bugs and edge cases encountered by the user.
In order for Slowburn to identify targets to scan, it must first be initialized. This initialization step collects the necessary data from various API's and deposits them into a JSON file stored locally. Once this initialization step is complete, Slowburn will automatically begin selecting and scanning one target at a time.
To initalize Slowburn, simply run the following command:
python3 slowburn.py --initialize
Once the data has been collected, it is up to the user whether they want to re-initialize the tool upon the next scan.
Remember that the scope and targets on public bug bounty programs can change frequently. If you choose to run Slowburn without initializing the data, you may be scanning domains that are no longer in scope for the program. It is strongly recommended that Slowburn be re-initialized each time before running.
If you choose not to re-initialize the target data, you can run Slowburn using the previously collected data with the following command:
python3 slowburn.py
The Ars0n Framework's Sub-Modules are designed to be leveraged by the Core Modules to divide the Recon & Enumeration phases into specific tasks. The data collected in each Sub-Module is used by the others to expand your picture of the target's attack surface.
Fire-Starter is the first step to performing recon against a target domain. The goal of this script is to collect a wealth of information about the attack surface of your target. Once collected, this data will be used by all other Sub-Modules to help the user identify a specific URL that is potentially vulnerable.
Fire-Starter works by running a series of open-source tools to enumerate hidden subdomains, DNS records, and the ASN's to identify where those external entries are hosted. Currently, Fire-Starter works by chaining together the following widely used open-source tools:
These tools cover a wide range of techniques to identify hidden subdomains, including web scraping, brute force, and crawling to identify links and JavaScript URLs.
Once the scan is complete, the Dashboard will be updated and available to the user.
Most Sub-Modules in The Ars0n Framework requre the data collected from the Fire-Starter module to work. With this in mind, Fire-Starter must be included in the first scan against a target for any usable data to be collected.
Coming soon...
Fire-Scanner uses the results of Fire-Starter and Fire-Cloud to perform Wide-Band Scanning against all subdomains and cloud services that have been discovered from previous scans.
At this stage of development, this script leverages Nuclei almost exclusively for all scanning. Instead of simply running the tool, Fire-Scanner breaks the scan down into specific collections of Nuclei Templates and scans them one by one. This strategy helps ensure the scans are stable and produce consistent results, removes any unnecessary or unsafe scan checks, and produces actionable results.
The vast majority of issues installing and/or running the Ars0n Framework are caused by not installing the tool on a clean installation of Kali Linux.
It is important to remember that, at its core, the Ars0n Framework is a collection of automation scripts designed to run existing open-source tools. Each of these tools have their own ways of operating and can experience unexpected behavior if conflicts emerge with any existing service/tool running on the user's system. This complexity is the reason why running The Ars0n Framework should only be run on a clean installation of Kali Linux.
Another very common issue users experience is caused by MongoDB not successfully installing and/or running on their machine. The most common manifestation of this issue is the user is unable to add an initial FQDN and simply sees a broken GUI. If this occurs, please ensure that your machine has the necessary system requirements to run MongoDB. Unfortunately, there is no current solution if you run into this issue.
Coming soon...

As election season approaches, the importance of safeguarding our democratic processes has never been more critical. Ensuring election security is not just the responsibility of government bodies but also of every individual voter. This blog post aims to provide valuable insights and practical tips for consumers to protect their votes and understand the mechanisms in place to secure elections.
Election security encompasses a broad range of practices designed to ensure the integrity, confidentiality, and accessibility of the voting process. This includes safeguarding against cyber threats, ensuring the accuracy of voter registration databases, protecting the physical security of voting equipment, and maintaining transparency in the vote counting process. As voters, being aware of these elements helps us appreciate the complexity and importance of secure elections.
One of the first steps to secure your vote is to ensure that you are registered correctly. Check your voter registration status well in advance of the election day through your local election office or official state website. This helps to avoid any last-minute issues and ensures your eligibility to vote.
Misinformation can spread rapidly, especially during election periods. Rely on official sources for information about polling locations, voting procedures, and deadlines. Avoid sharing unverified information on social media and report any suspicious content to the relevant authorities.
Whether you are voting in person or by mail, make sure to follow the recommended procedures. If voting by mail, request your ballot from a verified source and return it through secure methods such as official drop boxes or by mail with sufficient time to ensure it is received before the deadline.
Scammers often target voters to steal personal information. Be cautious of unsolicited phone calls, emails, or texts asking for your personal details. Official election offices will not request sensitive information such as your Social Security number via these methods.
If you notice anything unusual at your polling place or have concerns about the voting process, report it immediately to election officials. This includes any signs of tampering with voting machines, suspicious behavior, or attempts to intimidate voters.
Familiarize yourself with the voting process in your area. This includes knowing your polling location, understanding what identification is required, and learning about the different ways you can cast your vote. Many states provide detailed guides and resources for first-time voters.
Plan your voting day in advance. Decide whether you will vote in person or by mail, and make sure you have all necessary documentation ready. If you are voting in person, consider going during off-peak hours to avoid long lines.
Before you head to the polls, research the candidates and issues on the ballot. This will help you make informed decisions and feel more confident in your choices.
Don’t hesitate to ask for help if you need it. Election officials and poll workers are there to assist you. Additionally, many organizations offer support for first-time voters, including transportation to polling places and information hotlines.
Understand the security measures your state has implemented to protect the election process. This might include the use of paper ballots, post-election audits, and cybersecurity protocols. Being aware of these measures can increase your confidence in the election’s integrity.
If your state offers early voting, take advantage of it. Early voting can reduce the stress of long lines and crowded polling places on election day, making the process smoother and more secure.
Encourage friends and family to vote and educate them about election security. A well-informed electorate is a key component of a secure and fair election.
Keep up with reputable news sources to stay informed about any potential security threats or changes in the voting process. This will help you stay prepared and responsive to any issues that might arise.
By following these tips and staying vigilant, every voter can contribute to a secure and fair election process. Remember, your vote is your voice, and protecting it is essential for the health of our democracy. Happy voting!
The post What You Need to Know About Election Security appeared first on McAfee Blog.
Law enforcement agencies in the United States and Europe today announced Operation Endgame, a coordinated action against some of the most popular cybercrime platforms for delivering ransomware and data-stealing malware. Dubbed “the largest ever operation against botnets,” the international effort is being billed as the opening salvo in an ongoing campaign targeting advanced malware “droppers” or “loaders” like IcedID, Smokeloader and Trickbot.

A frame from one of three animated videos released today in connection with Operation Endgame.
Operation Endgame targets the cybercrime ecosystem supporting droppers/loaders, slang terms used to describe tiny, custom-made programs designed to surreptitiously install malware onto a target system. Droppers are typically used in the initial stages of a breach, and they allow cybercriminals to bypass security measures and deploy additional harmful programs, including viruses, ransomware, or spyware.
Droppers like IcedID are most often deployed through email attachments, hacked websites, or bundled with legitimate software. For example, cybercriminals have long used paid ads on Google to trick people into installing malware disguised as popular free software, such as Microsoft Teams, Adobe Reader and Discord. In those cases, the dropper is the hidden component bundled with the legitimate software that quietly loads malware onto the user’s system.
Droppers remain such a critical, human-intensive component of nearly all major cybercrime enterprises that the most popular have turned into full-fledged cybercrime services of their own. By targeting the individuals who develop and maintain dropper services and their supporting infrastructure, authorities are hoping to disrupt multiple cybercriminal operations simultaneously.
According to a statement from the European police agency Europol, between May 27 and May 29, 2024 authorities arrested four suspects (one in Armenia and three in Ukraine), and disrupted or took down more than 100 Internet servers in Bulgaria, Canada, Germany, Lithuania, the Netherlands, Romania, Switzerland, the United Kingdom, United States and Ukraine. Authorities say they also seized more than 2,000 domain names that supported dropper infrastructure online.
In addition, Europol released information on eight fugitives suspected of involvement in dropper services and who are wanted by Germany; their names and photos were added to Europol’s “Most Wanted” list on 30 May 2024.
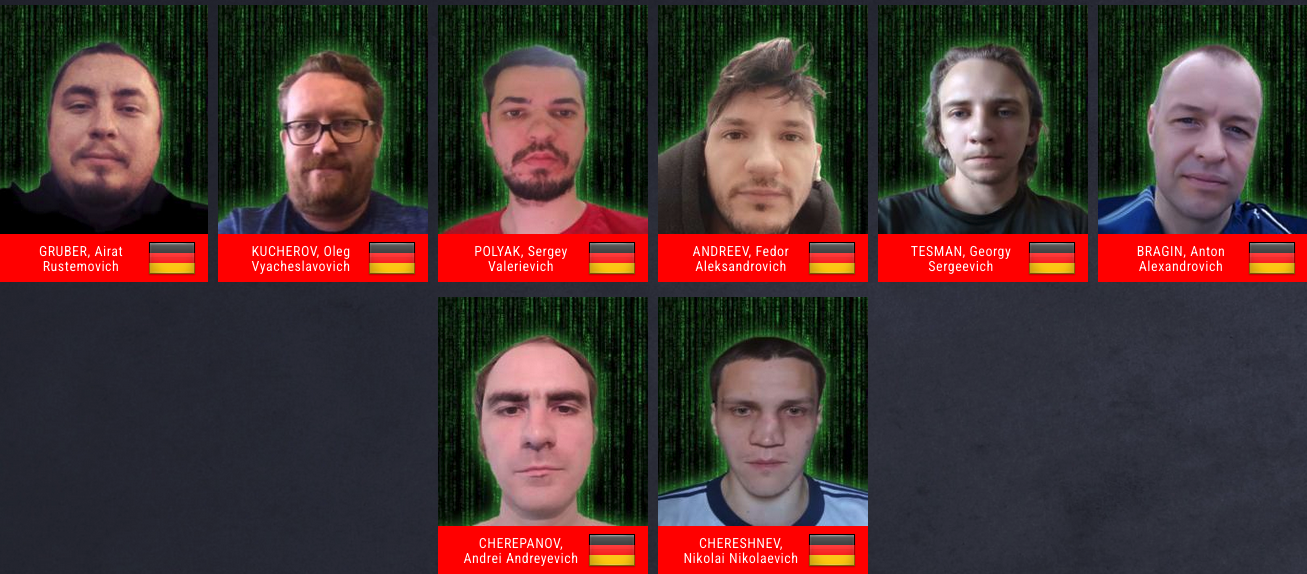
A “wanted” poster including the names and photos of eight suspects wanted by Germany and now on Europol’s “Most Wanted” list.
“It has been discovered through the investigations so far that one of the main suspects has earned at least EUR 69 million in cryptocurrency by renting out criminal infrastructure sites to deploy ransomware,” Europol wrote. “The suspect’s transactions are constantly being monitored and legal permission to seize these assets upon future actions has already been obtained.”
There have been numerous such coordinated malware takedown efforts in the past, and yet often the substantial amount of coordination required between law enforcement agencies and cybersecurity firms involved is not sustained after the initial disruption and/or arrests.
But a new website erected to detail today’s action — operation-endgame.com — makes the case that this time is different, and that more takedowns and arrests are coming. “Operation Endgame does not end today,” the site promises. “New actions will be announced on this website.”
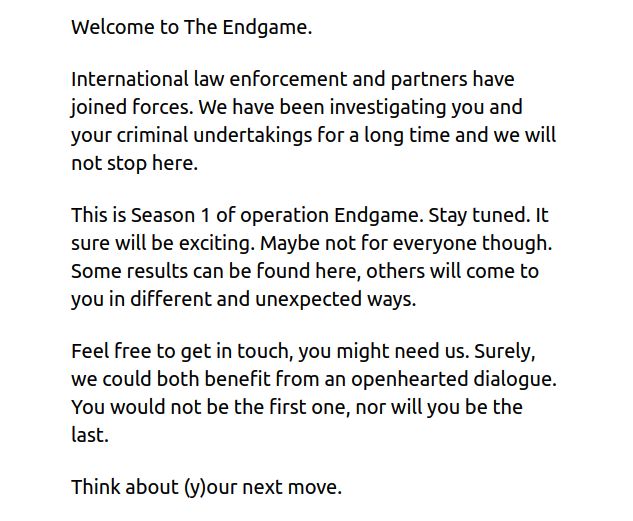
A message on operation-endgame.com promises more law enforcement and disruption actions.
Perhaps in recognition that many of today’s top cybercriminals reside in countries that are effectively beyond the reach of international law enforcement, actions like Operation Endgame seem increasingly focused on mind games — i.e., trolling the hackers.
Writing in this month’s issue of Wired, Matt Burgess makes the case that Western law enforcement officials have turned to psychological measures as an added way to slow down Russian hackers and cut to the heart of the sweeping cybercrime ecosystem.
“These nascent psyops include efforts to erode the limited trust the criminals have in each other, driving subtle wedges between fragile hacker egos, and sending offenders personalized messages showing they’re being watched,” Burgess wrote.
When authorities in the U.S. and U.K. announced in February 2024 that they’d infiltrated and seized the infrastructure used by the infamous LockBit ransomware gang, they borrowed the existing design of LockBit’s victim shaming website to link instead to press releases about the takedown, and included a countdown timer that was eventually replaced with the personal details of LockBit’s alleged leader.
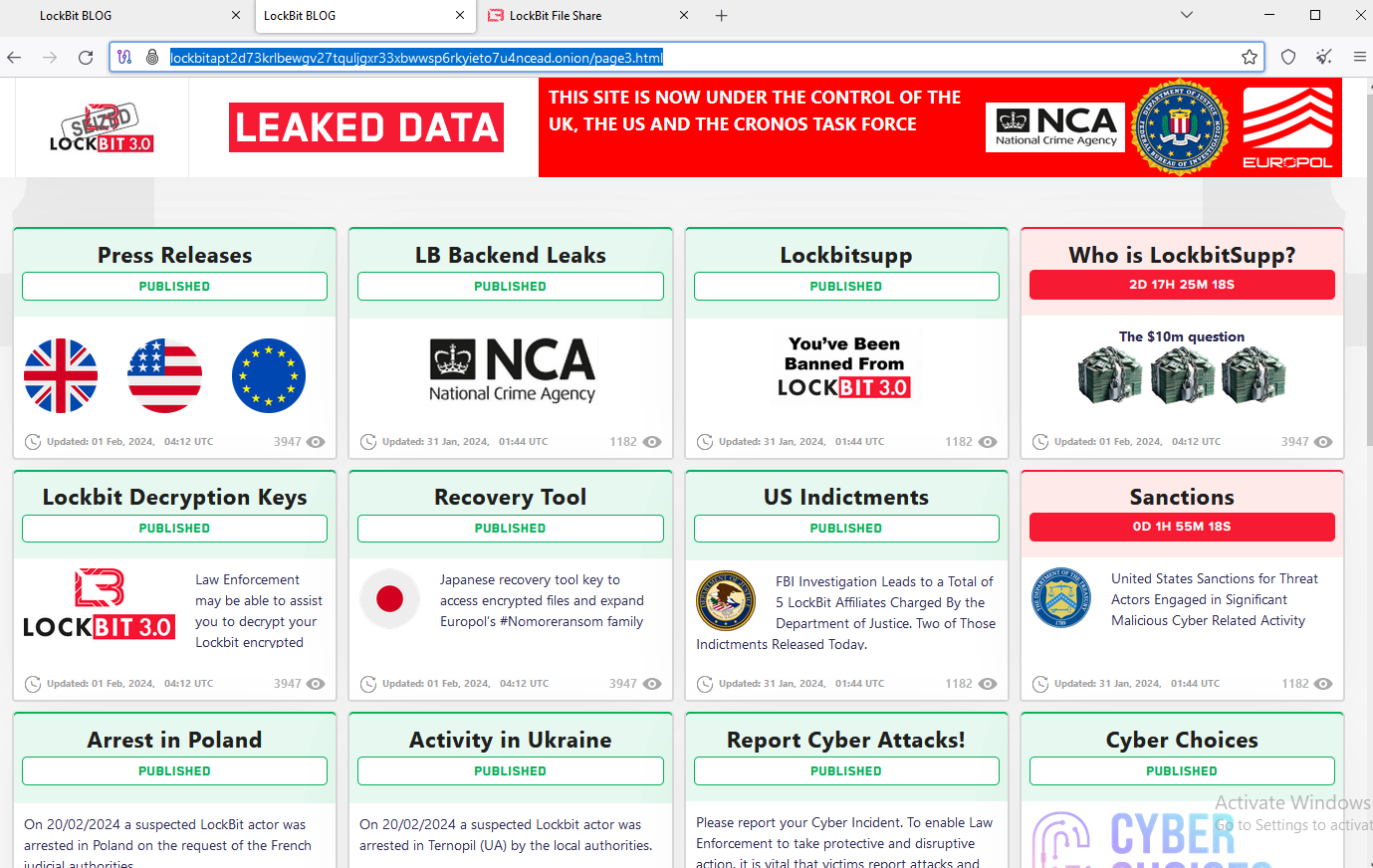
The feds used the existing design on LockBit’s victim shaming website to feature press releases and free decryption tools.
The Operation Endgame website also includes a countdown timer, which serves to tease the release of several animated videos that mimic the same sort of flashy, short advertisements that established cybercriminals often produce to promote their services online. At least two of the videos include a substantial amount of text written in Russian.
The coordinated takedown comes on the heels of another law enforcement action this week against what the director of the FBI called “likely the world’s largest botnet ever.” On Wednesday U.S. Department of Justice (DOJ) announced the arrest of YunHe Wang, the alleged operator of the ten-year-old online anonymity service 911 S5. The government also seized 911 S5’s domains and online infrastructure, which allegedly turned computers running various “free VPN” products into Internet traffic relays that facilitated billions of dollars in online fraud and cybercrime.

As the name implies, spear phishing attacks are highly targeted scams. They often occur in professional settings, where the scammers go after one “big phish,” such as a ranking employee with access to finances or data. From there, the scammers employ social engineering (aka manipulation) to trick the target into transferring funds to them or giving them access to sensitive company systems. Sometimes, it’s a mix of both.
Some of the most striking examples of spear phishing attacks come from the Shamoon2 attacks seen in Saudi Arabia back in 2016. Successive waves of attacks ultimately infected machines with malware and destroyed systems.
So, how did this specific spear phishing attack work, exactly? Cybercriminals targeted specific organizations in Saudi Arabia with emails that included malicious attachments in them. Then, when victims clicked and opened the attachment, they were infected, valuable company data was taken and systems were quickly wiped.
Spear phishing has been around for quite some time yet remains as effective as ever. Spear phishing’s success is based on familiarity. Usually, cybercriminals pretend to be an organization or individual that you know and include a piece of content—a link, an email attachment, etc.—that they know you’ll want to interact with.
For example, cybercriminals have taken advantage of tragedies in the headlines and used targeted emails claiming to be a charitable organization asking for donations. In the case of Shamoon2, the attackers lured in victims with a tempting email attachment sent from organizations the victims were likely to trust. But instead of giving to their charity of choice, or opening a seemingly harmless workplace attachment, victims then self-infect their systems with malware.
Moreover, we have seen spear phishing attacks take on an entirely new form with the advent of AI deepfakes. Now, instead of reaching out to victims via email, sophisticated scammers create deepfakes that pose as employees on video calls. All in real-time. Such was the case in Hong Kong in February 2024 where a host of deepfakes pressured a company’s finance officer into transferring $25 million to the scammers running the deepfakes.[i]
Moral of the story: spear phishing (and regular phishing) attacks can be tricky. However, fear not, there’s a lot you can do to stay on top of this threat.
For starters:
Spear phishing attacks can be easily deceiving. In fact, cybercriminals have been able to impersonate known, credible charities or an employer’s business partners and customers. So, if you receive an email from an organization asking for donations or a partner asking you to open a file you didn’t request, a good rule of thumb is to go directly to the organization through a communications channel other than email. Go to the company’s site and do more research from there. That way, you can ensure you’re gaining accurate information and can interact with the right people, rather than cyber-attackers.
Always check for legitimacy first. Spear phishing emails rely on you—they want you to click a link, or open an attachment. But before you do anything, you always need to check an email’s content for legitimacy. Hover over a link and see if it’s going to a reliable URL. Or, if you’re unsure about an email’s content or the source it came from, do a quick Google search and look for other instances of this campaign, and what those instances could tell you about the email’s legitimacy.
Fraudsters select their victims carefully in these targeted attacks. They hunt down employees with access to info and funds and then do their research on them. Using public records, data broker sites, “people finder” sites, and info from social media, fraudsters collect intel on their marks. Armed with that, they can pepper their conversations with references that sound more informed, more personal, and thus more convincing. Just because what’s being said feels or sounds somewhat familiar doesn’t always mean it’s coming from a trustworthy source.
With that, employees can reduce the amount of personal info others can find online. Features like McAfee Personal Data Cleanup can help remove personal info from some of the riskiest data broker sites out there. I also keep tabs on those sites if more personal info appears on them later. Additionally, employees can set their social media profiles to private by limiting access to “friends and family only,” which denies fraudsters another avenue of info gathering. Using our Social Privacy Manager can make that even easier. With just a few clicks, it can adjust more than 100 privacy settings across their social media accounts — making them more private as a result.
[i] https://metro.co.uk/2024/02/05/horrifying-deepfake-tricks-employee-giving-away-20-million-20225490/
The post How to Protect Yourself From a Spear Phishing Scam appeared first on McAfee Blog.
To install headerpwn, run the following command:
go install github.com/devanshbatham/headerpwn@v0.0.3
headerpwn allows you to test various headers on a target URL and analyze the responses. Here's how to use the tool:
-url flag.-headers flag to specify the path to this file.Example usage:
headerpwn -url https://example.com -headers my_headers.txt
my_headers.txt should be like below:Proxy-Authenticate: foobar
Proxy-Authentication-Required: foobar
Proxy-Authorization: foobar
Proxy-Connection: foobar
Proxy-Host: foobar
Proxy-Http: foobar
Follow following steps to proxy requests through Burp Suite:
Export Burp's Certificate:
127.0.0.1:8080
Install Burp's Certificate:
You should be all set:
headerpwn -url https://example.com -headers my_headers.txt -proxy 127.0.0.1:8080
The headers.txt file is compiled from various sources, including the SecLists">Seclists project. These headers are used for testing purposes and provide a variety of scenarios for analyzing how servers respond to different headers.
The U.S. Department of Justice (DOJ) today said they arrested the alleged operator of 911 S5, a ten-year-old online anonymity service that was powered by what the director of the FBI called “likely the world’s largest botnet ever.” The arrest coincided with the seizure of the 911 S5 website and supporting infrastructure, which the government says turned computers running various “free VPN” products into Internet traffic relays that facilitated billions of dollars in online fraud and cybercrime.

The Cloud Router homepage, which was seized by the FBI this past weekend. Cloud Router was previously called 911 S5.
On May 24, authorities in Singapore arrested the alleged creator and operator of 911 S5, a 35-year-old Chinese national named YunHe Wang. In a statement on his arrest today, the DOJ said 911 S5 enabled cybercriminals to bypass financial fraud detection systems and steal billions of dollars from financial institutions, credit card issuers, and federal lending programs.
For example, the government estimates that 560,000 fraudulent unemployment insurance claims originated from compromised Internet addresses, resulting in a confirmed fraudulent loss exceeding $5.9 billion.
“Additionally, in evaluating suspected fraud loss to the Economic Injury Disaster Loan (EIDL) program, the United States estimates that more than 47,000 EIDL applications originated from IP addresses compromised by 911 S5,” the DOJ wrote. “Millions of dollars more were similarly identified by financial institutions in the United States as loss originating from IP addresses compromised by 911 S5.”
From 2015 to July 2022, 911 S5 sold access to hundreds of thousands of Microsoft Windows computers daily, as “proxies” that allowed customers to route their Internet traffic through PCs in virtually any country or city around the globe — but predominantly in the United States.
911 S5 built its proxy network mainly by offering “free” virtual private networking (VPN) services. 911’s VPN performed largely as advertised for the user — allowing them to surf the web anonymously — but it also quietly turned the user’s computer into a traffic relay for paying 911 S5 customers.
911 S5’s reliability and extremely low prices quickly made it one of the most popular services among denizens of the cybercrime underground, and the service became almost shorthand for connecting to that “last mile” of cybercrime. Namely, the ability to route one’s malicious traffic through a computer that is geographically close to the consumer whose stolen credit card is about to be used, or whose bank account is about to be emptied.
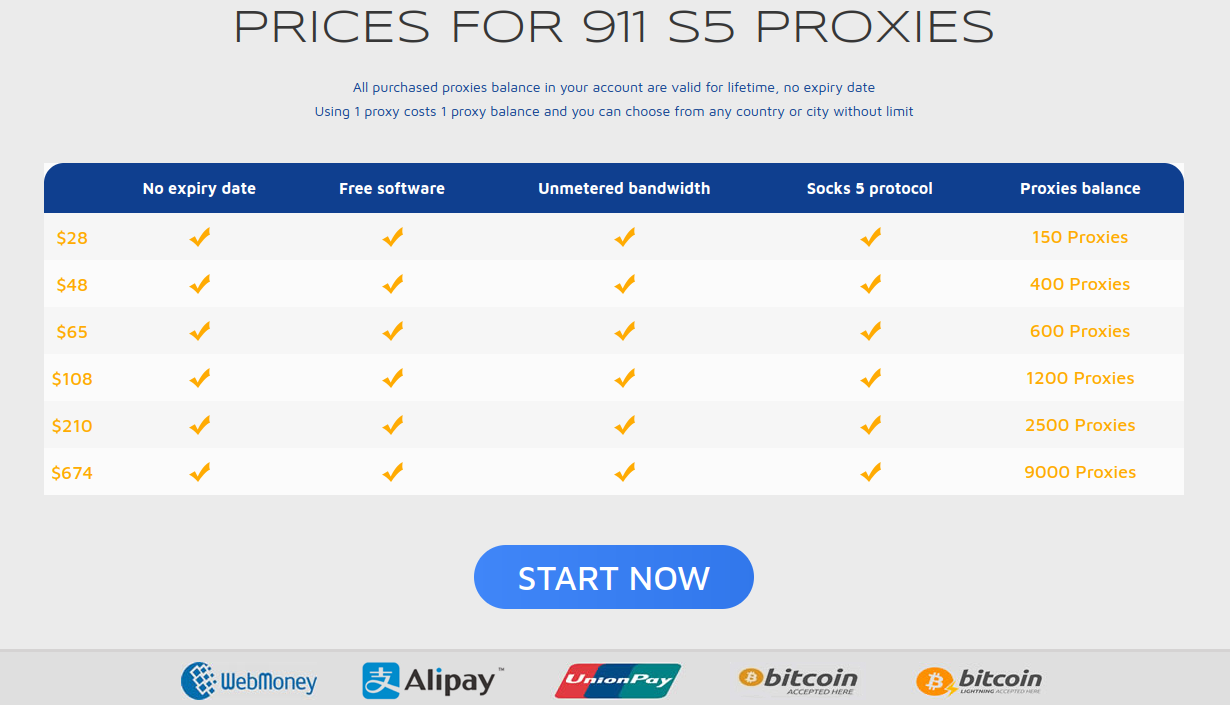
The prices page for 911 S5, circa July 2022. $28 would let users cycle through 150 proxies on this popular service.
KrebsOnSecurity first identified Mr. Wang as the proprietor of the popular service in a deep dive on 911 S5 published in July 2022. That story showed that 911 S5 had a history of paying people to install its software by secretly bundling it with other software — including fake security updates for common programs like Flash Player, and “cracked” or pirated commercial software distributed on file-sharing networks.
Ten days later, 911 S5 closed up shop, claiming it had been hacked. But experts soon tracked the reemergence of the proxy network by another name: Cloud Router.
The announcement of Wang’s arrest came less than 24 hours after the U.S. Department of the Treasury sanctioned Wang and two associates, as well as several companies the men allegedly used to launder the nearly $100 million in proceeds from 911 S5 and Cloud Router customers.
Cloud Router’s homepage now features a notice saying the domain has been seized by the U.S. government. In addition, the DOJ says it worked with authorities in Singapore, Thailand and Germany to search residences tied to the defendant, and seized approximately $30 million in assets.

The Cloud Router homepage now features a seizure notice from the FBI in multiple languages.
Those assets included a 2022 Ferrari F8 Spider S-A, a BMW i8, a BMW X7 M50d, a Rolls Royce, more than a dozen domestic and international bank accounts, over two dozen cryptocurrency wallets, several luxury wristwatches, and 21 residential or investment properties.
The government says Wang is charged with conspiracy to commit computer fraud, substantive computer fraud, conspiracy to commit wire fraud, and conspiracy to commit money laundering. If convicted on all counts, he faces a maximum penalty of 65 years in prison.
Brett Leatherman, deputy assistant director of the FBI’s Cyber Division, said the DOJ is working with the Singaporean government on extraditing Wang to face charges in the United States.
Leatherman encouraged Internet users to visit a new FBI webpage that can help people determine whether their computers may be part of the 911 S5 botnet, which the government says spanned more than 19 million individual computers in at least 190 countries.
Leatherman said 911 S5 and Cloud Router used several “free VPN” brands to lure consumers into installing the proxy service, including MaskVPN, DewVPN, PaladinVPN, Proxygate, Shield VPN, and ShineVPN.
“American citizens who didn’t know that their IP space was being utilized to attack US businesses or defraud the U.S. government, they were unaware,” Leatherman said. “But these kind of operations breed that awareness.”
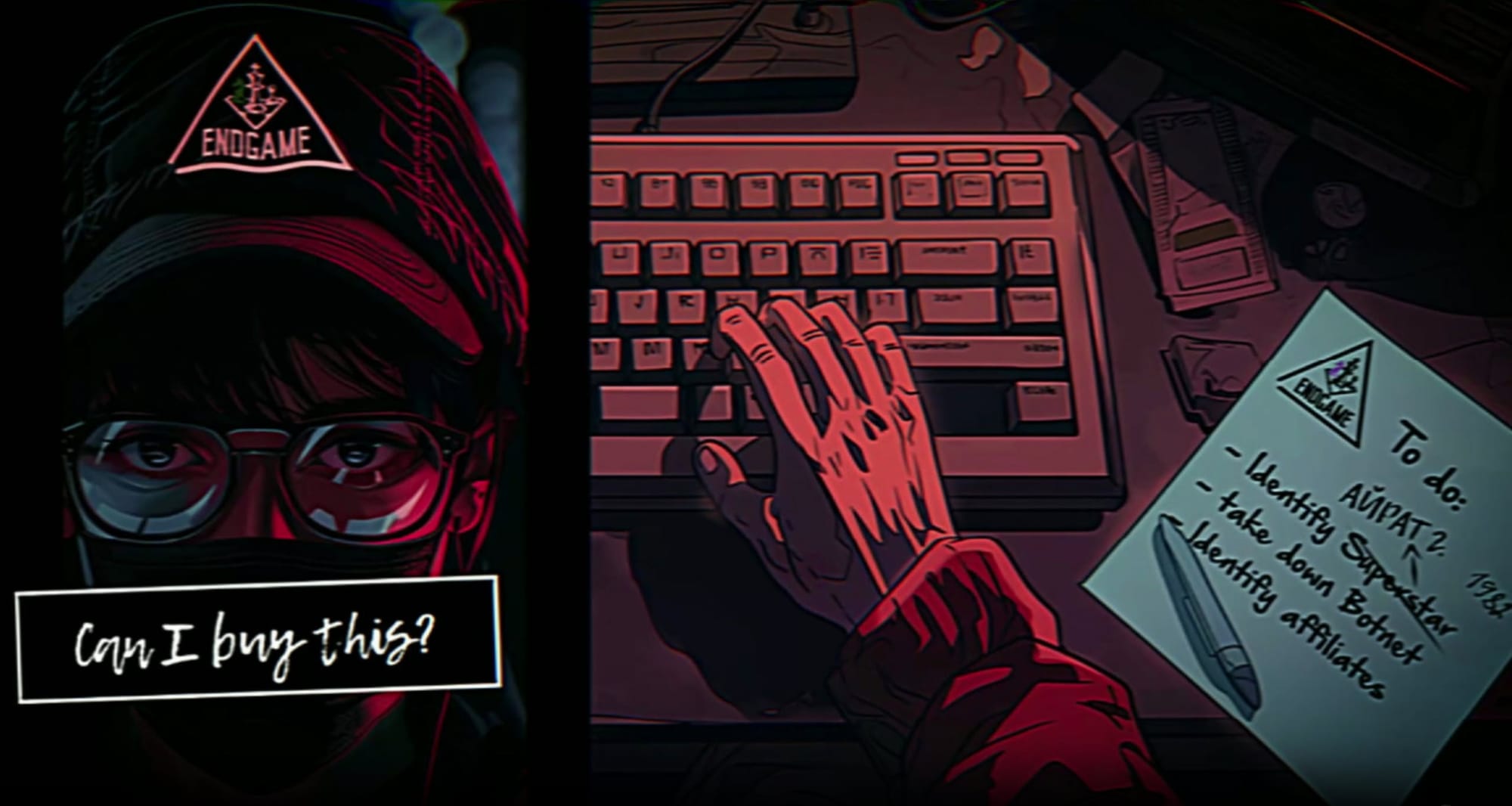
Today we loaded 16.5M email addresses and 13.5M unique passwords provided by law enforcement agencies into Have I Been Pwned (HIBP) following botnet takedowns in a campaign they've coined Operation Endgame. That link provides an excellent overview so start there then come back to this blog post which adds some insight into the data and explains how HIBP fits into the picture.
Since 2013 when I kicked off HIBP as a pet project, it has become an increasingly important part of the security posture of individuals, organisations, governments and law enforcement agencies. Gradually and organically, it has found a fit where it's able to provide a useful service to the good guys after the bad guys have done evil cyber things. The phrase I've been fond of this last decade is that HIBP is there to do good things with data after bad things happen. The reputation and reach the service has gained in this time has led to partnerships such as the one you're reading about here today. So, with that in mind, let's get into the mechanics of the data:
In terms of the email addresses, there were 16.5M in total with 4.5M of them not having been seen in previous data breaches already in HIBP. We found 25k of our own individual subscribers in the corpus of data, plus another 20k domain subscribers which is usually organisations monitoring the exposure of their customers (all of these subscribers have now been sent notification emails). As the data was provided to us by law enforcement for the public good, the breach is flagged as subscription free which means any organisation that can prove control of the domain can search it irrespective of the subscription model we launched for large domains in August last year.
The only data we've been provided with is email addresses and disassociated password hashes, that is they don't appear alongside a corresponding address. This is the bare minimum we need to make that data searchable and useful to those impacted. So, let's talk about those standalone passwords:
There are 13.5 million unique passwords of which 8.9M were already in Pwned Passwords. Those passwords have had their prevalence counts updated accordingly (we received counts for each password with many appearing in the takedown multiple times over), so if you're using Pwned Passwords already, you'll see new numbers next to some entries. That also means there are 4.6M passwords we've never seen before which you can freely download using our open source tool. Or even better, if you're querying Pwned Passwords on demand you don't need to do anything as the new entries are automatically added to the result set. All this is made possible by feeding the data into the law enforcement pipeline we built for the FBI and NCA a few years ago.
A quick geek-out moment on Pwned Passwords: at present, we're serving almost 8 billion requests per month to this service:
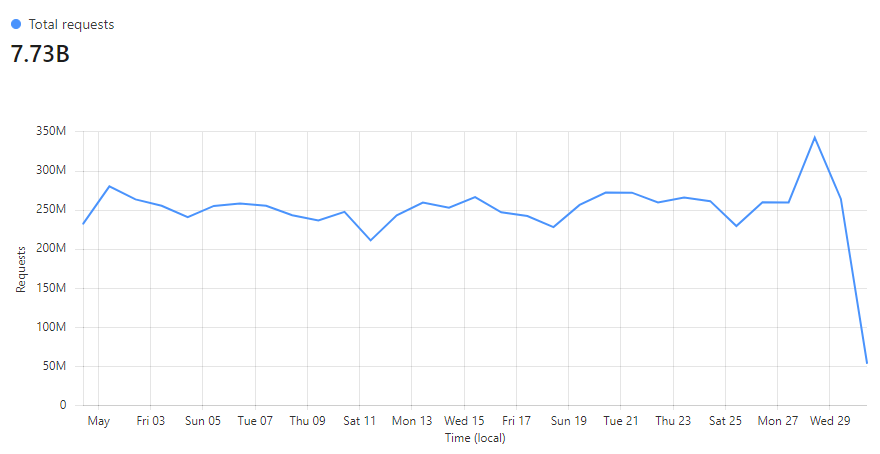
Taking just last week as an example, we're a rounding error off 100% of requests being served directly from Cloudflare's cache:
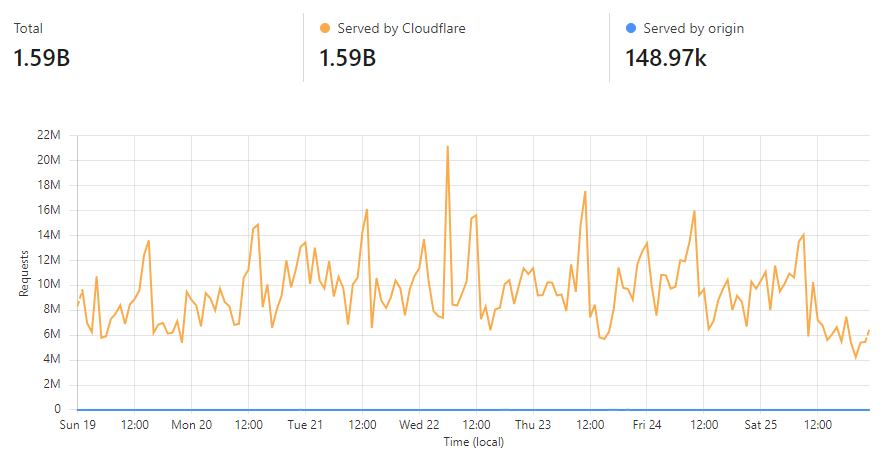
That's over 99.99% of all requests during that period that were served from one of Cloudflare's edge nodes that sit in 320 cities globally. What that means for consumers of the service is massively fast response times due to the low latency of serving content from a nearby location and huge confidence in availability as there's only about a one-in-ten-thousand chance of the request being served by our origin service. If you'd like to know more about how we achieved this, check out my post from a year ago on using Cloudflare Cache Reserve.
After pushing out the new passwords today, all but 5 hash prefixes were modified (read more about how we use hashes to enable anonymous password searches) so we did a complete Cloudflare cache flush. By the time you read this, almost the entire 16^5 possible hash ranges have been completely repopulated into cache due to the volume of requests the service receives:
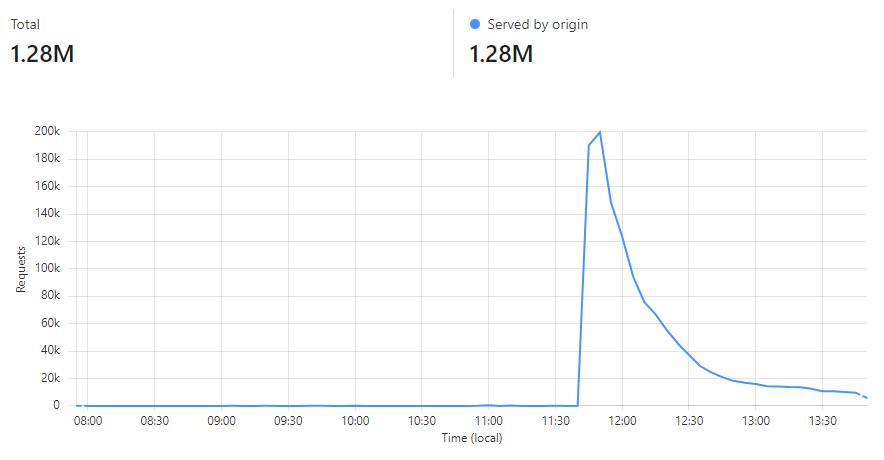
Lastly, when we talk about passwords in HIBP, the inputs we receive from law enforcement consist of 3 parts:
The rationale for this is explained in the links above but in a nutshell, the SHA-1 format ensures any badly parsed data that may inadvertently include PII is protected and it aligns with the underlying data structure that drives the k-anonymity searches. We have NTLM hashes as well because many orgs use them to check passwords in their own Active Directory instances.
So, what can you do if you find your data in this incident? It's a similar story to the Emotet malware provided by the FBI and NHTCU a few years ago in that the sage old advice applies: get a password manager and make them all strong and unique, turn on 2FA everywhere, keep machines patched, etc. If you find your password in the data (the HIBP password search feature anonymises it before searching, or password managers like 1Password can scan all of your passwords in one go), obviously change it everywhere you've used it.
This operation will be significant in terms of the impact on cybercrime, and I'm glad we've been able to put this little project to good use by supporting our friends in law enforcement who are doing their best to support all of us as online citizens.
A tool to generate a wordlist from the information present in LDAP, in order to crack non-random passwords of domain accounts.
The bigger the domain is, the better the wordlist will be.
name and sAMAccountName
name and sAMAccountName
name
name
name and descriptions
descriptions
--outputfile
To generate a wordlist from the LDAP of the domain domain.local you can use this command:
./LDAPWordlistHarvester.py -d 'domain.local' -u 'Administrator' -p 'P@ssw0rd123!' --dc-ip 192.168.1.101
You will get the following output if using the Python version:
You will get the following output if using the Powershell version:
Once you have this wordlist, you should crack your NTDS using hashcat, --loopback and the rule clem9669_large.rule.
./hashcat --hash-type 1000 --potfile-path ./client.potfile ./client.ntds ./wordlist.txt --rules ./clem9669_large.rule --loopback
$ ./LDAPWordlistHarvester.py -h
LDAPWordlistHarvester.py v1.1 - by @podalirius_
usage: LDAPWordlistHarvester.py [-h] [-v] [-o OUTPUTFILE] --dc-ip ip address [-d DOMAIN] [-u USER] [--ldaps] [--no-pass | -p PASSWORD | -H [LMHASH:]NTHASH | --aes-key hex key] [-k]
options:
-h, --help show this help message and exit
-v, --verbose Verbose mode. (default: False)
-o OUTPUTFILE, --outputfile OUTPUTFILE
Path to output file of wordlist.
Authentication & connection:
--dc-ip ip address IP Address of the domain controller or KDC (Key Distribution Center) for Kerberos. If omitted it will use the domain part (FQDN) specified in the identity parameter
-d DOMAIN, --domain DOMAIN
(FQDN) domain to authenticate to
-u USER, --user USER user to authenticate with
--ldaps Use LDAPS instead of LDAP
Credentials:
--no- pass Don't ask for password (useful for -k)
-p PASSWORD, --password PASSWORD
Password to authenticate with
-H [LMHASH:]NTHASH, --hashes [LMHASH:]NTHASH
NT/LM hashes, format is LMhash:NThash
--aes-key hex key AES key to use for Kerberos Authentication (128 or 256 bits)
-k, --kerberos Use Kerberos authentication. Grabs credentials from .ccache file (KRB5CCNAME) based on target parameters. If valid credentials cannot be found, it will use the ones specified in the command line
The U.S. Department of the Treasury today unveiled sanctions against three Chinese nationals for allegedly operating 911 S5, an online anonymity service that for many years was the easiest and cheapest way to route one’s Web traffic through malware-infected computers around the globe. KrebsOnSecurity identified one of the three men in a July 2022 investigation into 911 S5, which was massively hacked and then closed ten days later.
The 911 S5 botnet-powered proxy service, circa July 2022.
From 2015 to July 2022, 911 S5 sold access to hundreds of thousands of Microsoft Windows computers daily, as “proxies” that allowed customers to route their Internet traffic through PCs in virtually any country or city around the globe — but predominantly in the United States.
911 built its proxy network mainly by offering “free” virtual private networking (VPN) services. 911’s VPN performed largely as advertised for the user — allowing them to surf the web anonymously — but it also quietly turned the user’s computer into a traffic relay for paying 911 S5 customers.
911 S5’s reliability and extremely low prices quickly made it one of the most popular services among denizens of the cybercrime underground, and the service became almost shorthand for connecting to that “last mile” of cybercrime. Namely, the ability to route one’s malicious traffic through a computer that is geographically close to the consumer whose stolen credit card is about to be used, or whose bank account is about to be emptied.
In July 2022, KrebsOnSecurity published a deep dive into 911 S5, which found the people operating this business had a history of encouraging the installation of their proxy malware by any means available. That included paying affiliates to distribute their proxy software by secretly bundling it with other software.
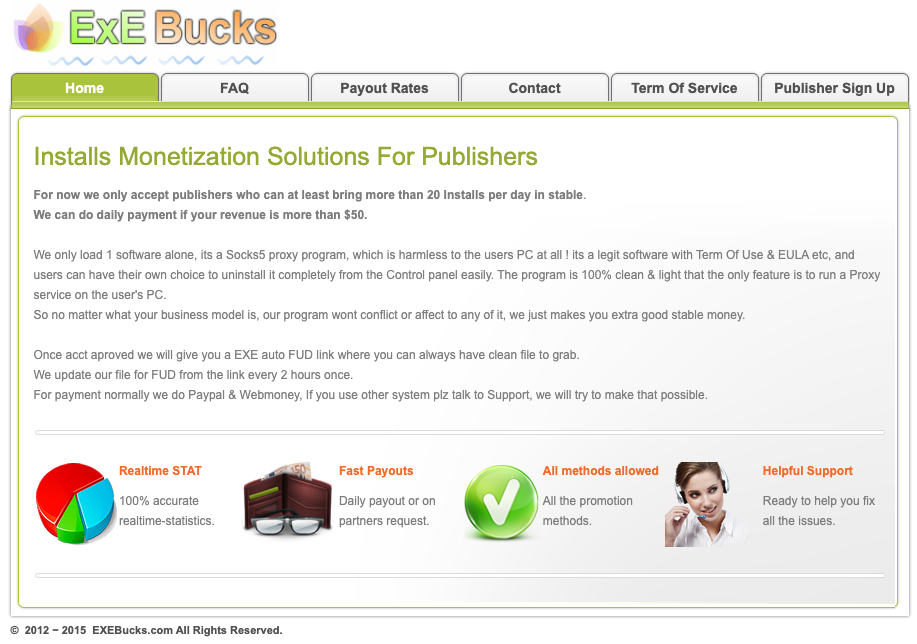
A cached copy of flashupdate dot net, a pay-per-install affiliate program that incentivized the silent installation of 911’s proxy software.
That story named Yunhe Wang from Beijing as the apparent owner or manager of the 911 S5 proxy service. In today’s Treasury action, Mr. Wang was named as the primary administrator of the botnet that powered 911 S5.
“A review of records from network infrastructure service providers known to be utilized by 911 S5 and two Virtual Private Networks (VPNs) specific to the botnet operation (MaskVPN and DewVPN) showed Yunhe Wang as the registered subscriber to those providers’ services,” reads the Treasury announcement.
Update, May 29, 12:26 p.m. ET: The U.S. Department of Justice (DOJ) just announced they have arrested Wang in connection with the 911 S5 botnet. The DOJ says 911 S5 customers have stolen billions of dollars from financial institutions, credit card issuers, and federal lending programs.
“911 S5 customers allegedly targeted certain pandemic relief programs,” a DOJ statement on the arrest reads. “For example, the United States estimates that 560,000 fraudulent unemployment insurance claims originated from compromised IP addresses, resulting in a confirmed fraudulent loss exceeding $5.9 billion. Additionally, in evaluating suspected fraud loss to the Economic Injury Disaster Loan (EIDL) program, the United States estimates that more than 47,000 EIDL applications originated from IP addresses compromised by 911 S5. Millions of dollars more were similarly identified by financial institutions in the United States as loss originating from IP addresses compromised by 911 S5.”
The sanctions say Jingping Liu was Yunhe Wang’s co-conspirator in the laundering of criminally derived proceeds generated from 911 S5, mainly virtual currency. The government alleges the virtual currencies paid by 911 S5 users were converted into U.S. dollars using over-the-counter vendors who wired and deposited funds into bank accounts held by Liu.
“Jingping Liu assisted Yunhe Wang by laundering criminally derived proceeds through bank accounts held in her name that were then utilized to purchase luxury real estate properties for Yunhe Wang,” the document continues. “These individuals leveraged their malicious botnet technology to compromise personal devices, enabling cybercriminals to fraudulently secure economic assistance intended for those in need and to terrorize our citizens with bomb threats.”
The third man sanctioned is Yanni Zheng, a Chinese national the U.S. Treasury says acted as an attorney for Wang and his firm — Spicy Code Company Limited — and helped to launder proceeds from the business into real estate holdings. Spicy Code Company was also sanctioned, as well as Wang-controlled properties Tulip Biz Pattaya Group Company Limited, and Lily Suites Company Limited.
Ten days after the July 2022 story here on 911 S5, the proxy network abruptly closed up shop, citing a data breach that destroyed key components of its business operations.
In the months that followed, however, 911 S5 would resurrect itself under a different name: Cloud Router. That’s according to spur.us, a U.S.-based startup that tracks proxy and VPN services. In February 2024, Spur published research showing the Cloud Router operators reused many of the same components from 911 S5, making it relatively simple to draw a connection between the two.

The Cloud Router homepage, which according to Spur has been unreachable since this past weekend.
Spur found that Cloud Router was being powered by a new VPN service called PaladinVPN, which made it much more explicit to users that their Internet connections were going to be used to relay traffic for others. At the time, Spur found Cloud Router had more than 140,000 Internet addresses for rent.
Spur co-founder Riley Kilmer said Cloud Router appears to have suspended or ceased operations sometime this past weekend. Kilmer said the number of proxies advertised by the service had been trending downwards quite recently before the website suddenly went offline.
Cloud Router’s homepage is currently populated by a message from Cloudflare saying the site’s domain name servers are pointing to a “prohibited IP.”