
Tax season is a prime time for cybercriminals, especially those running phishing scams to steal W-2s. With many people filing their tax returns, scammers take advantage of the rush to trick unsuspecting individuals into handing over sensitive financial data. This blog highlights the rise in tax-related cybercrime and offers practical tips to keep your information safe.
W-2 phishing scams often involve emails that appear to be from the IRS or another official source, requesting personal information. These phishing emails can be highly sophisticated, often mimicking the look and feel of legitimate communications. The goal is to trick the recipient into revealing confidential data, such as social security numbers and financial information, which the perpetrator can then use for fraudulent purposes. The first step in protecting against such scams is understanding how they work and being able to recognize the red flags.
Phishing scams are fundamentally deception tactics—disguised as legitimate correspondence, they aim to trick the recipient into parting with sensitive information. In the case of W-2 phishing scams, the perpetrator often poses as an employer, government agency, or financial institution. The message may request that the recipient update their personal information, verify their identity, or provide their W-2 form. Typically, these emails have a sense of urgency, indicating that failure to comply will result in adverse consequences.
The contents of a phishing email are often compelling and appear to be authentic. They may contain official logos, legal disclaimers, and even legitimate contact details. However, closer examination often reveals telltale signs of phishing. For example, the email address of the sender may not match the organization they claim to represent, or the message may contain poor grammar and spelling. Additionally, phishing emails often require the recipient to click a link or open an attachment—actions that could potentially install malware on the victim’s device or redirect them to a fraudulent website.
McAfee Pro Tip: Nowadays, those sneaky social engineering tricks look a lot like legit messages from well-known folks. They’re super well-crafted, with proper grammar, and seamlessly fit into everyday situations. But don’t be fooled by their slick appearance – underneath it all, they’re still after your sensitive info. Keep your personal stuff safe and sound with McAfee+ to dodge the headaches that come with social engineering.
Recent years have seen a significant increase in the number of reported W-2 phishing scams. According to the FBI’s Internet Crime Complaint Center (IC3), thousands of these scams occur every tax season, leading to substantial financial losses and ID theft. Not only does this affect individuals, but businesses too. In fact, some companies have reported instances where their entire workforce was targeted, resulting in massive data breaches.
The impact of falling for a W-2 phishing scam can be devastating. Once cybercriminals have gained access to your financial data, they can use it in a variety of malicious ways. This may include filing fraudulent tax returns, opening new credit accounts, or even selling the information on the black market. The recovery process from such scams can be lengthy and stressful, as victims have to prove their identity to the IRS, their bank, and credit reporting agencies. Additionally, they need to monitor their financial activity closely for signs of any further unauthorized transactions or fraudulent activities.
→ Dig Deeper: Watch Out For IRS Scams and Avoid Identity Theft
Given the prevalence and potential impact of W-2 phishing scams, it’s crucial to take steps to protect yourself. One of the most effective strategies is to improve your digital literacy, namely your ability to identify and respond appropriately to phishing attempts. This includes being skeptical of unsolicited emails, especially those that ask for personal or financial information. Always verify the sender’s identity before responding or clicking any links. Remember, legitimate organizations rarely request sensitive information via email.
Another important safeguard is to ensure your computer and mobile devices are protected with up-to-date security software. This can help identify and block potential phishing emails and malicious links. Further, regularly backing up data can help mitigate the potential damage caused by a successful breach. Consider using a secure cloud service or an external storage device for this purpose.
Next is to file your tax returns as early as possible. By doing so, you can beat the scammers who might make an attempt to file a fraudulent tax return in your name. Additionally, if you receive an email that appears suspicious, do not click on the links or download the attachments included in that email. Instead, forward the suspicious email to phishing@irs.gov.
Using a VPN also adds an extra layer of security by encrypting your internet connection, protecting your personal data from hackers, especially when accessing sensitive information like tax documents.
Finally, two-factor authentication (2FA) is another excellent way to safeguard your data. By enabling 2FA, you are adding an extra layer of security that makes it harder for cybercriminals to access your data even if they get your password. Additionally, always be cautious about sharing your personal and financial information online. Make sure that you only enter such information on secure websites – those with ‘https://’ in the URL. Regularly check your financial accounts for any suspicious activity and report immediately to your bank if you notice anything unusual.
If you believe you have fallen victim to a W-2 phishing scam, it is crucial to act quickly. If you have divulged your social security number, contact the IRS immediately. They can aid you in taking steps to prevent potential tax fraud. Additionally, it would be wise to file an identity theft affidavit (Form 14039) with the IRS. This form alerts the IRS to the theft of your identity and allows them to secure your tax account.
Additionally, you should report the phishing scam to the Federal Trade Commission (FTC) using the FTC Complaint Assistant at FTC.gov. If you have clicked on a link or downloaded a suspicious attachment, run a full antivirus scan to check for malware. You should also consider placing a fraud alert or a credit freeze on your credit reports, which makes it harder for someone to open a new account in your name. Finally, you should check your credit reports frequently for any signs of fraudulent activity.
→Dig Deeper: Credit Lock and Credit Freeze: Which Service Is Best for You? Both!
Protecting your financial data during tax season is crucial, and being aware of phishing scams can save you from a world of trouble. By understanding the nature of W-2 phishing scams and implementing the above-mentioned best practices, you can keep your sensitive information safe. Remember to always be skeptical of unsolicited emails and never share personal or financial information unless you can confirm the legitimacy of the request. By doing so, you will not only protect yourself but also contribute to the collective fight against cybercrime.
Protecting your W-2 information during tax season is not a one-time effort but a continuous process. Always stay vigilant, and remember that it’s better to be safe than sorry. If you ever suspect that you have become a victim of a W-2 phishing scam, take prompt action by reporting it to the relevant authorities and taking necessary measures to mitigate possible damages. The key to staying safe is staying informed, vigilant, and prepared.
The post How to Protect Your Financial Data During Tax Season appeared first on McAfee Blog.

When we come across the term Artificial Intelligence (AI), our mind often ventures into the realm of sci-fi movies like I, Robot, Matrix, and Ex Machina. We’ve always perceived AI as a futuristic concept, something that’s happening in a galaxy far, far away. However, AI is not only here in our present but has also been a part of our lives for several years in the form of various technological devices and applications.
In our day-to-day lives, we use AI in many instances without even realizing it. AI has permeated into our homes, our workplaces, and is at our fingertips through our smartphones. From cell phones with built-in smart assistants to home assistants that carry out voice commands, from social networks that determine what content we see to music apps that curate playlists based on our preferences, AI has its footprints everywhere. Therefore, it’s integral to not only embrace the wows of this impressive technology but also understand and discuss the potential risks associated with it.
→ Dig Deeper: Artificial Imposters—Cybercriminals Turn to AI Voice Cloning for a New Breed of Scam
AI, a term that might sound intimidating to many, is not so when we understand it. It is essentially technology that can be programmed to achieve certain goals without assistance. In simple words, it’s a computer’s ability to predict, process data, evaluate it, and take necessary action. This smart way of performing tasks is being implemented in education, business, manufacturing, retail, transportation, and almost every other industry and cultural sector you can think of.
AI has been doing a lot of good too. For instance, Instagram, the second most popular social network, is now deploying AI technology to detect and combat cyberbullying in both comments and photos. No doubt, AI is having a significant impact on everyday life and is poised to metamorphose the future landscape. However, alongside its benefits, AI has brought forward a set of new challenges and risks. From self-driving cars malfunctioning to potential jobs lost to AI robots, from fake videos and images to privacy breaches, the concerns are real and need timely discussions and preventive measures.
AI has made it easier for people to face-swap within images and videos, leading to “deep fake” videos that appear remarkably realistic and often go viral. A desktop application called FakeApp allows users to seamlessly swap faces and share fake videos and images. While this displays the power of AI technology, it also brings to light the responsibility and critical thinking required when consuming and sharing online content.
→ Dig Deeper: The Future of Technology: AI, Deepfake, & Connected Devices
Yet another concern raised by AI is privacy breaches. The Cambridge Analytica/Facebook scandal of 2018, alleged to have used AI technology unethically to collect Facebook user data, serves as a reminder that our private (and public) information can be exploited for financial or political gain. Thus, it becomes crucial to discuss and take necessary steps like locking down privacy settings on social networks and being mindful of the information shared in the public feed, including reactions and comments on other content.
McAfee Pro Tip: Cybercriminals employ advanced methods to deceive individuals, propagating sensationalized fake news, creating deceptive catfish dating profiles, and orchestrating harmful impersonations. Recognizing sophisticated AI-generated content can pose a challenge, but certain indicators may signal that you’re encountering a dubious image or interacting with a perpetrator operating behind an AI-generated profile. Know the indicators.
With the advent of AI, cybercrime has found a new ally. As per McAfee’s Threats Prediction Report, AI technology might enable hackers to bypass security measures on networks undetected. This can lead to data breaches, malware attacks, ransomware, and other criminal activities. Moreover, AI-generated phishing emails are scamming people into unknowingly handing over sensitive data.
→ Dig Deeper: How to Keep Your Data Safe From the Latest Phishing Scam
Bogus emails are becoming highly personalized and can trick intelligent users into clicking malicious links. Given the sophistication of these AI-related scams, it is vital to constantly remind ourselves and our families to be cautious with every click, even those from known sources. The need to be alert and informed cannot be overstressed, especially in times when AI and cybercrime often seem to be two sides of the same coin.
As homes evolve to be smarter and synced with AI-powered Internet of Things (IoT) products, potential threats have proliferated. These threats are not limited to computers and smartphones but extend to AI-enabled devices such as voice-activated assistants. According to McAfee’s Threat Prediction Report, these IoT devices are particularly susceptible as points of entry for cybercriminals. Other devices at risk, as highlighted by security experts, include routers, and tablets.
This means we need to secure all our connected devices and home internet at its source – the network. Routers provided by your ISP (Internet Security Provider) are often less secure, so consider purchasing your own. As a primary step, ensure that all your devices are updated regularly. More importantly, change the default password on these devices and secure your primary network along with your guest network with strong passwords.
Having an open dialogue about AI and its implications is key to navigating through the intricacies of this technology. Parents need to have open discussions with kids about the positives and negatives of AI technology. When discussing fake videos and images, emphasize the importance of critical thinking before sharing any content online. Possibly, even introduce them to the desktop application FakeApp, which allows users to swap faces within images and videos seamlessly, leading to the production of deep fake photos and videos. These can appear remarkably realistic and often go viral.
Privacy is another critical area for discussion. After the Cambridge Analytica/Facebook scandal of 2018, the conversation about privacy breaches has become more significant. These incidents remind us how our private (and public) information can be misused for financial or political gain. Locking down privacy settings, being mindful of the information shared, and understanding the implications of reactions and comments are all topics worth discussing.
Awareness and knowledge are the best tools against AI-enabled cybercrime. Making families understand that bogus emails can now be highly personalized and can trick even the most tech-savvy users into clicking malicious links is essential. AI can generate phishing emails, scamming people into handing over sensitive data. In this context, constant reminders to be cautious with every click, even those from known sources, are necessary.
→ Dig Deeper: Malicious Websites – The Web is a Dangerous Place
The advent of AI has also likely allowed hackers to bypass security measures on networks undetected, leading to data breaches, malware attacks, and ransomware. Therefore, being alert and informed is more than just a precaution – it is a vital safety measure in the digital age.
Artificial Intelligence has indeed woven itself into our everyday lives, making things more convenient, efficient, and connected. However, with these advancements come potential risks and challenges. From privacy breaches, and fake content, to AI-enabled cybercrime, the concerns are real and need our full attention. By understanding AI better, having open discussions, and taking appropriate security measures, we can leverage this technology’s immense potential without falling prey to its risks. In our AI-driven world, being informed, aware, and proactive is the key to staying safe and secure.
To safeguard and fortify your online identity, we strongly recommend that you delve into the extensive array of protective features offered by McAfee+. This comprehensive cybersecurity solution is designed to provide you with a robust defense against a wide spectrum of digital threats, ranging from malware and phishing attacks to data breaches and identity theft.
The post AI & Your Family: The Wows and Potential Risks appeared first on McAfee Blog.

In the shadow of the COVID-19 pandemic, workplaces worldwide have undergone a seismic shift towards remote working. This adjustment involves much more than just allowing employees to access work resources from various locations. It necessitates the update of remote working policies and heightened cybersecurity security awareness.
Cybercriminals and potential nation-states are reportedly exploiting the global health crisis for their own gain. Hackers have targeted an array of sectors, including healthcare, employing COVID-19-related baits to manipulate user behavior. This article aims to provide a comprehensive guide on how you, as an employee, can augment your cybersecurity measures and stay safe when working remotely.
It has been reported that criminals are using COVID-19 as bait in phishing emails, domains, malware, and more. While the exploitation of this global crisis is disheartening, it is unsurprising as criminals habitually leverage large events to their advantage. That said, it’s crucial to identify potential targets, particularly in certain geographic regions.
The data so far reveals a broad geographic dispersion of ‘targets,’ with many countries that are typical phishing targets being hit. However, there are anomalies such as Panama, Taiwan, and Japan, suggesting possible campaigns targeting specific countries. The landscape is continuously evolving as more threats are identified, necessitating vigilant monitoring on your part to stay safe.
→ Dig Deeper: McAfee Labs Report Reveals Latest COVID-19 Threats and Malware Surges
The abrupt shift to remote work has left many employees unprepared, with some needing to operate from personal devices. These personal devices, if lacking appropriate security measures, can expose both you and your company or employer to various potential attacks.
Over the last few years, there has been a surge in targeted ransomware attacks, particularly through “commodity malware.” This malware type is often directed at consumers. Consequently, accessing work networks from potentially infected personal devices without appropriate security measures significantly increases the risk. Both employees and employers are left vulnerable to breaches and ransomware lockdowns.
Office closures and working-from-home mandates due to COVID-19 permanently changed the way we look at workplace connectivity. A recent Fenwick poll among HR, privacy, and security professionals across industries noted that approximately 90% of employees now handle intellectual property, confidential, and personal information on their in-home Wi-Fi as opposed to in-office networks. Additionally, many are accessing this information on personal and mobile devices that often do not have the same protections as company-owned devices. The elevated number of unprotected devices connected to unsecured networks creates weak areas in a company’s infrastructure, making it harder to protect against hackers.
One technology your organization should be especially diligent about is video conferencing software. Hackers can infiltrate video conferencing software to eavesdrop on private discussions and steal vital information. Many disrupt video calls via brute force, where they scan a list of possible meeting IDs to try and connect to a meeting. Others seek more complex infiltration methods through vulnerabilities in the actual software. Up until recently, Agora’s video conferencing software exhibited these same vulnerabilities.
Hackers will usually try to gain access to these network vulnerabilities by targeting unsuspecting employees through phishing scams which can lead to even greater consequences if they manage to insert malware or hold your data for ransom. Without proper training on how to avoid these threats, many employees wouldn’t know how to handle the impact should they become the target.
If you’re an employee working remotely, it is essential to comprehend and adhere to best security practices. Here are some guidelines you could follow:
Considering the rise of remote working, it is more crucial than ever for employees, especially those working remotely, to invest in secure solutions and tools. However, as end-users, it’s also wisest to take extra steps like installing comprehensive security software to ward off cyber threats. These software have features that collectively provide a holistic approach to security, detecting vulnerabilities, and minimizing the chance of an attack.
We recommend McAfee+ and McAfee Total Protection if you want an all-inclusive security solution. With a powerful combination of real-time threat detection, antivirus, and malware protection, secure browsing, identity theft prevention, and privacy safeguards, McAfee+ and McAfee Total Protection ensure that your devices and personal information remain secure and your online experience is worry-free.
McAfee Pro Tip: Gauge your security protection and assess your security needs before you get a comprehensive security plan. This proactive approach is the foundation for establishing robust cybersecurity measures tailored to your specific requirements and potential vulnerabilities. Learn more about our award-winning security products award-winning security products.
In the current digital age, employees must be aware of their crucial role in maintaining organizational security. As such, you should consider engaging in tailored security education and training programs that help employees identify and avoid potential threats such as phishing and malicious downloads. Regular training and updates can be beneficial as employees are often the first line of defense and can significantly help mitigate potential security breaches.
To ensure effective acquisition of knowledge, engage in security training that is designed in an engaging, easy-to-understand manner and utilizes practical examples that you can relate to. Successful training programs often incorporate interactive modules, quizzes, and even games to instill important security concepts.
Effective communication and collaboration are paramount in a remote working environment. Employees need to share information and collaborate on projects effectively while ensuring that sensitive information remains secure. Use and participate in platforms that enable secure communication and collaboration. Tools such as secure messaging apps, encrypted email services, secure file sharing, and collaboration platforms will ensure information protection while allowing seamless collaboration.
Make sure that you’re provided with detailed guidelines and training on the proper use of these tools and their security features. This will help prevent data leaks and other security issues that can arise from misuse or misunderstanding.
→ Dig Deeper: Five Tips from McAfee’s Remote Workers
The transition to a remote working environment brings with it various cybersecurity challenges. Prioritizing secure communication and collaboration tools, coupled with ongoing education and adherence to best practices, can help you navigate these challenges with confidence, ultimately reaping the benefits of a flexible and efficient remote work environment while safeguarding critical data and information. McAfee can help you with that and more, so choose the best combination of features that fits your remote work setup.
The post Staying Safe While Working Remotely appeared first on McAfee Blog.

It’s that time of year again: election season! You already know what to expect when you flip on the TV. Get ready for a barrage of commercials, each candidate saying enough to get you to like them but nothing specific enough to which they must stay beholden should they win.
What you might not expect is for sensationalist election “news” to barge in uninvited on your screens. Fake news – or exaggerated or completely falsified articles claiming to be unbiased and factual journalism, often spread via social media – can pop up anytime and anywhere. This election season’s fake news machine will be different than previous years because of the emergence of mainstream artificial intelligence tools.
Here are a few ways desperate zealots may use various AI tools to stir unease and spread misinformation around the upcoming election.
We’ve had time to learn and operate by the adage of “Don’t believe everything you read on the internet.” But now, thanks to deepfake, that lesson must extend to “Don’t believe everything you SEE on the internet.” Deepfake is the digital manipulation of a video or photo. The result often depicts a scene that never happened. At a quick glance, deepfakes can look very real! Some still look real after studying them for a few minutes.
People may use deepfake to paint a candidate in a bad light or to spread sensationalized false news reports. For example, a deepfake could make it look like a candidate flashed a rude hand gesture or show a candidate partying with controversial public figures.
According to McAfee’s Beware the Artificial Imposter report, it only takes three seconds of authentic audio and minimal effort to create a mimicked voice with 85% accuracy. When someone puts their mind to it and takes the time to hone the voice clone, they can achieve a 95% voice match to the real deal.
Well-known politicians have thousands of seconds’ worth of audio clips available to anyone on the internet, giving voice cloners plenty of samples to choose from. Fake news spreaders could employ AI voice generators to add an authentic-sounding talk track to a deepfake video or to fabricate a snappy and sleazy “hot mike” clip to share far and wide online.
Programs like ChatGPT and Bard can make anyone sound intelligent and eloquent. In the hands of rabble-rousers, AI text generation tools can create articles that sound almost professional enough to be real. Plus, AI allows people to churn out content quickly, meaning that people could spread dozens of fake news reports daily. The number of fake articles is only limited by the slight imagination necessary to write a short prompt.
Before you get tricked by a fake news report, here are some ways to spot a malicious use of AI intended to mislead your political leanings:
Is what you’re reading or seeing or hearing too bizarre to be true? That means it probably isn’t. If you’re interested in learning more about a political topic you came across on social media, do a quick search to corroborate a story. Have a list of respected news establishments bookmarked to make it quick and easy to ensure the authenticity of a report.
If you encounter fake news, the best way you can interact with it is to ignore it. Or, in cases where the content is offensive or incendiary, you should report it. Even if the fake news is laughably off-base, it’s still best not to share it with your network, because that’s exactly what the original poster wants: For as many people as possible to see their fabricated stories. All it takes is for someone within your network to look at it too quickly, believe it, and then perpetuate the lies.
It’s great if you’re passionate about politics and the various issues on the ballot. Passion is a powerful driver of change. But this election season, try to focus on what unites us, not what divides us.
The post This Election Season, Be on the Lookout for AI-generated Fake News appeared first on McAfee Blog.

The first of August marks the celebration of World Wide Web Day – a day dedicated to the global network that powers our online activity, creating a wealth of knowledge at our fingertips. The World Wide Web (WWW) has revolutionized the way we communicate, learn, and explore, becoming an integral part of our daily lives. With the importance of the internet only growing stronger, it’s only fitting to honor the World Wide Web with a special day of commemoration. But with the internet comes risks, and it’s important to make sure your family is protected from potential threats. Here are some tips and tricks to keep your family safe online.
Phishing scams are a type of fraud that involves sending emails or other messages that appear to be from a legitimate source. The goal of these messages is to trick users into providing personal information such as passwords, credit card numbers, and bank account details. To protect against phishing scams, teach your family to:
Identity theft is a crime in which someone uses another person’s personal information to commit fraud or other crimes. Teach your family to protect against identity theft by:
A virtual private network (VPN) is a type of technology that provides a secure connection to a private network over the internet. A VPN can help protect your family’s online activity by encrypting the data and hiding your online activity from others. To ensure your family’s online safety, teach them to:
Strong passwords are an important part of online security. Teach your family to create strong passwords and to never share them with anyone. Additionally, use a password manager to store and manage your family’s passwords. A password manager can help by:
To conclude, celebrations on World Wide Web Day allow us to give thanks for the incredible world of knowledge, commerce, entertainment, communication, and innovation that the internet has provided, and continues to provide for us all. By following these tips and tricks, your family can stay safe online and enjoy all the benefits of the internet. Happy World Wide Web Day!
The WWW has enabled us to achieve so many things that were simply impossible before. From the ability to catch up with friends and family across the globe to finding information about virtually any topic, the power of the internet is remarkable. In fact, the World Wide Web has significantly enriched our lives in countless ways.
Did you know that the first-ever image posted on the World Wide Web was a photo of Les Horribles Cernettes, a parody pop band founded by employees at CERN? It was uploaded in 1992 by Sir Tim Berners-Lee, who used a NeXT computer as the first-ever web server. And although we use the term “surfing the net” regularly, do you know who actually coined the phrase? A librarian by the name of Jean Armour Polly wrote an article titled “Surfing the Internet” in the Wilson Library Bulletin at the University of Minnesota in 1992.
There are many other remarkable facts about the World Wide Web, including its growth over the years. By the start of the year 1993, there were only 50 servers worldwide, but that number had grown to over 500 by October of the same year. Advances in data compression enabled media streaming to happen over the web, which was previously impractical due to high bandwidth requirements for uncompressed media. Although the number of websites online was still small in comparison to today’s figure, notable sites such as Yahoo! Directory and Yahoo! Search were launched in 1994 and 1995, respectively, marking the beginning of web commerce.
On World Wide Web Day, you can celebrate by exploring the capabilities of the internet and discovering how it has changed over the years. Many organizations worldwide host events featuring conversations and interviews with technology leaders, entrepreneurs, and creators. There are also different talks, activities, and discussions online that you can join, allowing you to delve deeper into the history and potential of the World Wide Web. You could even consider running an event at your local business to market the day and celebrate what WWW has done for us all!
The post World Wide Web Day: How to Protect Your Family Online appeared first on McAfee Blog.

There are plenty of phish in the sea.
Millions of bogus phishing emails land in millions of inboxes each day with one purpose in mind—to rip off the recipient. Whether they’re out to crack your bank account, steal personal information, or both, you can learn how to spot phishing emails and keep yourself safe.
And some of today’s phishing emails are indeed getting tougher to spot.
They seem like they come from companies you know and trust, like your bank, your credit card company, or services like Netflix, PayPal, and Amazon. And some of them look convincing. The writing and the layout are crisp, and the overall presentation looks professional. Yet still, there’s still something off about them.
And there’s certainly something wrong with that email. It was written by a scammer. Phishing emails employ a bait-and-hook tactic, where an urgent or enticing message is the bait and malware or a link to a phony login page is the hook.
Once the hook gets set, several things might happen. That phony login page may steal account and personal information. Or that malware might install keylogging software that steals information, viruses that open a back door through which data can get hijacked, or ransomware that holds a device and its data hostage until a fee is paid.
Again, you can sidestep these attacks if you know how to spot them. There are signs.
Let’s look at how prolific these attacks are, pick apart a few examples, and then break down the things you should look for.
In the U.S. alone, more than 300,000 victims reported a phishing attack to the FBI in 2022. Phishing attacks topped the list of reported complaints, roughly six times greater than the second top offender, personal data breaches. The actual figure is undoubtedly higher, given that not all attacks get reported.
Looking at phishing attacks worldwide, one study suggests that more than 255 million phishing attempts were made in the second half of 2022 alone. That marks a 61% increase over the previous year. Another study concluded that 1 in every 99 mails sent contained a phishing attack.
Yet scammers won’t always cast such a wide net. Statistics point to a rise in targeted spear phishing, where the attacker goes after a specific person. They will often target people at businesses who have the authority to transfer funds or make payments. Other targets include people who have access to sensitive information like passwords, proprietary data, and account information.
As such, the price of these attacks can get costly. In 2022, the FBI received 21,832 complaints from businesses that said they fell victim to a spear phishing attack. The adjusted losses were over $2.7 billion—an average cost of $123,671 per attack.
So while exacting phishing attack statistics remain somewhat elusive, there’s no question that phishing attacks are prolific. And costly.
Nearly every phishing attack sends an urgent message. One designed to get you to act.
Some examples …
When set within a nice design and paired some official-looking logos, it’s easy to see why plenty of people click the link or attachment that comes with messages like these.
And that’s the tricky thing with phishing attacks. Scammers have leveled up their game in recent years. Their phishing emails can look convincing. Not long ago, you could point to misspellings, lousy grammar, poor design, and logos that looked stretched or that used the wrong colors. Poorly executed phishing attacks like that still make their way into the world. However, it’s increasingly common to see far more sophisticated attacks today. Attacks that appear like a genuine message or notice.
Case in point:
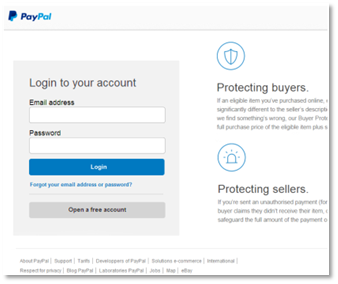
Say you got an email that said your PayPal account had an issue. Would you type your account information here if you found yourself on this page? If so, you would have handed over your information to a scammer.
We took the screenshot above as part of following a phishing attack to its end—without entering any legitimate info, of course. In fact, we entered a garbage email address and password, and it still let us in. That’s because the scammers were after other information, as you’ll soon see.
As we dug into the site more deeply, it looked pretty spot on. The design mirrored PayPal’s style, and the footer links appeared official enough. Yet then we looked more closely.
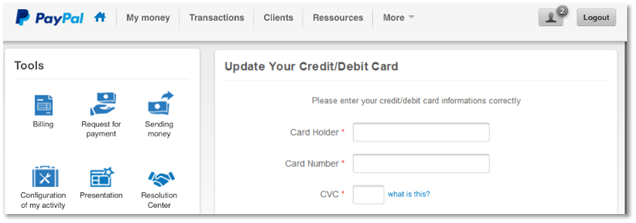
Note the subtle errors, like “card informations” and “Configuration of my activity.” While companies make grammatical errors on occasion, spotting them in an interface should hoist a big red flag. Plus, the site asks for credit card information very early in the process. All suspicious.
Here’s where the attackers really got bold.
They ask for bank “informations,” which not only includes routing and account numbers, but they ask for the account password too. As said, bold. And entirely bogus.
Taken all together, the subtle errors and the bald-faced grab for exacting account information clearly mark this as a scam.
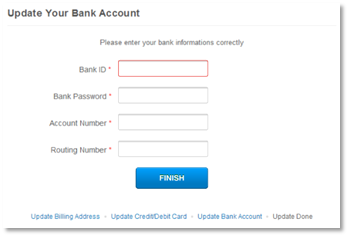
Let’s take a few steps back, though. Who sent the phishing email that directed us to this malicious site? None other than “paypal at inc dot-com.”
Clearly, that’s a phony email. And typical of a phishing attack where an attacker shoehorns a familiar name into an unassociated email address, in this case “inc dot-com.” Attackers may also gin up phony addresses that mimic official addresses, like “paypalcustsv dot-com.” Anything to trick you.
Likewise, the malicious site that the phishing email sent us to used a spoofed address as well. It had no official association with PayPal at all—which is proof positive of a phishing attack.
Note that companies only send emails from their official domain names, just as their sites only use their official domain names. Several companies and organizations will list those official domains on their websites to help curb phishing attacks.
For example, PayPal has a page that clearly states how it will and will not contact you. At McAfee, we have an entire page dedicated to preventing phishing attacks, which also lists the official email addresses we use.
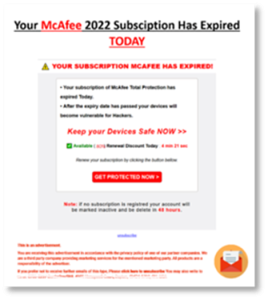
Not every scammer is so sophisticated, at least in the way that they design their phishing emails. We can point to a few phishing emails that posed as legitimate communication from McAfee as examples.
There’s a lot going on in this first email example. The scammers try to mimic the McAfee brand, yet don’t pull it off. Still, they do several things to try to act convincing.

Note the use of photography and the box shot of our software, paired with a prominent “act now” headline. It’s not the style of photography we use. Not that people would generally know this. However, some might have a passing thought like, “Huh. That doesn’t really look like what McAfee usually sends me.”
Beyond that, there are a few capitalization errors, some misplaced punctuation, and the “order now” and “60% off” icons look rather slapped on. Also note the little dash of fear it throws in with a mention of “There are (42) viruses on your computer …”
Taken all together, someone can readily spot that this is a scam with a closer look.
This next ad falls into the less sophisticated category. It’s practically all text and goes heavy on the red ink. Once again, it hosts plenty of capitalization errors, with a few gaffes in grammar as well. In all, it doesn’t read smoothly. Nor is it easy on the eye, as a proper email about your account should be.
What sets this example apart is the “advertisement” disclaimer below, which tries to lend the attack some legitimacy. Also note the phony “unsubscribe” link, plus the (scratched out) mailing address and phone, which all try to do the same.
This last example doesn’t get our font right, and the trademark symbol is awkwardly placed. The usual grammar and capitalization errors crop up again, yet this piece of phishing takes a slightly different approach. 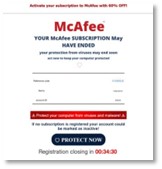
The scammers placed a little timer at the bottom of the email. That adds a degree of scarcity. They want you to think that you have about half an hour before you are unable to register for protection. That’s bogus, of course.
Seeing any recurring themes? There are a few for sure. With these examples in mind, get into the details—how you can spot phishing attacks and how you can avoid them altogether.
Just as we saw, some phishing attacks indeed appear fishy from the start. Yet sometimes it takes a bit of time and a particularly critical eye to spot.
And that’s what scammers count on. They hope that you’re moving quickly or otherwise a little preoccupied when you’re going through your email or messages. Distracted enough so that you might not pause to think, is this message really legit?
One of the best ways to beat scammers is to take a moment to scrutinize that message while keeping the following in mind …
Fear. That’s a big one. Maybe it’s an angry-sounding email from a government agency saying that you owe back taxes. Or maybe it’s another from a family member asking for money because there’s an emergency. Either way, scammers will lean heavily on fear as a motivator.
If you receive such a message, think twice. Consider if it’s genuine. For instance, consider that tax email example. In the U.S., the Internal Revenue Service (IRS) has specific guidelines as to how and when they will contact you. As a rule, they will likely contact you via physical mail delivered by the U.S. Postal Service. (They won’t call or apply pressure tactics—only scammers do that.) Likewise, other nations will have similar standards as well.
Scammers also love urgency. Phishing attacks begin by stirring up your emotions and getting you to act quickly. Scammers might use threats or overly excitable language to create that sense of urgency, both of which are clear signs of a potential scam.
Granted, legitimate businesses and organizations might reach out to notify you of a late payment or possible illicit activity on one of your accounts. Yet they’ll take a far more professional and even-handed tone than a scammer would. For example, it’s highly unlikely that your local electric utility will angrily shut off your service if you don’t pay your past due bill immediately.
Gift cards, cryptocurrency, money orders—these forms of payment are another sign that you might be looking at a phishing attack. Scammers prefer these methods of payment because they’re difficult to trace. Additionally, consumers have little or no way to recover lost funds from these payment methods.
Legitimate businesses and organizations won’t ask for payments in those forms. If you get a message asking for payment in one of those forms, you can bet it’s a scam.
Here’s another way you can spot a phishing attack. Take a close look at the addresses the message is using. If it’s an email, look at the email address. Maybe the address doesn’t match the company or organization at all. Or maybe it does somewhat, yet it adds a few letters or words to the name. This marks yet another sign that you might have a phishing attack on your hands.
Likewise, if the message contains a web link, closely examine that as well. If the name looks at all unfamiliar or altered from the way you’ve seen it before, that might also mean you’re looking at a phishing attempt.
Online protection software can protect you from phishing attacks in several ways.
For starters, it offers web protection that warns you when links lead to malicious websites, such as the ones used in phishing attacks. In the same way, online protection software can warn you about malicious downloads and email attachments so that you don’t end up with malware on your device. And, if the unfortunate does happen, antivirus can block and remove malware.
Online protection software like ours can also address the root of the problem. Scammers must get your email address from somewhere. Often, they get it from online data brokers, sites that gather and sell personal information to any buyer—scammers included.
Data brokers source this information from public records and third parties alike that they sell in bulk, providing scammers with massive mailing lists that can target thousands of potential victims. You can remove your personal info from some of the riskiest data broker sites with our Personal Data Cleanup, which can lower your exposure to scammers by keeping your email address out of their hands.
In all, phishing emails have telltale signs, some more difficult to see than others. Yet you can spot them when you know what to look for and take the time to look for them. With these attacks so prevalent and on the rise, looking at your email with a critical eye is a must today.
The post How to Spot Phishing Emails and Scams appeared first on McAfee Blog.